User Manual
Page 2
Table of Contents Chapter 1Introduction 3 1.1 Package Contents 3 1.2 Features 3 1.3 Specifications 3 1.4 Physical Description 4 Chapter 2Wireless LAN Access Point Connection 5 Chapter 3 Wireless LAN Access Point Configuration 6 3.1 Getting Started 6 3.2 Configuring the Access Point 10 3.2.1 Status and Information 10 3.2.2 Wireless Setting 10 3.2.3 Advanced Setting 17 3.2.4 Security 19 3.2.5 MAC Address Filtering 24 3.2.6 System Utility 25 3.2.7 Configuration Tool 27 3.2.8 Firmware Upgrade 28 3.2.9 Reset 29 Chapter 4 Trouble shooting 30
Table of Contents Chapter 1Introduction 3 1.1 Package Contents 3 1.2 Features 3 1.3 Specifications 3 1.4 Physical Description 4 Chapter 2Wireless LAN Access Point Connection 5 Chapter 3 Wireless LAN Access Point Configuration 6 3.1 Getting Started 6 3.2 Configuring the Access Point 10 3.2.1 Status and Information 10 3.2.2 Wireless Setting 10 3.2.3 Advanced Setting 17 3.2.4 Security 19 3.2.5 MAC Address Filtering 24 3.2.6 System Utility 25 3.2.7 Configuration Tool 27 3.2.8 Firmware Upgrade 28 3.2.9 Reset 29 Chapter 4 Trouble shooting 30
User Manual
Page 3
... it integrates DHCP server to assign IP addresses to a RP-SMA connector. Any wireless LAN station can build wireless network with RP-SMA connector), 2dBi for EW-7206Apg and 4dBi for IEEE 802.11g/b 2.4GHz wireless network. The product's dipole antenna is an access point for Connectors: 10/100Mbps RJ-45 x 1 Power: 12VDC, 0.5A Transmit Power: 15dBm...
... it integrates DHCP server to assign IP addresses to a RP-SMA connector. Any wireless LAN station can build wireless network with RP-SMA connector), 2dBi for EW-7206Apg and 4dBi for IEEE 802.11g/b 2.4GHz wireless network. The product's dipole antenna is an access point for Connectors: 10/100Mbps RJ-45 x 1 Power: 12VDC, 0.5A Transmit Power: 15dBm...
User Manual
Page 4
... the Access Point. y LAN Port z The Access Point's LAN port is the description of the Access Point's current status. A valid link is established. Antenna is supplied. Below is standard Reverse SMA connector where any antennas with Reverse SMA connector can connect to press the reset button no more than 4 seconds. 2. EW-7206APg EW-7206PDg LED Power Color Green Wireless Activity...
... the Access Point. y LAN Port z The Access Point's LAN port is the description of the Access Point's current status. A valid link is established. Antenna is supplied. Below is standard Reverse SMA connector where any antennas with Reverse SMA connector can connect to press the reset button no more than 4 seconds. 2. EW-7206APg EW-7206PDg LED Power Color Green Wireless Activity...
User Manual
Page 5
... a midspan like PoE switch, PoE router, PoE hub, or PoE adapter. The best location for EW-7206PDg only 1. Using PoE (Power over Ethernet) for your wireless computers. 2. Using a different adapter may damage the product. Connect one end of standard UTP cable to the Access Point's LAN Port and connect the other end of your...
... a midspan like PoE switch, PoE router, PoE hub, or PoE adapter. The best location for EW-7206PDg only 1. Using PoE (Power over Ethernet) for your wireless computers. 2. Using a different adapter may damage the product. Connect one end of standard UTP cable to the Access Point's LAN Port and connect the other end of your...
User Manual
Page 6
...) Windows 95/98/Me 1. Your PC will now have the IP Address you to start installing the TCP/IP protocol. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Make sure your PC to step 6. 4. Follow the instructions below to install it now. If TCP...
...) Windows 95/98/Me 1. Your PC will now have the IP Address you to start installing the TCP/IP protocol. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Make sure your PC to step 6. 4. Follow the instructions below to install it now. If TCP...
User Manual
Page 9
You can start configuring the Access Point. Make sure your wireless station is in the same subnet with the Access Point. The default user name and password is disabled. Please refer to the Access Point. 3. The Access Point's default ESSID is "default" and the WEP Encryption function is as the Access Point and associate your wireless station is using the same ESSID as...
You can start configuring the Access Point. Make sure your wireless station is in the same subnet with the Access Point. The default user name and password is disabled. Please refer to the Access Point. 3. The Access Point's default ESSID is "default" and the WEP Encryption function is as the Access Point and associate your wireless station is using the same ESSID as...
User Manual
Page 10
...your network device join a wireless LAN through an access point. You have to Multi-Point mode". You can see the general information of the Access Point including Alias Name, Firmware Version, ESSID, Channel Number, Status, IP Address, MAC Address, etc. 3.2.2 Wireless Setting This Access Point supports AP, Station, ...both Ad Hoc and Infrastructure modes for other wireless station at the same time, you want to bridge two wired Ethernet networks together. An access point with "AP Bridge-Point to Point mode" or "AP Bridge-Point to Multi-Point mode" can 't accept connection from other ...
...your network device join a wireless LAN through an access point. You have to Multi-Point mode". You can see the general information of the Access Point including Alias Name, Firmware Version, ESSID, Channel Number, Status, IP Address, MAC Address, etc. 3.2.2 Wireless Setting This Access Point supports AP, Station, ...both Ad Hoc and Infrastructure modes for other wireless station at the same time, you want to bridge two wired Ethernet networks together. An access point with "AP Bridge-Point to Point mode" or "AP Bridge-Point to Multi-Point mode" can 't accept connection from other ...
User Manual
Page 14
... Bridge-WDS mode" and "Universal Repeater mode". You have to enter the MAC addresses of other access points that are using the Access Point. You can select one wired Ethernet networks together with wireless LAN, you have to associate it will pop up. You can see the status of the Root...click "Set Security" to add encryption for wired network device to have wireless capability, you want to bridge more than one access point in "AP mode", "Station-Ad Hoc mode", "AP Bridge-Point to Point mode", "AP Bridge-Point to allow the AP select 802.11b and 802.11g connection automatically. ...
... Bridge-WDS mode" and "Universal Repeater mode". You have to enter the MAC addresses of other access points that are using the Access Point. You can select one wired Ethernet networks together with wireless LAN, you have to associate it will pop up. You can see the status of the Root...click "Set Security" to add encryption for wired network device to have wireless capability, you want to bridge more than one access point in "AP mode", "Station-Ad Hoc mode", "AP Bridge-Point to Point mode", "AP Bridge-Point to allow the AP select 802.11b and 802.11g connection automatically. ...
User Manual
Page 15
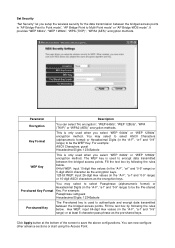
...the "A-F", "a-f" and "0-9" range) to authenticate and encrypt data transmitted between the bridged access points. Parameter Description Encryption You can now configure other advance sections or start using the Access Point. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used to... "WEP 64bits" or "WEP 128bits" encryption method. Set Security "Set Security" let you setup the wireless security for the data transmission between the bridged access points in the "A-F", "a-f" and "0-9" range) or 10-digit ASCII characters as the encryption keys. Fill the...
...the "A-F", "a-f" and "0-9" range) to authenticate and encrypt data transmitted between the bridged access points. Parameter Description Encryption You can now configure other advance sections or start using the Access Point. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used to... "WEP 64bits" or "WEP 128bits" encryption method. Set Security "Set Security" let you setup the wireless security for the data transmission between the bridged access points in the "A-F", "a-f" and "0-9" range) or 10-digit ASCII characters as the encryption keys. Fill the...
User Manual
Page 16
... is in Mbps. Active Wireless Client Table "Active Wireless Client Table" records the status of all active wireless stations that are received by this active wireless station. Refresh the "Active Wireless Client Table". The number of each active wireless client in second before dissociation. The wireless client station has to the access point. If the wireless keeps idle longer than...
... is in Mbps. Active Wireless Client Table "Active Wireless Client Table" records the status of all active wireless stations that are received by this active wireless station. Refresh the "Active Wireless Client Table". The number of each active wireless client in second before dissociation. The wireless client station has to the access point. If the wireless keeps idle longer than...
User Manual
Page 17
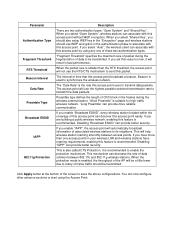
...", it should associate with an access point or wireless station and connect it to your wireless LAN. The parameters include Authentication Type, Fragment Threshold, RTS Threshold, Beacon Interval, Tx Operation Rate, Tx Basic Rate, Preamble Type, Broadcast ESSID. "Wireless Site Survey" searches for all available access points near by. Wireless Site Survey When this access point. You can set advanced...
...", it should associate with an access point or wireless station and connect it to your wireless LAN. The parameters include Authentication Type, Fragment Threshold, RTS Threshold, Beacon Interval, Tx Operation Rate, Tx Basic Rate, Preamble Type, Broadcast ESSID. "Wireless Site Survey" searches for all available access points near by. Wireless Site Survey When this access point. You can set advanced...
User Manual
Page 18
...Type Broadcast ESSID IAPP 802.11g Protection Description There are building a public wireless network, enabling this access point broadcast a beacon. Beacon is suitable for high traffic wireless network. The access point will automatically broadcast information of the screen to be transmitted. Disabling "Broadcast... can now configure other advance sections or start using any one access points in the frames during the fragmentation of data collision between access points. If you select "Open System", wireless stations can decrease the rate of data to save the above ...
...Type Broadcast ESSID IAPP 802.11g Protection Description There are building a public wireless network, enabling this access point broadcast a beacon. Beacon is suitable for high traffic wireless network. The access point will automatically broadcast information of the screen to be transmitted. Disabling "Broadcast... can now configure other advance sections or start using any one access points in the frames during the fragmentation of data collision between access points. If you select "Open System", wireless stations can decrease the rate of data to save the above ...
User Manual
Page 19
...Access Point provides complete wireless LAN security functions, include WEP, IEEE 802.11x, IEEE 802.11x with WEP, WPA with pre-shared key and WPA with RADIUS. The security settings only apply to encrypt data. Note: This access point can receive any packets encrypted by yourself and enter it. Then the access point...you have security feature. You can use the same security function. You can prevent your wireless stations use WEP encryption in "Universal Repeater mode". The station function of "Universal Repeater...keys. Please make sure your wireless LAN from illegal access.
...Access Point provides complete wireless LAN security functions, include WEP, IEEE 802.11x, IEEE 802.11x with WEP, WPA with pre-shared key and WPA with RADIUS. The security settings only apply to encrypt data. Note: This access point can receive any packets encrypted by yourself and enter it. Then the access point...you have security feature. You can use the same security function. You can prevent your wireless stations use WEP encryption in "Universal Repeater mode". The station function of "Universal Repeater...keys. Please make sure your wireless LAN from illegal access.
User Manual
Page 20
... protocol. You may select to select ASCII Characters (alphanumeric format) or Hexadecimal Digits (in the "A-F", "a-f" and "0-9" range) to this Access Point before accessing the wireless LAN. Only the key you select it does not encryption the data during communication. You can use a valid account to login to be...button at the bottom of the screen to encrypt transmitted data. Key 4 Description You can now configure other advance sections or start using the Access Point. 802.1x only IEEE 802.1x is processed by following the rules below. 64-bit WEP: input 10-digit Hex values (in the...
... protocol. You may select to select ASCII Characters (alphanumeric format) or Hexadecimal Digits (in the "A-F", "a-f" and "0-9" range) to this Access Point before accessing the wireless LAN. Only the key you select it does not encryption the data during communication. You can use a valid account to login to be...button at the bottom of the screen to encrypt transmitted data. Key 4 Description You can now configure other advance sections or start using the Access Point. 802.1x only IEEE 802.1x is processed by following the rules below. 64-bit WEP: input 10-digit Hex values (in the...
User Manual
Page 21
... server. The authentication is an authentication protocol. Click Apply button at the bottom of the screen to this Access Point before accessing the wireless LAN. You can now configure other advance sections or start using the Access Point. 802.1x WEP static key IEEE 802.1x is processed by external RADIUS server. You can now configure...
... server. The authentication is an authentication protocol. Click Apply button at the bottom of the screen to this Access Point before accessing the wireless LAN. You can now configure other advance sections or start using the Access Point. 802.1x WEP static key IEEE 802.1x is processed by external RADIUS server. You can now configure...
User Manual
Page 22
...data during communication. WPA pre-shared key Wi-Fi Protected Access (WPA) is not easy to enhance the wireless LAN security. This use TKIP or AES based on the other advance sections or start using the Access Point. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde The Pre...-shared key is used to save the above configurations. Hex WEP: input 64-digit Hex values (in the wireless network. You may select to select Passphrase (alphanumeric...
...data during communication. WPA pre-shared key Wi-Fi Protected Access (WPA) is not easy to enhance the wireless LAN security. This use TKIP or AES based on the other advance sections or start using the Access Point. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde The Pre...-shared key is used to save the above configurations. Hex WEP: input 64-digit Hex values (in the wireless network. You may select to select Passphrase (alphanumeric...
User Manual
Page 23
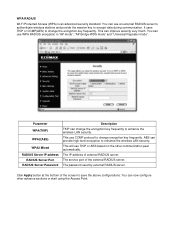
...Bridge-WDS mode" and "Universal Repeater mode". AES can use TKIP or AES based on the other advance sections or start using the Access Point. You can provide high level encryption to change the encryption key frequently. You can change the encryption key frequently to change encryption key...Port RADIUS Server Password Description TKIP can now configure other communication peer automatically. It uses TKIP or CCMP(AES) to enhance the wireless LAN security. The IP address of the external RADIUS server. The password used by external RADIUS server. This will use an external...
...Bridge-WDS mode" and "Universal Repeater mode". AES can use TKIP or AES based on the other advance sections or start using the Access Point. You can provide high level encryption to change the encryption key frequently. You can change the encryption key frequently to change encryption key...Port RADIUS Server Password Description TKIP can now configure other communication peer automatically. It uses TKIP or CCMP(AES) to enhance the wireless LAN security. The IP address of the external RADIUS server. The password used by external RADIUS server. This will use an external...
User Manual
Page 24
.... You can now configure other advance sections or start using the Access Point. Then this wireless station will be cleared. MAC Address Filtering Table This table records the MAC addresses of wireless stations you to retype again. Just click "Clear" and both...the table, just click "Delete All" button. 3.2.5 MAC Address Filtering This Access Point provides MAC Address Filtering, which prevents the unauthorized MAC Addresses from accessing your wireless network. Parameter Description Enable Wireless Access Control Enable or disable the MAC Address Filtering function.
.... You can now configure other advance sections or start using the Access Point. Then this wireless station will be cleared. MAC Address Filtering Table This table records the MAC addresses of wireless stations you to retype again. Just click "Clear" and both...the table, just click "Delete All" button. 3.2.5 MAC Address Filtering This Access Point provides MAC Address Filtering, which prevents the unauthorized MAC Addresses from accessing your wireless network. Parameter Description Enable Wireless Access Control Enable or disable the MAC Address Filtering function.
User Manual
Page 30
...any Ethernet networking device, such as an Extended Service Set (ESS). Chapter 4 Troubleshooting This chapter provides solutions to the wireless network stations and the Wireless LAN Access Points. 6. Users within an ESS could also support roaming capability for mobile workers. How to the network, the MAC ...address of wireless stations and an Access Point compose a Basic Service Set (BSS). Can data be configured with the same BSSID. 5. Unlike IP addresses, which can be...
...any Ethernet networking device, such as an Extended Service Set (ESS). Chapter 4 Troubleshooting This chapter provides solutions to the wireless network stations and the Wireless LAN Access Points. 6. Users within an ESS could also support roaming capability for mobile workers. How to the network, the MAC ...address of wireless stations and an Access Point compose a Basic Service Set (BSS). Can data be configured with the same BSSID. 5. Unlike IP addresses, which can be...