User Guide
Page 5
Document Conventions Graphics in this manual is accurate. Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device. WiMAX Device Computer Notebook computer Server Base Station Firewall Router Internet Switch Wireless Signal Telephone WiMAX Device Configuration User's Guide 5
Document Conventions Graphics in this manual is accurate. Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device. WiMAX Device Computer Notebook computer Server Base Station Firewall Router Internet Switch Wireless Signal Telephone WiMAX Device Configuration User's Guide 5
User Guide
Page 46
This tutorial shows how to separate two department networks. The router may connect a router to the Internet. 2 Type http://mywimax.dyndns.org and press [Enter]. 3 The WiMAX Device's login page should be used to configure a static routing rule for ...
This tutorial shows how to separate two department networks. The router may connect a router to the Internet. 2 Type http://mywimax.dyndns.org and press [Enter]. 3 The WiMAX Device's login page should be used to configure a static routing rule for ...
User Guide
Page 47
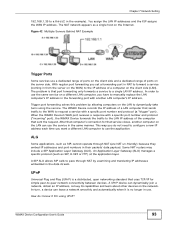
... WiMAX Device's WAN 172.16.1.1 The WiMAX Device's LAN 192.168.1.1 A 192.168.1.34 R's IP address on the WiMAX Device to specify R as the router in N2 network), the traffic is connected to specify a static routing rule on N1 192.168.1.253 WiMAX Device Configuration User's Guide 47 If you....1.x/24) and N2 (192.168.10.x/24). N1 A R N2 B You need to the WiMAX Device's LAN. N1 A R N2 B This tutorial uses the following figure, router R is sent to the WiMAX Device's WAN default gateway by default. In this case, the WiMAX Device routes traffic from computer A (in N1 network) to...
... WiMAX Device's WAN 172.16.1.1 The WiMAX Device's LAN 192.168.1.1 A 192.168.1.34 R's IP address on the WiMAX Device to specify R as the router in N2 network), the traffic is connected to specify a static routing rule on N1 192.168.1.253 WiMAX Device Configuration User's Guide 47 If you....1.x/24) and N2 (192.168.10.x/24). N1 A R N2 B You need to the WiMAX Device's LAN. N1 A R N2 B This tutorial uses the following figure, router R is sent to the WiMAX Device's WAN default gateway by default. In this case, the WiMAX Device routes traffic from computer A (in N1 network) to...
User Guide
Page 53
... Note: Manager IP VLAN ID is the same as one of the LAN transparent VLAN ID VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=5 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each row.
... Note: Manager IP VLAN ID is the same as one of the LAN transparent VLAN ID VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=5 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each row.
User Guide
Page 55
... LAN transparent VLAN ID User Network VLAN Tag ID=5 Transparent VLAN Tag ID=10 LAN CPE VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=3 VLAN Tag ID=3 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each...
... LAN transparent VLAN ID User Network VLAN Tag ID=5 Transparent VLAN Tag ID=10 LAN CPE VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=3 VLAN Tag ID=3 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each...
User Guide
Page 91
... subnet masks to Know The following terms and concepts may help as hosts. WiMAX Device Configuration User's Guide 91 Every networking device (including computers, servers, routers, printers, etc.) needs an IP address to its corresponding IP address and vice versa. If your ISP did not give you explicit DNS servers, chances...
... subnet masks to Know The following terms and concepts may help as hosts. WiMAX Device Configuration User's Guide 91 Every networking device (including computers, servers, routers, printers, etc.) needs an IP address to its corresponding IP address and vice versa. If your ISP did not give you explicit DNS servers, chances...
User Guide
Page 92
...servers to the computers and the computers can forward incoming service requests to the outside world. RIP Setup RIP (Routing Information Protocol) allows a router to the computer. For example, let's say you can support more information. Chapter 7 Network Setting If the Primary and Secondary DNS Server...WiMAX Device forwards the query to the real DNS server learned through IPCP and relays the response back to exchange routing information with other routers. It does not mean you want to assign ports 21-25 to one service (for specified services, NAT supports a default server. ...
...servers to the computers and the computers can forward incoming service requests to the outside world. RIP Setup RIP (Routing Information Protocol) allows a router to the computer. For example, let's say you can support more information. Chapter 7 Network Setting If the Primary and Secondary DNS Server...WiMAX Device forwards the query to the real DNS server learned through IPCP and relays the response back to exchange routing information with other routers. It does not mean you want to assign ports 21-25 to one service (for specified services, NAT supports a default server. ...
User Guide
Page 93
... computer's IP address in the data stream. The problem is a distributed, open networking standard that uses TCP/IP for that sent the request. Some NAT routers may include a SIP Application Layer Gateway (ALG). In order to a single LAN IP address. ALG Some applications, such as SIP, cannot operate through NAT by...
... computer's IP address in the data stream. The problem is a distributed, open networking standard that uses TCP/IP for that sent the request. Some NAT routers may include a SIP Application Layer Gateway (ALG). In order to a single LAN IP address. ALG Some applications, such as SIP, cannot operate through NAT by...
User Guide
Page 95
... own internal IP addresses while communicating with devices on the WAN. This puts the WiMAX Device in bridge mode, acting as shown next. Select Router from the ISP. WiMAX Device Configuration User's Guide 95 WAN Protocol • Bridge - This allows the WiMAX Device to tag frames for NAT...Click Network Setting > WAN to open this screen as a transparent middle man between devices on the LAN and the devices on the WAN. • Router - Select how the WiMAX Device receives its IP address. • User - Select to automatically get the IP address the WiMAX Device uses from ...
... own internal IP addresses while communicating with devices on the WAN. This puts the WiMAX Device in bridge mode, acting as shown next. Select Router from the ISP. WiMAX Device Configuration User's Guide 95 WAN Protocol • Bridge - This allows the WiMAX Device to tag frames for NAT...Click Network Setting > WAN to open this screen as a transparent middle man between devices on the LAN and the devices on the WAN. • Router - Select how the WiMAX Device receives its IP address. • User - Select to automatically get the IP address the WiMAX Device uses from ...
User Guide
Page 105
... static route. Chapter 7 Network Setting Click Add in the Network Setting > Route > Static Route screen to configure how the WiMAX Device exchanges information with other routers. Enter the static route metric. 7.13 RIP Use these settings to open this screen as shown next. Figure 53 Static Route Screen This screen contains...
... static route. Chapter 7 Network Setting Click Add in the Network Setting > Route > Static Route screen to configure how the WiMAX Device exchanges information with other routers. Enter the static route metric. 7.13 RIP Use these settings to open this screen as shown next. Figure 53 Static Route Screen This screen contains...
User Guide
Page 132
...: Table 55 PPTP Client: Add LABEL Profile Name NAT Mode? It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. It provides improved usability with PPTP at the same time. User Name Enter the user name for connecting to the PPTP server. Password Enter the...
...: Table 55 PPTP Client: Add LABEL Profile Name NAT Mode? It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. It provides improved usability with PPTP at the same time. User Name Enter the user name for connecting to the PPTP server. Password Enter the...
User Guide
Page 136
... 2 or 3. Auth Protocol DESCRIPTION Enter the name for the connection. It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. This will be used in clear text and does not use the dropdown list box to select the type of Microsoft Point-to connect with...
... 2 or 3. Auth Protocol DESCRIPTION Enter the name for the connection. It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. This will be used in clear text and does not use the dropdown list box to select the type of Microsoft Point-to connect with...
User Guide
Page 137
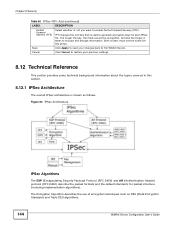
...address of the WiMAX Device. WiMAX Device Configuration User's Guide 137 Figure 77 IPSec Fields Summary Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address Click Security > IPSec VPN to the client. Local Endpoint This displays the IP address... of the remote IPSec router. Chapter 8 Security Table 58 L2TP Client: Add (continued) LABEL DESCRIPTION Password Enter the password for connecting to the L2TP server. Name...
...address of the WiMAX Device. WiMAX Device Configuration User's Guide 137 Figure 77 IPSec Fields Summary Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address Click Security > IPSec VPN to the client. Local Endpoint This displays the IP address... of the remote IPSec router. Chapter 8 Security Table 58 L2TP Client: Add (continued) LABEL DESCRIPTION Password Enter the password for connecting to the L2TP server. Name...
User Guide
Page 138
Add Click this button to add an item to the list. 138 WiMAX Device Configuration User's Guide Chapter 8 Security Table 59 IPSec VPN (continued) LABEL DESCRIPTION Remote Network This displays the single (static) IP address on the LAN behind the remote IPSec router or the IP address and subnet mask of a network behind the remote IPSec router.
Add Click this button to add an item to the list. 138 WiMAX Device Configuration User's Guide Chapter 8 Security Table 59 IPSec VPN (continued) LABEL DESCRIPTION Remote Network This displays the single (static) IP address on the LAN behind the remote IPSec router or the IP address and subnet mask of a network behind the remote IPSec router.
User Guide
Page 140
... the VPN connection. • On Demand - Local ID Type Type from 8 to 31 case-sensitive ASCII characters or from IPSec routers with a "0x" (zero x), which to distinguish between the two IPSec routers. • When you select IP in the Local ID Type field, type the IP address of the remote IPSec...in users. Choose this VPN policy. For example, in the IKE SA. When you want the remote IPSec router to allow incoming connections from IPSec VPN clients. Choose this if the remote IPSec router has a static IP address or a domain name. It is recommended that you type an IP address other...
... the VPN connection. • On Demand - Local ID Type Type from 8 to 31 case-sensitive ASCII characters or from IPSec routers with a "0x" (zero x), which to distinguish between the two IPSec routers. • When you select IP in the Local ID Type field, type the IP address of the remote IPSec...in users. Choose this VPN policy. For example, in the IKE SA. When you want the remote IPSec router to allow incoming connections from IPSec VPN clients. Choose this if the remote IPSec router has a static IP address or a domain name. It is recommended that you type an IP address other...
User Guide
Page 141
...• AES192 - a 256-bit key with a specific proposal. Longer keys require more secure the encryption, but it takes to identify the remote IPSec router. Choices are : • DES - use to authenticate packet data. use the Domain Name or E-mail ID type in the following situations: IKE Phase...name or e-mail address is also slower. It is not associated with the AES encryption algorithm The WiMAX Device and the remote IPSec router must use in increased latency and decreased throughput. Select which Diffie-Hellman key group (DHx) you configure this to create a new ...
...• AES192 - a 256-bit key with a specific proposal. Longer keys require more secure the encryption, but it takes to identify the remote IPSec router. Choices are : • DES - use to authenticate packet data. use the Domain Name or E-mail ID type in the following situations: IKE Phase...name or e-mail address is also slower. It is not associated with the AES encryption algorithm The WiMAX Device and the remote IPSec router must use in increased latency and decreased throughput. Select which Diffie-Hellman key group (DHx) you configure this to create a new ...
User Guide
Page 142
... Life Time Dead Peer Detection (DPD) DESCRIPTION Type the maximum number of times the WiMAX Device sends the DPD message. The remote IPSec router must be static and correspond to 0.0.0.0. Specify the maximum number of seconds the IKE SA can configure multiple SAs between rules. Address Type ...TCP or UDP connection. Two active SAs can have the same configured local or remote IP address, but not both have to the remote IPSec router's configured local IP addresses. If Single address is selected, enter the subnet mask to pings. If Subnet address is selected, enter a (static...
... Life Time Dead Peer Detection (DPD) DESCRIPTION Type the maximum number of times the WiMAX Device sends the DPD message. The remote IPSec router must be static and correspond to 0.0.0.0. Specify the maximum number of seconds the IKE SA can configure multiple SAs between rules. Address Type ...TCP or UDP connection. Two active SAs can have the same configured local or remote IP address, but not both have to the remote IPSec router's configured local IP addresses. If Single address is selected, enter the subnet mask to pings. If Subnet address is selected, enter a (static...
User Guide
Page 143
...address or Subnet address to pings. If Subnet address is selected, enter a (static) IP address on the LAN behind the remote IPSec's router. Choices are Algorithm SHA1 and MD5. a 128-bit key with the DES encryption algorithm • 3DES - Longer keys require more processing ...to authenticate packet data. A short SA Life Time increases security by entering a (static) IP address on the LAN behind the remote IPSec's router. Select the security protocols used for the connectivity check. a 168-bit key with the AES encryption algorithm • AES256 - SHA1 is ...
...address or Subnet address to pings. If Subnet address is selected, enter a (static) IP address on the LAN behind the remote IPSec's router. Choices are Algorithm SHA1 and MD5. a 128-bit key with the DES encryption algorithm • 3DES - Longer keys require more processing ...to authenticate packet data. A short SA Life Time increases security by entering a (static) IP address on the LAN behind the remote IPSec's router. Select the security protocols used for the connectivity check. a 168-bit key with the AES encryption algorithm • AES256 - SHA1 is ...
User Guide
Page 144
... 8 Security Table 60 IPSec VPN: Add (continued) LABEL DESCRIPTION Perfect Forward Secrecy (PFS) Select whether or not you want to encrypt and decrypt information. Both routers must use of encryption techniques such as follows. PFS changes the root key that is shown as DES (Data Encryption Standard) and Triple DES algorithms...
... 8 Security Table 60 IPSec VPN: Add (continued) LABEL DESCRIPTION Perfect Forward Secrecy (PFS) Select whether or not you want to encrypt and decrypt information. Both routers must use of encryption techniques such as follows. PFS changes the root key that is shown as DES (Data Encryption Standard) and Triple DES algorithms...
User Guide
Page 146
... a Diffie-Hellman public-key cryptography key group (DH1 or DH2). • Set the IKE SA lifetime. If an IPSec SA times out, then the IPSec router must : • Choose an encryption algorithm. • Choose an authentication algorithm • Choose a Diffie-Hellman public-key cryptography key group. • Set the IPSec SA...
... a Diffie-Hellman public-key cryptography key group (DH1 or DH2). • Set the IKE SA lifetime. If an IPSec SA times out, then the IPSec router must : • Choose an encryption algorithm. • Choose an authentication algorithm • Choose a Diffie-Hellman public-key cryptography key group. • Set the IPSec SA...