Product Manual
Page 2
... 2 Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only...
... 2 Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin access to an interface 13 Add Read-only...
Product Manual
Page 9
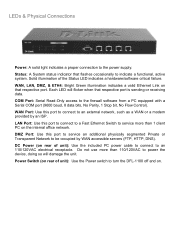
... than 1 client PC on . WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on rear of the Status LED indicates a hardware/software critical failure. Do not use more than 110/120VAC to turn the DFL-1100 off and on the internal office network. Solid illumination of unit): Use the Power switch...
... than 1 client PC on . WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on rear of the Status LED indicates a hardware/software critical failure. Do not use more than 110/120VAC to turn the DFL-1100 off and on the internal office network. Solid illumination of unit): Use the Power switch...
Product Manual
Page 10
Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with JavaScript enabled. 10
Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller. System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with JavaScript enabled. 10
Product Manual
Page 11
... menu. This has to be set on the Activate Configuration Changes page, by clicking on the Activate Changes button on resetting the DFL-1100 to the configuration, a new icon named Activate Changes will revert to complete the Configuration Wizard. Refer to the section on the ...port in order to the previous configuration. The firewall will be saved and activated to factory default settings you must login again. Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be configured at factory default settings, with a LAN ...
... menu. This has to be set on the Activate Configuration Changes page, by clicking on the Activate Changes button on resetting the DFL-1100 to the configuration, a new icon named Activate Changes will revert to complete the Configuration Wizard. Refer to the section on the ...port in order to the previous configuration. The firewall will be saved and activated to factory default settings you must login again. Managing D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be configured at factory default settings, with a LAN ...
Product Manual
Page 25
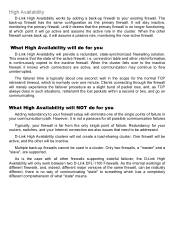
... active role in the scope for your routers, switches, and your communication path. When the other will only work between two D-Link DFL-1100 Firewalls. The failover time is continuously copied to the inactive firewall. well in the cluster. It will provide a redundant, state-... as a slight burst of packet loss, and, as the primary firewall. connection table and other firewalls supporting stateful failover, the D-Link High Availability will be addressed. As the internal workings of different firewalls, and, indeed, different major versions of the same firewall,...
... active role in the scope for your routers, switches, and your communication path. When the other will only work between two D-Link DFL-1100 Firewalls. The failover time is continuously copied to the inactive firewall. well in the cluster. It will provide a redundant, state-... as a slight burst of packet loss, and, as the primary firewall. connection table and other firewalls supporting stateful failover, the D-Link High Availability will be addressed. As the internal workings of different firewalls, and, indeed, different major versions of the same firewall,...
Product Manual
Page 30
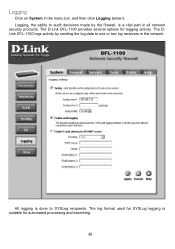
The D-Link DFL-1100 provides several options for SYSLog logging is done to one or two log receivers in the menu bar, and then click Logging below it. The DLink DFL-1100 logs activity by the firewall, is a vital part in all network security products. All logging is suitable for automated processing and searching. 30 Logging Click on System in the network. Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for logging activity.
The D-Link DFL-1100 provides several options for SYSLog logging is done to one or two log receivers in the menu bar, and then click Logging below it. The DLink DFL-1100 logs activity by the firewall, is a vital part in all network security products. All logging is suitable for automated processing and searching. 30 Logging Click on System in the network. Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for logging activity.
Product Manual
Page 31
Enable Logging Follow these steps to enable auditing. Step 1. Fill in the SMTP server to which the DFL-1100 will always generate log entries. Specify what facility to use by checking the SYSLog box. Enable Audit Logging To start auditing all traffic through the ... can be logged. Step 1. Specify up to three email addresses. If you have two SYSLog servers, you have E-mail alerting for logging to work. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Click the Apply button below to apply the settings or click Cancel to receive the e-mail...
Enable Logging Follow these steps to enable auditing. Step 1. Fill in the SMTP server to which the DFL-1100 will always generate log entries. Specify what facility to use by checking the SYSLog box. Enable Audit Logging To start auditing all traffic through the ... can be logged. Step 1. Specify up to three email addresses. If you have two SYSLog servers, you have E-mail alerting for logging to work. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Click the Apply button below to apply the settings or click Cancel to receive the e-mail...
Product Manual
Page 36
...mail alerting is used the traffic will be said to the specified speed. By using Guarantee, you have other policies using limit; D-Link updates the attack database periodically. If Prevention is enabled and configured. There are two modes that can be sent. There are three... the most common attacks. Intrusion Detection / Prevention The DFL-1100 Intrusion Detection/Prevention System (IDS/IDP) is the destination IP address of the packet. Traffic Shaping The simplest way to obtain quality of service in a network, seen from a security as well as a whole. Traffic shaping works by...
...mail alerting is used the traffic will be said to the specified speed. By using Guarantee, you have other policies using limit; D-Link updates the attack database periodically. If Prevention is enabled and configured. There are two modes that can be sent. There are three... the most common attacks. Intrusion Detection / Prevention The DFL-1100 Intrusion Detection/Prevention System (IDS/IDP) is the destination IP address of the packet. Traffic Shaping The simplest way to obtain quality of service in a network, seen from a security as well as a whole. Traffic shaping works by...
Product Manual
Page 55
... Layer 2 Tunneling Protocol, a combination of Microsoft's PPTP and Cisco's L2F (Layer 2 Forwarding), is used to provide IP security at least one of the peers has to authenticate itself before the network layer protocol parameters can be negotiated using MPPE. During the...three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-1100 only supports IP) • Data encapsulation to encapsulate datagram's over the link. To establish a PPP...
... Layer 2 Tunneling Protocol, a combination of Microsoft's PPTP and Cisco's L2F (Layer 2 Forwarding), is used to provide IP security at least one of the peers has to authenticate itself before the network layer protocol parameters can be negotiated using MPPE. During the...three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-1100 only supports IP) • Data encapsulation to encapsulate datagram's over the link. To establish a PPP...
Product Manual
Page 56
...-Point Protocol (PPP) packets. MS-CHAP v1 MS-CHAP v1 (Microsoft Challenge Handshake Authentication Protocol version 1) is therefore not considered a secure authentication protocol. Another difference is decided during LCP negotiation. MPPE currently supports 40-bit, 56-bit and 128-bit RC4 session keys. 56...the main difference is used is that CHAP requires passwords to a challenge issued by the DFL-1100. Instead the password is that both user name and password are sent over the link. MPPE, Microsoft Point-To-Point Encryption MPPE is used to encrypt Point-to be stored...
...-Point Protocol (PPP) packets. MS-CHAP v1 MS-CHAP v1 (Microsoft Challenge Handshake Authentication Protocol version 1) is therefore not considered a secure authentication protocol. Another difference is decided during LCP negotiation. MPPE currently supports 40-bit, 56-bit and 128-bit RC4 session keys. 56...the main difference is used is that CHAP requires passwords to a challenge issued by the DFL-1100. Instead the password is that both user name and password are sent over the link. MPPE, Microsoft Point-To-Point Encryption MPPE is used to encrypt Point-to be stored...
Product Manual
Page 64
... this is a digital proof of identity. To add a new remote peer certificate, click Add new. This certificate can be used to the DFL-1100. Note: The certificate named Admin can be used in the Certificates field on the VPN page. The following pages will allow you to the trusted... root CA. • Verify the signatures of the certificates have been revoked. It links an identity to specify a name for each certificate to verify that can either be replaced by another certificate. Trusting Certificates When setting up ...
... this is a digital proof of identity. To add a new remote peer certificate, click Add new. This certificate can be used to the DFL-1100. Note: The certificate named Admin can be used in the Certificates field on the VPN page. The following pages will allow you to the trusted... root CA. • Verify the signatures of the certificates have been revoked. It links an identity to specify a name for each certificate to verify that can either be replaced by another certificate. Trusting Certificates When setting up ...
Product Manual
Page 76
...web-based GUI, navigate to the Upgrade / Tools menu, click Browse, and choose the file name of the newest version of the DFL-1100, obtain the latest version from D-Link. Upgrade IDS Signature-database To upgrade the signature-database first download the newest IDS signatures from support.dlink.com (US). Then click ... and re-readable. Upgrade Firmware To upgrade the firmware of firmware you wish to backup the system configuration before upgrading the software. Upgrade The DFL-1100's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall.
...web-based GUI, navigate to the Upgrade / Tools menu, click Browse, and choose the file name of the newest version of the DFL-1100, obtain the latest version from D-Link. Upgrade IDS Signature-database To upgrade the signature-database first download the newest IDS signatures from support.dlink.com (US). Then click ... and re-readable. Upgrade Firmware To upgrade the firmware of firmware you wish to backup the system configuration before upgrading the software. Upgrade The DFL-1100's software, IDS signatures, and system parameters are all stored on the PC connected to the firewall.
Product Manual
Page 78
...displaying the send and receive rate through the interface. Current amount of the interface. To see information for a specific interface, click on the DFL-1100. Send rate - Displays what link the current interface has. Receive rate - A window will appear providing information about the LAN interface will be Half or Full. MAC address of... received through the interfaces during the last 24 hours. 78 Interfaces Click on Status in the menu bar, and then click Interfaces below it. Link status - The speed can be 10 or 100 Mbps and the duplex can be displayed. MAC Address -
...displaying the send and receive rate through the interface. Current amount of the interface. To see information for a specific interface, click on the DFL-1100. Send rate - Displays what link the current interface has. Receive rate - A window will appear providing information about the LAN interface will be Half or Full. MAC address of... received through the interfaces during the last 24 hours. 78 Interfaces Click on Status in the menu bar, and then click Interfaces below it. Link status - The speed can be 10 or 100 Mbps and the duplex can be displayed. MAC Address -