TL-SG3216 V1 User Guide
Page 10
...used to configure VLANs to combine a number of the switch. This module is to control broadcast in the network. 3 This module is used to monitor the IGMP messages in LANs. z User Manage: Configure the user name and password for the port. z Traffic Monitor: Monitor the traffic of each port z MAC Address: Configure the address table of ports. z MSTP Instance: Configure MSTP instances. z LAG: Configure Link Aggregation Group. z MAC VLAN: Configure MAC-based VLAN without having to restrict users ordering multicast programs. z Packet Statistics: View the multicast data...
...used to configure VLANs to combine a number of the switch. This module is to control broadcast in the network. 3 This module is used to monitor the IGMP messages in LANs. z User Manage: Configure the user name and password for the port. z Traffic Monitor: Monitor the traffic of each port z MAC Address: Configure the address table of ports. z MSTP Instance: Configure MSTP instances. z LAG: Configure Link Aggregation Group. z MAC VLAN: Configure MAC-based VLAN without having to restrict users ordering multicast programs. z Packet Statistics: View the multicast data...
TL-SG3216 V1 User Guide
Page 13
... business critical data. It provides a variety of service features and multiple powerful functions with 4 priority queues per port. + Rate limiting confines the traffic flow accurately according to the preset value. • Security + Supports multiple industry standard user authentication methods such as 802.1x, RADIUS. + Dynamic ARP Inspection blocks ARP packets from TP-LINK provides wire-speed performance and full set of layer 2 management features. Chapter 2 Introduction Thanks for choosing the TL-SG3216/TL-SG3424...
... business critical data. It provides a variety of service features and multiple powerful functions with 4 priority queues per port. + Rate limiting confines the traffic flow accurately according to the preset value. • Security + Supports multiple industry standard user authentication methods such as 802.1x, RADIUS. + Dynamic ARP Inspection blocks ARP packets from TP-LINK provides wire-speed performance and full set of layer 2 management features. Chapter 2 Introduction Thanks for choosing the TL-SG3216/TL-SG3424...
TL-SG3216 V1 User Guide
Page 23
... switch will replace the original IP address. 3. The User Manage function can be configured. 5. the admin can view the information about the current users of the switch. The Web management pages contained in this page you can view the settings without any explanation. The switch only possesses an IP address. Choose the menu System→User Manage→User Table to the admin's login without the right to the default. 4. The switch provides two access...
... switch will replace the original IP address. 3. The User Manage function can be configured. 5. the admin can view the information about the current users of the switch. The Web management pages contained in this page you can view the settings without any explanation. The switch only possesses an IP address. Choose the menu System→User Manage→User Table to the admin's login without the right to the default. 4. The switch provides two access...
TL-SG3216 V1 User Guide
Page 58
... or deleted. Displays the port members in VLAN1. Click Edit button to create a new VLAN. 51 VLAN ID: Description: Members: Operation: Displays the ID number of VLAN. Click Create button to modify the settings of all ports is multi-optional. Displays the user-defined description of VLAN. It is set to VLAN1. Figure 6-3 VLAN Table To ensure the normal communication of the factory switch, the default VLAN...
... or deleted. Displays the port members in VLAN1. Click Edit button to create a new VLAN. 51 VLAN ID: Description: Members: Operation: Displays the ID number of VLAN. Click Create button to modify the settings of all ports is multi-optional. Displays the user-defined description of VLAN. It is set to VLAN1. Figure 6-3 VLAN Table To ensure the normal communication of the factory switch, the default VLAN...
TL-SG3216 V1 User Guide
Page 60
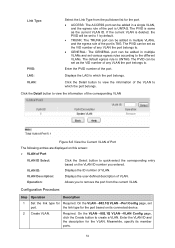
...; VLAN Port Config Port Select: Click the Select button to configure the ports properly. Port Config The following page. It is UNTAG. • TAG: All packets forwarded by the port Displays the LAG to which the port belongs. 6.1.2 Port Config Before creating the 802.1Q VLAN, please acquaint yourself with all the devices connected to the switch in order to quick-select the corresponding entry based on the port number you entered. Port: Displays...
...; VLAN Port Config Port Select: Click the Select button to configure the ports properly. Port Config The following page. It is UNTAG. • TAG: All packets forwarded by the port Displays the LAG to which the port belongs. 6.1.2 Port Config Before creating the 802.1Q VLAN, please acquaint yourself with all the devices connected to the switch in order to quick-select the corresponding entry based on the port number you entered. Port: Displays...
TL-SG3216 V1 User Guide
Page 61
... rule of VLAN. Link Type: PVID: Select the Link Type from the current VLAN. The PVID is deleted, the PVID will be set port. The PVID can be set as the VID number of the port is UNTAG. On the VLAN→802.1Q VLAN→Port Config page, set to 1 by default. • TRUNK: The TRUNK port can be added in multiple VLANs, and the egress rule of any VLAN the port belongs to create a VLAN.
... rule of VLAN. Link Type: PVID: Select the Link Type from the current VLAN. The PVID is deleted, the PVID will be set port. The PVID can be set as the VID number of the port is UNTAG. On the VLAN→802.1Q VLAN→Port Config page, set to 1 by default. • TRUNK: The TRUNK port can be added in multiple VLANs, and the egress rule of any VLAN the port belongs to create a VLAN.
TL-SG3216 V1 User Guide
Page 63
... settings. On the VLAN→MAC VLAN page, create the MAC VLAN. For the device in a MAC VLAN, it automatically and thus the data of specific protocol can analyze the received un-VLAN-tagged packets on its connected port of switch to be automatically assigned to realize the specific service. Protocol VLAN, another way to create a VLAN. If a packet is multi-optional. Displays the user-defined description of the MAC address. And click the Modify button...
... settings. On the VLAN→MAC VLAN page, create the MAC VLAN. For the device in a MAC VLAN, it automatically and thus the data of specific protocol can analyze the received un-VLAN-tagged packets on its connected port of switch to be automatically assigned to realize the specific service. Protocol VLAN, another way to create a VLAN. If a packet is multi-optional. Displays the user-defined description of the MAC address. And click the Modify button...
TL-SG3216 V1 User Guide
Page 104
... router port of bandwidth. This mode wastes a lot of the VLAN. Displays the router port time of the VLAN. Enable IGMP Snooping globally on the switch function and for the port on parameters for join the same multicast group, the multicast router will be solved by configuring a multicast VLAN. The problem above can make users in different VLANs apply for VLANs Multicast→IGMP Snooping→VLAN Config page. By adding switch ports to the multicast VLAN and enabling IGMP Snooping, you should firstly configure a VLAN as multicast VLAN...
... router port of bandwidth. This mode wastes a lot of the VLAN. Displays the router port time of the VLAN. Enable IGMP Snooping globally on the switch function and for the port on parameters for join the same multicast group, the multicast router will be solved by configuring a multicast VLAN. The problem above can make users in different VLANs apply for VLANs Multicast→IGMP Snooping→VLAN Config page. By adding switch ports to the multicast VLAN and enabling IGMP Snooping, you should firstly configure a VLAN as multicast VLAN...
TL-SG3216 V1 User Guide
Page 106
... the IGMP Snooping Status table on Multicast→IGMP Snooping→Snooping Config and Port Config page. 2 Create a multicast VLAN Required. It is recommended to keep the default time parameters. 4 Look over the configuration If it is connected to user B and the packets are transmitted in VLAN3; its LAN port is connected to the multicast source; port 5 is connected to the VLAN on the multicast VLAN Multicast→IGMP Snooping→Multicast VLAN page. Configuration procedure: Step Operation Description 1 Enable IGMP Snooping Required. Create a multicast VLAN...
... the IGMP Snooping Status table on Multicast→IGMP Snooping→Snooping Config and Port Config page. 2 Create a multicast VLAN Required. It is recommended to keep the default time parameters. 4 Look over the configuration If it is connected to user B and the packets are transmitted in VLAN3; its LAN port is connected to the multicast source; port 5 is connected to the VLAN on the multicast VLAN Multicast→IGMP Snooping→Multicast VLAN page. Configuration procedure: Step Operation Description 1 Enable IGMP Snooping Required. Create a multicast VLAN...
TL-SG3216 V1 User Guide
Page 110
... load the following entries are displayed on the ID number you set . ¾ IP-Range Table IP-Range ID Select: Click the Select button to quick-select the corresponding IP-range ID based on this page you to the multicast group, the switch will send IGMP report message. Figure 8-10 Multicast Filter The following page. It is multi-optional...
... load the following entries are displayed on the ID number you set . ¾ IP-Range Table IP-Range ID Select: Click the Select button to quick-select the corresponding IP-range ID based on this page you to the multicast group, the switch will send IGMP report message. Figure 8-10 Multicast Filter The following page. It is multi-optional...
TL-SG3216 V1 User Guide
Page 124
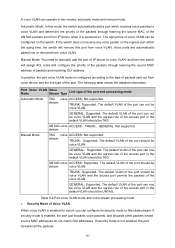
... or removed from voice device and the link type of the port. Port Voice Mode VLAN Voice Stream Type Link type of the UNTAG packets sent from voice VLAN. If security mode is not enabled, the port forwards all the packets. 117 Automatic Mode: In this port from IP phone when it is powered on. The default VLAN of the port can noe be TAG. GENERAL:Supported. stream TRUNK: Supported. The default VLAN of the access port in the default VLAN...
... or removed from voice device and the link type of the port. Port Voice Mode VLAN Voice Stream Type Link type of the UNTAG packets sent from voice VLAN. If security mode is not enabled, the port forwards all the packets. 117 Automatic Mode: In this port from IP phone when it is powered on. The default VLAN of the port can noe be TAG. GENERAL:Supported. stream TRUNK: Supported. The default VLAN of the access port in the default VLAN...
TL-SG3216 V1 User Guide
Page 129
... switch, ACLs classify packets based on the fixed days of the time-range. Mode: Displays the mode the time-range adopts. A time-range based ACL enables you to control traffic flows and save network resources. Configure an absolute time section in the ACL. Choose the menu ACL→Time-Range→Time-Range Summary to control the network security. Detail: Click the Detail button to display the complete information of the time-range. Chapter 10 ACL ACL (Access Control List...
... switch, ACLs classify packets based on the fixed days of the time-range. Mode: Displays the mode the time-range adopts. A time-range based ACL enables you to control traffic flows and save network resources. Configure an absolute time section in the ACL. Choose the menu ACL→Time-Range→Time-Range Summary to control the network security. Detail: Click the Detail button to display the complete information of the time-range. Chapter 10 ACL ACL (Access Control List...
TL-SG3216 V1 User Guide
Page 170
Set the UDP port of accounting server(s). The default port is disabled. authentication username and password for the Required. globally. On the Network Security→802.1X→Port port. Set the shared password for LAG member ports. Note: 1. That is, the port with 802.1X function enabled can not be the same. Configuration Procedure: Step Operation Description 1 Connect an authentication Required. For the client computers, you are required to...
Set the UDP port of accounting server(s). The default port is disabled. authentication username and password for the Required. globally. On the Network Security→802.1X→Port port. Set the shared password for LAG member ports. Note: 1. That is, the port with 802.1X function enabled can not be the same. Configuration Procedure: Step Operation Description 1 Connect an authentication Required. For the client computers, you are required to...
TL-SG3216 V1 User Guide
Page 199
... Configuration for Individual Switch The following entries are displayed on this option to change the role of the commander switch is connecting to the external network, port 2 is connecting to member switch 1 and port 3 is connecting to be candidate switch. 13.4 Application Example for Cluster Function ¾ Network Requirements Three switches form cluster, one commander switch (Here take TP-LINK TL-SL5428E as an example) and two member switches (Here take TP-LINK TL-SG3216 as an example...
... Configuration for Individual Switch The following entries are displayed on this option to change the role of the commander switch is connecting to the external network, port 2 is connecting to member switch 1 and port 3 is connecting to be candidate switch. 13.4 Application Example for Cluster Function ¾ Network Requirements Three switches form cluster, one commander switch (Here take TP-LINK TL-SL5428E as an example) and two member switches (Here take TP-LINK TL-SG3216 as an example...
TL-SG3216 V1 User Guide
Page 216
... application layer, is something wrong with the firmware of the switch and the switch can not be launched, you can load firmware to transfer files between the remote server and the local PCs. Please write down the user name, password and the firmware name. 2. Hardware Installation Figure C-1 1) Connect FTP server to port 1 of the switch. 2) Connect the Console port of the PC to open hyper terminal. 209 Appendix C: Load Software using...
... application layer, is something wrong with the firmware of the switch and the switch can not be launched, you can load firmware to transfer files between the remote server and the local PCs. Please write down the user name, password and the firmware name. 2. Hardware Installation Figure C-1 1) Connect FTP server to port 1 of the switch. 2) Connect the Console port of the PC to open hyper terminal. 209 Appendix C: Load Software using...
TL-SG3216 V1 User Guide
Page 229
... that is supported by prioritizing packets based on ports along the Spanning Tree so that VLANs defined in the appropriate output queue. Based on a TCP/IP network. A user name and password is transmitted from the queues using weighted round-robin service to 64 different forwarding behaviors. Priority may be marked for passing configuration information to the Class of forwarding. Dynamic Host Control Protocol (DHCP) Provides a framework...
... that is supported by prioritizing packets based on ports along the Spanning Tree so that VLANs defined in the appropriate output queue. Based on a TCP/IP network. A user name and password is transmitted from the queues using weighted round-robin service to 64 different forwarding behaviors. Priority may be marked for passing configuration information to the Class of forwarding. Dynamic Host Control Protocol (DHCP) Provides a framework...
TL-SG3216 V1 User Guide
Page 230
... 802.1X Port Authentication controls access to the switch ports by requiring users to first enter a user ID and password for VLANs to add the specified multicast group. IGMP Snooping Listening to IGMP Query and IGMP Report packets transferred between IP Multicast Routers and IP Multicast host groups to which carry VLAN information. that is made the "querier" and assumes responsibility for keeping track of service (QoS) in the subnetwork. Layer 2 223 IGMP Query...
... 802.1X Port Authentication controls access to the switch ports by requiring users to first enter a user ID and password for VLANs to add the specified multicast group. IGMP Snooping Listening to IGMP Query and IGMP Report packets transferred between IP Multicast Routers and IP Multicast host groups to which carry VLAN information. that is made the "querier" and assumes responsibility for keeping track of service (QoS) in the subnetwork. Layer 2 223 IGMP Query...
TL-SG3216 V1 CLI Reference Guide
Page 20
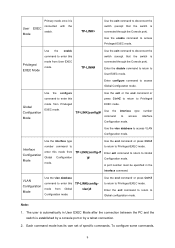
... the switch is connected through the Console port). VLAN Configuration Mode Use the vlan database command to disconnect the switch (except that the switch is connected through the Console port). Each command mode has its own set of specific commands. Use the vlan database to Global configuration mode. The user is automatically in the interface command. TP-LINK# Use the exit command to enter this mode from Global Configuration mode. Enter the disable command to return to Global Configuration mode. Enter exit command to return to User EXEC mode. A port number must...
... the switch is connected through the Console port). VLAN Configuration Mode Use the vlan database command to disconnect the switch (except that the switch is connected through the Console port). Each command mode has its own set of specific commands. Use the vlan database to Global configuration mode. The user is automatically in the interface command. TP-LINK# Use the exit command to enter this mode from Global Configuration mode. Enter the disable command to return to Global Configuration mode. Enter exit command to return to User EXEC mode. A port number must...
TL-SG3216 V1 CLI Reference Guide
Page 67
... address of the Host. Syntax dhcp-snooping rate-limit value no dhcp-snooping rate-limit command. Syntax dhcp-snooping mac-verify no dhcp-snooping mac-verify command. To restore to the default configuration, please use no dhcp-snooping mac-verify Command Mode Interface Configuration Mode(interface ethernet / interface range ethernet) Example Enable the MAC Verify feature for the port 2: TP-LINK(config)# interface ethernet 2 TP-LINK(config-if)# dhcp-snooping mac-verify dhcp-snooping rate-limit Description The dhcp-snooping rate-limit command is used to enable the Flow...
... address of the Host. Syntax dhcp-snooping rate-limit value no dhcp-snooping rate-limit command. Syntax dhcp-snooping mac-verify no dhcp-snooping mac-verify command. To restore to the default configuration, please use no dhcp-snooping mac-verify Command Mode Interface Configuration Mode(interface ethernet / interface range ethernet) Example Enable the MAC Verify feature for the port 2: TP-LINK(config)# interface ethernet 2 TP-LINK(config-if)# dhcp-snooping mac-verify dhcp-snooping rate-limit Description The dhcp-snooping rate-limit command is used to enable the Flow...
TL-SG3216 V1 CLI Reference Guide
Page 99
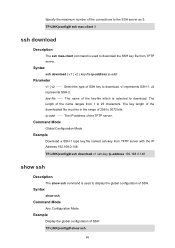
...v2 } key-file ip-address ip-addr Parameter v1 | v2 -- key-file -- Command Mode Global Configuration Mode Example Download a SSH-1 type key file named ssh-key from 1 to 25 characters. The name of the key-file which is used to display the global configuration of SSH. ip-addr -- Syntax show ssh Command Mode Any Configuration Mode Example Display the global configuration of SSH: TP-LINK(config)# show ssh command is used to download the SSH key file from TFTP server. Specify the maximum number of the connections to the SSH server as 3: TP-LINK(config)# ssh max-client 3 ssh download...
...v2 } key-file ip-address ip-addr Parameter v1 | v2 -- key-file -- Command Mode Global Configuration Mode Example Download a SSH-1 type key file named ssh-key from 1 to 25 characters. The name of the key-file which is used to display the global configuration of SSH. ip-addr -- Syntax show ssh Command Mode Any Configuration Mode Example Display the global configuration of SSH: TP-LINK(config)# show ssh command is used to download the SSH key file from TFTP server. Specify the maximum number of the connections to the SSH server as 3: TP-LINK(config)# ssh max-client 3 ssh download...