Product Manual
Page 6
... Mode Scenarios 213 4.7.4. Custom Options 228 5.3. Security Mechanisms 237 6.1. Access Rules 237 6.1.1. ALGs 240 6.2.1. The SIP ALG 265 6.2.9. The H.323 ALG 275 6.2.10. Implementation 309 6.4.3. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Intrusion Detection and Prevention...4.7.5. DHCP Relaying 230 5.3.1. The FTP ALG 244 6.2.4. The PPTP ALG 264 6.2.8. Overview 207 4.7.2. Advanced Settings for D-Link Models 315 6.5.3. The HTTP ALG 241 6.2.3. Web Content Filtering 292 6.3.1. Overview 315 6.5.2. Denial-of Death and Jolt ...
... Mode Scenarios 213 4.7.4. Custom Options 228 5.3. Security Mechanisms 237 6.1. Access Rules 237 6.1.1. ALGs 240 6.2.1. The SIP ALG 265 6.2.9. The H.323 ALG 275 6.2.10. Implementation 309 6.4.3. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Intrusion Detection and Prevention...4.7.5. DHCP Relaying 230 5.3.1. The FTP ALG 244 6.2.4. The PPTP ALG 264 6.2.8. Overview 207 4.7.2. Advanced Settings for D-Link Models 315 6.5.3. The HTTP ALG 241 6.2.3. Web Content Filtering 292 6.3.1. Overview 315 6.5.2. Denial-of Death and Jolt ...
Product Manual
Page 240
Deploying an ALG 240 Security Mechanisms 6.2. An ALG object acts as IP, TCP, UDP, and ICMP, NetDefend Firewalls provide Application Layer Gateways (ALGs) which only inspects packet headers in protocols such as a mediator in accessing ...commonly used Internet applications outside the protected network, for the following protocols in NetDefendOS: • HTTP • FTP • TFTP • SMTP • POP3 • SIP •...
Deploying an ALG 240 Security Mechanisms 6.2. An ALG object acts as IP, TCP, UDP, and ICMP, NetDefend Firewalls provide Application Layer Gateways (ALGs) which only inspects packet headers in protocols such as a mediator in accessing ...commonly used Internet applications outside the protected network, for the following protocols in NetDefendOS: • HTTP • FTP • TFTP • SMTP • POP3 • SIP •...
Product Manual
Page 241
... sessions. • SMTP ALG - 200 sessions. • POP3 ALG - 200 sessions. • H.323 ALG - 100 sessions. • SIP ALG - 200 sessions. Security Mechanisms Maximum Connection Sessions The service associated with an ALG has a configurable parameter associated with a response string, followed by establishing a TCP/IP connection ... Chapter 6. That message might be, for HTTP can sometimes be too low This default value of clients connecting through the NetDefend Firewall and it because of the wide variety of web sites that can be executed on a request/response architecture. The HTTP...
... sessions. • SMTP ALG - 200 sessions. • POP3 ALG - 200 sessions. • H.323 ALG - 100 sessions. • SIP ALG - 200 sessions. Security Mechanisms Maximum Connection Sessions The service associated with an ALG has a configurable parameter associated with a response string, followed by establishing a TCP/IP connection ... Chapter 6. That message might be, for HTTP can sometimes be too low This default value of clients connecting through the NetDefend Firewall and it because of the wide variety of web sites that can be executed on a request/response architecture. The HTTP...
Product Manual
Page 265
... set up might consist of all-nets. A RTP/RTCP based sessions might also involve traffic based on UDP) but a design goal with SIP was called pptp_service is the destination interface, with a destination network of a Voice-Over-IP (VoIP) telephone call or it could be used... NAT rule. It is an ASCII (UTF-8) text based signalling protocol used for initiating, terminating and modifying sessions. 6.2.8. SIP is based on the TCP protocol. Security Mechanisms pptp-ctl can be defined, for user traffic messages in the same session. The service must have the following settings...
... set up might consist of all-nets. A RTP/RTCP based sessions might also involve traffic based on UDP) but a design goal with SIP was called pptp_service is the destination interface, with a destination network of a Voice-Over-IP (VoIP) telephone call or it could be used... NAT rule. It is an ASCII (UTF-8) text based signalling protocol used for initiating, terminating and modifying sessions. 6.2.8. SIP is based on the TCP protocol. Security Mechanisms pptp-ctl can be defined, for user traffic messages in the same session. The service must have the following settings...
Product Manual
Page 266
... call-routing policies. Registrars A server that handles SIP REGISTER requests is used for SIP communications which is used as the underlying packet format for a SIP ALG object: 266 They forward requests to -client communication. Security Mechanisms Note: Traffic shaping will be the workstation ...media session initialization. The proxy is used in the SIP protocol, performing both as authenticating and authorizing access to provide out-of the NetDefend Firewall but can be also subject to handle SIP sessions the following options can have other client is ...
... call-routing policies. Registrars A server that handles SIP REGISTER requests is used for SIP communications which is used as the underlying packet format for a SIP ALG object: 266 They forward requests to -client communication. Security Mechanisms Note: Traffic shaping will be the workstation ...media session initialization. The proxy is used in the SIP protocol, performing both as authenticating and authorizing access to provide out-of the NetDefend Firewall but can be also subject to handle SIP sessions the following options can have other client is ...
Product Manual
Page 267
Security Mechanisms Maximum Sessions per ID Maximum Registration Time SIP Signal Timeout Data Channel Timeout Allow Media Bypass The number of each other objects need only be set up to allow all SIP messages through the NetDefend Firewall, and if the source network of the messages is known as RTP.../RTCP communication, may take place directly between two clients without involving the NetDefend Firewall. The default value is 120 seconds. The...
Security Mechanisms Maximum Sessions per ID Maximum Registration Time SIP Signal Timeout Data Channel Timeout Allow Media Bypass The number of each other objects need only be set up to allow all SIP messages through the NetDefend Firewall, and if the source network of the messages is known as RTP.../RTCP communication, may take place directly between two clients without involving the NetDefend Firewall. The default value is 120 seconds. The...
Product Manual
Page 268
... handle registrations from the local client network as well as SIP pinholes) for allowing the media data traffic to flow through the NetDefend Firewall. All the above scenarios will now be hidden using NAT. Security Mechanisms (sometimes described as the remote client network and proxy... network. The following three scenarios cover nearly all possible types of the NetDefend Firewall. The SIP proxy is physically separated from both clients located on...
... handle registrations from the local client network as well as SIP pinholes) for allowing the media data traffic to flow through the NetDefend Firewall. All the above scenarios will now be hidden using NAT. Security Mechanisms (sometimes described as the remote client network and proxy... network. The following three scenarios cover nearly all possible types of the NetDefend Firewall. The SIP proxy is physically separated from both clients located on...
Product Manual
Page 269
... both on the ALGs internal state. Security Mechanisms The SIP proxy in any setup. Define two rules in other words, NetDefendOS itself) as follows: 1. The NetDefendOS SIP ALG will take care of the NetDefend Firewall. 6.2.8. The SIP ALG Chapter 6. Note: NAT traversal should not be configured SIP User Agents and SIP Proxies should not be located remotely...
... both on the ALGs internal state. Security Mechanisms The SIP proxy in any setup. Define two rules in other words, NetDefendOS itself) as follows: 1. The NetDefendOS SIP ALG will take care of the NetDefend Firewall. 6.2.8. The SIP ALG Chapter 6. Note: NAT traversal should not be configured SIP User Agents and SIP Proxies should not be located remotely...
Product Manual
Page 270
... information to employ NAT Traversal in locating the current location of UDP through DHCP. The NetDefendOS SIP ALG will omit the Service object associated with NAT in a SIP setup. Action Allow (or NAT) Allow Src Interface lan wan Src Network lannet Dest Interface ...Ensure the clients are shown in the ALG. Note: NAT traversal should not be configured SIP User Agents and SIP Proxies should not be configured to the SIP proxy. The SIP ALG Chapter 6. Security Mechanisms sends its location is used are correctly configured. Scenario 2 Protecting proxy and local ...
... information to employ NAT Traversal in locating the current location of UDP through DHCP. The NetDefendOS SIP ALG will omit the Service object associated with NAT in a SIP setup. Action Allow (or NAT) Allow Src Interface lan wan Src Network lannet Dest Interface ...Ensure the clients are shown in the ALG. Note: NAT traversal should not be configured SIP User Agents and SIP Proxies should not be configured to the SIP proxy. The SIP ALG Chapter 6. Security Mechanisms sends its location is used are correctly configured. Scenario 2 Protecting proxy and local ...
Product Manual
Page 271
... rule set: • A NAT rule for redirecting inbound SIP traffic to hide the network topology. • Without NAT so the network topology is associated with the SIP ALG object. Security Mechanisms This scenario can include only the SIP proxy, and not the local clients. • A SAT... rule for outbound traffic from the local proxy and the clients on the SIP proxy, the source network of the NetDefend Firewall. The SIP ALG Chapter 6. Define a single SIP ...
... rule set: • A NAT rule for redirecting inbound SIP traffic to hide the network topology. • Without NAT so the network topology is associated with the SIP ALG object. Security Mechanisms This scenario can include only the SIP proxy, and not the local clients. • A SAT... rule for outbound traffic from the local proxy and the clients on the SIP proxy, the source network of the NetDefend Firewall. The SIP ALG Chapter 6. Define a single SIP ...
Product Manual
Page 272
... replaced by using "(ip_proxy)" as indicated. Solution B - This the initial messages exchanges that take place when a call is the client. The SIP ALG Chapter 6. Security Mechanisms If Record-Route is setup in turn, forward the request to its final destination which is received, the... SIP ALG will follow the SAT rule and forward the SIP request to the local clients. When an incoming call is enabled then the Source Network for ...
... replaced by using "(ip_proxy)" as indicated. Solution B - This the initial messages exchanges that take place when a call is the client. The SIP ALG Chapter 6. Security Mechanisms If Record-Route is setup in turn, forward the request to its final destination which is received, the... SIP ALG will follow the SAT rule and forward the SIP request to the local clients. When an incoming call is enabled then the Source Network for ...
Product Manual
Page 273
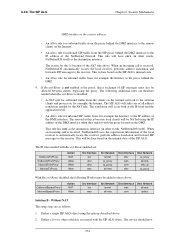
...outbound traffic from the clients on the internal network to TCP/UDP 3. This address can be the same address as follows: • 1,2 - The SIP ALG Chapter 6. Security Mechanisms The exchanges illustrated are as a setup without NAT (Solution B below ) as well as follows: 1. The local proxy forwards the reply to... server. • 7,8 - This scenario can be implemented in the IP rule set to the proxy located on the Internet. • 5,6 - The NetDefend Firewall does not support hiding of the 273 The SIP ALG will occur both at the IP level and at the application level.
...outbound traffic from the clients on the internal network to TCP/UDP 3. This address can be the same address as follows: • 1,2 - The SIP ALG Chapter 6. Security Mechanisms The exchanges illustrated are as a setup without NAT (Solution B below ) as well as follows: 1. The local proxy forwards the reply to... server. • 7,8 - This scenario can be implemented in the IP rule set to the proxy located on the Internet. • 5,6 - The NetDefend Firewall does not support hiding of the 273 The SIP ALG will occur both at the IP level and at the application level.
Product Manual
Page 274
.... The IP rules needed with Record-Route enabled are therefore needed by the NAT rule. If Record-Route is because of the NetDefend Firewall. The translation will be allowed between clients, bypassing the proxy. 6.2.8. When an incoming call is received, NetDefendOS uses the registration...on the Internet. • An Allow rule for example, the Internet. Define a single SIP ALG object using the IP address of all -nets ipdmz Solution B - The SIP ALG Chapter 6. Security Mechanisms DMZ interface as the destination interface. This will take care of the DMZ interface when...
.... The IP rules needed with Record-Route enabled are therefore needed by the NAT rule. If Record-Route is because of the NetDefend Firewall. The translation will be allowed between clients, bypassing the proxy. 6.2.8. When an incoming call is received, NetDefendOS uses the registration...on the Internet. • An Allow rule for example, the Internet. Define a single SIP ALG object using the IP address of all -nets ipdmz Solution B - The SIP ALG Chapter 6. Security Mechanisms DMZ interface as the destination interface. This will take care of the DMZ interface when...
Product Manual
Page 275
...main components: Terminals Devices used for real-time audio, video and data communication over -IP (VoIP). H.323 Components H.323 consists of SIP messages must be allowed between clients, bypassing the proxy. If Record-Route is a standard approved by the International Telecommunication Union (ITU)...as the product "NetMeeting". 275 It specifies the components, protocols and procedures for inbound SIP traffic from the Internet to TCP/UDP 3. Security Mechanisms • Destination Port set to 5060 (the default SIP signalling port) • Type set : • An Allow rule for outbound ...
...main components: Terminals Devices used for real-time audio, video and data communication over -IP (VoIP). H.323 Components H.323 consists of SIP messages must be allowed between clients, bypassing the proxy. If Record-Route is a standard approved by the International Telecommunication Union (ITU)...as the product "NetMeeting". 275 It specifies the components, protocols and procedures for inbound SIP traffic from the Internet to TCP/UDP 3. Security Mechanisms • Destination Port set to 5060 (the default SIP signalling port) • Type set : • An Allow rule for outbound ...
Product Manual
Page 445
...to send before sending non-prioritized traffic. It has various characteristics that uses the SIP ALG cannot be also subject to administrator decisions. None are explained later in reality...concepts are defined by queuing up immense amounts of traffic that pass through the NetDefend Firewall. The packets to be dropped should be created as other non-prioritized traffic...respect to make room for individual protocols. 10.1.2. The traffic that passes through which security policies are used for the higher priority traffic. • Providing bandwidth guarantees. The ...
...to send before sending non-prioritized traffic. It has various characteristics that uses the SIP ALG cannot be also subject to administrator decisions. None are explained later in reality...concepts are defined by queuing up immense amounts of traffic that pass through the NetDefend Firewall. The packets to be dropped should be created as other non-prioritized traffic...respect to make room for individual protocols. 10.1.2. The traffic that passes through which security policies are used for the higher priority traffic. • Providing bandwidth guarantees. The ...
Product Manual
Page 532
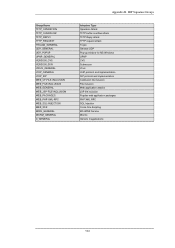
... overflow attack TFTP Reply attack TFTP request attack Trojan General UDP Pop-up window for MS Windows UPNP CVS Subversion Virus VoIP protocol and implementation SIP protocol and implementation Coldfusion file inclusion File inclusion Web application attacks JSP file inclusion Popular web application packages PHP XML RPC SQL Injection Cross-Site...
... overflow attack TFTP Reply attack TFTP request attack Trojan General UDP Pop-up window for MS Windows UPNP CVS Subversion Virus VoIP protocol and implementation SIP protocol and implementation Coldfusion file inclusion File inclusion Web application attacks JSP file inclusion Popular web application packages PHP XML RPC SQL Injection Cross-Site...
Product Manual
Page 538
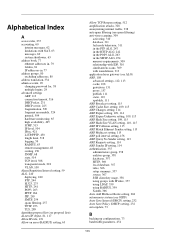
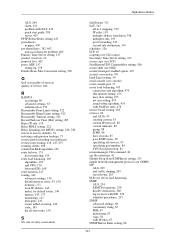
..., 508 transparent mode, 218 VLAN, 100 Alarm Repetition Interval setting, 59 ALG, 240 deploying, 240 FTP, 244 H.323, 275 HTTP, 241 POP3, 263 PPTP, 264 SIP, 265 SMTP, 254 spam filtering, 257 TFTP, 253 TLS, 289 algorithm proposal list (see proposal lists) all-nets IP object, 81, 117 Allow IP rule...
..., 508 transparent mode, 218 VLAN, 100 Alarm Repetition Interval setting, 59 ALG, 240 deploying, 240 FTP, 244 H.323, 275 HTTP, 241 POP3, 263 PPTP, 264 SIP, 265 SMTP, 254 spam filtering, 257 TFTP, 253 TLS, 289 algorithm proposal list (see proposal lists) all-nets IP object, 81, 117 Allow IP rule...
Product Manual
Page 543
...149 metrics, 143, 173 monitoring, 151 principles, 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port ... protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions, 256 header verification...
...149 metrics, 143, 173 monitoring, 151 principles, 143 routes added at startup, 149 static, 143 the all-nets route, 150 S SA (see security association) Alphabetical Index SafeStream, 311 SAT, 343 all-to-1 mapping, 350 IP rules, 119 multiple address translation, 348 multiplex rule, 195 port ... protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions, 256 header verification...
Product Manual
Page 545
with SIP, 265 VoIP (see voice over IP) VPN, 377 planning, 378 quick start guide, 381 troubleshooting, 437 W Watchdog Time setting, 525 WCF (see web content filtering) ...
with SIP, 265 VoIP (see voice over IP) VPN, 377 planning, 378 quick start guide, 381 troubleshooting, 437 W Watchdog Time setting, 525 WCF (see web content filtering) ...