User Guide
Page 2
Linksys, Cisco and the Cisco Logo are trademarks or registered trademarks of their respective holders. and certain other reproductive harm. All rights reserved. Other brands and product names are registered trademarks or trademarks of Contents". Look for technical terms that could damage your property or the Wireless-G Broadband Router... defects or other countries. WRTU54G-TM-UG-81009-B-BW-DF-JL How to Use This User Guide This User Guide has been designed to make understanding networking with 2 Phone Ports Copyright and Trademarks Specifications are definitions for the following...
Linksys, Cisco and the Cisco Logo are trademarks or registered trademarks of their respective holders. and certain other reproductive harm. All rights reserved. Other brands and product names are registered trademarks or trademarks of Contents". Look for technical terms that could damage your property or the Wireless-G Broadband Router... defects or other countries. WRTU54G-TM-UG-81009-B-BW-DF-JL How to Use This User Guide This User Guide has been designed to make understanding networking with 2 Phone Ports Copyright and Trademarks Specifications are definitions for the following...
User Guide
Page 4
... Vista Instructions 62 For the Router's Web-based Utility 63 Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Linksys Software License Agreement 81 Schedule 2 84 Schedule 3 89 Schedule 4 97 Appendix K: Contact Information 100 Wireless 41 The Status Tab...
... Vista Instructions 62 For the Router's Web-based Utility 63 Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Linksys Software License Agreement 81 Schedule 2 84 Schedule 3 89 Schedule 4 97 Appendix K: Contact Information 100 Wireless 41 The Status Tab...
User Guide
Page 10
... the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of terms frequently used in this User Guide? Wireless-G Broadband Router with 2 Phone...
... the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of terms frequently used in this User Guide? Wireless-G Broadband Router with 2 Phone...
User Guide
Page 11
... with both your 802.11b and 802.11g products. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. infrastructure: a wireless network that is bridged to communicate with your Ethernet hardware as the Wireless-G Broadband Router, which can set identifier): your wireless network to a wired network via an access point. An infrastructure configuration...
... with both your 802.11b and 802.11g products. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. infrastructure: a wireless network that is bridged to communicate with your Ethernet hardware as the Wireless-G Broadband Router, which can set identifier): your wireless network to a wired network via an access point. An infrastructure configuration...
User Guide
Page 28
... which performs dynamic routing over your Ethernet and wireless networks. The Router determines the network packets' route based on your network. You can also select LAN & Wireless, which portion is the host portion. Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Setup Tab -... which one PC acts like a network- This interface tells you 've already set up . If this Router will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to set up a fixed route to assign a static route...
... which performs dynamic routing over your Ethernet and wireless networks. The Router determines the network packets' route based on your network. You can also select LAN & Wireless, which portion is the host portion. Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Setup Tab -... which one PC acts like a network- This interface tells you 've already set up . If this Router will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to set up a fixed route to assign a static route...
User Guide
Page 36
... these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to pass through the Router's firewall. Firewall Figure 5-27: Security Tab - Select Disabled to allow L2TP tunnels to cancel your network. Filter Internet NAT...or Disabled to disable this feature. L2TP Pass-through the Router, click Enable. Wireless-G Broadband Router with 2 Phone Ports The Security Tab - Firewall Firewall Protection. Select Enable to disable this feature. Select Disable to specific recipients at the IP layer. Enable the Block WAN Request ...
... these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to pass through the Router's firewall. Firewall Figure 5-27: Security Tab - Select Disabled to allow L2TP tunnels to cancel your network. Filter Internet NAT...or Disabled to disable this feature. L2TP Pass-through the Router, click Enable. Wireless-G Broadband Router with 2 Phone Ports The Security Tab - Firewall Firewall Protection. Select Enable to disable this feature. Select Disable to specific recipients at the IP layer. Enable the Block WAN Request ...
User Guide
Page 37
...To return to block or allow specific kinds of PCs. You can select a PC by selecting the policy or policies and clicking the Delete button. To enable this screen to cancel your changes. The List of PCs 30 Wireless-G Broadband Router with 2 Phone Ports The Access...Decide which the policy will be in effect, or select Everyday. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during which days and what times...
...To return to block or allow specific kinds of PCs. You can select a PC by selecting the policy or policies and clicking the Delete button. To enable this screen to cancel your changes. The List of PCs 30 Wireless-G Broadband Router with 2 Phone Ports The Access...Decide which the policy will be in effect, or select Everyday. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during which days and what times...
User Guide
Page 38
...a separate field next to edit a service's settings, then click the Add/Edit Service button. If you want to block websites with specific URL addresses, enter each keyword in the Port Range fields. Change these settings as FTP or telnet, by selecting services from the Protocol ... changes on the Port Services screen, click the Apply button to save the policy's settings. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Select its protocol from the drop-down menu, and enter its name, protocol setting, or port range. To delete...
...a separate field next to edit a service's settings, then click the Add/Edit Service button. If you want to block websites with specific URL addresses, enter each keyword in the Port Range fields. Change these settings as FTP or telnet, by selecting services from the Protocol ... changes on the Port Services screen, click the Apply button to save the policy's settings. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Select its protocol from the drop-down menu, and enter its name, protocol setting, or port range. To delete...
User Guide
Page 39
...servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Port Range Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - Start/End. Figure 5-33: Applications and Gaming Tab - For each line for... gaming. Each name can be up public services on each application, enter the IP Address of the PC running the specific application. This is the port range. Protocol. Enable. Change these settings as described here and click the Save Settings ...
...servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Port Range Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - Start/End. Figure 5-33: Applications and Gaming Tab - For each line for... gaming. Each name can be up public services on each application, enter the IP Address of the PC running the specific application. This is the port range. Protocol. Enable. Change these settings as described here and click the Save Settings ...
User Guide
Page 40
...click the Save Settings button to apply your changes or Cancel Changes to watch outgoing data for the port number(s) needed . Wireless-G Broadband Router with the Internet application documentation for the port number(s) needed . Port Triggering Start Port. End Port. Port Triggering Application. ..., list the forwarded port number range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router with the Internet application documentation for specific port numbers. Port Triggering The Port Triggering screen allows the...
...click the Save Settings button to apply your changes or Cancel Changes to watch outgoing data for the port number(s) needed . Wireless-G Broadband Router with the Internet application documentation for the port number(s) needed . Port Triggering Start Port. End Port. Port Triggering Application. ..., list the forwarded port number range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router with the Internet application documentation for specific port numbers. Port Triggering The Port Triggering screen allows the...
User Guide
Page 43
... servers on which you are giving wireless access to your guests, you can disable wireless access to manage specific Router functions for higher security. Wireless Access Web - Select Enable to enable wireless access to the Router's web-based utility or Disable to disable wireless access to security, this feature is selected. Remote Router Access. Change these settings as described...
... servers on which you are giving wireless access to your guests, you can disable wireless access to manage specific Router functions for higher security. Wireless Access Web - Select Enable to enable wireless access to the Router's web-based utility or Disable to disable wireless access to security, this feature is selected. Remote Router Access. Change these settings as described...
User Guide
Page 46
... a DHCP connection, click this would have been entered on the Setup Tab. Router This is the specific name for connection to the Router's Internet port. This is the Router's MAC Address, as you set on the Setup Tab. Current Time. Domain Name. Wireless-G Broadband Router with 2 Phone Ports 39 The Status Tab - This information was entered...
... a DHCP connection, click this would have been entered on the Setup Tab. Router This is the specific name for connection to the Router's Internet port. This is the Router's MAC Address, as you set on the Setup Tab. Current Time. Domain Name. Wireless-G Broadband Router with 2 Phone Ports 39 The Status Tab - This information was entered...
User Guide
Page 54
...get the Internet game, server, or application to host Unreal Tournament (UT), you are not sure which port services to use . The best way to a specific computer. Enter any port forwarding or DMZ hosting. For example, if the web server's Ethernet adapter IP address is available when an application requires too... be cases when you want to work without doing any name you are using , TCP and/or UDP. 5. Wireless-G Broadband Router with 2 Phone Ports 7. Consider the example below: Application UT Halflife PC Anywhere VPN IPSEC Start and End 7777 to 27900 27015 to 27015 5631 to...
...get the Internet game, server, or application to host Unreal Tournament (UT), you are not sure which port services to use . The best way to a specific computer. Enter any port forwarding or DMZ hosting. For example, if the web server's Ethernet adapter IP address is available when an application requires too... be cases when you want to work without doing any name you are using , TCP and/or UDP. 5. Wireless-G Broadband Router with 2 Phone Ports 7. Consider the example below: Application UT Halflife PC Anywhere VPN IPSEC Start and End 7777 to 27900 27015 to 27015 5631 to...
User Guide
Page 64
... 5 should be easily decrypted and contain much of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to join a wireless network, wireless networking products first listen for more information. 57 Refer to "Chapter 5: Configuring the Wireless-G Broadband Router." Enable MAC Address Filtering. 5. Change the administrator's password...
... 5 should be easily decrypted and contain much of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to join a wireless network, wireless networking products first listen for more information. 57 Refer to "Chapter 5: Configuring the Wireless-G Broadband Router." Enable MAC Address Filtering. 5. Change the administrator's password...
User Guide
Page 72
... Access/Collision Avoidance) - CTS (Clear To Send) - DMZ (Demilitarized Zone) - A specific name for a limited amount of time, instead of assigning permanent IP addresses. To receive a file transmitted over traditional phone lines. DSSS (Direct-Sequence Spread-Spectrum) - Dynamic IP Address - Wireless-G Broadband Router with a redundant bit pattern resulting in a lower probability of information being...
... Access/Collision Avoidance) - CTS (Clear To Send) - DMZ (Demilitarized Zone) - A specific name for a limited amount of time, instead of assigning permanent IP addresses. To receive a file transmitted over traditional phone lines. DSSS (Direct-Sequence Spread-Spectrum) - Dynamic IP Address - Wireless-G Broadband Router with a redundant bit pattern resulting in a lower probability of information being...
User Guide
Page 73
... a combination of a network from users from a common transmission medium. Half Duplex - Hardware - Wireless-G Broadband Router with the T-Mobile phone. Many specific authentication methods work within this framework. EasyKeySetup - Data transmission that specifies how data is placed on your... EAP-PEAP (Extensible Authentication Protocol-Protected Extensible Authentication Protocol) - If you have a key already in the wireless router, EasyKeySetup will use the currently security settings and share those with 2 Phone Ports EAP (Extensible Authentication Protocol) ...
... a combination of a network from users from a common transmission medium. Half Duplex - Hardware - Wireless-G Broadband Router with the T-Mobile phone. Many specific authentication methods work within this framework. EasyKeySetup - Data transmission that specifies how data is placed on your... EAP-PEAP (Extensible Authentication Protocol-Protected Extensible Authentication Protocol) - If you have a key already in the wireless router, EasyKeySetup will use the currently security settings and share those with 2 Phone Ports EAP (Extensible Authentication Protocol) ...
User Guide
Page 78
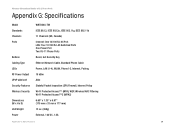
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
User Guide
Page 79
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
User Guide
Page 80
...specific legal rights, and You may not apply to You. Some jurisdictions do not allow the exclusion or limitation of purchase. If the Product proves defective during the Warranty Period call Linksys Technical Support in accordance with 2 Phone Ports Appendix H: Warranty Information LIMITED WARRANTY Linksys... all shipping and handling charges. Box 18558, Irvine, CA 92623 USA. 73 Appendix H: Warranty Information Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. If...
...specific legal rights, and You may not apply to You. Some jurisdictions do not allow the exclusion or limitation of purchase. If the Product proves defective during the Warranty Period call Linksys Technical Support in accordance with 2 Phone Ports Appendix H: Warranty Information LIMITED WARRANTY Linksys... all shipping and handling charges. Box 18558, Irvine, CA 92623 USA. 73 Appendix H: Warranty Information Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. If...
User Guide
Page 81
...802.11g operation of the FCC Rules. There may cause undesired operation. FCC Radiation Exposure Statement This equipment complies with the specifications for compliance could void the user's authority to Part 15 of fire, use this product during an electrical storm. These ... Avoid using this product near water, for an uncontrolled environment. Safety Notices Caution: To reduce the risk of the FCC Rules. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74 This product has been tested and complies with FCC radiation exposure limits set ...
...802.11g operation of the FCC Rules. There may cause undesired operation. FCC Radiation Exposure Statement This equipment complies with the specifications for compliance could void the user's authority to Part 15 of fire, use this product during an electrical storm. These ... Avoid using this product near water, for an uncontrolled environment. Safety Notices Caution: To reduce the risk of the FCC Rules. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74 This product has been tested and complies with FCC radiation exposure limits set ...