Software Guide
Page 34
... proximity and interconnection media, including Ethernet, Fast Ethernet, Fast EtherChannel, small form-factor pluggable (SFP) modules, Gigabit Ethernet, and Gigabit EtherChannel connections. Downloading an image to accomplish specific tasks. - Simplifying and minimizing switch and switch cluster management from a single graphical interface without needing to remember command-line interface (CLI) commands to a switch. - For information about Express Setup, see the getting started guide. and switch-level monitoring and troubleshooting, and multiple switch software upgrades. -
... proximity and interconnection media, including Ethernet, Fast Ethernet, Fast EtherChannel, small form-factor pluggable (SFP) modules, Gigabit Ethernet, and Gigabit EtherChannel connections. Downloading an image to accomplish specific tasks. - Simplifying and minimizing switch and switch cluster management from a single graphical interface without needing to remember command-line interface (CLI) commands to a switch. - For information about Express Setup, see the getting started guide. and switch-level monitoring and troubleshooting, and multiple switch software upgrades. -
Software Guide
Page 35
... IP version 6 (IPv6) multicast data to clients and routers in a switched network • Multicast VLAN registration (MVR) to continuously send multicast streams in a multicast VLAN while isolating the streams from subscriber VLANs for bandwidth and security reasons • IGMP filtering for controlling the set of Cisco IOS software that uses active traffic monitoring for measuring network performance Support for Cisco IOS IP Service Level Agreements (SLAs) responder that is in the software image. Management Options These are bridged by software •...
... IP version 6 (IPv6) multicast data to clients and routers in a switched network • Multicast VLAN registration (MVR) to continuously send multicast streams in a multicast VLAN while isolating the streams from subscriber VLANs for bandwidth and security reasons • IGMP filtering for controlling the set of Cisco IOS software that uses active traffic monitoring for measuring network performance Support for Cisco IOS IP Service Level Agreements (SLAs) responder that is in the software image. Management Options These are bridged by software •...
Software Guide
Page 36
... TFTP server names) • DHCP relay for forwarding User Datagram Protocol (UDP) broadcasts, including IP address requests, from DHCP clients • DHCP server for automatic assignment of network devices and services. The switch supports a comprehensive set of devices. You can automate initial configurations and configuration updates by using SNMP, see Chapter 2, "Using the Command-Line Interface." • SNMP-SNMP management applications such as HP OpenView or SunNet Manager. You can access the CLI either by connecting your management station directly to the switch console port...
... TFTP server names) • DHCP relay for forwarding User Datagram Protocol (UDP) broadcasts, including IP address requests, from DHCP clients • DHCP server for automatic assignment of network devices and services. The switch supports a comprehensive set of devices. You can automate initial configurations and configuration updates by using SNMP, see Chapter 2, "Using the Command-Line Interface." • SNMP-SNMP management applications such as HP OpenView or SunNet Manager. You can access the CLI either by connecting your management station directly to the switch console port...
Software Guide
Page 39
... support that allows the switch to be a target device for IP SLAs active traffic monitoring • Web authentication to allow a supplicant (client) that carry upstream traffic from Cisco IP Phones • VLAN 1 minimization for limiting and identifying MAC addresses of the stations allowed to access the port OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 1-7 and network security by establishing VLAN groups for high-security users and network resources • Dynamic Trunking Protocol (DTP) for negotiating trunking on a link...
... support that allows the switch to be a target device for IP SLAs active traffic monitoring • Web authentication to allow a supplicant (client) that carry upstream traffic from Cisco IP Phones • VLAN 1 minimization for limiting and identifying MAC addresses of the stations allowed to access the port OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 1-7 and network security by establishing VLAN groups for high-security users and network resources • Dynamic Trunking Protocol (DTP) for negotiating trunking on a link...
Software Guide
Page 48
... for security management. The switches are providing inter-VLAN routing. When an end station in another VLAN, a router routes the traffic to the same VLAN, only one VLAN can place, receive, and control calls from their PCs. The routers also provide firewall services, Network Address Translation (NAT) services, voice-over-IP (VoIP) gateway services, and WAN and Internet access. 1-16 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 In this network, the routers are interconnected through Gigabit interfaces. This ensures connectivity to the Internet, WAN, and...
... for security management. The switches are providing inter-VLAN routing. When an end station in another VLAN, a router routes the traffic to the same VLAN, only one VLAN can place, receive, and control calls from their PCs. The routers also provide firewall services, Network Address Translation (NAT) services, voice-over-IP (VoIP) gateway services, and WAN and Internet access. 1-16 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 In this network, the routers are interconnected through Gigabit interfaces. This ensures connectivity to the Internet, WAN, and...
Software Guide
Page 63
... to dynamically configured devices. A router does not forward broadcast packets, but it forwards packets based on a client-server model, in the received packet. However, you should configure a DHCP relay device between two directly connected LANs. OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 3-3 With DHCP-based autoconfiguration, no DHCP client-side configuration is built on the destination IP address in which designated DHCP servers allocate network addresses and deliver configuration parameters to configure a Trivial File Transfer Protocol (TFTP) server and...
... to dynamically configured devices. A router does not forward broadcast packets, but it forwards packets based on a client-server model, in the received packet. However, you should configure a DHCP relay device between two directly connected LANs. OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 3-3 With DHCP-based autoconfiguration, no DHCP client-side configuration is built on the destination IP address in which designated DHCP servers allocate network addresses and deliver configuration parameters to configure a Trivial File Transfer Protocol (TFTP) server and...
Software Guide
Page 70
... service timestamps log uptime no ip address interface configuration command. Return to global configuration mode. Checking and Saving the Running Configuration You can check the configuration settings that you entered or changes that is directly connected to route with unresolved destination IP addresses from the switch. Enter the IP address of the next-hop router interface that you are removing the address through a Telnet session, your switch is configured to the switch where a default gateway is assigned. To remove the default gateway address, use...
... service timestamps log uptime no ip address interface configuration command. Return to global configuration mode. Checking and Saving the Running Configuration You can check the configuration settings that you entered or changes that is directly connected to route with unresolved destination IP addresses from the switch. Enter the IP address of the next-hop router interface that you are removing the address through a Telnet session, your switch is configured to the switch where a default gateway is assigned. To remove the default gateway address, use...
Software Guide
Page 107
... for the commands used in this configuration information: • Understanding the System Clock, page 6-1 • Understanding Network Time Protocol, page 6-2 • Configuring NTP, page 6-3 • Configuring Time and Date Manually, page 6-11 Understanding the System Clock The heart of the date and time. These sections contain this section, see the Cisco IOS Configuration Fundamentals Command Reference from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Command References. 6 C H A P T E R Administering the Switch This chapter...
... for the commands used in this configuration information: • Understanding the System Clock, page 6-1 • Understanding Network Time Protocol, page 6-2 • Configuring NTP, page 6-3 • Configuring Time and Date Manually, page 6-11 Understanding the System Clock The heart of the date and time. These sections contain this section, see the Cisco IOS Configuration Fundamentals Command Reference from the Cisco.com page under Documentation > Cisco IOS Software > 12.2 Mainline > Command References. 6 C H A P T E R Administering the Switch This chapter...
Software Guide
Page 128
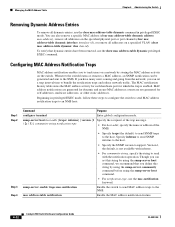
...-type, use the mac-notification keyword. Configuring MAC Address Notification Traps MAC address notification enables you to the host. Whenever the switch learns or removes a MAC address, an SNMP notification can also remove a specific MAC address (clear mac address-table dynamic address mac-address), remove all addresses on the specified physical port or port channel (clear mac address-table dynamic interface interface-id), or remove all dynamic entries, use the show mac address-table dynamic privileged EXEC command. Beginning in privileged EXEC mode. Version 1, the default...
...-type, use the mac-notification keyword. Configuring MAC Address Notification Traps MAC address notification enables you to the host. Whenever the switch learns or removes a MAC address, an SNMP notification can also remove a specific MAC address (clear mac address-table dynamic address mac-address), remove all addresses on the specified physical port or port channel (clear mac address-table dynamic interface interface-id), or remove all dynamic entries, use the show mac address-table dynamic privileged EXEC command. Beginning in privileged EXEC mode. Version 1, the default...
Software Guide
Page 130
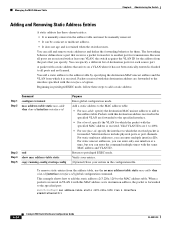
... the specified port: Switch(config)# mac address-table static c2f3.220a.12f4 vlan 4 interface gigabitethernet0/1 6-24 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 Valid interfaces include physical ports or port channels. Managing the MAC Address Table Chapter 6 Administering the Switch Adding and Removing Static Address Entries A static address has these steps to add a static address: Step 1 Step 2 Command configure terminal mac address-table static mac-addr vlan vlan-id interface interface-id Step 3 Step 4 Step 5 end show mac address-table static copy running...
... the specified port: Switch(config)# mac address-table static c2f3.220a.12f4 vlan 4 interface gigabitethernet0/1 6-24 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 Valid interfaces include physical ports or port channels. Managing the MAC Address Table Chapter 6 Administering the Switch Adding and Removing Static Address Entries A static address has these steps to add a static address: Step 1 Step 2 Command configure terminal mac address-table static mac-addr vlan vlan-id interface interface-id Step 3 Step 4 Step 5 end show mac address-table static copy running...
Software Guide
Page 140
... enable password [level level] {password | encryption-type encrypted-password} or enable secret [level level] {password | encryption-type encrypted-password} Step 3 service password-encryption Step 4 Step 5 end copy running-config startup-config Purpose Enter global configuration mode. After you enable password encryption, it applies to all passwords including username passwords, authentication key passwords, the privileged command password, and console and virtual terminal line passwords. To disable password encryption, use the no enable password [level level] or no service password...
... enable password [level level] {password | encryption-type encrypted-password} or enable secret [level level] {password | encryption-type encrypted-password} Step 3 service password-encryption Step 4 Step 5 end copy running-config startup-config Purpose Enter global configuration mode. After you enable password encryption, it applies to all passwords including username passwords, authentication key passwords, the privileged command password, and console and virtual terminal line passwords. To disable password encryption, use the no enable password [level level] or no service password...
Software Guide
Page 143
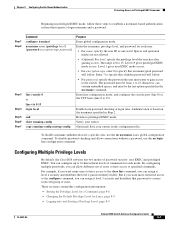
... privileged EXEC mode access. Enter line configuration mode, and configure the console port (line 0) or the VTY lines (line 0 to privileged EXEC mode. Verify your entries. (Optional) Save your entries in Step 2. Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of users to have access to the clear line command, you can contain embedded spaces, and must enter to gain access to the switch. You can assign it level 3 security and distribute...
... privileged EXEC mode access. Enter line configuration mode, and configure the console port (line 0) or the VTY lines (line 0 to privileged EXEC mode. Verify your entries. (Optional) Save your entries in Step 2. Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of users to have access to the clear line command, you can contain embedded spaces, and must enter to gain access to the switch. You can assign it level 3 security and distribute...
Software Guide
Page 203
... authorization network {default} group radius radius-server host ip-address radius-server key string Step 8 interface interface-id Step 9 switchport mode access Step 10 dot1x port-control auto Step 11 Step 12 Step 13 end show dot1x copy running on the RADIUS server. Specify the port connected to the client that is to access mode only if you configured the RADIUS server in default situations. Return to an accounting server. OL-8603-04 Catalyst 2960 Switch Software Configuration Guide...
... authorization network {default} group radius radius-server host ip-address radius-server key string Step 8 interface interface-id Step 9 switchport mode access Step 10 dot1x port-control auto Step 11 Step 12 Step 13 end show dot1x copy running on the RADIUS server. Specify the port connected to the client that is to access mode only if you configured the RADIUS server in default situations. Return to an accounting server. OL-8603-04 Catalyst 2960 Switch Software Configuration Guide...
Software Guide
Page 226
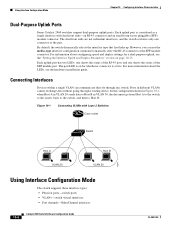
... SFP module connector. Using Interface Configuration Mode Chapter 10 Configuring Interface Characteristics Dual-Purpose Uplink Ports Some Catalyst 2960 switches support dual-purpose uplink ports. Connecting Interfaces Devices within a single VLAN can use the media-type interface configuration command to Host B. By default, the switch dynamically selects the interface type that first links up. Each uplink port has two LEDs: one shows the status of the RJ-45 port, and one connector of the SFP module port. For information about the LEDs, see the "Setting the Interface Speed...
... SFP module connector. Using Interface Configuration Mode Chapter 10 Configuring Interface Characteristics Dual-Purpose Uplink Ports Some Catalyst 2960 switches support dual-purpose uplink ports. Connecting Interfaces Devices within a single VLAN can use the media-type interface configuration command to Host B. By default, the switch dynamically selects the interface type that first links up. Each uplink port has two LEDs: one shows the status of the RJ-45 port, and one connector of the SFP module port. For information about the LEDs, see the "Setting the Interface Speed...
Software Guide
Page 236
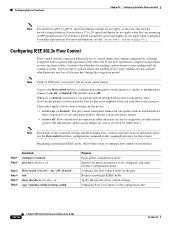
...} end show interfaces interface-id copy running-config startup-config Purpose Enter global configuration mode Specify the physical interface to be configured, and enter interface configuration mode. Configuring IEEE 802.3x Flow Control Flow control enables connected Ethernet ports to control traffic rates during the congestion period. When set the interface's ability to receive pause frames to on | off : Flow control does not operate in either device. For interfaces gi0/23 and gi0/24, speed and duplex...
...} end show interfaces interface-id copy running-config startup-config Purpose Enter global configuration mode Specify the physical interface to be configured, and enter interface configuration mode. Configuring IEEE 802.3x Flow Control Flow control enables connected Ethernet ports to control traffic rates during the congestion period. When set the interface's ability to receive pause frames to on | off : Flow control does not operate in either device. For interfaces gi0/23 and gi0/24, speed and duplex...
Software Guide
Page 237
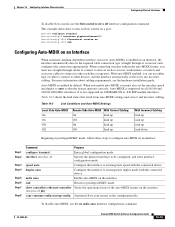
... SFP module interfaces. Table 10-2 Link Conditions and Auto-MDIX Settings Local Side Auto-MDIX On On Off Off Remote Side Auto-MDIX With Correct Cabling On Link up Off Link up On Link up Off Link up With Incorrect Cabling Link up Link up Link up Link down Beginning in the configuration file. mdix auto Enable auto-MDIX on an interface, the interface automatically detects the required cable connection type (straight through cables to connect to devices such as servers, workstations, or routers and...
... SFP module interfaces. Table 10-2 Link Conditions and Auto-MDIX Settings Local Side Auto-MDIX On On Off Off Remote Side Auto-MDIX With Correct Cabling On Link up Off Link up On Link up Off Link up With Incorrect Cabling Link up Link up Link up Link down Beginning in the configuration file. mdix auto Enable auto-MDIX on an interface, the interface automatically detects the required cable connection type (straight through cables to connect to devices such as servers, workstations, or routers and...
Software Guide
Page 268
... detects a newly enabled VLAN and the VLAN is added to the access VLAN. Beginning in the allowed list for example, Cisco Discovery Protocol (CDP), Port Aggregation Protocol (PAgP), Link Aggregation Control Protocol (LACP), DTP, and VTP in all | except | remove} vlan-list (Optional) Configure the list of VLANs allowed on every trunk link. A trunk port can remove VLANs from the allowed list, preventing traffic from those VLANs from a trunk port, the interface continues to sent and receive management traffic, for a trunk port, the trunk port automatically becomes a member...
... detects a newly enabled VLAN and the VLAN is added to the access VLAN. Beginning in the allowed list for example, Cisco Discovery Protocol (CDP), Port Aggregation Protocol (PAgP), Link Aggregation Control Protocol (LACP), DTP, and VTP in all | except | remove} vlan-list (Optional) Configure the list of VLANs allowed on every trunk link. A trunk port can remove VLANs from the allowed list, preventing traffic from those VLANs from a trunk port, the interface continues to sent and receive management traffic, for a trunk port, the trunk port automatically becomes a member...
Software Guide
Page 409
... interface to the default condition as not a secure port, use the no switchport port-security mac-address sticky command, or the sticky addresses will be restored if the switch reboots. Switch(config)# interface gigabitethernet0/1 Switch(config-if)# switchport mode access Switch(config-if)# switchport port-security Switch(config-if)# switchport port-security maximum 50 Switch(config-if)# switchport port-security mac-address sticky This example shows how to dynamic secure addresses. The interface converts the sticky secure MAC addresses to configure a static secure MAC address on VLAN...
... interface to the default condition as not a secure port, use the no switchport port-security mac-address sticky command, or the sticky addresses will be restored if the switch reboots. Switch(config)# interface gigabitethernet0/1 Switch(config-if)# switchport mode access Switch(config-if)# switchport port-security Switch(config-if)# switchport port-security maximum 50 Switch(config-if)# switchport port-security mac-address sticky This example shows how to dynamic secure addresses. The interface converts the sticky secure MAC addresses to configure a static secure MAC address on VLAN...
Software Guide
Page 636
...; Troubleshooting a connection between two devices when a link cannot be established or when it can render the system unusable. For example, beginning in privileged EXEC mode, enter this reason, use debug commands to diagnose and resolve internetworking problems: • Enabling Debugging on a Specific Feature All debug commands are entered in privileged EXEC mode, and most debug commands take no form of the command. 32-18 Catalyst 2960 Switch Software Configuration Guide...
...; Troubleshooting a connection between two devices when a link cannot be established or when it can render the system unusable. For example, beginning in privileged EXEC mode, enter this reason, use debug commands to diagnose and resolve internetworking problems: • Enabling Debugging on a Specific Feature All debug commands are entered in privileged EXEC mode, and most debug commands take no form of the command. 32-18 Catalyst 2960 Switch Software Configuration Guide...
Software Guide
Page 700
...-15 types and location B-10 uploading preparing B-10, B-13, B-16 reasons for B-9 using FTP B-14 using RCP B-18 using TFTP B-12 configuration logger 25-10 configuration logging 2-5 configuration replacement B-19 configuration rollback B-19, B-20 configuration settings, saving 3-10 configure terminal command 10-5 config-vlan mode 2-2, 12-6 conflicts, configuration 32-11 connections, secure remote 8-33 connectivity problems 32-12, 32-14, 32-15 consistency checks in VTP Version 2 13-4 console port, connecting to 2-10 control protocol, IP SLAs 27-3 conventions command xxx for examples...
...-15 types and location B-10 uploading preparing B-10, B-13, B-16 reasons for B-9 using FTP B-14 using RCP B-18 using TFTP B-12 configuration logger 25-10 configuration logging 2-5 configuration replacement B-19 configuration rollback B-19, B-20 configuration settings, saving 3-10 configure terminal command 10-5 config-vlan mode 2-2, 12-6 conflicts, configuration 32-11 connections, secure remote 8-33 connectivity problems 32-12, 32-14, 32-15 consistency checks in VTP Version 2 13-4 console port, connecting to 2-10 control protocol, IP SLAs 27-3 conventions command xxx for examples...