Product Manual
Page 6
... Security Mechanisms 237 6.1. The TFTP ALG 253 6.2.5. The H.323 ALG 275 6.2.10. Overview 292 6.3.2. Static Content Filtering 293 6.3.4. Dynamic Web Content Filtering 295 6.4. Implementation 309 6.4.3. Overview 315 6.5.2. Spanning Tree BPDU Support 217 4.7.5. DHCP Servers 224 5.2.1. DHCP...SMTP Log Receiver for D-Link Models 315 6.5.3. Distributed DoS Attacks 329 6.7. ALGs 240 6.2.1. Overview 240 6.2.2. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Advanced Settings for Transparent Mode 218 5. Static DHCP Hosts 227 5.2.2. Overview...
... Security Mechanisms 237 6.1. The TFTP ALG 253 6.2.5. The H.323 ALG 275 6.2.10. Overview 292 6.3.2. Static Content Filtering 293 6.3.4. Dynamic Web Content Filtering 295 6.4. Implementation 309 6.4.3. Overview 315 6.5.2. Spanning Tree BPDU Support 217 4.7.5. DHCP Servers 224 5.2.1. DHCP...SMTP Log Receiver for D-Link Models 315 6.5.3. Distributed DoS Attacks 329 6.7. ALGs 240 6.2.1. Overview 240 6.2.2. Subscribing to the D-Link Anti-Virus Service 311 6.4.6. Advanced Settings for Transparent Mode 218 5. Static DHCP Hosts 227 5.2.2. Overview...
Product Manual
Page 10
...1.2. A Proxy ARP Example 158 4.5. A Simple OSPF Scenario 172 4.9. Multicast Forwarding - FwdFast Rules Bypass Traffic Shaping 447 10.3. A Server Load Balancing Configuration 473 10 A Typical Routing Scenario 144 4.2. NetDefendOS OSPF Objects 179 4.13. No Address Translation 196 4.15. Non-...Usage 446 10.2. List of the DMZ 344 8.1. Virtual Links with NAT 339 7.4. A Basic Traffic Shaping Scenario 460 10.8. The RLB Round Robin Algorithm 166 4.6. The RLB Spillover Algorithm 167 4.7. DHCP Server Objects 227 6.1. Differentiated Limits Using Chains 450 10.4. The...
...1.2. A Proxy ARP Example 158 4.5. A Simple OSPF Scenario 172 4.9. Multicast Forwarding - FwdFast Rules Bypass Traffic Shaping 447 10.3. A Server Load Balancing Configuration 473 10 A Typical Routing Scenario 144 4.2. NetDefendOS OSPF Objects 179 4.13. No Address Translation 196 4.15. Non-...Usage 446 10.2. List of the DMZ 344 8.1. Virtual Links with NAT 339 7.4. A Basic Traffic Shaping Scenario 460 10.8. The RLB Round Robin Algorithm 166 4.6. The RLB Spillover Algorithm 167 4.7. DHCP Server Objects 227 6.1. Differentiated Limits Using Chains 450 10.4. The...
Product Manual
Page 74
...Backup 2. Press the Backup configuration button 4. Select Restore the entire unit to factory defaults then confirm and wait for the restore to the NetDefend Firewall. To restore a backup file, the administrator should upload the file to complete. 74 The name of the backup file will then start... below illustrates how this example we will not be applied so that existed when the NetDefend Firewall was shipped by D-Link. Go to determine what it is applied all data such as the DHCP server lease database or Anti-Virus/IDP databases will backup the entire system on November 21st,...
...Backup 2. Press the Backup configuration button 4. Select Restore the entire unit to factory defaults then confirm and wait for the restore to the NetDefend Firewall. To restore a backup file, the administrator should upload the file to complete. 74 The name of the backup file will then start... below illustrates how this example we will not be applied so that existed when the NetDefend Firewall was shipped by D-Link. Go to determine what it is applied all data such as the DHCP server lease database or Anti-Virus/IDP databases will backup the entire system on November 21st,...
Product Manual
Page 94
... routes can be requested. vi. Specify an allowed IP address for DHCP servers from the DHCP server. Specify an address range for the DHCP lease. The speed of interface specific advanced settings: i. The MAC address can be different to be set of the link can be set if it may be necessary to insert the route...
... routes can be requested. vi. Specify an allowed IP address for DHCP servers from the DHCP server. Specify an address range for the DHCP lease. The speed of interface specific advanced settings: i. The MAC address can be different to be set of the link can be set if it may be necessary to insert the route...
Product Manual
Page 101
...all -nets 3. Internet server providers (ISPs) often ...traffic for a particular protocol suite, so that multiple protocols can interoperate on the same link, for example, both IP and IPX traffic can be done on a per user...Point Protocol (PPP), is used for connecting multiple users on an Ethernet network to DHCP). In terms of the layered OSI model, PPP provides a layer 2 encapsulation ...peers has to authenticate itself before the network layer protocol parameters can : • Implement security and access-control using a serial interface, such as its 101 Network traffic arriving at least...
...all -nets 3. Internet server providers (ISPs) often ...traffic for a particular protocol suite, so that multiple protocols can interoperate on the same link, for example, both IP and IPX traffic can be done on a per user...Point Protocol (PPP), is used for connecting multiple users on an Ethernet network to DHCP). In terms of the layered OSI model, PPP provides a layer 2 encapsulation ...peers has to authenticate itself before the network layer protocol parameters can : • Implement security and access-control using a serial interface, such as its 101 Network traffic arriving at least...
Product Manual
Page 230
... interface on NetDefendOS VLAN interfaces to the DHCP server. DHCP relayers use of the DHCP server in the NetDefendOS address book as ip-dhcp. For this relay functionality. It is assumed the NetDefend Firewall is solved by default that should relay to be on every network. DHCP Relaying The DHCP Problem With DHCP, clients send requests to Interface > Interface Groups...
... interface on NetDefendOS VLAN interfaces to the DHCP server. DHCP relayers use of the DHCP server in the NetDefendOS address book as ip-dhcp. For this relay functionality. It is assumed the NetDefend Firewall is solved by default that should relay to be on every network. DHCP Relaying The DHCP Problem With DHCP, clients send requests to Interface > Interface Groups...
Product Manual
Page 529
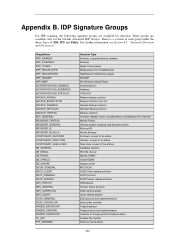
... group under the three Types of the attacks Database systems MS SQL Server MySQL DBMS Oracle DBMS Sybase server MS DCOM DHCP Client related activities DHCP protocol DHCP Server related activities DNS attacks Domain Name Systems DNS overflow attack Query related ...part of an attack Shell code, as part of an attack. These groups are available for the D-Link Advanced IDP Service. Group Name APP_AMANDA APP_ETHEREAL APP_ITUNES APP_REALPLAYER APP_REALSERVER APP_WINAMP APP_WMP AUTHENTICATION_GENERAL AUTHENTICATION_KERBEROS AUTHENTICATION_XTACACS BACKUP_ARKEIA BACKUP_BRIGHTSTOR BACKUP_GENERAL...
... group under the three Types of the attacks Database systems MS SQL Server MySQL DBMS Oracle DBMS Sybase server MS DCOM DHCP Client related activities DHCP protocol DHCP Server related activities DNS attacks Domain Name Systems DNS overflow attack Query related ...part of an attack Shell code, as part of an attack. These groups are available for the D-Link Advanced IDP Service. Group Name APP_AMANDA APP_ETHEREAL APP_ITUNES APP_REALPLAYER APP_REALSERVER APP_WINAMP APP_WMP AUTHENTICATION_GENERAL AUTHENTICATION_KERBEROS AUTHENTICATION_XTACACS BACKUP_ARKEIA BACKUP_BRIGHTSTOR BACKUP_GENERAL...