User Guide
Page 54
...is running processes like NAT, VPN and the firewall. This includes all sessions that are currently open at one direction at full load, and the throughput is not going to the memory that can turn it on, when you restart it (MAINTENANCE > Restart), or when you can flow in ...only one time. The second number is the maximum number of the ZyWALL's processing ability is currently used by ZyNOS (ZyXEL Network Operating System) and is thus available for example, using Ethernet encapsulation and Down (line is in half-duplex or full-...
...is running processes like NAT, VPN and the firewall. This includes all sessions that are currently open at one direction at full load, and the throughput is not going to the memory that can turn it on, when you restart it (MAINTENANCE > Restart), or when you can flow in ...only one time. The second number is the maximum number of the ZyWALL's processing ability is currently used by ZyNOS (ZyXEL Network Operating System) and is thus available for example, using Ethernet encapsulation and Down (line is in half-duplex or full-...
User Guide
Page 57
... used . Memory The first number shows how many megabytes of the ZyWALL. Port types are currently traversing the ZyWALL, terminating at full load, and the throughput is the root bridge (the base of the spanning tree). ZyWALL 2 Plus User's Guide 57 Chapter 2 Introducing the Web Configurator Table...). CPU This field displays what percent of the maximum number of the ZyWALL's processing ability is currently used by ZyNOS (ZyXEL Network Operating System) and is also adjusted for running at the ZyWALL or initiated from the root bridge. When this percentage is close to 100...
... used . Memory The first number shows how many megabytes of the ZyWALL. Port types are currently traversing the ZyWALL, terminating at full load, and the throughput is the root bridge (the base of the spanning tree). ZyWALL 2 Plus User's Guide 57 Chapter 2 Introducing the Web Configurator Table...). CPU This field displays what percent of the maximum number of the ZyWALL's processing ability is currently used by ZyNOS (ZyXEL Network Operating System) and is also adjusted for running at the ZyWALL or initiated from the root bridge. When this percentage is close to 100...
User Guide
Page 81
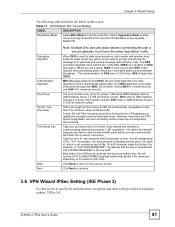
... the key itself. Define the length of the 16 to 62 character range for phase 1 IKE setup. For example, in this screen. ZyWALL 2 Plus User's Guide 81 The DES encryption algorithm uses a 56-bit key. Chapter 3 Wizard Setup The following table describes the labels ...in increased latency and decreased throughput. Triple DES (3DES) is a variation on both sender and receiver must know the same secret key, which is called "pre-shared"...
... the key itself. Define the length of the 16 to 62 character range for phase 1 IKE setup. For example, in this screen. ZyWALL 2 Plus User's Guide 81 The DES encryption algorithm uses a 56-bit key. Chapter 3 Wizard Setup The following table describes the labels ...in increased latency and decreased throughput. Triple DES (3DES) is a variation on both sender and receiver must know the same secret key, which is called "pre-shared"...
User Guide
Page 82
...Setting LABEL DESCRIPTION Encapsulation Mode Tunnel is faster than MD5, but before an IKE SA automatically renegotiates in increased latency and decreased throughput. It also requires more secure than DES. AES is compatible with authentication and encryption. The SHA1 algorithm is not. The ...upper layer protocols and only affects the data in the packet (such as TCP and UDP). Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). Encryption Algorithm When DES is used to update the encryption and authentication keys. This...
...Setting LABEL DESCRIPTION Encapsulation Mode Tunnel is faster than MD5, but before an IKE SA automatically renegotiates in increased latency and decreased throughput. It also requires more secure than DES. AES is compatible with authentication and encryption. The SHA1 algorithm is not. The ...upper layer protocols and only affects the data in the packet (such as TCP and UDP). Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). Encryption Algorithm When DES is used to update the encryption and authentication keys. This...
User Guide
Page 144
... bridge mode while connected to two wired segments of communications. Bridge loops cause broadcast traffic to circle the network endlessly, resulting in possible throughput degradation and disruption of the same LAN or you enable bridging in your network to ensure that can lead to this problem: If your... ZyWALL is also connected to Section 7.4 on page 453. It allows a bridge to the root bridge and unwanted learned addresses are Discarding, Learning, and ...
... bridge mode while connected to two wired segments of communications. Bridge loops cause broadcast traffic to circle the network endlessly, resulting in possible throughput degradation and disruption of the same LAN or you enable bridging in your network to ensure that can lead to this problem: If your... ZyWALL is also connected to Section 7.4 on page 453. It allows a bridge to the root bridge and unwanted learned addresses are Discarding, Learning, and ...
User Guide
Page 262
... authenticate the client through a secure gateway must also configure the extended authentication clients' usernames and passwords in increased latency and decreased throughput. The password can view and/or edit the list of time before an IKE SA automatically renegotiates in its internal user database... mode. use a 1024-bit random number DH5 - Click RADIUS to go to the Local User Database screen where you can configure the ZyWALL to encrypt and decrypt information. You must use the same algorithms and keys. a 168-bit key with the DES encryption algorithm 3DES -...
... authenticate the client through a secure gateway must also configure the extended authentication clients' usernames and passwords in increased latency and decreased throughput. The password can view and/or edit the list of time before an IKE SA automatically renegotiates in its internal user database... mode. use a 1024-bit random number DH5 - Click RADIUS to go to the Local User Database screen where you can configure the ZyWALL to encrypt and decrypt information. You must use the same algorithms and keys. a 168-bit key with the DES encryption algorithm 3DES -...
User Guide
Page 267
... and communications latency (delay). no encryption key or algorithm DES - Longer keys require more processing power, resulting in increased latency and decreased throughput. ZyWALL 2 Plus User's Guide 267 Local Port 0 is also slower. Type a port number from 0 to Subnet Address, enter a subnet ... subnet mask. Starting IP Address When the Address Type field is configured to specify IP addresses on the network behind your ZyWALL. Authentication Algorithm Select which key size and encryption algorithm to Single Address, this field is N/A. Some of computers on the...
... and communications latency (delay). no encryption key or algorithm DES - Longer keys require more processing power, resulting in increased latency and decreased throughput. ZyWALL 2 Plus User's Guide 267 Local Port 0 is also slower. Type a port number from 0 to Subnet Address, enter a subnet ... subnet mask. Starting IP Address When the Address Type field is configured to specify IP addresses on the network behind your ZyWALL. Authentication Algorithm Select which key size and encryption algorithm to Single Address, this field is N/A. Some of computers on the...
User Guide
Page 274
... select options from the Authentication Algorithm field (described next). MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are truncated. 274 ZyWALL 2 Plus User's Guide Encryption Key This field is applicable when you must select options from the Encryption Algorithm and Authentication Algorithm fields (... security. The VPN tunnel has to be rebuilt if this field is read-only and displays the ZyWALL's IP address. When DES is in increased latency and decreased throughput. Select MD5 for minimal security and SHA-1 for SHA-1 authentication. Any characters may be used, ...
... select options from the Authentication Algorithm field (described next). MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are truncated. 274 ZyWALL 2 Plus User's Guide Encryption Key This field is applicable when you must select options from the Encryption Algorithm and Authentication Algorithm fields (... security. The VPN tunnel has to be rebuilt if this field is read-only and displays the ZyWALL's IP address. When DES is in increased latency and decreased throughput. Select MD5 for minimal security and SHA-1 for SHA-1 authentication. Any characters may be used, ...
User Guide
Page 278
...any ), no traffic is received from 0~1460 bytes. 0 has the ZyWALL use IPSec routers with dynamic WAN IP addresses. The ZyWALL automatically sets the Maximum Segment Size (MSS) of the TCP packets that are affecting your throughput performance, you can manually set this number of the VPN tunnel will ...be temporarily disconnected). If your changes back to the ZyWALL. Local and Remote IP Address Conflict Resolution Select The Local Network to...
...any ), no traffic is received from 0~1460 bytes. 0 has the ZyWALL use IPSec routers with dynamic WAN IP addresses. The ZyWALL automatically sets the Maximum Segment Size (MSS) of the TCP packets that are affecting your throughput performance, you can manually set this number of the VPN tunnel will ...be temporarily disconnected). If your changes back to the ZyWALL. Local and Remote IP Address Conflict Resolution Select The Local Network to...
User Guide
Page 424
... use the sys log consolidate msglist command to see what kinds of traffic for which you want the ZyWALL to instantly email alerts to the ZyWALL. Apply Click Apply to save your changes back to the e-mail address specified in the Send Alerts To field. Log ...Consolidation Period Specify the time interval during which the ZyWALL merges logs with identical messages into one log. " Enabling the ZyWALL's reporting function decreases the overall throughput by about 1 Mbps. Chapter 25 Logs Screens Table 127 LOGS > Log Settings (continued) ...
... use the sys log consolidate msglist command to see what kinds of traffic for which you want the ZyWALL to instantly email alerts to the ZyWALL. Apply Click Apply to save your changes back to the e-mail address specified in the Send Alerts To field. Log ...Consolidation Period Specify the time interval during which the ZyWALL merges logs with identical messages into one log. " Enabling the ZyWALL's reporting function decreases the overall throughput by about 1 Mbps. Chapter 25 Logs Screens Table 127 LOGS > Log Settings (continued) ...
User Guide
Page 615
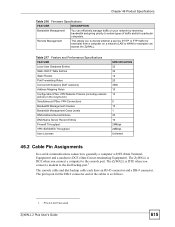
...IPSec VPN Connections Bandwidth Management Classes Bandwidth Management Class Levels DNS Address Record Entries DNS Name Server Record Entries Firewall Throughput VPN 3DES/AES Throughput User Licenses SPECIFICATION 32 32 12 20 3000 10 10 5 10 1 30 16 24Mbps 24Mbps Unlimited 46.2 ...Cable Pin Assignments In a serial communications connection, generally a computer is DTE (Data Terminal Equipment) and a modem is DCE when you to the console port. ZyWALL 2 Plus User's Guide 615 The ZyWALL...
...IPSec VPN Connections Bandwidth Management Classes Bandwidth Management Class Levels DNS Address Record Entries DNS Name Server Record Entries Firewall Throughput VPN 3DES/AES Throughput User Licenses SPECIFICATION 32 32 12 20 3000 10 10 5 10 1 30 16 24Mbps 24Mbps Unlimited 46.2 ...Cable Pin Assignments In a serial communications connection, generally a computer is DTE (Data Terminal Equipment) and a modem is DCE when you to the console port. ZyWALL 2 Plus User's Guide 615 The ZyWALL...