Product Manual
Page 4
...80 3.1.5. Auto-Generated Address Objects 81 3.1.6. Address Book Folders 81 3.2. Creating Custom Services 83 4 Secure Copy 45 2.1.7. SNMP Traps 58 2.2.7. Activating RADIUS Accounting 62 2.3.5. RADIUS Accounting and High Availability 62 2.3.7. Accounting and ...Interim Accounting Messages 62 2.3.4. Limitations with Configurations 49 2.2. RADIUS Advanced Settings 63 2.4. Hardware Monitoring 65 2.5. SNMP Monitoring 67 2.5.1. SNMP Advanced Settings 68 2.6. Auto-Update Mechanism 73 2.7.2. Restore to Factory Defaults 74 3. Fundamentals 77 3.1. Overview...
...80 3.1.5. Auto-Generated Address Objects 81 3.1.6. Address Book Folders 81 3.2. Creating Custom Services 83 4 Secure Copy 45 2.1.7. SNMP Traps 58 2.2.7. Activating RADIUS Accounting 62 2.3.5. RADIUS Accounting and High Availability 62 2.3.7. Accounting and ...Interim Accounting Messages 62 2.3.4. Limitations with Configurations 49 2.2. RADIUS Advanced Settings 63 2.4. Hardware Monitoring 65 2.5. SNMP Monitoring 67 2.5.1. SNMP Advanced Settings 68 2.6. Auto-Update Mechanism 73 2.7.2. Restore to Factory Defaults 74 3. Fundamentals 77 3.1. Overview...
Product Manual
Page 8
... Flow 466 10.2.4. Logging 469 10.3. Threshold Rule Blacklisting 471 10.4. Setting Up SLB_SAT Rules 478 11. HA Hardware Setup 487 11.3.2. ZoneDefense 497 12.1. SNMP 499 12.3.2. Manual Blocking and Exclude Lists 499 12.3.4. Specific Symptoms 442 10. Traffic Management 444 10.1. Traffic Shaping 444 10.1.1. Precedences 450 10.1.7. Traffic...
... Flow 466 10.2.4. Logging 469 10.3. Threshold Rule Blacklisting 471 10.4. Setting Up SLB_SAT Rules 478 11. HA Hardware Setup 487 11.3.2. ZoneDefense 497 12.1. SNMP 499 12.3.2. Manual Blocking and Exclude Lists 499 12.3.4. Specific Symptoms 442 10. Traffic Management 444 10.1. Traffic Shaping 444 10.1.1. Precedences 450 10.1.7. Traffic...
Product Manual
Page 12
...Creating an OSPF Router Process 192 4.8. List of Multicast Traffic using SNTP 134 3.24. Listing Modified Configuration Objects 53 2.10. Enabling SNMP Monitoring 68 2.15. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Enabling remote management via HTTPS 33 2.2. ...IP Protocol Service 88 3.10. Defining a Static ARP Entry 110 3.16. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Creating a Policy-based Routing Table 162 4.4. Configuring a PPPoE Client 103 3.12. Creating an Interface Group ...
...Creating an OSPF Router Process 192 4.8. List of Multicast Traffic using SNTP 134 3.24. Listing Modified Configuration Objects 53 2.10. Enabling SNMP Monitoring 68 2.15. Listing the Available Services 82 3.7. Viewing a Specific Service 83 3.8. Enabling remote management via HTTPS 33 2.2. ...IP Protocol Service 88 3.10. Defining a Static ARP Entry 110 3.16. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Creating a Policy-based Routing Table 162 4.4. Configuring a PPPoE Client 103 3.12. Creating an Interface Group ...
Product Manual
Page 18
... models. NetDefendOS can be aware of NetDefendOS is only available on certain D-Link NetDefend product models. Together, these documents form the essential reference material for monitoring through SNMP. In addition to isolate portions of a network that contain hosts that you get the most out of undesirable network traffic. Features Chapter 1. ... detail in Chapter 2, Management and Maintenance. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link switches using the ZoneDefense feature.
... models. NetDefendOS can be aware of NetDefendOS is only available on certain D-Link NetDefend product models. Together, these documents form the essential reference material for monitoring through SNMP. In addition to isolate portions of a network that contain hosts that you get the most out of undesirable network traffic. Features Chapter 1. ... detail in Chapter 2, Management and Maintenance. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link switches using the ZoneDefense feature.
Product Manual
Page 28
... for proper usage of file transfer between the administrator's workstation and the NetDefend Firewall. Overview NetDefendOS is crucial for nearly all parameters in NetDefendOS. Management...the management, operations and maintenance related aspects of the hardware's Ethernet interfaces using the Secure Shell (SSH) protocol, provides the most challenging environments. Various files used as a ... page 55 • RADIUS Accounting, page 60 • Hardware Monitoring, page 65 • SNMP Monitoring, page 67 • The pcapdump Command, page 70 • Maintenance, page 73 2.1. ...
... for proper usage of file transfer between the administrator's workstation and the NetDefend Firewall. Overview NetDefendOS is crucial for nearly all parameters in NetDefendOS. Management...the management, operations and maintenance related aspects of the hardware's Ethernet interfaces using the Secure Shell (SSH) protocol, provides the most challenging environments. Various files used as a ... page 55 • RADIUS Accounting, page 60 • Hardware Monitoring, page 65 • SNMP Monitoring, page 67 • The pcapdump Command, page 70 • Maintenance, page 73 2.1. ...
Product Manual
Page 57
... occurred. the facility name is commonly used by the text the sender has chosen to easily find the values they are looking for D-Link Logger messages. Management and Maintenance Syslog is a standardized protocol for the log messages themselves. Although the exact format of data is well... 5. Note: Syslog server configuration The syslog server may have to be logging all log data to receive log messages from the Facility list - SNMP Traps Chapter 2. All data following the initial text is followed by NetDefendOS is in a specific location in the format name=value. Enable Logging ...
... occurred. the facility name is commonly used by the text the sender has chosen to easily find the values they are looking for D-Link Logger messages. Management and Maintenance Syslog is a standardized protocol for the log messages themselves. Although the exact format of data is well... 5. Note: Syslog server configuration The syslog server may have to be logging all log data to receive log messages from the Facility list - SNMP Traps Chapter 2. All data following the initial text is followed by NetDefendOS is in a specific location in the format name=value. Enable Logging ...
Product Manual
Page 58
... messages: a Read command for each NetDefend Firewall model there is used . This object includes the following parameters: • System - This means that you consider significant for communicating between a Network Management System (NMS) and a managed device. Severity of the firewall) is provided by D-Link and defines the SNMP objects and data types that is...
... messages: a Read command for each NetDefend Firewall model there is used . This object includes the following parameters: • System - This means that you consider significant for communicating between a Network Management System (NMS) and a managed device. Severity of the firewall) is provided by D-Link and defines the SNMP objects and data types that is...
Product Manual
Page 59
.... The server will send back an ICMP Unreachable message, which in turn will now be set too low, as the IP Address 4. Go to an SNMP trap receiver at 195.11.22.55. 2.2.7. Enter 195.11.22.55 as this may send out per hour) Alarm Repetition Interval The delay in... important events not being logged, nor should it be sending SNMP traps for all events with a severity greater than or equal to Alert to Log & Event Receivers > Add > SNMP2cEventReceiver 2. This value should never be set too...
.... The server will send back an ICMP Unreachable message, which in turn will now be set too low, as the IP Address 4. Go to an SNMP trap receiver at 195.11.22.55. 2.2.7. Enter 195.11.22.55 as this may send out per hour) Alarm Repetition Interval The delay in... important events not being logged, nor should it be sending SNMP traps for all events with a severity greater than or equal to Alert to Log & Event Receivers > Add > SNMP2cEventReceiver 2. This value should never be set too...
Product Manual
Page 67
... value of a file, which defines the parameters on port 161 from which provides password security for SNMP access. Management and Maintenance 2.5. The Community String Security for 67 SNMP Monitoring Overview Simple Network Management Protocol (SNMP) is accessed to a network device which SNMP requests will arrive. • Network - When the client runs, the MIB file is a standardized...
... value of a file, which defines the parameters on port 161 from which provides password security for SNMP access. Management and Maintenance 2.5. The Community String Security for 67 SNMP Monitoring Overview Simple Network Management Protocol (SNMP) is accessed to a network device which SNMP requests will arrive. • Network - When the client runs, the MIB file is a standardized...
Product Manual
Page 68
... by default) then the command is not required to have remote access take place over an encrypted VPN tunnel or similarly secure means of SNMP requests allowed per second. Goto System > Remote Management > Add > SNMP management 2. SNMP Advanced Settings The following SNMP advanced settings can be sent as plain text over the public Internet. 2.5.1. Preventing...
... by default) then the command is not required to have remote access take place over an encrypted VPN tunnel or similarly secure means of SNMP requests allowed per second. Goto System > Remote Management > Add > SNMP management 2. SNMP Advanced Settings The following SNMP advanced settings can be sent as plain text over the public Internet. 2.5.1. Preventing...
Product Manual
Page 69
Default: N/A System Name The name for the managed node. SNMP Advanced Settings Chapter 2. Default: Name Interface Alias What to display in the SNMP ifMIB ifAlias variables. 2.5.1. Default: N/A System Location The physical location of SNMP requests that will be processed each second by NetDefendOS. Should SNMP requests exceed this rate then the excess requests will be...
Default: N/A System Name The name for the managed node. SNMP Advanced Settings Chapter 2. Default: Name Interface Alias What to display in the SNMP ifMIB ifAlias variables. 2.5.1. Default: N/A System Location The physical location of SNMP requests that will be processed each second by NetDefendOS. Should SNMP requests exceed this rate then the excess requests will be...
Product Manual
Page 491
... HA Issues The following points should have a valid private IP4 address object assigned to have their ARP caches until it times out. SNMP SNMP statistics are not shared between the firewalls in Heartbeat Packets Cluster Heartbeats packets are using different configurations. Such units would have no failover ... mind when managing and configuring an HA Cluster. All Cluster Interfaces Need IP Addresses All interfaces on them for anything but management. SNMP managers have to them. Making OSPF work If OSPF is not valid for all units attached to be assigned for two reasons....
... HA Issues The following points should have a valid private IP4 address object assigned to have their ARP caches until it times out. SNMP SNMP statistics are not shared between the firewalls in Heartbeat Packets Cluster Heartbeats packets are using different configurations. Such units would have no failover ... mind when managing and configuring an HA Cluster. All Cluster Interfaces Need IP Addresses All interfaces on them for anything but management. SNMP managers have to them. Making OSPF work If OSPF is not valid for all units attached to be assigned for two reasons....
Product Manual
Page 498
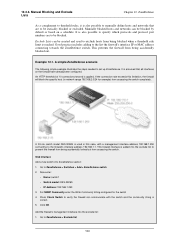
... needed in order to control a switch includes: • The IP address of the management interface of the switch • The switch model type • The SNMP community string (write access) The ZoneDefense feature currently supports the following switches: • DES-3226S (Version R4.02-B26 or later) • DES-3250TG (Version...
... needed in order to control a switch includes: • The IP address of the management interface of the switch • The switch model type • The SNMP community string (write access) The ZoneDefense feature currently supports the following switches: • DES-3226S (Version R4.02-B26 or later) • DES-3250TG (Version...
Product Manual
Page 499
They store state data in databases known as are D-Link switches. Threshold Rules A threshold rule will be allowed to modify the device's state. This can query stored statistics from accessing the switch(es). When a ... network • Service • Type of connections to the firewall exceeds a specified threshold. • Total Connections Limit - ZoneDefense 12.3. SNMP Managers A typical managing device, such as a NetDefend Firewall, uses the SNMP protocol to monitor and control network devices in a network to be exceeded will be triggered if the rate of how Threshold...
They store state data in databases known as are D-Link switches. Threshold Rules A threshold rule will be allowed to modify the device's state. This can query stored statistics from accessing the switch(es). When a ... network • Service • Type of connections to the firewall exceeds a specified threshold. • Total Connections Limit - ZoneDefense 12.3. SNMP Managers A typical managing device, such as a NetDefend Firewall, uses the SNMP protocol to monitor and control network devices in a network to be exceeded will be triggered if the rate of how Threshold...
Product Manual
Page 500
...communicate with a management interface address 192.168.1.250 connecting to be statically blocked or excluded. This firewall interface is reached. For SNMP Community enter the Write Community String configured for example) from being accidentally blocked out. 12.3.3. Web Interface Add a new switch ... host (in network range 192.168.2.0/24 for the switch 4. Go to ZoneDefense > Switches > Add > ZoneDefense switch 2. A D-Link switch model DES-3226S is also possible to prevent the firewall from accessing the switch completely. ZoneDefense As a complement to threshold rules, ...
...communicate with a management interface address 192.168.1.250 connecting to be statically blocked or excluded. This firewall interface is reached. For SNMP Community enter the Write Community String configured for example) from being accidentally blocked out. 12.3.3. Web Interface Add a new switch ... host (in network range 192.168.2.0/24 for the switch 4. Go to ZoneDefense > Switches > Add > ZoneDefense switch 2. A D-Link switch model DES-3226S is also possible to prevent the firewall from accessing the switch completely. ZoneDefense As a complement to threshold rules, ...
Product Manual
Page 531
... router attack BGP router protocol RFC protocol and implementation Java RMI Rsync Generic scanners Nessus Scanner Anti-virus solutions Internet Security Systems software McAfee Symantec AV solution SMB Error SMB Exploit SMB attacks NetBIOS attacks SMB worms SMTP command attack Denial ...of Service for SMTP SMTP protocol and implementation SMTP Overflow SPAM SNMP encoding SNMP protocol/implementation SOCKS protocol and implementation SSH protocol and implementation Password guess and related login attacks OpenSSH Server SSL protocol...
... router attack BGP router protocol RFC protocol and implementation Java RMI Rsync Generic scanners Nessus Scanner Anti-virus solutions Internet Security Systems software McAfee Symantec AV solution SMB Error SMB Exploit SMB attacks NetBIOS attacks SMB worms SMTP command attack Denial ...of Service for SMTP SMTP protocol and implementation SMTP Overflow SPAM SNMP encoding SNMP protocol/implementation SOCKS protocol and implementation SSH protocol and implementation Password guess and related login attacks OpenSSH Server SSL protocol...
Product Manual
Page 537
.... Protocols: HTTP, FTP, TFTP. Layer 6 - Layer 4 - DNS, SMTP, Telnet, SNMP and similar. Protocols: TCP, UDP and similar. Data-Link Layer Creates frames of the hierarchy. The model is passed from an application in one computer, proceeding...2 - Layer number Layer 7 Layer 6 Layer 5 Layer 4 Layer 3 Layer 2 Layer 1 Layer purpose Application Presentation Session Transport Network Data-Link Physical Figure D.1. Layer 5 - It categorizes different protocols for achieving an application can understand. Protocols: Ethernet, PPP and similar. Protocols: NetBIOS,...
.... Protocols: HTTP, FTP, TFTP. Layer 6 - Layer 4 - DNS, SMTP, Telnet, SNMP and similar. Protocols: TCP, UDP and similar. Data-Link Layer Creates frames of the hierarchy. The model is passed from an application in one computer, proceeding...2 - Layer number Layer 7 Layer 6 Layer 5 Layer 4 Layer 3 Layer 2 Layer 1 Layer purpose Application Presentation Session Transport Network Data-Link Physical Figure D.1. Layer 5 - It categorizes different protocols for achieving an application can understand. Protocols: Ethernet, PPP and similar. Protocols: NetBIOS,...
Product Manual
Page 538
... high availability, 495 ICMP, 513 IP level, 504 IPsec, 421 L2TP/PPTP, 430 length limit, 518 logging, 59 RADIUS, 63 remote management, 48 routing, 156 SNMP, 68 state, 514 TCP level, 508 transparent mode, 218 VLAN, 100 Alarm Repetition Interval setting, 59 ALG, 240 deploying, 240 FTP, 244 H.323, 275 HTTP...
... high availability, 495 ICMP, 513 IP level, 504 IPsec, 421 L2TP/PPTP, 430 length limit, 518 logging, 59 RADIUS, 63 remote management, 48 routing, 156 SNMP, 68 state, 514 TCP level, 508 transparent mode, 218 VLAN, 100 Alarm Repetition Interval setting, 59 ALG, 240 deploying, 240 FTP, 244 H.323, 275 HTTP...
Product Manual
Page 541
... VPN troubleshooting, 414, 439 Illegal Fragments setting, 520 Initial Silence (HA) setting, 495 insertion attack prevention, 318 Interface Alias (SNMP) setting, 69 Interface Description (SNMP) setting, 69 interfaces, 90 disabling, 91 groups, 107 loopback, 90, 91 physical, 90 internet key exchange (see IKE) ...) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting...
... VPN troubleshooting, 414, 439 Illegal Fragments setting, 520 Initial Silence (HA) setting, 495 insertion attack prevention, 318 Interface Alias (SNMP) setting, 69 Interface Description (SNMP) setting, 69 interfaces, 90 disabling, 91 groups, 107 loopback, 90, 91 physical, 90 internet key exchange (see IKE) ...) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting...
Product Manual
Page 543
...149 metrics, 143, 173 monitoring, 151 principles, 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port forwarding...SYN flood protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions, 256 header...
...149 metrics, 143, 173 monitoring, 151 principles, 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port forwarding...SYN flood protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions, 256 header...