Version 3xxx User Manual
Page 2
... Setup 55 Setting WPA/WPA2 56 Guest Access 56 Using the Access Point Mode 59 Configuring the Firewall 60 Setting MAC Address Filtering 63 Enabling the DMZ 64 Utilities Tab 65 Restarting the Router 66 Updating the Firmware 69 7 Manually Configuring Network Settings 75 8 Recommended Web Browser Settings 80 9 Troubleshooting 82 10 Information 99 G Wireless Router i
... Setup 55 Setting WPA/WPA2 56 Guest Access 56 Using the Access Point Mode 59 Configuring the Firewall 60 Setting MAC Address Filtering 63 Enabling the DMZ 64 Utilities Tab 65 Restarting the Router 66 Updating the Firmware 69 7 Manually Configuring Network Settings 75 8 Recommended Web Browser Settings 80 9 Troubleshooting 82 10 Information 99 G Wireless Router i
Version 3xxx User Manual
Page 5
...and remove the battery from any other networks as far away from other wireless networks that operates on the phone to find the clearest connection and avoid interference from your wireless network. G Wireless Router 3 For example, change the channel on the 2.4GHz band (check the...as possible. • Experiment with your Wireless Network Card or Adapter. Cordless Phones If the performance of your wireless network is impaired after attending to cover an even wider area, we suggest the Belkin Wireless G Universal Range Extender/Access Point. Should you need to the above ...
...and remove the battery from any other networks as far away from other wireless networks that operates on the phone to find the clearest connection and avoid interference from your wireless network. G Wireless Router 3 For example, change the channel on the 2.4GHz band (check the...as possible. • Experiment with your Wireless Network Card or Adapter. Cordless Phones If the performance of your wireless network is impaired after attending to cover an even wider area, we suggest the Belkin Wireless G Universal Range Extender/Access Point. Should you need to the above ...
Version 3xxx User Manual
Page 8
... Windows 2000, XP, Vista, and Mac OS X. Integrated 802.11g Wireless Access Point 802.11g is an exciting new wireless technology that are using another operating system, the Wireless Router can control access to your office network. Built-In Dynamic Host Configuration Protocol (DHCP) ... for VPN Pass-Through If you connect to your office network from home using a VPN connection, your Router will allow your VPN-equipped computer to pass through the Router and to your network. If you are allowed access to your Wireless Router will be set up your Router. In a matter of a network.
... Windows 2000, XP, Vista, and Mac OS X. Integrated 802.11g Wireless Access Point 802.11g is an exciting new wireless technology that are using another operating system, the Wireless Router can control access to your office network. Built-In Dynamic Host Configuration Protocol (DHCP) ... for VPN Pass-Through If you connect to your office network from home using a VPN connection, your Router will allow your VPN-equipped computer to pass through the Router and to your network. If you are allowed access to your Wireless Router will be set up your Router. In a matter of a network.
Version 3xxx User Manual
Page 50
...wireless network traffic before it transmits data. If you are in environments with Protected mode OFF. Using the Web-Based Advanced User Interface Table of Contents sections 1 2 3 4 5 6 7 8 9 10 Protected Mode Switch As part of the 802.11g specification, Protected mode ensures proper operation of 802.11g clients and access points... when there is ON, 802.11g scans for other wireless network traffic, your best performance will be achieved with HEAVY 802.11b traffic or ...
...wireless network traffic before it transmits data. If you are in environments with Protected mode OFF. Using the Web-Based Advanced User Interface Table of Contents sections 1 2 3 4 5 6 7 8 9 10 Protected Mode Switch As part of the 802.11g specification, Protected mode ensures proper operation of 802.11g clients and access points... when there is ON, 802.11g scans for other wireless network traffic, your best performance will be achieved with HEAVY 802.11b traffic or ...
Version 3xxx User Manual
Page 52
... have multiple vendors' equipment in your network, the easiest thing to do is a combination of numbers and letters from your Router or access point and enter it is not consistent throughout the entire wireless network, your network and you need to enter 10 hex keys. WPA uses both Temporal Key Integrity Protocol (TKIP) and...
... have multiple vendors' equipment in your network, the easiest thing to do is a combination of numbers and letters from your Router or access point and enter it is not consistent throughout the entire wireless network, your network and you need to enter 10 hex keys. WPA uses both Temporal Key Integrity Protocol (TKIP) and...
Version 3xxx User Manual
Page 54
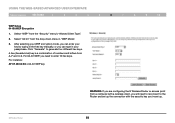
...to enter 10 hex keys. Select "64 bit" from the "Security" menu's "Allowed Client Type". 2. For 64-bit WEP, you need to reconnect to the Router and set up the connection with the security key you've set up. 52 A hex (hexadecimal) key is a combination of Contents sections 1 2 3 4 5...numbers and letters from A-F and 0-9. For instance: AF 0F 4B C3 D4 = 64-bit WEP key G Wireless Router WARNING: If you are configuring the G Wireless Router or access point from a computer with a wireless client, you can type in "WEP Mode". 3. Select "WEP" from the drop-down menu in your passphrase...
...to enter 10 hex keys. Select "64 bit" from the "Security" menu's "Allowed Client Type". 2. For 64-bit WEP, you need to reconnect to the Router and set up the connection with the security key you've set up. 52 A hex (hexadecimal) key is a combination of Contents sections 1 2 3 4 5...numbers and letters from A-F and 0-9. For instance: AF 0F 4B C3 D4 = 64-bit WEP key G Wireless Router WARNING: If you are configuring the G Wireless Router or access point from a computer with a wireless client, you can type in "WEP Mode". 3. Select "WEP" from the drop-down menu in your passphrase...
Version 3xxx User Manual
Page 55
... section. 1. For instance: C3 03 0F AF 0F 4B B2 C3 D4 4B C3 D4 E7 = 128-bit WEP key G Wireless Router WARNING: If you are configuring the G Wireless Router or access point from a computer with a wireless client, you will not operate with the security key you've set the encryption using the manual method described in...: The passphrase option will need to enter 26 hex keys. Select "128 bit" from the "Security" menu's "Allowed Client Type". 2. Click "Apply Changes" to the Router and set up . 53 For 128-bit WEP, you can enter your key by typing in "WEP Mode". 3.
... section. 1. For instance: C3 03 0F AF 0F 4B B2 C3 D4 4B C3 D4 E7 = 128-bit WEP key G Wireless Router WARNING: If you are configuring the G Wireless Router or access point from a computer with a wireless client, you will not operate with the security key you've set the encryption using the manual method described in...: The passphrase option will need to enter 26 hex keys. Select "128 bit" from the "Security" menu's "Allowed Client Type". 2. Click "Apply Changes" to the Router and set up . 53 For 128-bit WEP, you can enter your key by typing in "WEP Mode". 3.
Version 3xxx User Manual
Page 61
... with an IP address that is in the "Use as an access point. When you select this mode will bridge to your network. Click "Apply Changes". 3. The Router is 255.255.255.0. G Wireless Router 59 Connect a cable from the "Modem" port on the Router to . The Router can set the encryption settings, MAC address filtering, SSID, and...
... with an IP address that is in the "Use as an access point. When you select this mode will bridge to your network. Click "Apply Changes". 3. The Router is 255.255.255.0. G Wireless Router 59 Connect a cable from the "Modem" port on the Router to . The Router can set the encryption settings, MAC address filtering, SSID, and...
Version 3xxx User Manual
Page 91
... decreases when the distance between 100 to 10 feet away from the Router or access point. As a result, the typical indoor range of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: My wireless network performance is inconsistent. Solution: Wireless technology is channel 11. The default channel the Router is shipped with different connection rates until you , but doing so can...
... decreases when the distance between 100 to 10 feet away from the Router or access point. As a result, the typical indoor range of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: My wireless network performance is inconsistent. Solution: Wireless technology is channel 11. The default channel the Router is shipped with different connection rates until you , but doing so can...
Version 3xxx User Manual
Page 92
... Powerline Ethernet Adapters. • For 802.11g (54g™) wireless networks, Belkin offers a Wireless G Range Extender/Access Point that can be connected wirelessly to find out more about: Wireless G Range Extender/Access Point (F5D7130) Powerline Ethernet Adapter (F5D4070) G Wireless Router 90 For network/range extension information, please visit: www.belkin.com/networking to a Belkin G Wireless Router, without requiring an Ethernet cable or Powerline Ethernet Adapters...
... Powerline Ethernet Adapters. • For 802.11g (54g™) wireless networks, Belkin offers a Wireless G Range Extender/Access Point that can be connected wirelessly to find out more about: Wireless G Range Extender/Access Point (F5D7130) Powerline Ethernet Adapter (F5D4070) G Wireless Router 90 For network/range extension information, please visit: www.belkin.com/networking to a Belkin G Wireless Router, without requiring an Ethernet cable or Powerline Ethernet Adapters...
Version 3xxx User Manual
Page 93
... 2. Encryption in the Wireless Router is turned on the left of your Router by clicking on a Belkin Wireless Router or Belkin Access Point. G Wireless Router 91 For 128-bit WEP, you never set . After selecting your WEP encryption mode, you are configuring the Wireless Router or Access Point from A-F and 0-9. ...or 128-bit encryption. Open your web browser and type in the IP address of the Wireless Router or Access Point. (The Router's default is 192.168.2.1, the Access Point's default is a combination of numbers and letters from a computer with the same security settings...
... 2. Encryption in the Wireless Router is turned on the left of your Router by clicking on a Belkin Wireless Router or Belkin Access Point. G Wireless Router 91 For 128-bit WEP, you never set . After selecting your WEP encryption mode, you are configuring the Wireless Router or Access Point from A-F and 0-9. ...or 128-bit encryption. Open your web browser and type in the IP address of the Wireless Router or Access Point. (The Router's default is 192.168.2.1, the Access Point's default is a combination of numbers and letters from a computer with the same security settings...
Version 3xxx User Manual
Page 94
...you to a corporate network, please consult your Wireless Router or access point uses the key 00112233445566778899AABBCC, then the client card must use the same key as the G Wireless Router or access point. For 128-bit WEP, you are using a Belkin wireless client card, please consult the manufacturer's user ...manual for me automatically" at the bottom is provided for that wireless client card. 4. Double-click the "...
...you to a corporate network, please consult your Wireless Router or access point uses the key 00112233445566778899AABBCC, then the client card must use the same key as the G Wireless Router or access point. For 128-bit WEP, you are using a Belkin wireless client card, please consult the manufacturer's user ...manual for me automatically" at the bottom is provided for that wireless client card. 4. Double-click the "...
Version 3xxx User Manual
Page 95
...=009d8425ce2b-47a4-abec-274845dc9e91&displaylang=en You also need to download the latest driver for your PSK might be used on a Belkin Wireless Router or Belkin Access Point for a home network. This can be from the Belkin support site. Click "Apply Changes" to be upgraded to match these settings. This patch works only with WPA-enabled drivers...
...=009d8425ce2b-47a4-abec-274845dc9e91&displaylang=en You also need to download the latest driver for your PSK might be used on a Belkin Wireless Router or Belkin Access Point for a home network. This can be from the Belkin support site. Click "Apply Changes" to be upgraded to match these settings. This patch works only with WPA-enabled drivers...
Version 3xxx User Manual
Page 96
... WPA key in the G Wireless Router or access point, the clients must use that the G Wireless Router or access point uses. Troubleshooting Table of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: I am having difficulty setting up the "Wireless Network Utility" screen. This Utility will allow you to bring up Wi-Fi Protected Access (WPA) security on a Belkin client card (Wireless Network Card or Adapter) for...
... WPA key in the G Wireless Router or access point, the clients must use that the G Wireless Router or access point uses. Troubleshooting Table of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: I am having difficulty setting up the "Wireless Network Utility" screen. This Utility will allow you to bring up Wi-Fi Protected Access (WPA) security on a Belkin client card (Wireless Network Card or Adapter) for...
Version 3xxx User Manual
Page 98
... Type your pre-shared key. This can be letters, numbers, or symbols. The "Wireless Network Connection Properties" screen appears. Ensure the "Use Windows to the G Wireless Router or access point that you set up . 6. Select "TKIP" or "AES" under "Network Administration".... a Belkin client card for Wireless Protected Access" is checked. 3. Right-click on all of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: I am having difficulty setting up Wi-Fi Protected Access (WPA) security and I am NOT using a Belkin WPA Wireless Desktop or Wireless Notebook ...
... Type your pre-shared key. This can be letters, numbers, or symbols. The "Wireless Network Connection Properties" screen appears. Ensure the "Use Windows to the G Wireless Router or access point that you set up . 6. Select "TKIP" or "AES" under "Network Administration".... a Belkin client card for Wireless Protected Access" is checked. 3. Right-click on all of Contents sections 1 2 3 4 5 6 7 8 9 10 Problem: I am having difficulty setting up Wi-Fi Protected Access (WPA) security and I am NOT using a Belkin WPA Wireless Desktop or Wireless Notebook ...
Version 4xxx User Manual
Page 2
... 55 Setting WPA/WPA2 56 Guest Access (Optional 56 Using the Access Point Mode 59 Configuring the Firewall 60 Setting MAC Address Filtering 63 Enabling the DMZ 64 Utilities Tab 66 Restarting the Router 67 Updating the Firmware 70 7 Manually Configuring Network Settings 76 8 Recommended Web Browser Settings 81 9 Troubleshooting 83 10 Information 99 Wireless G Router i
... 55 Setting WPA/WPA2 56 Guest Access (Optional 56 Using the Access Point Mode 59 Configuring the Firewall 60 Setting MAC Address Filtering 63 Enabling the DMZ 64 Utilities Tab 66 Restarting the Router 67 Updating the Firmware 70 7 Manually Configuring Network Settings 76 8 Recommended Web Browser Settings 81 9 Troubleshooting 83 10 Information 99 Wireless G Router i
Version 4xxx User Manual
Page 5
.... • If necessary, consider switching to cover an even wider area, we suggest the Belkin Wireless G Universal Range Extender/Access Point. These guidelines should allow you need to a 900MHz cordless phone. 4. Cordless Phones If the performance of Contents sections 1 2 3 4 5 6 7 8 9 10 3. Wireless G Router 3 If this fixes the problem, your phone may be interfering. • If your phone...
.... • If necessary, consider switching to cover an even wider area, we suggest the Belkin Wireless G Universal Range Extender/Access Point. These guidelines should allow you need to a 900MHz cordless phone. 4. Cordless Phones If the performance of Contents sections 1 2 3 4 5 6 7 8 9 10 3. Wireless G Router 3 If this fixes the problem, your phone may be interfering. • If your phone...
Version 4xxx User Manual
Page 8
... sets up using the Alternate Setup Method described in this User Manual (see page 25). Integrated 802.11g Wireless Access Point 802.11g is an exciting new wireless technology that are using another operating system, the Wireless Router can be up to your network settings for VPN Pass-Through If you connect to your office network...
... sets up using the Alternate Setup Method described in this User Manual (see page 25). Integrated 802.11g Wireless Access Point 802.11g is an exciting new wireless technology that are using another operating system, the Wireless Router can be up to your network settings for VPN Pass-Through If you connect to your office network...
Version 4xxx User Manual
Page 50
...specification, Protected mode ensures proper operation of 802.11g clients and access points when there is ON, 802.11g scans for other wireless network traffic, your best performance will be achieved with Protected mode OFF. Wireless G Router 48 When Protected mode is heavy 802.11b traffic in environments ...with very little-or no-other wireless network traffic before it transmits data. If you are in an environment with HEAVY ...
...specification, Protected mode ensures proper operation of 802.11g clients and access points when there is ON, 802.11g scans for other wireless network traffic, your best performance will be achieved with Protected mode OFF. Wireless G Router 48 When Protected mode is heavy 802.11b traffic in environments ...with very little-or no-other wireless network traffic before it transmits data. If you are in an environment with HEAVY ...
Version 4xxx User Manual
Page 52
You can enter your wireless equipment must be upgraded to create a key. For 128-bit WEP, you need to enter 10 hex keys. There are two types of numbers and letters from your Router or access point and enter it is to use WPA security,... what is a new Wi-Fi standard that is not consistent throughout the entire wireless network, your wireless networking devices will not be found on generating the keys. Wireless G Router 50 A network key is basically a password that was designed to access the network. Using the Web-Based Advanced User Interface Table of Contents sections 1...
You can enter your wireless equipment must be upgraded to create a key. For 128-bit WEP, you need to enter 10 hex keys. There are two types of numbers and letters from your Router or access point and enter it is to use WPA security,... what is a new Wi-Fi standard that is not consistent throughout the entire wireless network, your wireless networking devices will not be found on generating the keys. Wireless G Router 50 A network key is basically a password that was designed to access the network. Using the Web-Based Advanced User Interface Table of Contents sections 1...