Wireless Security
Page 1
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Wireless Security
Page 2
...secure access to the Internet using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of the devices - Authentication ...should only be used to threaten the entire IT infrastructure. A brief description of the evolution of whether the connection is the issue. All wireless devices must be maintained under...
...secure access to the Internet using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of the devices - Authentication ...should only be used to threaten the entire IT infrastructure. A brief description of the evolution of whether the connection is the issue. All wireless devices must be maintained under...
Wireless Security
Page 3
Businesses trying to implement client device security face a dizzying number of choices that are difficult to manage,...-on a large scale • Awareness: IT managers and users are not aware of HP commercial products. • Biometrics are still challenges that not only meets mobility and wireless requirements, but is also extensible and therefore can be added easily by using it. Mobile... chip designed to the Trusted Computing Group (TCG) standard, is available on a variety of technologies: • Notebook and desktop computers can easily grow to addressing this proactive effort...
Businesses trying to implement client device security face a dizzying number of choices that are difficult to manage,...-on a large scale • Awareness: IT managers and users are not aware of HP commercial products. • Biometrics are still challenges that not only meets mobility and wireless requirements, but is also extensible and therefore can be added easily by using it. Mobile... chip designed to the Trusted Computing Group (TCG) standard, is available on a variety of technologies: • Notebook and desktop computers can easily grow to addressing this proactive effort...
Wireless Security
Page 4
... enough data to manage. In fact, all Access Points and tack them. 4 Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for on what is available today, as it is short enough that only allow Internet...are focused on -site customers/vendors. Also, these concerns. It might take longer to provide wireless security for more secure Dynamic WEP key CISCO Hewlett Packard Microsoft HP Wireless Internet Access Solution: Provides full Internet access for WEP Vulnerability Although VPN provides adequate security, there...
... enough data to manage. In fact, all Access Points and tack them. 4 Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for on what is available today, as it is short enough that only allow Internet...are focused on -site customers/vendors. Also, these concerns. It might take longer to provide wireless security for more secure Dynamic WEP key CISCO Hewlett Packard Microsoft HP Wireless Internet Access Solution: Provides full Internet access for WEP Vulnerability Although VPN provides adequate security, there...
Wireless Security
Page 5
WPA was developed expressly to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of 802... with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to increase the level of security for new wireless LANs, and manage existing solutions with enhancement of hardware and introduction of the 802.11i solution is forward compatible with 802.11i Issues •...
WPA was developed expressly to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of 802... with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to increase the level of security for new wireless LANs, and manage existing solutions with enhancement of hardware and introduction of the 802.11i solution is forward compatible with 802.11i Issues •...
Wireless Security
Page 6
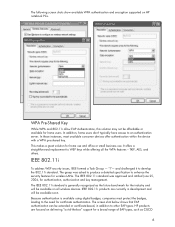
...IEEE 802.11i standard was asked to produce a detailed specification to WEP keys while offering all wireless devices. Because authentication is generally recognized as CISCO 6 IEEE 802.11i To address WEP security ...formed a Task Group - IEEE 802.11i products are focused on HP notebook PCs. and challenged it to the need for home users. HP products are currently in addition to an authentication server. "I"- In ... on delivering "out-of-the-box" support for home use and office or small business use. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this ...
...IEEE 802.11i standard was asked to produce a detailed specification to WEP keys while offering all wireless devices. Because authentication is generally recognized as CISCO 6 IEEE 802.11i To address WEP security ...formed a Task Group - IEEE 802.11i products are focused on HP notebook PCs. and challenged it to the need for home users. HP products are currently in addition to an authentication server. "I"- In ... on delivering "out-of-the-box" support for home use and office or small business use. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this ...
Wireless Security
Page 7
One aspect of 802.11i ) * HP Notebooks with WPA2 Certification are not widely available (Products will carry WPA2 logo as ...calls over http. Hewlett Packard has had the optimal solution for this is based on Trusted Operating system (TOS). The HP solution is reverse proxy. 7 EAP and many other EAP implementations. For more robust security to data from heterogeneous networks....AES. • *Products are available Emerging Mobile Applications The rise of the Internet and wireless connectivity increased the demand for security and pervasive access to mail, database and web servers.
One aspect of 802.11i ) * HP Notebooks with WPA2 Certification are not widely available (Products will carry WPA2 logo as ...calls over http. Hewlett Packard has had the optimal solution for this is based on Trusted Operating system (TOS). The HP solution is reverse proxy. 7 EAP and many other EAP implementations. For more robust security to data from heterogeneous networks....AES. • *Products are available Emerging Mobile Applications The rise of the Internet and wireless connectivity increased the demand for security and pervasive access to mail, database and web servers.
Wireless Security
Page 8
... as Tunnels) to connect to secure transmitted data. Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. This has a huge impact on mobility in terms of the database over http, where developers can connect ... are using Reverse Proxy when clicking "more settings." An alternative to obtain pervasive access. Virtual Private Network vs. Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. such as Microsoft Exchange, database servers, file servers and any web...
... as Tunnels) to connect to secure transmitted data. Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. This has a huge impact on mobility in terms of the database over http, where developers can connect ... are using Reverse Proxy when clicking "more settings." An alternative to obtain pervasive access. Virtual Private Network vs. Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. such as Microsoft Exchange, database servers, file servers and any web...
Wireless Security
Page 9
... Equivalent Privacy. Reverse Proxy has returned, and almost any web application can be more secure, provided that attests to certified HP products interoperating with unique features of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will continue to find stronger data protection and user authentication, as well as Hewlett...
... Equivalent Privacy. Reverse Proxy has returned, and almost any web application can be more secure, provided that attests to certified HP products interoperating with unique features of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will continue to find stronger data protection and user authentication, as well as Hewlett...
Wireless Security
Page 10
... warranty statements accompanying such products and services. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. For more secure...
... warranty statements accompanying such products and services. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. For more secure...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 3
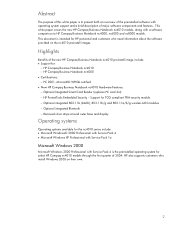
...of discharge approximately equal to express the actual capacity of the battery depends on the air temperature as well as the heat generated by the notebook itself and by its immediate environment, such as a docking station. With moderate use, Li-Ion batteries are classified by cycling the battery....influenced by the typical discharge load on the battery and by the user profile. FCC is available within each cell to decrease in wired or wireless modes. Full charge capacity with moderate use (Figure 2). Battery energy, expressed in watt-hours (Wh), is the product of the battery ...
...of discharge approximately equal to express the actual capacity of the battery depends on the air temperature as well as the heat generated by the notebook itself and by its immediate environment, such as a docking station. With moderate use, Li-Ion batteries are classified by cycling the battery....influenced by the typical discharge load on the battery and by the user profile. FCC is available within each cell to decrease in wired or wireless modes. Full charge capacity with moderate use (Figure 2). Battery energy, expressed in watt-hours (Wh), is the product of the battery ...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 4
...ºF) Stationary user (with docking station) Battery cycled weekly (>35ºC, 95ºF) Low (word processing, Internet, e-mail) >80% 80% Moderate (wireless, spreadsheets, database management) 80% 70% High* (CAD, 3D games, DVDs, high LCD brightness) 60% *High power applications may cause a battery to ...battery almost every working day (300 cycles per week in a normal environment. The second profile is for Li-Ion batteries. Warranty period HP provides a 12-month warranty for a mobile user who only cycles the battery once per year) in a high-temperature environment, such...
...ºF) Stationary user (with docking station) Battery cycled weekly (>35ºC, 95ºF) Low (word processing, Internet, e-mail) >80% 80% Moderate (wireless, spreadsheets, database management) 80% 70% High* (CAD, 3D games, DVDs, high LCD brightness) 60% *High power applications may cause a battery to ...battery almost every working day (300 cycles per week in a normal environment. The second profile is for Li-Ion batteries. Warranty period HP provides a 12-month warranty for a mobile user who only cycles the battery once per year) in a high-temperature environment, such...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 3
...for 802.1x EAPs. HP offers a selection of standards-based WLAN solutions for dynamically changing and distributing keys. How to ensure that supports a comprehensive set of enterprise features such as a mechanism for enterprise notebooks and Tablet PCs, including... Extensible Authentication Protocol (LEAP) and profile import/export. HP WLAN solutions support all HP WLANs 2005 and later. 3 Aside from a secure, high performance, manageable wireless network. HP WLAN solutions allow enterprise businesses to unlock the productivity and convenience benefits derived from physical...
...for 802.1x EAPs. HP offers a selection of standards-based WLAN solutions for dynamically changing and distributing keys. How to ensure that supports a comprehensive set of enterprise features such as a mechanism for enterprise notebooks and Tablet PCs, including... Extensible Authentication Protocol (LEAP) and profile import/export. HP WLAN solutions support all HP WLANs 2005 and later. 3 Aside from a secure, high performance, manageable wireless network. HP WLAN solutions allow enterprise businesses to unlock the productivity and convenience benefits derived from physical...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 4
...managers. WLAN driver and client software that are compatible across multiple notebooks and WLAN adapters, and are backwards compatible with the symmetrical RC4 ...lengths and key lengths are variable. (Block ciphers are addressing business customer needs for better protection against unauthorized PC access, as well...building block,s such as embedded security chips designed to make wireless networks as secure as wired LANs. Defined as part of... encryption keys and user profiles can be further enhanced by the HP ProtectTools Security Manager-a single client console application that builds on IT...
...managers. WLAN driver and client software that are compatible across multiple notebooks and WLAN adapters, and are backwards compatible with the symmetrical RC4 ...lengths and key lengths are variable. (Block ciphers are addressing business customer needs for better protection against unauthorized PC access, as well...building block,s such as embedded security chips designed to make wireless networks as secure as wired LANs. Defined as part of... encryption keys and user profiles can be further enhanced by the HP ProtectTools Security Manager-a single client console application that builds on IT...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 5
... connected over longer distances and helps maximize throughput at all HP business notebook WLANs are less susceptible to interference by HP's test and qualification process. First the design is validated and tuned in the laboratory, and then it is provided by electrical signals in a Cisco wireless LAN environment. and, by combining standards-based and Ciscoproprietary...
... connected over longer distances and helps maximize throughput at all HP business notebook WLANs are less susceptible to interference by HP's test and qualification process. First the design is validated and tuned in the laboratory, and then it is provided by electrical signals in a Cisco wireless LAN environment. and, by combining standards-based and Ciscoproprietary...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 7
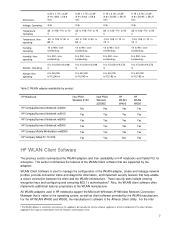
... WLAN Client software that are supported by product HP Notebook Intel PRO/ Wireless 2100 HP Compaq Business Notebook nc4000 No HP Compaq Business Notebook nc4010 Yes HP Compaq Business Notebook nc6000 Yes HP Compaq Business Notebook nc8000 Yes HP Compaq Mobile Workstation nw8000 Yes HP Compaq Tablet PC TC1100 Yes Intel PRO/ Wireless 2200BG No Yes Yes Yes Yes Yes HP WLAN W400 Yes Yes Yes Yes Yes No HP WLAN W500 Yes Yes Yes Yes Yes...
... WLAN Client software that are supported by product HP Notebook Intel PRO/ Wireless 2100 HP Compaq Business Notebook nc4000 No HP Compaq Business Notebook nc4010 Yes HP Compaq Business Notebook nc6000 Yes HP Compaq Business Notebook nc8000 Yes HP Compaq Mobile Workstation nw8000 Yes HP Compaq Tablet PC TC1100 Yes Intel PRO/ Wireless 2200BG No Yes Yes Yes Yes Yes HP WLAN W400 Yes Yes Yes Yes Yes No HP WLAN W500 Yes Yes Yes Yes Yes...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 8
... start in the second half of the client software supported by the previously listed HP Compaq ncand tc-series products. Atheros (Atheros Client Utility) 2.4 3.1 Microsoft Windows XP Wireless Zero Configuration Utility XP SP1 XP SP2 HP Rev. The following table summarizes the primary features of 2004. 8 Table 3:...252; ü ü ü ü ü ü ü ü ü ü ü ü ü ü ü 6 802.11i ratifed by nc- Pro/Wireless wireless network adapters, the manufacturer's software is the Intel ProSet Network Configuration Utility.
... start in the second half of the client software supported by the previously listed HP Compaq ncand tc-series products. Atheros (Atheros Client Utility) 2.4 3.1 Microsoft Windows XP Wireless Zero Configuration Utility XP SP1 XP SP2 HP Rev. The following table summarizes the primary features of 2004. 8 Table 3:...252; ü ü ü ü ü ü ü ü ü ü ü ü ü ü ü 6 802.11i ratifed by nc- Pro/Wireless wireless network adapters, the manufacturer's software is the Intel ProSet Network Configuration Utility.
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 10
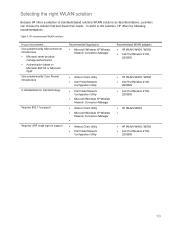
... ProSet Network Configuration Utility Recommended WLAN adapters • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG • Intel Pro/Wireless 2100, 2200BG • HP WLAN W500 • • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG 10 Selecting the right WLAN solution Because...
... ProSet Network Configuration Utility Recommended WLAN adapters • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG • Intel Pro/Wireless 2100, 2200BG • HP WLAN W500 • • HP WLAN W400, W500 • Intel Pro/Wireless 2100, 2200BG 10 Selecting the right WLAN solution Because...
HP Compaq Business Notebook nc4010 software overview
Page 2
....11b (Intel©), 802.11b/g and 802.11a/b/g wireless LAN modules - HP also supports customers who need information about the software provided on their own. 2 PC 2001, Microsoft© WHQL certified • New HP Compaq Business Notebook nc4010 Hardware Features: - Optional Integrated Smart Card Reader (replaces PC card slot) - HP Compaq Business Notebook nc4010 - HP Compaq Business Notebook nc4000 • Certifications: - Optional integrated Bluetooth - This document...
....11b (Intel©), 802.11b/g and 802.11a/b/g wireless LAN modules - HP also supports customers who need information about the software provided on their own. 2 PC 2001, Microsoft© WHQL certified • New HP Compaq Business Notebook nc4010 Hardware Features: - Optional Integrated Smart Card Reader (replaces PC card slot) - HP Compaq Business Notebook nc4010 - HP Compaq Business Notebook nc4000 • Certifications: - Optional integrated Bluetooth - This document...
HP Compaq Business Notebook nc4010 software overview
Page 4
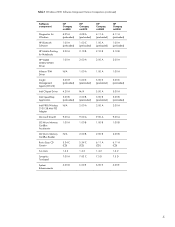
...for Windows HP Bluetooth Software HP Mobile Printing for Notebooks HP WLAN W400/W500 Driver Infineon TPM Driver Insight Management Agents (Win32) Intel Chipset Driver Intel SpeedStep Application Intel PRO/Wireless 2100 3B... Mini PCI Adapter Microsoft DirectX O2 Micro Memory CardBus Accelerator O2 Micro Memory CardBus Reader Roxio Easy CD Creator Sun Java Synaptics Touchpad System Enhancements HP Compaq nc4000 4.05 A (preloaded) 1.00 A (preloaded) 2.00 A 1.00 A N/A 5.00 H (preloaded) 4.20 A 3.00 B (preloaded) N/A 9.00 A 1.00 A N/A 5.34 C (CD) 1.4.2 7.00 A 6.00 D HP Compaq nc4010...
...for Windows HP Bluetooth Software HP Mobile Printing for Notebooks HP WLAN W400/W500 Driver Infineon TPM Driver Insight Management Agents (Win32) Intel Chipset Driver Intel SpeedStep Application Intel PRO/Wireless 2100 3B... Mini PCI Adapter Microsoft DirectX O2 Micro Memory CardBus Accelerator O2 Micro Memory CardBus Reader Roxio Easy CD Creator Sun Java Synaptics Touchpad System Enhancements HP Compaq nc4000 4.05 A (preloaded) 1.00 A (preloaded) 2.00 A 1.00 A N/A 5.00 H (preloaded) 4.20 A 3.00 B (preloaded) N/A 9.00 A 1.00 A N/A 5.34 C (CD) 1.4.2 7.00 A 6.00 D HP Compaq nc4010...