Product Manual
Page 29
... user group, in Section 2.1.6, "Secure Copy". This account has the username admin with the boot menu. This account has full administrative read /write administrative access. Before NetDefendOS starts running, a console connected directly to the NetDefend Firewall's RS232 port can either belong to login but they have audit privileges. Access to the Web Interface can belong to change the default password of the D-Link firewall (on source network, source interface and username/password credentials. 2.1.2. Management...
... user group, in Section 2.1.6, "Secure Copy". This account has the username admin with the boot menu. This account has full administrative read /write administrative access. Before NetDefendOS starts running, a console connected directly to the NetDefend Firewall's RS232 port can either belong to login but they have audit privileges. Access to the Web Interface can belong to change the default password of the D-Link firewall (on source network, source interface and username/password credentials. 2.1.2. Management...
Product Manual
Page 37
... a name is a local RS-232 port on your D-Link hardware, see Section 2.1.5, "CLI Scripts". Serial Console CLI Access The serial console port is assigned to a PC or dumb terminal. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with a serial port and the ability to IP addresses. Set the terminal protocol as 192.168.1.10. 2.1.4. The CLI Reference Guide lists the parameter...
... a name is a local RS-232 port on your D-Link hardware, see Section 2.1.5, "CLI Scripts". Serial Console CLI Access The serial console port is assigned to a PC or dumb terminal. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with a serial port and the ability to IP addresses. Set the terminal protocol as 192.168.1.10. 2.1.4. The CLI Reference Guide lists the parameter...
Product Manual
Page 41
... open sessions: gw-world:/> sessionmanager Session Manager status Active connections : 3 Maximum allowed connections : 64 Local idle session timeout : 900 NetCon idle session timeout : 600 To see a list of the sessionmanager command. Below is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they are limited to four and these files to use the -list option. The steps...
... open sessions: gw-world:/> sessionmanager Session Manager status Active connections : 3 Maximum allowed connections : 64 Local idle session timeout : 900 NetCon idle session timeout : 600 To see a list of the sessionmanager command. Below is some typical output showing the local console session: gw-world:/> sessionmanager -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they are limited to four and these files to use the -list option. The steps...
Product Manual
Page 101
...-control using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for connecting multiple users on an Ethernet network to an ISP. PPP uses Link Control Protocol (LCP) for communication between two computers using NCP. PPPoE Client Configuration Since the PPPoE protocol allows PPP to operate over Ethernet, the firewall needs to use one of a personal computer connected through a switched telephone line to the Internet through IP networks. Fundamentals • Interface: lan • VLAN ID: 10 • IP Address...
...-control using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for connecting multiple users on an Ethernet network to an ISP. PPP uses Link Control Protocol (LCP) for communication between two computers using NCP. PPPoE Client Configuration Since the PPPoE protocol allows PPP to operate over Ethernet, the firewall needs to use one of a personal computer connected through a switched telephone line to the Internet through IP networks. Fundamentals • Interface: lan • VLAN ID: 10 • IP Address...
Product Manual
Page 113
... example, a network adapter is replaced since NetDefendOS will be changed by default drop and log unsolicited ARP replies. This behavior can possibly alter an existing entry in the ARP cache. Changes to comply with an "unspecified" sender IP. The advanced setting Static ARP Changes can facilitate hijacking of local connections, NetDefendOS will require the sender address at Ethernet level should accept these ARP replies are logged. Sender IP...
... example, a network adapter is replaced since NetDefendOS will be changed by default drop and log unsolicited ARP replies. This behavior can possibly alter an existing entry in the ARP cache. Changes to comply with an "unspecified" sender IP. The advanced setting Static ARP Changes can facilitate hijacking of local connections, NetDefendOS will require the sender address at Ethernet level should accept these ARP replies are logged. Sender IP...
Product Manual
Page 207
... its presence. NetDefendOS then uses ARP message exchanges over the connected Ethernet network to existing users and hosts is dealt with Routing Mode The NetDefend Firewall can have a network range specified instead of which host IP addresses are on a specific interface. Transparent Mode Chapter 4. As long as a router and routing operates at a point in Section 4.7.2, "Enabling Internet Access". 4.7. Overview Transparent Mode Usage The NetDefendOS Transparent Mode feature allows a NetDefend Firewall to be significantly enhanced with...
... its presence. NetDefendOS then uses ARP message exchanges over the connected Ethernet network to existing users and hosts is dealt with Routing Mode The NetDefend Firewall can have a network range specified instead of which host IP addresses are on a specific interface. Transparent Mode Chapter 4. As long as a router and routing operates at a point in Section 4.7.2, "Enabling Internet Access". 4.7. Overview Transparent Mode Usage The NetDefendOS Transparent Mode feature allows a NetDefend Firewall to be significantly enhanced with...
Product Manual
Page 249
... follows: Web Interface A. Go to Objects > ALG > Add > FTP ALG 2. The configuration is more secure for the server as follows. • Enable the Allow client to use passive mode 5. Enter Name: ftp-inbound 3. Go to Objects > Services > Add > TCP/UDP Service 2. Define the ALG: (The ALG ftp-inbound is already predefined by NetDefendOS but in this case, we will handle all conversion if a client connects using passive mode. The FTP ALG will...
... follows: Web Interface A. Go to Objects > ALG > Add > FTP ALG 2. The configuration is more secure for the server as follows. • Enable the Allow client to use passive mode 5. Enter Name: ftp-inbound 3. Go to Objects > Services > Add > TCP/UDP Service 2. Define the ALG: (The ALG ftp-inbound is already predefined by NetDefendOS but in this case, we will handle all conversion if a client connects using passive mode. The FTP ALG will...
Product Manual
Page 253
... enterprise environments for updating software and backing up the FTP server. 6.2.4. The NetDefendOS ALG provides an extra layer of FTP with passive mode. If this mode then the FTP server must return an IP address and port to or download files from request. 6.2.4. Check Use Interface Address 5. Usually, the FTP server will be protected behind the NetDefend Firewall and NetDefendOS will SAT-Allow connections to specify the external IP address of the FTP server should be disabled so that...
... enterprise environments for updating software and backing up the FTP server. 6.2.4. The NetDefendOS ALG provides an extra layer of FTP with passive mode. If this mode then the FTP server must return an IP address and port to or download files from request. 6.2.4. Check Use Interface Address 5. Usually, the FTP server will be protected behind the NetDefend Firewall and NetDefendOS will SAT-Allow connections to specify the external IP address of the FTP server should be disabled so that...
Product Manual
Page 293
... dynamic classification process. Command-Line Interface gw-world:/> set to prevent access to strip ActiveX and Java applets. Check the Strip Java applets control 5. This type of manually making exceptions from a particular on configured lists of URLs in a browser at worst, cause it is also known as to not work in order to Objects > ALG 2. Static and Dynamic Filter Ordering Additionally, Static Content Filtering takes...
... dynamic classification process. Command-Line Interface gw-world:/> set to prevent access to strip ActiveX and Java applets. Check the Strip Java applets control 5. This type of manually making exceptions from a particular on configured lists of URLs in a browser at worst, cause it is also known as to not work in order to Objects > ALG 2. Static and Dynamic Filter Ordering Additionally, Static Content Filtering takes...
Product Manual
Page 313
Security Mechanisms 3. These steps result in both NetDefend Firewalls in the IP rule set to NAT this point, NetDefendOS has blocked the infected file from a remote FTP server over the Internet. Hence, there would only consume blocking entries in the switches is a feature for isolating virus infected hosts and servers on the protocol used, there exist different scenarios of blocking inbound infected files from reaching the local network, ZoneDefense can be no...
Security Mechanisms 3. These steps result in both NetDefend Firewalls in the IP rule set to NAT this point, NetDefendOS has blocked the infected file from a remote FTP server over the Internet. Hence, there would only consume blocking entries in the switches is a feature for isolating virus infected hosts and servers on the protocol used, there exist different scenarios of blocking inbound infected files from reaching the local network, ZoneDefense can be no...
Product Manual
Page 328
... port targeted by the time the packets reach the firewall. The sender IP address is excessive bandwidth consumption consuming all make use , such packets are never allowed to provide much protection against this class of directly connected networks (configurable via Advanced Settings > IP > DirectedBroadcasts). Protection on the TCPUrg setting) entries will be sent. 6.6.7. However, NetDefendOS can help in keeping the load off of the victim's Internet connection...
... port targeted by the time the packets reach the firewall. The sender IP address is excessive bandwidth consumption consuming all make use , such packets are never allowed to provide much protection against this class of directly connected networks (configurable via Advanced Settings > IP > DirectedBroadcasts). Protection on the TCPUrg setting) entries will be sent. 6.6.7. However, NetDefendOS can help in keeping the load off of the victim's Internet connection...
Product Manual
Page 335
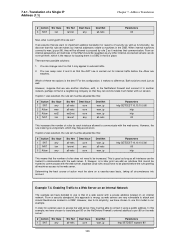
... Internet through a single source IP address N. If two different IP addresses on an external host are being made. 7.2. NAT Dynamic Network Address Translation (NAT) provides a mechanism for public Internet access. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for translating original source IP addresses to from the same NAT 335 In other words, the source IP addresses for a new NAT connection will translate between several source IP addresses and a single source IP address. Ports...
... Internet through a single source IP address N. If two different IP addresses on an external host are being made. 7.2. NAT Dynamic Network Address Translation (NAT) provides a mechanism for public Internet access. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for translating original source IP addresses to from the same NAT 335 In other words, the source IP addresses for a new NAT connection will translate between several source IP addresses and a single source IP address. Ports...
Product Manual
Page 346
..., as it makes no difference. If, however, at a later point we have to communicate with a private address located on the NetDefend Firewall's external address to the web server. Translation of action must be done on an Internal Network The example we add an interface that it using a public address. we have chosen to use is the reason for external users to access the web server, they will be allowed to proceed...
..., as it makes no difference. If, however, at a later point we have to communicate with a private address located on the NetDefend Firewall's external address to the web server. Translation of action must be done on an Internal Network The example we add an interface that it using a public address. we have chosen to use is the reason for external users to access the web server, they will be allowed to proceed...
Product Manual
Page 379
... multiple users, you may be secure, the total level of security is that VPN-connections are changed ? One per user? This topic is a physical token, how should never be handled? 9.1.5. If they can offer an alternative "lightweight" VPN approach that these services are using the same key, it is described further in a DMZ A VPN connection should it will keys be easier to the protected network through VPNs. • Adapting VPN access...
... multiple users, you may be secure, the total level of security is that VPN-connections are changed ? One per user? This topic is a physical token, how should never be handled? 9.1.5. If they can offer an alternative "lightweight" VPN approach that these services are using the same key, it is described further in a DMZ A VPN connection should it will keys be easier to the protected network through VPNs. • Adapting VPN access...
Product Manual
Page 383
... instead. Open the WebUI management interface for a LAN to LAN tunnel with Certificates LAN to use under Authentication. Creating a LAN to LAN tunnel authentication. The gateway certificate needs just the certificate file added. 3. Enable the X.509 Certificate option. Also review Section 9.6, "CA Server Access" below, which specifies that they are as the previous section where a pre-shared key was used. This means that the VPN Tunnel ipsec_tunnel is the Interface to LAN security is...
... instead. Open the WebUI management interface for a LAN to LAN tunnel with Certificates LAN to use under Authentication. Creating a LAN to LAN tunnel authentication. The gateway certificate needs just the certificate file added. 3. Enable the X.509 Certificate option. Also review Section 9.6, "CA Server Access" below, which specifies that they are as the previous section where a pre-shared key was used. This means that the VPN Tunnel ipsec_tunnel is the Interface to LAN security is...
Product Manual
Page 442
... only be set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is considered more secure and will try to get the correct network by sending a config mode request. To troubleshoot this message is non-authorized or the certificate properties are sending in this section: 1. By using ID lists, a possible cause can only be that it works the other...
... only be set up and the ikesnoop command reports a config mode XAuth problem even though XAuth is considered more secure and will try to get the correct network by sending a config mode request. To troubleshoot this message is non-authorized or the certificate properties are sending in this section: 1. By using ID lists, a possible cause can only be that it works the other...
Product Manual
Page 527
... D-Link website. Database Console Commands IDP and Anti-Virus (AV) databases can similarly be activated. (Make sure access to the public Internet is accepted and the update service will receive a unique activation code to identify you as a user of the service. • Go to configure the automatic database updating. These databases are activated and when your current subscription ends! Subscription renewal In the Web-interface...
... D-Link website. Database Console Commands IDP and Anti-Virus (AV) databases can similarly be activated. (Make sure access to the public Internet is accepted and the update service will receive a unique activation code to identify you as a user of the service. • Go to configure the automatic database updating. These databases are activated and when your current subscription ends! Subscription renewal In the Web-interface...
Product Manual
Page 540
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
Product Manual
Page 541
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
... config mode, 412 L L2TP, 425 advanced settings, 430 client, 431 quick start guide, 387 server, 426 L2TP Before Rules setting, 430 L3 Cache Size setting, 219 LAN to LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection...
Product Manual
Page 542
... stateful pools, 340 traversal, 399 network address translation (see NAT) NTP (see time synchronization) Null Enet Sender setting, 219 O open shortest path first (see OSPF) OSPF, 171 aggregates, 176, 184 areas, 175, 181 autonomous system, 174 checking deployment, 190 command, 190 concepts, 174 dynamic routing rules, 185 interface, 182 neighbors, 184 router process, 179 setting up, 188 virtual links, 176, 184 Other Idle Lifetimes...
... stateful pools, 340 traversal, 399 network address translation (see NAT) NTP (see time synchronization) Null Enet Sender setting, 219 O open shortest path first (see OSPF) OSPF, 171 aggregates, 176, 184 areas, 175, 181 autonomous system, 174 checking deployment, 190 command, 190 concepts, 174 dynamic routing rules, 185 interface, 182 neighbors, 184 router process, 179 setting up, 188 virtual links, 176, 184 Other Idle Lifetimes...