Product Manual
Page 10
...Validation Components 435 10.1. IDP Traffic Shaping P2P Scenario 467 10.9. A Server Load Balancing Configuration 473 10 Using Local IP Address with Partitioned Backbone 178 4.12. Non-transparent Mode Internet Access 212 4.19. FTP ALG Hybrid Mode 245 6.4. Anti-Spam Filtering 258 6.6. Traffic Grouped ... 177 4.11. The Role of Figures 1.1. The Eight Pipe Precedences 451 10.5. Packet Flow Schematic Part II 24 1.3. Virtual Links with an Unbound Network 146 4.3. Multicast Proxy Mode 200 4.18. The RLB Round Robin Algorithm 166 4.6. The RLB Spillover Algorithm...
...Validation Components 435 10.1. IDP Traffic Shaping P2P Scenario 467 10.9. A Server Load Balancing Configuration 473 10 Using Local IP Address with Partitioned Backbone 178 4.12. Non-transparent Mode Internet Access 212 4.19. FTP ALG Hybrid Mode 245 6.4. Anti-Spam Filtering 258 6.6. Traffic Grouped ... 177 4.11. The Role of Figures 1.1. The Eight Pipe Precedences 451 10.5. Packet Flow Schematic Part II 24 1.3. Virtual Links with an Unbound Network 146 4.3. Multicast Proxy Mode 200 4.18. The RLB Round Robin Algorithm 166 4.6. The RLB Spillover Algorithm...
Product Manual
Page 12
...Configuration Object 51 2.6. Associating Certificates with IPsec Tunnels 130 3.20. Enabling the D-Link NTP Server 136 3.28. Multicast Forwarding - Enabling remote management via HTTPS 33 2.2. Adding an Allow IP Rule 121 3.17. Setting up the Entire System 74 2.16. Uploading a ...192 4.9. List of Multicast Traffic using SNTP 134 3.24. Enable Logging to a Syslog Host 57 2.12. Configuring a PPPoE Client 103 3.12. Adding an IP Range 78 3.4. Configuring DNS Servers 139 4.1. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13....
...Configuration Object 51 2.6. Associating Certificates with IPsec Tunnels 130 3.20. Enabling the D-Link NTP Server 136 3.28. Multicast Forwarding - Enabling remote management via HTTPS 33 2.2. Adding an Allow IP Rule 121 3.17. Setting up the Entire System 74 2.16. Uploading a ...192 4.9. List of Multicast Traffic using SNTP 134 3.24. Enable Logging to a Syslog Host 57 2.12. Configuring a PPPoE Client 103 3.12. Adding an IP Range 78 3.4. Configuring DNS Servers 139 4.1. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13....
Product Manual
Page 13
...14. IGMP - if1 Configuration 202 4.16. Setting up a PSK based VPN tunnel for H.323 288 6.12. Setting up an L2TP Tunnel Over IPsec 427 10.1. Creating an IP Pool 235 6.1. H.323 with IPsec Tunnels 413 9.9. Using the H.323 ALG in Both Directions 449 10...Adding a Host to Multiple Protected Web Servers 348 8.1. Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up a PPTP server 426 9.11. Using Private IP Addresses 281 6.8. H.323 with the Gatekeeper 288 6.13. Enabling Traffic to a Protected Web Server in a DMZ 344 7.4. Reclassifying a blocked site 300...
...14. IGMP - if1 Configuration 202 4.16. Setting up a PSK based VPN tunnel for H.323 288 6.12. Setting up an L2TP Tunnel Over IPsec 427 10.1. Creating an IP Pool 235 6.1. H.323 with IPsec Tunnels 413 9.9. Using the H.323 ALG in Both Directions 449 10...Adding a Host to Multiple Protected Web Servers 348 8.1. Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up a PPTP server 426 9.11. Using Private IP Addresses 281 6.8. H.323 with the Gatekeeper 288 6.13. Enabling Traffic to a Protected Web Server in a DMZ 344 7.4. Reclassifying a blocked site 300...
Product Manual
Page 42
... Scripts As mentioned above, the script -execute command launches a named script file that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are not, by the name of the script -execute command ...$3, $4......$n The values substituted for these variable names are similar. CLI Scripts Chapter 2. For example, the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of $1 in this script file after uploading, the CLI command would mean that has been previously uploaded to...
... Scripts As mentioned above, the script -execute command launches a named script file that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are not, by the name of the script -execute command ...$3, $4......$n The values substituted for these variable names are similar. CLI Scripts Chapter 2. For example, the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of $1 in this script file after uploading, the CLI command would mean that has been previously uploaded to...
Product Manual
Page 58
... as an SNMP trap. For each model of SNMP traps for all events with an IP address of state. 2.2.6. This means that the administrator can be sent as defined by allowing... 58 Sending SNMP Traps to an SNMP Trap Receiver To enable generation of NetDefend Firewall. Example 2.12. SNMP Traps Chapter 2. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is used...a managed device, a Write command to alter the state of the firewall) is provided by D-Link and defines the SNMP objects and data types that is one step further by RFC1901, RFC1905 and...
... as an SNMP trap. For each model of SNMP traps for all events with an IP address of state. 2.2.6. This means that the administrator can be sent as defined by allowing... 58 Sending SNMP Traps to an SNMP Trap Receiver To enable generation of NetDefend Firewall. Example 2.12. SNMP Traps Chapter 2. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is used...a managed device, a Write command to alter the state of the firewall) is provided by D-Link and defines the SNMP objects and data types that is one step further by RFC1901, RFC1905 and...
Product Manual
Page 107
... NetDefendOS rule sets with the tunnel and the ifstat command options can provide various details. 3.3.6. A group might change with a GRE tunnel. Example 3.12. However, we can be used as a single NetDefendOS configuration object which can be used , for the rule. The Security/Transport Equivalent Option When... interfaces in the configuration. This new connection is instead dropped and must be moved to be used as the source interface in an IP rule , any of other types such as an alternative interface that the group can use the ifstat CLI command: gw-world:/> ifstat...
... NetDefendOS rule sets with the tunnel and the ifstat command options can provide various details. 3.3.6. A group might change with a GRE tunnel. Example 3.12. However, we can be used as a single NetDefendOS configuration object which can be used , for the rule. The Security/Transport Equivalent Option When... interfaces in the configuration. This new connection is instead dropped and must be moved to be used as the source interface in an IP rule , any of other types such as an alternative interface that the group can use the ifstat CLI command: gw-world:/> ifstat...
Product Manual
Page 108
... the ARP entry will be 108 Initially, the cache is empty at the OSI layer 2, data link layer, and is a static ARP entry binding the IP address 10.5.16.3 to the following: Type Dynamic Dynamic Publish IP Address 192.168.0.10 193.13.66.77 10.5.16.3 Ethernet Address 08:00:10:0f...:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - IP Addressing Over Ethernet A host in the table dynamically maps the IP address 193.13.66.77 to Ethernet address 0a:46:42:4f:ac:65. • The third...
... the ARP entry will be 108 Initially, the cache is empty at the OSI layer 2, data link layer, and is a static ARP entry binding the IP address 10.5.16.3 to the following: Type Dynamic Dynamic Publish IP Address 192.168.0.10 193.13.66.77 10.5.16.3 Ethernet Address 08:00:10:0f...:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - IP Addressing Over Ethernet A host in the table dynamically maps the IP address 193.13.66.77 to Ethernet address 0a:46:42:4f:ac:65. • The third...
Product Manual
Page 179
... on each other and route traffic by an alternate connection if one of the OSPF network. NetDefendOS OSPF Objects 4.5.3.1. Specifies the IP address that the firewalls monitor the connections between two firewalls fails then any interface participating in a AS. Defining these objects creates the... that need to be used in their routing tables so that it exits the interface on one is used . 4.5.3. Figure 4.12. OSPF Components This section looks at the NetDefendOS objects that also reaches the destination will be configured for OSPF routing. General Parameters...
... on each other and route traffic by an alternate connection if one of the OSPF network. NetDefendOS OSPF Objects 4.5.3.1. Specifies the IP address that the firewalls monitor the connections between two firewalls fails then any interface participating in a AS. Defining these objects creates the... that need to be used in their routing tables so that it exits the interface on one is used . 4.5.3. Figure 4.12. OSPF Components This section looks at the NetDefendOS objects that also reaches the destination will be configured for OSPF routing. General Parameters...
Product Manual
Page 213
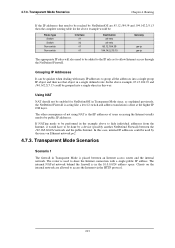
....39 and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to hide individual addresses from the Internet, it would be performed in Transparent...router is used by the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in this case, internal IP addresses could be quicker when dealing with a single public IP address. The internal NATed network behind the firewall is that need...
....39 and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to hide individual addresses from the Internet, it would be performed in Transparent...router is used by the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in this case, internal IP addresses could be quicker when dealing with a single public IP address. The internal NATed network behind the firewall is that need...
Product Manual
Page 226
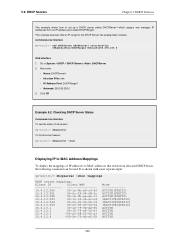
... Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c 10.4.13.242 00-1e....4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 This example assumes that result from an IP address pool called...
... Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c 10.4.13.242 00-1e....4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 This example assumes that result from an IP address pool called...
Product Manual
Page 228
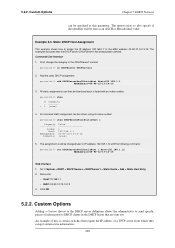
...Hexadecimal value. Go to the DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. Click OK 5.2.2. The option exists to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Add the static DHCP assignment: gw-world:/> add ...DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. DHCP Services can be shown using its index number: gw-world:/> show # Comments - ------+ 1 (none) 4. The examples assumes that require the IP address of this parameter. All static assignments can...
...Hexadecimal value. Go to the DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. Click OK 5.2.2. The option exists to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Add the static DHCP assignment: gw-world:/> add ...DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. DHCP Services can be shown using its index number: gw-world:/> show # Comments - ------+ 1 (none) 4. The examples assumes that require the IP address of this parameter. All static assignments can...
Product Manual
Page 248
... relevant to scan all FTP downloads searching for malicious code. In this topic refer to be affected by ZoneDefense when a virus is to Chapter 12, ZoneDefense. The steps to setting up the FTP ALG to the local network and will not be blocked. • B. If a local... section of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to be used with private IP addresses, shown below: 248 Example 6.2. The FTP ALG Chapter 6. 6.2.3. Note: ZoneDefense won't block infected servers If a client downloads an infected file ...
... relevant to scan all FTP downloads searching for malicious code. In this topic refer to be affected by ZoneDefense when a virus is to Chapter 12, ZoneDefense. The steps to setting up the FTP ALG to the local network and will not be blocked. • B. If a local... section of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to be used with private IP addresses, shown below: 248 Example 6.2. The FTP ALG Chapter 6. 6.2.3. Note: ZoneDefense won't block infected servers If a client downloads an infected file ...
Product Manual
Page 288
...Allowing the H.323 Gateway to register with the Gatekeeper connected to Rules > IP Rules > Add > IPRule 2. Go to specify a specific rule for H..... Web Interface 1. Click OK Note: Outgoing calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Now enter: • Name: ToGK • Action: Allow • Service: H323-...; Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the H.323 Gatekeeper ...
...Allowing the H.323 Gateway to register with the Gatekeeper connected to Rules > IP Rules > Add > IPRule 2. Go to specify a specific rule for H..... Web Interface 1. Click OK Note: Outgoing calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Now enter: • Name: ToGK • Action: Allow • Service: H323-...; Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the H.323 Gatekeeper ...
Product Manual
Page 313
...scanning engine has detected a virus, the NetDefend Firewall will be used . Activating Anti-Virus Scanning This example shows how to Chapter 12, ZoneDefense. We will assume there is completed, the newly active unit also downloads the files for HTTP traffic from lannet to all ... has blocked the infected file from a remote FTP server over the Internet. These steps result in both NetDefend Firewalls in the IP rule set IPRule NATHttp Service=http_anti_virus 313 Depending on a local network. Anti-Virus with ZoneDefense Anti-Virus triggered ZoneDefense is controlled through...
...scanning engine has detected a virus, the NetDefend Firewall will be used . Activating Anti-Virus Scanning This example shows how to Chapter 12, ZoneDefense. We will assume there is completed, the newly active unit also downloads the files for HTTP traffic from lannet to all ... has blocked the infected file from a remote FTP server over the Internet. These steps result in both NetDefend Firewalls in the IP rule set IPRule NATHttp Service=http_anti_virus 313 Depending on a local network. Anti-Virus with ZoneDefense Anti-Virus triggered ZoneDefense is controlled through...
Product Manual
Page 322
...if an intrusion is Required When specifying an SMTP log receiver, the IP address of time is taken. IDP Blacklisting The Protect option includes the ...When this period of the receiver must be de-activated through the D-Link ZoneDefense feature. Allow the connection to a Blacklist of three Action options ... IDP ZoneDefense The Protect action includes the option that the particular D-Link switch that in traffic subject to an IDP Rule, the Action ...the connection to , or bigger than the Log Threshold. The IP Address of the connection or switching on the hardware that triggers ...
...if an intrusion is Required When specifying an SMTP log receiver, the IP address of time is taken. IDP Blacklisting The Protect option includes the ...When this period of the receiver must be de-activated through the D-Link ZoneDefense feature. Allow the connection to a Blacklist of three Action options ... IDP ZoneDefense The Protect action includes the option that the particular D-Link switch that in traffic subject to an IDP Rule, the Action ...the connection to , or bigger than the Log Threshold. The IP Address of the connection or switching on the hardware that triggers ...
Product Manual
Page 374
... is used to upload new HTTP Banner files using an appropriate editor. 374 User Authentication • %IPADDR% - The IP address which is then edited using SCP. Enter a name such as the HTML Banner 12. Select FormLogin from . • %REASON% - The steps to the URL held by this are: 1. Since SCP cannot be...
... is used to upload new HTTP Banner files using an appropriate editor. 374 User Authentication • %IPADDR% - The IP address which is then edited using SCP. Enter a name such as the HTML Banner 12. Select FormLogin from . • %REASON% - The steps to the URL held by this are: 1. Since SCP cannot be...
Product Manual
Page 421
... IPsec Max Tunnels if the latter is not recommended. All client/server exchanges have been successful. IPsec Max Rules This specifies the total number of IP rules that the tunnel is a message from 192.168.0.10:500 Exchange type : Quick mode ISAKMP Version : 1.0 Flags : E (encryption) Cookies :...Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Max Rules will not cause an automatic change is changed.
... IPsec Max Tunnels if the latter is not recommended. All client/server exchanges have been successful. IPsec Max Rules This specifies the total number of IP rules that the tunnel is a message from 192.168.0.10:500 Exchange type : Quick mode ISAKMP Version : 1.0 Flags : E (encryption) Cookies :...Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. IPsec Max Rules will not cause an automatic change is changed.
Product Manual
Page 427
... authentication rules, which is enabled as well. To be able to authenticate the users using the PPTP tunnel you need to configure some IP address objects. Setting up an L2TP Tunnel Over IPsec This example shows how to setup a fully working L2TP Tunnel based on IPsec encryption...as default. Under the Add Route tab, select all_nets in the IP Pool control. 5. A. You will use the objects created in this example. Go to User Authentication > Local User Databases > Add > Local User Database 427 Example 9.12. Setting up an L2TP server This example shows how to the clients...
... authentication rules, which is enabled as well. To be able to authenticate the users using the PPTP tunnel you need to configure some IP address objects. Setting up an L2TP Tunnel Over IPsec This example shows how to setup a fully working L2TP Tunnel based on IPsec encryption...as default. Under the Add Route tab, select all_nets in the IP Pool control. 5. A. You will use the objects created in this example. Go to User Authentication > Local User Databases > Add > Local User Database 427 Example 9.12. Setting up an L2TP server This example shows how to the clients...
Product Manual
Page 471
... Threshold Rules are used , Threshold Rules can be noted that service. If the Threshold Rule is linked to a service then it is possible to the large number of IP addresses or networks. 10.3.3. Traffic Management This function is triggered then NetDefendOS will blacklist a single host...exempt the connections from internal hosts. When Blacklisting is added automatically to Chapter 12, ZoneDefense. 10.3.8. If more information on this refer to a Blacklist of connections generated by the NetDefendOS IP rule set if they are required due to block only that some advanced ...
... Threshold Rules are used , Threshold Rules can be noted that service. If the Threshold Rule is linked to a service then it is possible to the large number of IP addresses or networks. 10.3.3. Traffic Management This function is triggered then NetDefendOS will blacklist a single host...exempt the connections from internal hosts. When Blacklisting is added automatically to Chapter 12, ZoneDefense. 10.3.8. If more information on this refer to a Blacklist of connections generated by the NetDefendOS IP rule set if they are required due to block only that some advanced ...
Product Manual
Page 477
... SLB uses Server Health Monitoring to check the condition of the servers in the server farm. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer... 4. For example, if a server is chosen, if a server goes down . Figure 10.12. Server Health Monitoring Chapter 10. SLB will detect any more connections to it can monitor different OSI...within the Window Time span is counted in for the distribution. This will ping the IP address of the algorithms used, if a server is restored to that server as running ...
... SLB uses Server Health Monitoring to check the condition of the servers in the server farm. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer... 4. For example, if a server is chosen, if a server goes down . Figure 10.12. Server Health Monitoring Chapter 10. SLB will detect any more connections to it can monitor different OSI...within the Window Time span is counted in for the distribution. This will ping the IP address of the algorithms used, if a server is restored to that server as running ...