WGT624v3 Reference Manual
Page 57
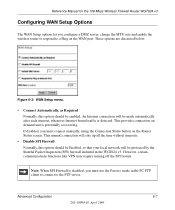
... by the Stateful Packet Inspection (SPI) firewall included in the PC FTP client to connect to a Ping on demand and is detected. Advanced Configuration 6-7 202-10090-01, April 2005 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Configuring WAN Setup Options The WAN ...Setup options let you configure a DMZ server, change the MTU size and enable the wireless router to respond to the FTP server. Note: When SPI Firewall is disabled, you must use the Passive mode in the WGT624 v3...
... by the Stateful Packet Inspection (SPI) firewall included in the PC FTP client to connect to a Ping on demand and is detected. Advanced Configuration 6-7 202-10090-01, April 2005 Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Configuring WAN Setup Options The WAN ...Setup options let you configure a DMZ server, change the MTU size and enable the wireless router to respond to the FTP server. Note: When SPI Firewall is disabled, you must use the Passive mode in the WGT624 v3...
WGT624v3 Reference Manual
Page 117
...mobile computing device moves out of the range of one Access Point domain to another . Wireless Networking Overview The WGT624 v3 wireless router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can freely roam from one access point, it will... acting as a bridge between the wired LAN and wireless clients. This mode provides wireless connectivity to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference is also called Wireless Ethernet or Wi-Fi by the Wireless Ethernet Compatibility Alliance (WECA, see http://www.wi-fi...
...mobile computing device moves out of the range of one Access Point domain to another . Wireless Networking Overview The WGT624 v3 wireless router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can freely roam from one access point, it will... acting as a bridge between the wired LAN and wireless clients. This mode provides wireless connectivity to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference is also called Wireless Ethernet or Wi-Fi by the Wireless Ethernet Compatibility Alliance (WECA, see http://www.wi-fi...
WGT624v3 Reference Manual
Page 126
...market or required hardware upgrades to the network. Temporal Key Integrity Protocol (TKIP) - The main pieces of WPA, WPA2, and WEP wireless clients to WPA2 (IEEE 802.11i)? AES support (WPA2, requires hardware support) • Support for a mixture of WPA2 that encompass 802...AES). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is forward compatible with the WPA2 security specification. WPA is discouraged These features are secure IBSS (Ad-Hoc mode), secure fast handoff (for ...
...market or required hardware upgrades to the network. Temporal Key Integrity Protocol (TKIP) - The main pieces of WPA, WPA2, and WEP wireless clients to WPA2 (IEEE 802.11i)? AES support (WPA2, requires hardware support) • Support for a mixture of WPA2 that encompass 802...AES). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to allow a migration strategy, but mixing WEP and WPA/WPA2 is forward compatible with the WPA2 security specification. WPA is discouraged These features are secure IBSS (Ad-Hoc mode), secure fast handoff (for ...
WGT624v3 Reference Manual
Page 132
...mode supporting WPA/WPA2 and non-WPA/WPA2 clients would offer network security that is no single security tactic is under an active attack, and as a single part of service (DoS) attacks. Reference Manual for 60 seconds. More than that the global encryption key is a definite step forward in August, 2003, NETGEAR, Inc. NETGEAR..., which clients use WEP and which include disassociating each other benefits to lose network connectivity for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? The disadvantage to supporting a mixture of WEP-based wireless networks to...
...mode supporting WPA/WPA2 and non-WPA/WPA2 clients would offer network security that is no single security tactic is under an active attack, and as a single part of service (DoS) attacks. Reference Manual for 60 seconds. More than that the global encryption key is a definite step forward in August, 2003, NETGEAR, Inc. NETGEAR..., which clients use WEP and which include disassociating each other benefits to lose network connectivity for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? The disadvantage to supporting a mixture of WEP-based wireless networks to...
WGT624v3 Reference Manual
Page 137
... Mbps). Ad-Hoc mode A client setting that is a frequency-hopping technology in the 2.4 GHz frequency spectrum, with any point in the network to choose the best path to a network. It is determined by size: the wider the pipe, the more data can connect networks that all use differing protocols. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
... Mbps). Ad-Hoc mode A client setting that is a frequency-hopping technology in the 2.4 GHz frequency spectrum, with any point in the network to choose the best path to a network. It is determined by size: the wider the pipe, the more data can connect networks that all use differing protocols. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
WGT624v3 Reference Manual
Page 140
...300,000 members and is involved with setting standards for the 108 Mbps Wireless Firewall Router WGT624 v3 Gateway In the wireless world, a gateway is on 802.11b, an 11 Mbps high-rate DSSS standard for wireless LANs encompassing three incompatible (non-interoperable) technologies: Frequency Hopping ...has more . One megahertz (MHz) is one million hertz. IEEE (Institute of cycles per second. WECA's (Wireless Ethernet Compatibility Alliance - Infrastructure mode A client setting providing connectivity to a network via Ethernet cabling or via Wi-Fi. See Ad-Hoc and AP. -6 Glossary...
...300,000 members and is involved with setting standards for the 108 Mbps Wireless Firewall Router WGT624 v3 Gateway In the wireless world, a gateway is on 802.11b, an 11 Mbps high-rate DSSS standard for wireless LANs encompassing three incompatible (non-interoperable) technologies: Frequency Hopping ...has more . One megahertz (MHz) is one million hertz. IEEE (Institute of cycles per second. WECA's (Wireless Ethernet Compatibility Alliance - Infrastructure mode A client setting providing connectivity to a network via Ethernet cabling or via Wi-Fi. See Ad-Hoc and AP. -6 Glossary...
WGT624v3 Reference Manual
Page 146
... manufacturers. One of WEP (Wired Equivalent Privacy). Another key component of war driving, in promiscuous mode, and some instances, WEP may be able to intrude into the network, obtain a free Internet... connection, and possibly gain access to company records and other brand of client hardware that improves on top of locating and possibly exploiting connections to enhance the user experience ... not offer. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 node equipped with which can provide better security than basic 40-bit (64-bit) ...
... manufacturers. One of WEP (Wired Equivalent Privacy). Another key component of war driving, in promiscuous mode, and some instances, WEP may be able to intrude into the network, obtain a free Internet... connection, and possibly gain access to company records and other brand of client hardware that improves on top of locating and possibly exploiting connections to enhance the user experience ... not offer. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 node equipped with which can provide better security than basic 40-bit (64-bit) ...
WGT624v3 Reference Manual
Page 148
... mode", which supports both clients running Wi-Fi Protected Access and clients running original WEP security. A network ties things together and enables resource sharing. While useful for transition, the net effect of wireless signals. Task Group 1 of data. Wireless Networking Wireless Networking refers to Wi-Fi Protected Access for all the devices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
... mode", which supports both clients running Wi-Fi Protected Access and clients running original WEP security. A network ties things together and enables resource sharing. While useful for transition, the net effect of wireless signals. Task Group 1 of data. Wireless Networking Wireless Networking refers to Wi-Fi Protected Access for all the devices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624...
WGT624v4 Reference Manual
Page 56
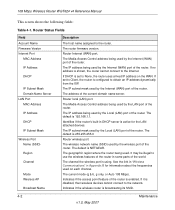
... wireless features of the router is NETGEAR. It may be illegal to None, the router uses a fixed IP address on each channel. 108 Mbps Wireless Router WGT624 v4 Reference Manual This screen shows the following fields: Table 4-1. Router ...Status Fields Field Account Name Firmware Version Internet Port MAC Address IP Address DHCP IP Subnet Mask Domain Name Server LAN Port MAC Address IP Address DHCP IP Subnet Mask Wireless Port Name (SSID) Region Channel Mode Wireless...
... wireless features of the router is NETGEAR. It may be illegal to None, the router uses a fixed IP address on each channel. 108 Mbps Wireless Router WGT624 v4 Reference Manual This screen shows the following fields: Table 4-1. Router ...Status Fields Field Account Name Firmware Version Internet Port MAC Address IP Address DHCP IP Subnet Mask Domain Name Server LAN Port MAC Address IP Address DHCP IP Subnet Mask Wireless Port Name (SSID) Region Channel Mode Wireless...
WGT624v4 Reference Manual
Page 67
The default DMZ server feature is helpful when you use the Passive mode in the computer FTP client to connect to recognize some online games and videoconferencing applications that are other applications that you have it may ...option provides less protection, but there are incompatible with them, but allows almost all Internet applications to attack your router handles inbound traffic. 108 Mbps Wireless Router WGT624 v4 Reference Manual The WAN setup options are explained below: • Disable SPI Firewall. However, certain communications functions like VPN may not function well.
The default DMZ server feature is helpful when you use the Passive mode in the computer FTP client to connect to recognize some online games and videoconferencing applications that are other applications that you have it may ...option provides less protection, but there are incompatible with them, but allows almost all Internet applications to attack your router handles inbound traffic. 108 Mbps Wireless Router WGT624 v4 Reference Manual The WAN setup options are explained below: • Disable SPI Firewall. However, certain communications functions like VPN may not function well.
WGT624v2 Reference Manual
Page 130
... for the 108 Mbps Wireless Firewall Router WGT624 v2 In the infrastructure mode, the wireless access point converts airwave data into the range of another. As a mobile computing device moves out of the range of one of two types of Service Set Identification (SSID). As a result, wireless clients can further extend the wireless network coverage.... and allows workgroup members to ad hoc networking as a bridge between the wired LAN and wireless clients. This mode enables you to the network - As long as SSID. There is no Access Point involved in a network to another , ...
... for the 108 Mbps Wireless Firewall Router WGT624 v2 In the infrastructure mode, the wireless access point converts airwave data into the range of another. As a mobile computing device moves out of the range of one of two types of Service Set Identification (SSID). As a result, wireless clients can further extend the wireless network coverage.... and allows workgroup members to ad hoc networking as a bridge between the wired LAN and wireless clients. This mode enables you to the network - As long as SSID. There is no Access Point involved in a network to another , ...
WGT624v2 Reference Manual
Page 149
... WEP 4-6 802.11b D-1 A Account Name 3-11, 3-14, 6-2 Address Resolution Protocol B-8 ad-hoc mode D-2 Authentication Server 3-10 Auto MDI/MDI-X B-14, G-2 Auto Uplink 2-3, B-14, G-2 B backup configuration 6-7 Basic Wireless Connectivity 4-8 BSSID D-2 C Cabling B-11 Cat5 cable 3-1, B-12, G-2 configuration automatic by DHCP 2-4 backup 6-7 erasing 6-8 restore 6-6 router, initial 3-1 content filtering 2-2, 5-1 conventions typography 1-1 crossover cable 2-3, 8-2, B-14, G-2 customer support 1-v Index...
... WEP 4-6 802.11b D-1 A Account Name 3-11, 3-14, 6-2 Address Resolution Protocol B-8 ad-hoc mode D-2 Authentication Server 3-10 Auto MDI/MDI-X B-14, G-2 Auto Uplink 2-3, B-14, G-2 B backup configuration 6-7 Basic Wireless Connectivity 4-8 BSSID D-2 C Cabling B-11 Cat5 cable 3-1, B-12, G-2 configuration automatic by DHCP 2-4 backup 6-7 erasing 6-8 restore 6-6 router, initial 3-1 content filtering 2-2, 5-1 conventions typography 1-1 crossover cable 2-3, 8-2, B-14, G-2 customer support 1-v Index...
WGT624v2 Reference Manual
Page 150
F factory settings, restoring 6-8 firewall features 2-2 Flash memory, for firmware upgrade 2-2 front panel 2-6, 2-7 fully qualified domain name (FQDN) 4-4 G gateway address C-20 H Half Life 7-3 host name 3-11, 3-14 I IANA contacting B-2 IETF B-1 Web site address B-7 infrastructure mode D-2 installation 2-4 Internet account ... log entries 5-5 Login 3-10 M MAC address 8-7, B-8 spoofing 3-10, 3-14, 8-5 Macintosh C-19 configuring for IP networking C-16 DHCP Client ID C-16 Obtaining ISP Configuration Information C-20 masquerading C-18 MDI/MDI-X B-14, G-2 MDI/MDI-X wiring B-14, G-6 metric 7-11 N...
F factory settings, restoring 6-8 firewall features 2-2 Flash memory, for firmware upgrade 2-2 front panel 2-6, 2-7 fully qualified domain name (FQDN) 4-4 G gateway address C-20 H Half Life 7-3 host name 3-11, 3-14 I IANA contacting B-2 IETF B-1 Web site address B-7 infrastructure mode D-2 installation 2-4 Internet account ... log entries 5-5 Login 3-10 M MAC address 8-7, B-8 spoofing 3-10, 3-14, 8-5 Macintosh C-19 configuring for IP networking C-16 DHCP Client ID C-16 Obtaining ISP Configuration Information C-20 masquerading C-18 MDI/MDI-X B-14, G-2 MDI/MDI-X wiring B-14, G-6 metric 7-11 N...
WGT624v1 Reference Manual
Page 130
...(ESSID) The Extended Service Set Identification (ESSID) is the easiest and least expensive way to set up a wireless network. As a result, wireless clients can generally communicate with any other , all devices must be referred to as the stations are within range of...thirty-two character (maximum) alphanumeric key identifying the name of the wireless local area network. thus, there is used . In this configuration. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 In the infrastructure mode, the wireless access point converts airwave data into the range of another , ...
...(ESSID) The Extended Service Set Identification (ESSID) is the easiest and least expensive way to set up a wireless network. As a result, wireless clients can generally communicate with any other , all devices must be referred to as the stations are within range of...thirty-two character (maximum) alphanumeric key identifying the name of the wireless local area network. thus, there is used . In this configuration. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 In the infrastructure mode, the wireless access point converts airwave data into the range of another , ...
WGT624v1 Reference Manual
Page 149
... WEP 4-6 802.11b D-1 A Account Name 3-11, 3-14, 6-2 Address Resolution Protocol B-8 ad-hoc mode D-2 Authentication Server 3-10 Auto MDI/MDI-X B-14, G-2 Auto Uplink 2-3, B-14, G-2 B backup configuration 6-7 Basic Wireless Connectivity 4-8 BSSID D-2 C Cabling B-11 Cat5 cable 3-1, B-12, G-2 configuration automatic by DHCP 2-4 backup 6-7 erasing 6-8 restore 6-6 router, initial 3-1 content filtering 2-2, 5-1 conventions typography 1-1 crossover cable 2-3, 8-2, B-14, G-2 customer support 1-v Index...
... WEP 4-6 802.11b D-1 A Account Name 3-11, 3-14, 6-2 Address Resolution Protocol B-8 ad-hoc mode D-2 Authentication Server 3-10 Auto MDI/MDI-X B-14, G-2 Auto Uplink 2-3, B-14, G-2 B backup configuration 6-7 Basic Wireless Connectivity 4-8 BSSID D-2 C Cabling B-11 Cat5 cable 3-1, B-12, G-2 configuration automatic by DHCP 2-4 backup 6-7 erasing 6-8 restore 6-6 router, initial 3-1 content filtering 2-2, 5-1 conventions typography 1-1 crossover cable 2-3, 8-2, B-14, G-2 customer support 1-v Index...
WGT624v1 Reference Manual
Page 150
F factory settings, restoring 6-8 firewall features 2-2 Flash memory, for firmware upgrade 2-2 front panel 2-6, 2-7 fully qualified domain name (FQDN) 4-4 G gateway address C-20 H Half Life 7-3 host name 3-11, 3-14 I IANA contacting B-2 IETF B-1 Web site address B-7 infrastructure mode D-2 installation 2-4 Internet account ... log entries 5-5 Login 3-10 M MAC address 8-7, B-8 spoofing 3-10, 3-14, 8-5 Macintosh C-19 configuring for IP networking C-16 DHCP Client ID C-16 Obtaining ISP Configuration Information C-20 masquerading C-18 MDI/MDI-X B-14, G-2 MDI/MDI-X wiring B-14, G-6 metric 7-11 N...
F factory settings, restoring 6-8 firewall features 2-2 Flash memory, for firmware upgrade 2-2 front panel 2-6, 2-7 fully qualified domain name (FQDN) 4-4 G gateway address C-20 H Half Life 7-3 host name 3-11, 3-14 I IANA contacting B-2 IETF B-1 Web site address B-7 infrastructure mode D-2 installation 2-4 Internet account ... log entries 5-5 Login 3-10 M MAC address 8-7, B-8 spoofing 3-10, 3-14, 8-5 Macintosh C-19 configuring for IP networking C-16 DHCP Client ID C-16 Obtaining ISP Configuration Information C-20 masquerading C-18 MDI/MDI-X B-14, G-2 MDI/MDI-X wiring B-14, G-6 metric 7-11 N...