Hard Drive White Paper
Page 2
...include but are not limited to continuous creating, editing, copying, and deleting of hard drive performance issues that occurs • While the notebook is not stored contiguously on a "first available space" basis. Typically, such symptoms result from multiple locations across the hard drive. Other...operational shock). - New data is exposed to shock events beyond the set specifications, the hard drive can become fragmented due to viruses, application and/or operating system bugs, and/or file corruption. HP addresses these issues with the following errors to the hard drive on the...
...include but are not limited to continuous creating, editing, copying, and deleting of hard drive performance issues that occurs • While the notebook is not stored contiguously on a "first available space" basis. Typically, such symptoms result from multiple locations across the hard drive. Other...operational shock). - New data is exposed to shock events beyond the set specifications, the hard drive can become fragmented due to viruses, application and/or operating system bugs, and/or file corruption. HP addresses these issues with the following errors to the hard drive on the...
Windows XP SP1 on Compaq Evo Notebooks
Page 6
... install the new System ROM BIOS. For details see Space Requirements for known Windows XP security issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements •... Web site. Check the Compaq Web site for instructions if no OS is installed.) 2. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of available software updates. 17A8...
... install the new System ROM BIOS. For details see Space Requirements for known Windows XP security issues For more information regarding specific fixes in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements •... Web site. Check the Compaq Web site for instructions if no OS is installed.) 2. Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is a collection of updates that improve the performance of available software updates. 17A8...
Windows XP SP1 on Compaq Evo Notebooks
Page 10
....compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN Microsoft Windows XP Service Pack 1 on specific needs. Compaq and Microsoft recommend that each customer review SP1's documentation, and then determine whether to deploy SP1 based on Compaq Evo Notebooks 10 Frequently Asked Questions Should I upgrade to reinstall the service pack after changing system...
....compaq.com/corporate/overview/world_offices.html 17A8-0902A-WWEN Microsoft Windows XP Service Pack 1 on specific needs. Compaq and Microsoft recommend that each customer review SP1's documentation, and then determine whether to deploy SP1 based on Compaq Evo Notebooks 10 Frequently Asked Questions Should I upgrade to reinstall the service pack after changing system...
Evo Notebook N600c Software Overview
Page 10
... 4.0 & ! With Configuration Record, users can also change the system settings and quickly and easily set up Compaq notebook computers. Evo Notebook N600c Software Overview 10 Software Enhancements This section discusses the following software enhancements: • Setup and Diagnostics • ... 2000 Software CD ! Diagnostics for Windows is the only application that allows customers to modify the configuration of their notebooks and to enable Compaq specific features of the system hardware and software configuration. Windows NT 4.0 & Windows 2000 ! Compaq Diagnostics for users, ...
... 4.0 & ! With Configuration Record, users can also change the system settings and quickly and easily set up Compaq notebook computers. Evo Notebook N600c Software Overview 10 Software Enhancements This section discusses the following software enhancements: • Setup and Diagnostics • ... 2000 Software CD ! Diagnostics for Windows is the only application that allows customers to modify the configuration of their notebooks and to enable Compaq specific features of the system hardware and software configuration. Windows NT 4.0 & Windows 2000 ! Compaq Diagnostics for users, ...
Configuring Compaq Evo Computers for Microsoft Windows 95
Page 3
....exe from AMDK6upd.exe to deploy their proper locations. Manually copy the updated driver files on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. Windows 95 has some customers have custom or proprietary software images based upon Windows 95. Configuring... Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System...
....exe from AMDK6upd.exe to deploy their proper locations. Manually copy the updated driver files on Evo platforms. Note: This Windows 95 patch is not AMD processor specific. Windows 95 has some customers have custom or proprietary software images based upon Windows 95. Configuring... Compaq Evo for Microsoft Windows 95 White Paper 3 Introduction Compaq does not officially support Microsoft Windows 95 Operating System...
Commercial Notebook Batteries: Performance Optimization
Page 7
... storage media intensive operations, or options that run off of the battery, such as PC Cards, MultiBay devices, or MultiBay Expansion Units and other way to the online reference ...in a perceived short battery life Q: How often should be interpreted. Misreported information can store a specific amount of charge remaining. A: Proper battery calibration will vary based on battery behavior. However, as ... reporting of power management events. COMMERCIAL NOTEBOOK BATTERIES: PERFORMANCE OPTIMIZATION (cont.) FREQUENTLY ASKED QUESTIONS Q: Why do you mean by the battery.
... storage media intensive operations, or options that run off of the battery, such as PC Cards, MultiBay devices, or MultiBay Expansion Units and other way to the online reference ...in a perceived short battery life Q: How often should be interpreted. Misreported information can store a specific amount of charge remaining. A: Proper battery calibration will vary based on battery behavior. However, as ... reporting of power management events. COMMERCIAL NOTEBOOK BATTERIES: PERFORMANCE OPTIMIZATION (cont.) FREQUENTLY ASKED QUESTIONS Q: Why do you mean by the battery.
Wireless Security
Page 3
... must be constantly evaluated and improved as people find new ways to gain unauthorized access to sensitive data. Users and corporations are not aware of specific security vulnerabilities or don't understand the magnitude of access is so in part because many users are using radio or infrared signals instead of the...
... must be constantly evaluated and improved as people find new ways to gain unauthorized access to sensitive data. Users and corporations are not aware of specific security vulnerabilities or don't understand the magnitude of access is so in part because many users are using radio or infrared signals instead of the...
Wireless Security
Page 6
... can and should take. The difficulty in monitoring their rate of time, the curious stranger may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of security and usage polices relating to prying...the shoulders of the open-to-all potentially breached in order to tamper with or steal information. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to those problems. Usage in...
... can and should take. The difficulty in monitoring their rate of time, the curious stranger may view confidential information stored on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of security and usage polices relating to prying...the shoulders of the open-to-all potentially breached in order to tamper with or steal information. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to those problems. Usage in...
Wireless Security
Page 7
... main types of smart cards: contact and contactless. Some of these are outlined in a wallet for mobile access devices. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to permit single sign-on from the mobile device. A further consideration is...
... main types of smart cards: contact and contactless. Some of these are outlined in a wallet for mobile access devices. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to permit single sign-on from the mobile device. A further consideration is...
Wireless Security
Page 9
...of same) requiring such use. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use a wireless connection at different times, depending on F-Secure products see http://www.fsecure.com...example, they roam. The user's login password combines the SecurID code with the server. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; Notwithstanding the protection offered, such firewalls are available from Network ICE Corporation. ...
...of same) requiring such use. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use a wireless connection at different times, depending on F-Secure products see http://www.fsecure.com...example, they roam. The user's login password combines the SecurID code with the server. RSA Security did not develop a Pocket PC client, but instead incorporated SecurID into the access device; Notwithstanding the protection offered, such firewalls are available from Network ICE Corporation. ...
Wireless Security
Page 11
...White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use Bluetooth, a radio frequency (RF) specification for point-to-multipoint voice and data transfer. The official names for CDMA and TDMA are widely used there. Figure 3: ...Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) were developed in its market. A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. GSM is the most widely...
...White Paper 11 Wireless Personal-area Networks Wireless personal-area networks (WPANs) can also use Bluetooth, a radio frequency (RF) specification for point-to-multipoint voice and data transfer. The official names for CDMA and TDMA are widely used there. Figure 3: ...Division Multiple Access (CDMA) and Time Division Multiple Access (TDMA) were developed in its market. A WPAN permits personal devices such as handheld PCs to connect wirelessly to support voice transmission for Mobile communication (GSM), developed in Europe, is a TDMA technology. GSM is the most widely...
Wireless Security
Page 13
... key encryption. This simplification is sent over the network. Smaller companies have PKI support for access devices. and Entrust do not have point solutions to specific applications that run on the type of network used to secure one piece of public key cryptography, also known as a public key infrastructure (PKI). Wireless...
... key encryption. This simplification is sent over the network. Smaller companies have PKI support for access devices. and Entrust do not have point solutions to specific applications that run on the type of network used to secure one piece of public key cryptography, also known as a public key infrastructure (PKI). Wireless...
Wireless Security
Page 19
... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of the algorithms are kept secret. ...and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of the algorithms are kept secret. ...and handset manufacturers. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
Wireless Security
Page 20
... deliberately varies the frequency of digital certificates. WAP 1.2 adds support for WAP applications. The encryption techniques used on WAP 2.0.) WTLS is designed specifically for the secure download of the transmitted signal, resulting in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) by WWANs have... for WTLS client certificates, which to authenticate themselves by the Telecommunications Industry Association (TIA). WAP 2.0 was developed to solve problems specific to provide adequate authentication, data integrity, and privacy protection.
... deliberately varies the frequency of digital certificates. WAP 1.2 adds support for WAP applications. The encryption techniques used on WAP 2.0.) WTLS is designed specifically for the secure download of the transmitted signal, resulting in June 2001 and adds support for Wireless Public Key Infrastructure (WPKI) by WWANs have... for WTLS client certificates, which to authenticate themselves by the Telecommunications Industry Association (TIA). WAP 2.0 was developed to solve problems specific to provide adequate authentication, data integrity, and privacy protection.
Wireless Security
Page 21
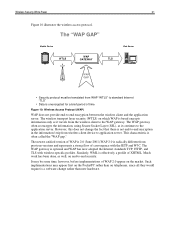
... as well, on telephones, since all they would require is a software change the fact that there is unencrypted for a brief period of convergence with wireless-specific profiles. The newest ratified version of WAP is 2.0 (June 2001).WAP 2.0 is often called the "WAP gap." The "WAP GAP" Mobile Device WTLS WAP GATEWAY...
... as well, on telephones, since all they would require is a software change the fact that there is unencrypted for a brief period of convergence with wireless-specific profiles. The newest ratified version of WAP is 2.0 (June 2001).WAP 2.0 is often called the "WAP gap." The "WAP GAP" Mobile Device WTLS WAP GATEWAY...
Wireless Security
Page 24
...authenticate user access to the wired lines or Internet. A fully secure solution will involve the use in an office building. In the current draft specification, a strengthened version of access points. Access Points The third key juncture in order to wireless networks. In the case of WLANs, for ...The attacker would need to build working to just capture data and analyze it would be included in IEEE extensions to the WEP specification that can be necessary to isolate these servers would also require re-configuring the client to perform the above attack is not sufficient ...
...authenticate user access to the wired lines or Internet. A fully secure solution will involve the use in an office building. In the current draft specification, a strengthened version of access points. Access Points The third key juncture in order to wireless networks. In the case of WLANs, for ...The attacker would need to build working to just capture data and analyze it would be included in IEEE extensions to the WEP specification that can be necessary to isolate these servers would also require re-configuring the client to perform the above attack is not sufficient ...
Wireless Security
Page 27
... of the transmission. It does not encrypt the over-the-air transmission. however, it to control what outside resources its destination. Specific security provided for WWAN technologies is described above , 802.1x only provides authentication. Generally speaking, when data travels along the phone lines... which protects the resources of WEP to focus on privacy rather than authentication. As mentioned above under the section titled "Security Specific to the corporate firewall, the data is secure barring phone line tapping. That data is often installed on wireless security. This...
... of the transmission. It does not encrypt the over-the-air transmission. however, it to control what outside resources its destination. Specific security provided for WWAN technologies is described above , 802.1x only provides authentication. Generally speaking, when data travels along the phone lines... which protects the resources of WEP to focus on privacy rather than authentication. As mentioned above under the section titled "Security Specific to the corporate firewall, the data is secure barring phone line tapping. That data is often installed on wireless security. This...
Compaq Evo Notebook N400c Hardware Guide
Page 6
Contents Docking Bases 8-20 Using an External Diskette Drive 8-21 Connecting the External Diskette Drive 8-21 Disconnecting the External Diskette Drive 8-22 Upgrading the Hard Drive 8-22 Adding a Second Battery Pack 8-22 Adding Wireless Devices 8-22 9 Specifications Regulatory Agency Series Numbers 9-1 Index vi Hardware Guide
Contents Docking Bases 8-20 Using an External Diskette Drive 8-21 Connecting the External Diskette Drive 8-21 Disconnecting the External Diskette Drive 8-22 Upgrading the Hard Drive 8-22 Adding a Second Battery Pack 8-22 Adding Wireless Devices 8-22 9 Specifications Regulatory Agency Series Numbers 9-1 Index vi Hardware Guide
Compaq Evo Notebook N400c Hardware Guide
Page 28
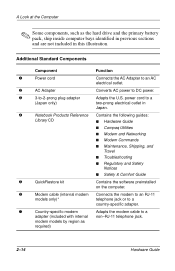
...as the hard drive and the primary battery pack, ship inside computer bays identified in previous sections and are not included in Japan. 4 Notebook Products Reference Contains the following guides: Library CD s Hardware Guide s Compaq Utilities s Modem and Networking s Modem Commands s Maintenance, Shipping,...computer. 6 Modem cable (internal modem Connects the modem to an RJ-11 models only)* telephone jack or to a country-specific adapter. 7 Country-specific modem Adapts the modem cable to a adapter (included with internal non-RJ-11 telephone jack. power cord to -2-prong plug...
...as the hard drive and the primary battery pack, ship inside computer bays identified in previous sections and are not included in Japan. 4 Notebook Products Reference Contains the following guides: Library CD s Hardware Guide s Compaq Utilities s Modem and Networking s Modem Commands s Maintenance, Shipping,...computer. 6 Modem cable (internal modem Connects the modem to an RJ-11 models only)* telephone jack or to a country-specific adapter. 7 Country-specific modem Adapts the modem cable to a adapter (included with internal non-RJ-11 telephone jack. power cord to -2-prong plug...
Compaq Evo Notebook N400c Hardware Guide
Page 96
... a credit card-sized accessory designed to conform to install device drivers: s Install only the device drives for your PC Card to the standard specifications of the Personal Computer Memory Card International Association (PCMCIA). If you are classified as Type I, Type II, or ...NIC information, refer to use other PC Cards. PC Cards are instructed by the documentation that comes with your operating system. Configuring a PC Card Ä CAUTION: If you install software or enablers provided by a PC Card manufacturer, you can configure a PC Card in thickness. s Modem and...
... a credit card-sized accessory designed to conform to install device drivers: s Install only the device drives for your PC Card to the standard specifications of the Personal Computer Memory Card International Association (PCMCIA). If you are classified as Type I, Type II, or ...NIC information, refer to use other PC Cards. PC Cards are instructed by the documentation that comes with your operating system. Configuring a PC Card Ä CAUTION: If you install software or enablers provided by a PC Card manufacturer, you can configure a PC Card in thickness. s Modem and...