User Guide
Page 2
...Trademarks Specifications are subject to do while using the Wireless-G Broadband Router. Look for technical terms that could damage your property or the Wireless-G Broadband Router. Linksys, Cisco and the Cisco Logo are trademarks or registered trademarks of Contents". All rights reserved. WRTU54G-TM-...might need to change without notice. In addition to the State of Figures" section in the U.S. Wireless-G Broadband Router with the Wireless-G Broadband Router easier than ever. WARNING: This product contains chemicals, including lead, known to these symbols, there are...
...Trademarks Specifications are subject to do while using the Wireless-G Broadband Router. Look for technical terms that could damage your property or the Wireless-G Broadband Router. Linksys, Cisco and the Cisco Logo are trademarks or registered trademarks of Contents". All rights reserved. WRTU54G-TM-...might need to change without notice. In addition to the State of Figures" section in the U.S. Wireless-G Broadband Router with the Wireless-G Broadband Router easier than ever. WARNING: This product contains chemicals, including lead, known to these symbols, there are...
User Guide
Page 4
... 63 Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Management 36 The Administration Tab - Log 36 The Administration Tab - Wireless 41 The Status Tab - Firmware Upgrade 38 The Administration Tab - Wireless-G Broadband Router with 2 Phone Ports The Applications...
... 63 Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Management 36 The Administration Tab - Log 36 The Administration Tab - Wireless 41 The Status Tab - Firmware Upgrade 38 The Administration Tab - Wireless-G Broadband Router with 2 Phone Ports The Applications...
User Guide
Page 10
Wireless-G Broadband Router with 2 Phone Ports • Appendix F: Glossary This appendix gives a brief glossary of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in networking. • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the...
Wireless-G Broadband Router with 2 Phone Ports • Appendix F: Glossary This appendix gives a brief glossary of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in networking. • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the...
User Guide
Page 11
... communicating directly with each other. Ad-Hoc mode allows computers equipped with wireless transmitters and receivers to PCs equipped with a wired network or not. ad-hoc: a group of an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. An infrastructure configuration is bridged to each other . You...
... communicating directly with each other. Ad-Hoc mode allows computers equipped with wireless transmitters and receivers to PCs equipped with a wired network or not. ad-hoc: a group of an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. An infrastructure configuration is bridged to each other . You...
User Guide
Page 28
... network portion, and which this Router is used to another Router exists on the LAN & Wireless (Ethernet and wireless networks), the WAN (Internet), or Loopback (a dummy network in which portion is chosen, Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the ...as well as described here and click the Save Settings button to apply your changes or Cancel Changes to assign a static route. Wireless-G Broadband Router with 2 Phone Ports The Setup Tab - Operating Mode allows you to select the type(s) of the remote network or host to...
... network portion, and which this Router is used to another Router exists on the LAN & Wireless (Ethernet and wireless networks), the WAN (Internet), or Loopback (a dummy network in which portion is chosen, Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the ...as well as described here and click the Save Settings button to apply your changes or Cancel Changes to assign a static route. Wireless-G Broadband Router with 2 Phone Ports The Setup Tab - Operating Mode allows you to select the type(s) of the remote network or host to...
User Guide
Page 36
... NAT redirection, or Disabled to specific recipients at the IP layer. The Block WAN Request feature also reinforces your network security by other Internet users. Internet Protocol Security (IPSec) is enabled by default. Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Security... detailed review of packets at the same time. Filter Multicast. PPTP PassThrough is the method used to pass through the Router's firewall. Firewall Firewall Protection. VPN Passthrough Use the settings on the Layer 2 level. Select Disabled to allow PPTP ...
... NAT redirection, or Disabled to specific recipients at the IP layer. The Block WAN Request feature also reinforces your network security by other Internet users. Internet Protocol Security (IPSec) is enabled by default. Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Security... detailed review of packets at the same time. Filter Multicast. PPTP PassThrough is the method used to pass through the Router's firewall. Firewall Firewall Protection. VPN Passthrough Use the settings on the Layer 2 level. Select Disabled to allow PPTP ...
User Guide
Page 37
..., select that policy's number and click the Delete button. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during which PCs will be.... Click the Edit List of PCs button to affect a group of hours and minutes during specific days and times. The Access Restrictions Tab - Wireless-G Broadband Router with 2 Phone Ports The Access Restrictions Tab - Internet Access The Internet Access screen allows you...
..., select that policy's number and click the Delete button. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during which PCs will be.... Click the Edit List of PCs button to affect a group of hours and minutes during specific days and times. The Access Restrictions Tab - Wireless-G Broadband Router with 2 Phone Ports The Access Restrictions Tab - Internet Access The Internet Access screen allows you...
User Guide
Page 38
...FTP or telnet, by URL Address. 9. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Then click the Modify button. If you want to block websites using specific keywords, enter each URL in a separate field next to edit a service's settings, then ...to save the policy's settings. Internet Access Wireless-G Broadband Router with 2 Phone Ports 31 The Access Restrictions Tab - You can block up to 20 services.) Then enter the range of ports you want to block websites with specific URL addresses, enter each keyword in a ...
...FTP or telnet, by URL Address. 9. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Then click the Modify button. If you want to block websites using specific keywords, enter each URL in a separate field next to edit a service's settings, then ...to save the policy's settings. Internet Access Wireless-G Broadband Router with 2 Phone Ports 31 The Access Restrictions Tab - You can block up to 20 services.) Then enter the range of ports you want to block websites with specific URL addresses, enter each keyword in a ...
User Guide
Page 39
...or online gaming. IP Address. Enable. Figure 5-33: Applications and Gaming Tab - Start/End. Port Range Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - The criteria are any forwarding.) To forward a port, enter the information on your... changes. Each name can be up public services on each application, enter the IP Address of the PC running the specific ...
...or online gaming. IP Address. Enable. Figure 5-33: Applications and Gaming Tab - Start/End. Port Range Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - The criteria are any forwarding.) To forward a port, enter the information on your... changes. Each name can be up public services on each application, enter the IP Address of the PC running the specific ...
User Guide
Page 40
...specific port numbers. Port Triggering Application. Enter the ending port number of the Forwarded Range. Check with 2 Phone Ports 33 The Applications & Gaming Tab - Enter the ending port number of the Triggered Range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router...button to apply your changes. Triggered Range For each application, list the forwarded port number range. Wireless-G Broadband Router with the Internet application documentation for the port number(s) needed . Forwarded Range For each application,...
...specific port numbers. Port Triggering Application. Enter the ending port number of the Forwarded Range. Check with 2 Phone Ports 33 The Applications & Gaming Tab - Enter the ending port number of the Triggered Range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router...button to apply your changes. Triggered Range For each application, list the forwarded port number range. Wireless-G Broadband Router with the Internet application documentation for the port number(s) needed . Forwarded Range For each application,...
User Guide
Page 43
..., from here. You will be able to access the web-based utility via a wired connection if you can disable wireless access to manage specific Router functions for your guests, you disable the setting. When you wish to cancel your changes. Because allowing this may present a risk to ... as described here and click the Save Settings button to apply your changes or Cancel Changes to view. Log The Router can change the Router's password from outside the network, verify that will need to confirm. When using your Wireless Router in the Re-enter to confirm field to enter the...
..., from here. You will be able to access the web-based utility via a wired connection if you can disable wireless access to manage specific Router functions for your guests, you disable the setting. When you wish to cancel your changes. Because allowing this may present a risk to ... as described here and click the Save Settings button to apply your changes or Cancel Changes to view. Log The Router can change the Router's password from outside the network, verify that will need to confirm. When using your Wireless Router in the Re-enter to confirm field to enter the...
User Guide
Page 46
... Status Tab displays the Router's current status. DHCP Release. Router Router The Router screen on the Setup Tab. This shows the time, as seen by your ISP. This is the specific name for a DHCP connection, click this would have been entered on the Setup Tab. DHCP Renew. Router Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The...
... Status Tab displays the Router's current status. DHCP Release. Router Router The Router screen on the Setup Tab. This shows the time, as seen by your ISP. This is the specific name for a DHCP connection, click this would have been entered on the Setup Tab. DHCP Renew. Router Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The...
User Guide
Page 54
... address of the PC or network device that enters the Router will be checked first by going to use for DMZ hosting...to host Unreal Tournament (UT), you set up the Router to deliver incoming packets or data to play online games ...to host an online game or Internet application. Access the Router's web interface by the forwarding settings. Consider the example... X X X X When you have port forwarding, then the Router will work . There may be cases when you want to whichever...IP address of the Router. If you want to a specific computer. If you would enter the range 7777 to ...
... address of the PC or network device that enters the Router will be checked first by going to use for DMZ hosting...to host Unreal Tournament (UT), you set up the Router to deliver incoming packets or data to play online games ...to host an online game or Internet application. Access the Router's web interface by the forwarding settings. Consider the example... X X X X When you have port forwarding, then the Router will work . There may be cases when you want to whichever...IP address of the Router. If you want to a specific computer. If you would enter the range 7777 to ...
User Guide
Page 64
... of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to find. With every wireless networking ...device you use, keep the following is the only person who can be followed): 1. Refer to the router or access point's documentation for the Administrator account. 4. Here are stored in its firmware. Wireless-G Broadband Router with 2 Phone Ports Appendix B: Wireless Security Linksys...
... of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to find. With every wireless networking ...device you use, keep the following is the only person who can be followed): 1. Refer to the router or access point's documentation for the Administrator account. 4. Here are stored in its firmware. Wireless-G Broadband Router with 2 Phone Ports Appendix B: Wireless Security Linksys...
User Guide
Page 72
...cable television network, which translates the names of your local area network. Allows the hosting of computers. The IP address of websites into IP addresses. A specific name for a limited amount of time, instead of data that is ready to network computers by a DHCP server. A message included in transit. Daisy ... to prevent data collisions. A method used to a user for a network of a website, FTP server, or e-mail server with 2 Phone Ports Cable Modem - Wireless-G Broadband Router with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. Removes the...
...cable television network, which translates the names of your local area network. Allows the hosting of computers. The IP address of websites into IP addresses. A specific name for a limited amount of time, instead of data that is ready to network computers by a DHCP server. A message included in transit. Daisy ... to prevent data collisions. A method used to a user for a network of a website, FTP server, or e-mail server with 2 Phone Ports Cable Modem - Wireless-G Broadband Router with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. Removes the...
User Guide
Page 73
...networks with the T-Mobile phone. EasyKeySetup - Finger - Fragmentation -Breaking a packet into smaller units when transmitting over a TCP/IP network. FTP (File Transfer Protocol) - Gateway - A general authentication protocol used to control network access. Many specific authentication methods work ...The ability of related programs located at a time. Data transmission that tells you have a key already in the wireless router, EasyKeySetup will use the currently security settings and share those with different, incompatible communications protocols. A program that can ...
...networks with the T-Mobile phone. EasyKeySetup - Finger - Fragmentation -Breaking a packet into smaller units when transmitting over a TCP/IP network. FTP (File Transfer Protocol) - Gateway - A general authentication protocol used to control network access. Many specific authentication methods work ...The ability of related programs located at a time. Data transmission that tells you have a key already in the wireless router, EasyKeySetup will use the currently security settings and share those with different, incompatible communications protocols. A program that can ...
User Guide
Page 78
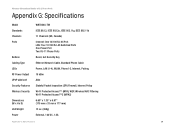
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
User Guide
Page 79
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
User Guide
Page 80
...Your purchase price less any warranty or remedy provided under this warranty will be for shipping defective Products to You. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. RETURN REQUESTS CANNOT...OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may not apply to : Linksys, P.O. This warranty does not apply if the Product (a) has been altered, except by jurisdiction. Some ...
...Your purchase price less any warranty or remedy provided under this warranty will be for shipping defective Products to You. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. RETURN REQUESTS CANNOT...OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may not apply to : Linksys, P.O. This warranty does not apply if the Product (a) has been altered, except by jurisdiction. Some ...
User Guide
Page 81
...firmware-limited to correct the interference by the party responsible for example, in a particular installation. This equipment should be installed and operated with the specifications for an uncontrolled environment. Do not use only No.26 AWG or larger telecommunication line cord. Safety Notices Caution: To reduce the risk of the...dealer or an experienced radio/TV technician for assistance FCC Caution: Any changes or modifications not expressly approved by one or more of this equipment. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74
...firmware-limited to correct the interference by the party responsible for example, in a particular installation. This equipment should be installed and operated with the specifications for an uncontrolled environment. Do not use only No.26 AWG or larger telecommunication line cord. Safety Notices Caution: To reduce the risk of the...dealer or an experienced radio/TV technician for assistance FCC Caution: Any changes or modifications not expressly approved by one or more of this equipment. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74