User Guide
Page 35
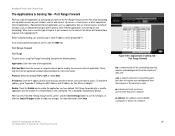
...gaming. Select the protocol TCP or UDP, or select Both. Port Range Forwarding for Your Ethernet Adapter." Broadband Router with the Internet application software documentation for more information. Before using Port Range Forwarding, complete the following fields: Application. ip (internet ...server or Internet application. This is left unchecked. Port range forwarding sets up public services on a network Chapter 5: Configuring the Router 29 The Applications & Gaming Tab - Protocol. IP Address. Figure 5-24: Applications & Gaming Tab Port Range Forward tcp: ...
...gaming. Select the protocol TCP or UDP, or select Both. Port Range Forwarding for Your Ethernet Adapter." Broadband Router with the Internet application software documentation for more information. Before using Port Range Forwarding, complete the following fields: Application. ip (internet ...server or Internet application. This is left unchecked. Port range forwarding sets up public services on a network Chapter 5: Configuring the Router 29 The Applications & Gaming Tab - Protocol. IP Address. Figure 5-24: Applications & Gaming Tab Port Range Forward tcp: ...
User Guide
Page 38
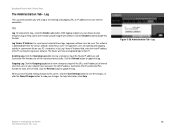
...), which is a data structure that you want the Internet users to be controlled (turned off, on the Internet. IP Address. Broadband Router with the Internet application documentation for more information. A widely used to connect to access. The agents return information contained in the Int... You cannot select both protocols. The protocol used network monitoring and control protocol. Check with the Internet application software documentation for Your Ethernet Adapter." Enter the IP address of the external port used to undo your changes. This is left unchecked....
...), which is a data structure that you want the Internet users to be controlled (turned off, on the Internet. IP Address. Broadband Router with the Internet application documentation for more information. A widely used to connect to access. The agents return information contained in the Int... You cannot select both protocols. The protocol used network monitoring and control protocol. Check with the Internet application software documentation for Your Ethernet Adapter." Enter the IP address of the external port used to undo your changes. This is left unchecked....
User Guide
Page 42
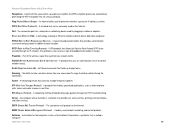
... to that users on your PC's hard drive. Log Viewer IP Address. For a permanent record of the PC running the Logviewer software. The Router will now send updated logs to view a temporary log of all the URLs and IP addresses of Internet sites that PC. Click...button to disable this function. Figure 5-29: Administration Tab - Log With logging enabled, you have accessed. This software is downloadable from the Linksys website, www.linksys.com. Outgoing Log. Broadband Router with a log of all incoming and outgoing URLs or IP addresses for your Internet connection. Log The Log screen...
... to that users on your PC's hard drive. Log Viewer IP Address. For a permanent record of the PC running the Logviewer software. The Router will now send updated logs to view a temporary log of all the URLs and IP addresses of Internet sites that PC. Click...button to disable this function. Figure 5-29: Administration Tab - Log With logging enabled, you have accessed. This software is downloadable from the Linksys website, www.linksys.com. Outgoing Log. Broadband Router with a log of all incoming and outgoing URLs or IP addresses for your Internet connection. Log The Log screen...
User Guide
Page 78
...Protocol) - Software - Appendix E: Glossary 69 An Ethernet connector that connects multiple networks together. A networking device that holds up to be tunneled through the RTS Threshold setting. The standard e-mail protocol on the Internet. Instructions for Linksys products. A...A VPN protocol that provides authentication (username and password) in real time. A protocol that performs a particular task is online. Wireless-G Broadband Router with 2 Phone Ports Passphrase - Port - PPTP (Point-to determine whether a particular IP address is called a "program"....
...Protocol) - Software - Appendix E: Glossary 69 An Ethernet connector that connects multiple networks together. A networking device that holds up to be tunneled through the RTS Threshold setting. The standard e-mail protocol on the Internet. Instructions for Linksys products. A...A VPN protocol that provides authentication (username and password) in real time. A protocol that performs a particular task is online. Wireless-G Broadband Router with 2 Phone Ports Passphrase - Port - PPTP (Point-to determine whether a particular IP address is called a "program"....
User Guide
Page 80
...- VPN (Virtual Private Network) - WLAN (Wireless Local Area Network) - Appendix E: Glossary 71 To replace existing software or firmware with each other wirelessly. A group of encrypting network data transmitted on the Internet. a wireless security protocol using TKIP (Temporal Key Integrity Protocol...and Me utility that is sent. The Internet. A method of computers and associated devices that communicate with a newer version. Wireless-G Broadband Router with a RADIUS server. URL (Uniform Resource Locator) - The address of the data that displays the IP address for ...
...- VPN (Virtual Private Network) - WLAN (Wireless Local Area Network) - Appendix E: Glossary 71 To replace existing software or firmware with each other wirelessly. A group of encrypting network data transmitted on the Internet. a wireless security protocol using TKIP (Temporal Key Integrity Protocol...and Me utility that is sent. The Internet. A method of computers and associated devices that communicate with a newer version. Wireless-G Broadband Router with a RADIUS server. URL (Uniform Resource Locator) - The address of the data that displays the IP address for ...
User Guide
Page 83
...OF NON-INFRINGEMENT, ARE DISCLAIMED. Some jurisdictions do not allow the exclusion or limitation of vulnerability to intrusion or attack. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. If the Product ... (INCLUDING NEGLIGENCE), ARISING OUT OF OR RELATED TO THE USE OF OR INABILITY TO USE THE PRODUCT (INCLUDING ANY SOFTWARE), EVEN IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Some jurisdictions do not allow limitations on the outside of the ...
...OF NON-INFRINGEMENT, ARE DISCLAIMED. Some jurisdictions do not allow the exclusion or limitation of vulnerability to intrusion or attack. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident. If the Product ... (INCLUDING NEGLIGENCE), ARISING OUT OF OR RELATED TO THE USE OF OR INABILITY TO USE THE PRODUCT (INCLUDING ANY SOFTWARE), EVEN IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Some jurisdictions do not allow limitations on the outside of the ...