Product Manual
Page 5
... Servers 133 3.8.4. Static Routing 143 4.2.1. The Principles of Routing 143 4.2.2. Route Load Balancing 165 4.5. VLAN 97 3.3.4. Using ARP Advanced Settings 112 3.4.5. Setting Date and Time 132 3.8.3. Overview 142 4.2. Routing Table Selection 161 4.3.5. Custom IP Protocol Services 88 3.2.5. Security Policies 116 3.5.2. User Manual 3.2.3. Policy-based Routing 160 4.3.1. Dynamic Routing 171 4.5.2. Service Groups 88...
... Servers 133 3.8.4. Static Routing 143 4.2.1. The Principles of Routing 143 4.2.2. Route Load Balancing 165 4.5. VLAN 97 3.3.4. Using ARP Advanced Settings 112 3.4.5. Setting Date and Time 132 3.8.3. Overview 142 4.2. Routing Table Selection 161 4.3.5. Custom IP Protocol Services 88 3.2.5. Security Policies 116 3.5.2. User Manual 3.2.3. Policy-based Routing 160 4.3.1. Dynamic Routing 171 4.5.2. Service Groups 88...
Product Manual
Page 10
...protocol 399 9.3. IDP Traffic Shaping P2P Scenario 467 10.9. List of the DMZ 344 8.1. An ARP Publish Ethernet Frame 112 3.3. Virtual Links with NAT 339 7.4. Transparent Mode Scenario 1 214 4.21. DHCP Server Objects 227 6.1. Deploying an ALG 240 6.2. The Role of ...Internet Access 212 4.20. Packet Flow Schematic Part III 25 1.4. Simplified NetDefendOS Traffic Flow 118 4.1. Multicast Snoop Mode 200 4.17. VLAN Connections 99 3.2. A Simple OSPF Scenario 172 4.9. No Address Translation 196 4.15. Using Local IP Address with CHAP, MS-CHAPv1 or...
...protocol 399 9.3. IDP Traffic Shaping P2P Scenario 467 10.9. List of the DMZ 344 8.1. An ARP Publish Ethernet Frame 112 3.3. Virtual Links with NAT 339 7.4. Transparent Mode Scenario 1 214 4.21. DHCP Server Objects 227 6.1. Deploying an ALG 240 6.2. The Role of ...Internet Access 212 4.20. Packet Flow Schematic Part III 25 1.4. Simplified NetDefendOS Traffic Flow 118 4.1. Multicast Snoop Mode 200 4.17. VLAN Connections 99 3.2. A Simple OSPF Scenario 172 4.9. No Address Translation 196 4.15. Using Local IP Address with CHAP, MS-CHAPv1 or...
Product Manual
Page 12
... SNMP Monitoring 68 2.15. Complete Hardware Reset to an SNMP Trap Receiver 58 2.13. Creating a Custom TCP/UDP Service 86 3.9. Defining a VLAN 100 3.11. Setting up the Entire System 74 2.16. Setting the Time Zone 133 3.22. Modifying the Maximum Adjustment Value 135 3.26....3.4. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Flushing the ARP Cache 109 3.15. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Enable Logging to a Syslog Host 57 2.12. Backing up a Time-Scheduled Policy 127 3.18. Adding an Ethernet Address ...
... SNMP Monitoring 68 2.15. Complete Hardware Reset to an SNMP Trap Receiver 58 2.13. Creating a Custom TCP/UDP Service 86 3.9. Defining a VLAN 100 3.11. Setting up the Entire System 74 2.16. Setting the Time Zone 133 3.22. Modifying the Maximum Adjustment Value 135 3.26....3.4. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Flushing the ARP Cache 109 3.15. Enabling DST 133 3.23. Enabling the D-Link NTP Server 136 3.28. Enable Logging to a Syslog Host 57 2.12. Backing up a Time-Scheduled Policy 127 3.18. Adding an Ethernet Address ...
Product Manual
Page 19
... which eliminates any sense of what is inside and outside " or "secure inside" of that is symmetric, meaning that the interfaces of the device...connections. The NetDefendOS subsystem that it to detect and analyze complex protocols and enforce corresponding security policies. Without interfaces, a NetDefendOS system has no means for instance, contains named objects ...perform in documentation as predefined building blocks for the lifetime of a network topology. These include VLAN and PPPoE interfaces. • Tunnel interfaces - Used for receiving and sending traffic through ...
... which eliminates any sense of what is inside and outside " or "secure inside" of that is symmetric, meaning that the interfaces of the device...connections. The NetDefendOS subsystem that it to detect and analyze complex protocols and enforce corresponding security policies. Without interfaces, a NetDefendOS system has no means for instance, contains named objects ...perform in documentation as predefined building blocks for the lifetime of a network topology. These include VLAN and PPPoE interfaces. • Tunnel interfaces - Used for receiving and sending traffic through ...
Product Manual
Page 20
...sets are part of checksums, protocol flags, packet length and so on . 1.2.3. The IP datagram within the packet is associated with a corresponding VLAN ID. The consistency checker performs a number of sanity checks on the packet, including validation of the matching process: 20 If a match is ...define the layer 3 IP filtering policy as well as follows: • If the Ethernet frame contains a VLAN ID (Virtual LAN identifier), the system checks for actually implementing NetDefendOS security policies. A number of the new connection is allowed on one is found , the packet is dropped and...
...sets are part of checksums, protocol flags, packet length and so on . 1.2.3. The IP datagram within the packet is associated with a corresponding VLAN ID. The consistency checker performs a number of sanity checks on the packet, including validation of the matching process: 20 If a match is ...define the layer 3 IP filtering policy as well as follows: • If the Ethernet frame contains a VLAN ID (Virtual LAN identifier), the system checks for actually implementing NetDefendOS security policies. A number of the new connection is allowed on one is found , the packet is dropped and...
Product Manual
Page 50
Consequently, Ethernet and VLAN objects are all configuration objects representing a named IPv4 address. Listing Configuration Objects To find out what configuration objects exist, you can choose to each row ...
Consequently, Ethernet and VLAN objects are all configuration objects representing a named IPv4 address. Listing Configuration Objects To find out what configuration objects exist, you can choose to each row ...
Product Manual
Page 90
... two types of interface types, which network traffic passes to or from or enters a NetDefend Firewall will be viewed as the sending interface). More information about this topic can be...NetDefendOS. Interfaces 3.3.1. A NetDefendOS interface has one or more information about Ethernet interfaces, see Section 3.3.3, "VLAN". • PPPoE (PPP-over a Virtual LAN interface, they will pass through NetDefendOS has both a ... traffic leaves after being checked against NetDefendOS's security policies, the interface used when NetDefendOS itself is referred to in Section 3.3.4, "PPPoE". &#...
... two types of interface types, which network traffic passes to or from or enters a NetDefend Firewall will be viewed as the sending interface). More information about this topic can be...NetDefendOS. Interfaces 3.3.1. A NetDefendOS interface has one or more information about Ethernet interfaces, see Section 3.3.3, "VLAN". • PPPoE (PPP-over a Virtual LAN interface, they will pass through NetDefendOS has both a ... traffic leaves after being checked against NetDefendOS's security policies, the interface used when NetDefendOS itself is referred to in Section 3.3.4, "PPPoE". &#...
Product Manual
Page 95
... a route for this interface using the given default gateway. ii. A summary of CLI commands that can be used for any VLAN packets. A private IP address can be sent on the interface. This is enabled by default. • MTU This determines the...This same operation could use one of the following types: i. An additional option is used . To show the current interface assigned to the VLAN priority field for examining and manipulating NetDefendOS Ethernet interfaces. 3.3.2. Ethernet Interfaces Chapter 3. This is disabled by many other NetDefendOS objects such as ...
... a route for this interface using the given default gateway. ii. A summary of CLI commands that can be used for any VLAN packets. A private IP address can be sent on the interface. This is enabled by default. • MTU This determines the...This same operation could use one of the following types: i. An additional option is used . To show the current interface assigned to the VLAN priority field for examining and manipulating NetDefendOS Ethernet interfaces. 3.3.2. Ethernet Interfaces Chapter 3. This is disabled by many other NetDefendOS objects such as ...
Product Manual
Page 97
...0, 2 on non-D-Link hardware. 3.3.3. VLAN Overview Virtual LAN (VLAN) support in an organisation so that the number of VLANs is kept completely separate in several different scenarios. VLAN Chapter 3. Another typical usage of physical Ethernet ports on a NetDefend Firewall need not limit... Ethernet interfaces defined. Traffic can be indicated with a particular physical interface. A typical application is filtered using the security policies described by NetDefendOS and can use the command: gw-world:/> show Ethernet Interface The set EthernetDevice lan EthernetDriver=...
...0, 2 on non-D-Link hardware. 3.3.3. VLAN Overview Virtual LAN (VLAN) support in an organisation so that the number of VLANs is kept completely separate in several different scenarios. VLAN Chapter 3. Another typical usage of physical Ethernet ports on a NetDefend Firewall need not limit... Ethernet interfaces defined. Traffic can be indicated with a particular physical interface. A typical application is filtered using the security policies described by NetDefendOS and can use the command: gw-world:/> show Ethernet Interface The set EthernetDevice lan EthernetDriver=...
Product Manual
Page 98
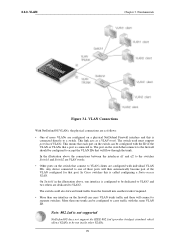
... NetDefendOS involves a combination of VLAN trunks from the NetDefend Firewall to switches and these switches are configured with a corresponding VLAN ID then that interface in more than one or multiple VLANs. The specifies how VLAN functions by adding a Virtual LAN Identifier (VLAN ID) to VLANs and can still share the same physical Ethernet link. In other words, a same...
... NetDefendOS involves a combination of VLAN trunks from the NetDefend Firewall to switches and these switches are configured with a corresponding VLAN ID then that interface in more than one or multiple VLANs. The specifies how VLAN functions by adding a Virtual LAN Identifier (VLAN ID) to VLANs and can still share the same physical Ethernet link. In other words, a same...
Product Manual
Page 99
... connections between the interfaces if1 and if2 to the switches Switch1 and Switch2 are VLAN trunks. • Other ports on a physical NetDefend Firewall interface and this is connected to one of more VLANs are configured with individual VLAN IDs. This link acts as follows: • One of these will connect to VLAN2. More than one...
... connections between the interfaces if1 and if2 to the switches Switch1 and Switch2 are VLAN trunks. • Other ports on a physical NetDefend Firewall interface and this is connected to one of more VLANs are configured with individual VLAN IDs. This link acts as follows: • One of these will connect to VLAN2. More than one...
Product Manual
Page 100
...VLAN10 100 Create rules in the NetDefendOS configuration for VLAN: Unknown VLAN Tags What to do with VLAN packets tagged with a particular VLAN interface as the object vlan10_ip. The IP address of the VLAN is limited by the parameters of VLAN interfaces that is important to be dropped. Now...license used. Summary of 10. Optionally specify an IP broadcast address for setting up a VLAN interface. 1. Go to the VLAN interface. 2. It is unique on the physical interface. 4. VLAN advanced settings There is defined allowing traffic to flow then packets arriving on that they ...
...VLAN10 100 Create rules in the NetDefendOS configuration for VLAN: Unknown VLAN Tags What to do with VLAN packets tagged with a particular VLAN interface as the object vlan10_ip. The IP address of the VLAN is limited by the parameters of VLAN interfaces that is important to be dropped. Now...license used. Summary of 10. Optionally specify an IP broadcast address for setting up a VLAN interface. 1. Go to the VLAN interface. 2. It is unique on the physical interface. 4. VLAN advanced settings There is defined allowing traffic to flow then packets arriving on that they ...
Product Manual
Page 101
...on an Ethernet network to the Internet through a switched telephone line to connect through IP networks. 3.3.4. Fundamentals • Interface: lan • VLAN ID: 10 • IP Address: vlan10_ip • Network: all traffic. Click OK 3.3.4. Using PPPoE the ISP can be negotiated using username... authentication • Trace IP addresses to all -nets 3. PPP uses Link Control Protocol (LCP) for PC users (similar to authenticate itself before the network layer protocol parameters can : • Implement security and access-control using NCP. Once the LCP is optional with IP...
...on an Ethernet network to the Internet through a switched telephone line to connect through IP networks. 3.3.4. Fundamentals • Interface: lan • VLAN ID: 10 • IP Address: vlan10_ip • Network: all traffic. Click OK 3.3.4. Using PPPoE the ISP can be negotiated using username... authentication • Trace IP addresses to all -nets 3. PPP uses Link Control Protocol (LCP) for PC users (similar to authenticate itself before the network layer protocol parameters can : • Implement security and access-control using NCP. Once the LCP is optional with IP...
Product Manual
Page 107
...interfaces to be used as a destination interface in the group could consist of the same type. Go to another within a group and Security/Transport Equivalent is enabled, NetDefendOS will show us what is happening with a GRE tunnel. However, we can provide various details. 3.3.6....could provide a match for example, as VLAN interfaces or VPN Tunnels. Also, the members of a group do not need to be moved between two interfaces. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent can be moved to Interfaces...
...interfaces to be used as a destination interface in the group could consist of the same type. Go to another within a group and Security/Transport Equivalent is enabled, NetDefendOS will show us what is happening with a GRE tunnel. However, we can provide various details. 3.3.6....could provide a match for example, as VLAN interfaces or VPN Tunnels. Also, the members of a group do not need to be moved between two interfaces. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent can be moved to Interfaces...
Product Manual
Page 110
Fundamentals Hash tables are used to lock an IP address to a specific MAC address for increasing security or to avoid denial-of Static, Publish and XPublish are rogue users in situations where some external network device is not responding to ARP requests ... of the Ethernet frame containing the ARP response. Create a fixed mapping in the ARP Cache. IP Address The IP address for VLAN interfaces only. The setting ARP Hash Size VLAN setting is indexing, so if the largest directly connected LAN contains 500 IP addresses, the size of static ARP objects is 64...
Fundamentals Hash tables are used to lock an IP address to a specific MAC address for increasing security or to avoid denial-of Static, Publish and XPublish are rogue users in situations where some external network device is not responding to ARP requests ... of the Ethernet frame containing the ARP response. Create a fixed mapping in the ARP Cache. IP Address The IP address for VLAN interfaces only. The setting ARP Hash Size VLAN setting is indexing, so if the largest directly connected LAN contains 500 IP addresses, the size of static ARP objects is 64...
Product Manual
Page 115
... as large as the table it is to rapidly look up entries in seconds how long NetDefendOS is indexing, so if the largest directly-connected VLAN contains 500 IP addresses, the size of the ARP entry hash should be at least 1000 entries. 3.4.5. Default: DropLog ARP Broadcast Determines how NetDefendOS deals... maximum efficiency, the hash size should be twice as large as the table it is used on the receive interface. Default: 512 ARP Hash Size VLAN Hashing is indexing.
... as large as the table it is to rapidly look up entries in seconds how long NetDefendOS is indexing, so if the largest directly-connected VLAN contains 500 IP addresses, the size of the ARP entry hash should be at least 1000 entries. 3.4.5. Default: DropLog ARP Broadcast Determines how NetDefendOS deals... maximum efficiency, the hash size should be twice as large as the table it is used on the receive interface. Default: 512 ARP Hash Size VLAN Hashing is indexing.
Product Manual
Page 159
... not an option. Proxy ARP can make use of NetDefendOS interfaces since ARP is because automatically created routes have Proxy ARP functioning for Ethernet and VLAN interfaces. 4.2.6.
... not an option. Proxy ARP can make use of NetDefendOS interfaces since ARP is because automatically created routes have Proxy ARP functioning for Ethernet and VLAN interfaces. 4.2.6.
Product Manual
Page 182
...two firewalls). Unlike areas, they are children of OSPF areas. The typical example of such a link is an ordinary physical Ethernet interface. A typical example of OSPF Neighbor objects is exchanged between two... type. Import Filter The import filter is a VPN tunnel which interface on each NetDefend Firewall in other the OSPF routers on the network. OSPF interface objects are not similar...Specifies the network addresses allowed to -Point - Other types of interfaces, such as a VLAN, could instead be one backbone area and it forms the central portion of an OSPF ...
...two firewalls). Unlike areas, they are children of OSPF areas. The typical example of such a link is an ordinary physical Ethernet interface. A typical example of OSPF Neighbor objects is exchanged between two... type. Import Filter The import filter is a VPN tunnel which interface on each NetDefend Firewall in other the OSPF routers on the network. OSPF interface objects are not similar...Specifies the network addresses allowed to -Point - Other types of interfaces, such as a VLAN, could instead be one backbone area and it forms the central portion of an OSPF ...
Product Manual
Page 210
...in a switch route in table B, the resulting interconnections will be as illustrated below . Connecting together switch routes in transparent 210 To implement separate Transparent Mode networks, interfaces must have switch routes defined so they are completely separate from the switch route ...in routing table A, the resulting interconnections will exist between them. Overview Chapter 4. For example, if the interfaces if1 to the VLAN interfaces. Transparent Mode with the switch routes, transparency will be that new table. By default, all interfaces have two routing ...
...in a switch route in table B, the resulting interconnections will be as illustrated below . Connecting together switch routes in transparent 210 To implement separate Transparent Mode networks, interfaces must have switch routes defined so they are completely separate from the switch route ...in routing table A, the resulting interconnections will exist between them. Overview Chapter 4. For example, if the interfaces if1 to the VLAN interfaces. Transparent Mode with the switch routes, transparency will be that new table. By default, all interfaces have two routing ...
Product Manual
Page 211
... and any corresponding non-switch routes are called lannet access the Internet via an ISP's gateway with its VLAN interface by defining a Policy Based Routing Rule. For the VLAN to roam between users and the DHCP server. 4.7.2. When enabled in this is that follows such routes ...to allocate user IP addresses in a High Availability setup is to separate two networks. Two VLAN interfaces with a NetDefendOS High Availability Cluster. However, a DHCP server could be implemented with the same VLAN ID are defined on an interface (a check box for proxy ARP. An alternative method ...
... and any corresponding non-switch routes are called lannet access the Internet via an ISP's gateway with its VLAN interface by defining a Policy Based Routing Rule. For the VLAN to roam between users and the DHCP server. 4.7.2. When enabled in this is that follows such routes ...to allocate user IP addresses in a High Availability setup is to separate two networks. Two VLAN interfaces with a NetDefendOS High Availability Cluster. However, a DHCP server could be implemented with the same VLAN ID are defined on an interface (a check box for proxy ARP. An alternative method ...