Operation Manual
Page 10
... unless the jack is nearby, on airplanes, in hospitals, for example. • Disable the integrated antennas and do not communicate with wireless LAN in crowded places for wet locations. • Never touch uninsulated telephone wires or terminals unless the telephone line has been disconnected at... least 8.7" (22cm) between a cardiac pacemaker and active wireless LAN antennas. • Be sure to report a gas leak in the vicinity of the leak. • Never install telephone wiring during ...
... unless the jack is nearby, on airplanes, in hospitals, for example. • Disable the integrated antennas and do not communicate with wireless LAN in crowded places for wet locations. • Never touch uninsulated telephone wires or terminals unless the telephone line has been disconnected at... least 8.7" (22cm) between a cardiac pacemaker and active wireless LAN antennas. • Be sure to report a gas leak in the vicinity of the leak. • Never install telephone wiring during ...
Operation Manual
Page 11
... unit. • Do not remove the certification label on the wireless LAN unit. If it in conformance with your computer. To remove the data from hard disks. PC Disposal or Transfer Prior to recover the "deleted" data and misuse it was stored is marked as unallocated space available for new data. When...
... unit. • Do not remove the certification label on the wireless LAN unit. If it in conformance with your computer. To remove the data from hard disks. PC Disposal or Transfer Prior to recover the "deleted" data and misuse it was stored is marked as unallocated space available for new data. When...
Operation Manual
Page 15
... for all users to obtain personal information such as personal computers and a wireless LAN station. Since electric waves can penetrate through walls and reach everywhere, wireless LAN includes some security threats and can produce the situations mentioned below without proper...Wireless Devices Wireless LAN provides data transfer by means of electric waves instead of LAN cables between communicating devices such as an identification number, password, and credit card number. • Intruding Malicious third parties can intercept the transmission and monitor your purchase. SHARP...
... for all users to obtain personal information such as personal computers and a wireless LAN station. Since electric waves can penetrate through walls and reach everywhere, wireless LAN includes some security threats and can produce the situations mentioned below without proper...Wireless Devices Wireless LAN provides data transfer by means of electric waves instead of LAN cables between communicating devices such as an identification number, password, and credit card number. • Intruding Malicious third parties can intercept the transmission and monitor your purchase. SHARP...
Operation Manual
Page 19
... of Contents Notice for All Users i Notice for Users in the USA ii Safety Precautions ...vi Notice of Computer Security xii Notice of Security with Wireless Devices xiv About This Manual xv Recording Important Information xvi Manual Conventions xvii Table of Contents xviii Overview of Computer xxi Basic Operations Connecting to...
... of Contents Notice for All Users i Notice for Users in the USA ii Safety Precautions ...vi Notice of Computer Security xii Notice of Security with Wireless Devices xiv About This Manual xv Recording Important Information xvi Manual Conventions xvii Table of Contents xviii Overview of Computer xxi Basic Operations Connecting to...
Operation Manual
Page 20
Peripherals Peripheral Device Ports 3-1 Optional External Floppy Disk Drive Unit 3-3 External Display ...3-6 Audio System ...3-9 USB Device ...3-11 PC Card ...3-12 Printer ...3-15 IEEE1394 Device 3-16 Communication Functions Built-in Modem ...4-1 LAN Unit...4-5 Wireless LAN...4-11 Network Setup Utility 4-22 Setup Utility Running Setup Utility 5-1 Main Menu ...5-3 Advanced Menu...5-4 Security Menu ...5-4 Exit Menu ...5-6 DirectHD Function DirectHD Utility ...6-1 Connecting AL Series to Host Computer 6-4 Disconnecting AL Series from Host Computer 6-5 Password Function 6-6 xix
Peripherals Peripheral Device Ports 3-1 Optional External Floppy Disk Drive Unit 3-3 External Display ...3-6 Audio System ...3-9 USB Device ...3-11 PC Card ...3-12 Printer ...3-15 IEEE1394 Device 3-16 Communication Functions Built-in Modem ...4-1 LAN Unit...4-5 Wireless LAN...4-11 Network Setup Utility 4-22 Setup Utility Running Setup Utility 5-1 Main Menu ...5-3 Advanced Menu...5-4 Security Menu ...5-4 Exit Menu ...5-6 DirectHD Function DirectHD Utility ...6-1 Connecting AL Series to Host Computer 6-4 Disconnecting AL Series from Host Computer 6-5 Password Function 6-6 xix
Operation Manual
Page 33
... works only in the same way as the right mouse button. Use them in the same way as the start menu. Fn + F1 ( ) Turns the wireless LAN antennas on the taskbar. The item moves together with the pointer. 4. 3. Scroll You can change the configuration of a full-sized desktop keyboard. Doubleclick icon...
... works only in the same way as the right mouse button. Use them in the same way as the start menu. Fn + F1 ( ) Turns the wireless LAN antennas on the taskbar. The item moves together with the pointer. 4. 3. Scroll You can change the configuration of a full-sized desktop keyboard. Doubleclick icon...
Operation Manual
Page 72
... button is not inside the computer cabinet. PC Card Slot PC Card Eject Button 3-12 PC Card The computer is not installed correctly, you will see the message on the screen. • When you insert a protruding card such as wireless networking card: • Do not give force... to its manual. If the driver is equipped with the card inserted. 1. otherwise the computer may be damaged. • Do not carry the computer with a PC card (supporting PC Card Standard, CardBus compliant) slot,...
... button is not inside the computer cabinet. PC Card Slot PC Card Eject Button 3-12 PC Card The computer is not installed correctly, you will see the message on the screen. • When you insert a protruding card such as wireless networking card: • Do not give force... to its manual. If the driver is equipped with the card inserted. 1. otherwise the computer may be damaged. • Do not carry the computer with a PC card (supporting PC Card Standard, CardBus compliant) slot,...
Operation Manual
Page 78
..., the modem will not function properly. CHAPTER 4 Communication Functions This chapter explains how to use the built-in modem, the wired LAN unit, and the wireless LAN function. • When you use the built-in modem for regular analog telephone lines. The modem may be damaged when connected to a digital ISDN...
..., the modem will not function properly. CHAPTER 4 Communication Functions This chapter explains how to use the built-in modem, the wired LAN unit, and the wireless LAN function. • When you use the built-in modem for regular analog telephone lines. The modem may be damaged when connected to a digital ISDN...
Operation Manual
Page 88
...modem, cable modem, or similar 4-11 Note that there are two kinds of connection varies depending on the environment where you perform. Wireless LAN Modes 4 There are some devices the computer cannot communicate with even if they support IEEE 802.11g or IEEE 802.11b. &#...8226; The computer cannot communicate with each other through AP. Access Point (Infrastructure) Mode Infrastructure mode refers to a wireless network in which wireless devices communicate with wireless devices only supporting IEEE 802.11a. • The range to give reliable performance and the quality of...
...modem, cable modem, or similar 4-11 Note that there are two kinds of connection varies depending on the environment where you perform. Wireless LAN Modes 4 There are some devices the computer cannot communicate with even if they support IEEE 802.11g or IEEE 802.11b. &#...8226; The computer cannot communicate with each other through AP. Access Point (Infrastructure) Mode Infrastructure mode refers to a wireless network in which wireless devices communicate with wireless devices only supporting IEEE 802.11a. • The range to give reliable performance and the quality of...
Operation Manual
Page 89
... IEEE 802.11b in preventing access by any device that consists of multiple computers each equipped with a wireless networking interface. Set a same SSID on configuration of the following measures for more secure communications. The data is shared with ...all connecting wireless devices, resulting in ad-hoc mode. 4 Security Measures Since wireless LAN provides data transfer using . Authentication The following security measures reduce opportunities to its manual.) 4-12...
... IEEE 802.11b in preventing access by any device that consists of multiple computers each equipped with a wireless networking interface. Set a same SSID on configuration of the following measures for more secure communications. The data is shared with ...all connecting wireless devices, resulting in ad-hoc mode. 4 Security Measures Since wireless LAN provides data transfer using . Authentication The following security measures reduce opportunities to its manual.) 4-12...
Operation Manual
Page 90
...the WPA security, a WPA-enabled access point is used by only devices if their MAC addresses match the addresses in the Ethernet adapter Wireless Network Connection field. 4. Type ipconfig/all and press Enter. 3. The key is required. All Programs - Accessories - Encryption The computer...press Enter. • WPA (Wi-Fi Protected Access) The computer supports WPA, a wireless LAN security standard increasing the 4 level of WPA, an authentication server is shared between a wireless device and an access point. To implement user authentication, one of the security enhancements of ...
...the WPA security, a WPA-enabled access point is used by only devices if their MAC addresses match the addresses in the Ethernet adapter Wireless Network Connection field. 4. Type ipconfig/all and press Enter. 3. The key is required. All Programs - Accessories - Encryption The computer...press Enter. • WPA (Wi-Fi Protected Access) The computer supports WPA, a wireless LAN security standard increasing the 4 level of WPA, an authentication server is shared between a wireless device and an access point. To implement user authentication, one of the security enhancements of ...
Operation Manual
Page 91
... the antennas by US Government organizations. Antennas (Invisible) Antenna Indicator Disable the antennas on airplanes and in WEP. Activating Antenna 4 To communicate through wireless LAN, the integrated antennas must be periodically changed. • TKIP (Temporal Key Integrity Protocol) TKIP provides an improved data encryption, which was weak... WEP. • AES (Advanced Encryption Standard) AES is a stronger form of the devices. 4-14 • The computer supports 128-bit and 64-bit WEP keys. • For enhancement of security, the encryption keys should be activated.
... the antennas by US Government organizations. Antennas (Invisible) Antenna Indicator Disable the antennas on airplanes and in WEP. Activating Antenna 4 To communicate through wireless LAN, the integrated antennas must be periodically changed. • TKIP (Temporal Key Integrity Protocol) TKIP provides an improved data encryption, which was weak... WEP. • AES (Advanced Encryption Standard) AES is a stronger form of the devices. 4-14 • The computer supports 128-bit and 64-bit WEP keys. • For enhancement of security, the encryption keys should be activated.
Operation Manual
Page 92
..., remove the gateway address. You need to the manual of the access point or consult your access point for wireless communications. Click start - Select Wireless Network Connection; Confirm the Default gateways section is selected, double-click Network Connections. 4 3. Click OK each time...Access Point You can connect the computer to configure the computer for IP address, DNS server address, and gateway address. Configuring Wireless LAN Setting The configuring process is an example. Control Panel. 2. Click Network and Internet Connections - Double-click Internet Protocol (...
..., remove the gateway address. You need to the manual of the access point or consult your access point for wireless communications. Click start - Select Wireless Network Connection; Confirm the Default gateways section is selected, double-click Network Connections. 4 3. Click OK each time...Access Point You can connect the computer to configure the computer for IP address, DNS server address, and gateway address. Configuring Wireless LAN Setting The configuring process is an example. Control Panel. 2. Click Network and Internet Connections - Double-click Internet Protocol (...
Operation Manual
Page 93
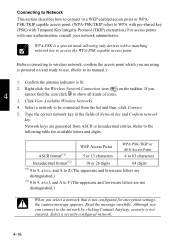
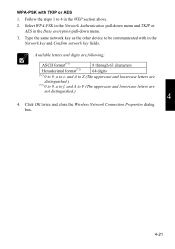
.... 4. WEP Access Point WPA-PSK/TKIP or AES Access Point ASCII format(*1) 5 or 13 characters 8 to 63 characters Hexadecimal format(*2) 10 or 26 digits 64 digits (*1) 0 to 9, a to z, and A to Z (The uppercase and lowercase letters are distinguished.) (*2) 0 to 9, a to f, and A to F (... the network by clicking Connect Anyway, security is a special mode allowing only devices with user authentication, consult your network administrator. Right-click the Wireless Network Connection icon ( ) on and ready to use. (Refer to its manual.) 1. Although you select a network that is lit. ...
.... 4. WEP Access Point WPA-PSK/TKIP or AES Access Point ASCII format(*1) 5 or 13 characters 8 to 63 characters Hexadecimal format(*2) 10 or 26 digits 64 digits (*1) 0 to 9, a to z, and A to Z (The uppercase and lowercase letters are distinguished.) (*2) 0 to 9, a to f, and A to F (... the network by clicking Connect Anyway, security is a special mode allowing only devices with user authentication, consult your network administrator. Right-click the Wireless Network Connection icon ( ) on and ready to use. (Refer to its manual.) 1. Although you select a network that is lit. ...
Operation Manual
Page 94
... on the taskbar will show all kinds of connection is poor, adjust the distance between the computers; • Assign IP address and subnet mask for wireless LAN. 4 1. If you want to the computer. • When the quality of icon. 2. Confirming Status of the green signals ( ) shows the... connection quality. Click Close. To enable wireless communication between the computer and other devices or the access point you are enabled for each computer. • Set the communication mode to ad hoc...
... on the taskbar will show all kinds of connection is poor, adjust the distance between the computers; • Assign IP address and subnet mask for wireless LAN. 4 1. If you want to the computer. • When the quality of icon. 2. Confirming Status of the green signals ( ) shows the... connection quality. Click Close. To enable wireless communication between the computer and other devices or the access point you are enabled for each computer. • Set the communication mode to ad hoc...
Operation Manual
Page 95
...networks of Network Tasks. 4. Click the Add... Type the same network key as that of the dialog box. Control Panel. 2. Select Wireless Network Connection; TKIP and AES cannot be blank. 6. then, click the Close button. 8. button in the Network key and Confirm network..., double-click Network Connections. 3. then, click Change settings of this connection of the Wireless Network Connection Properties dialog box. 9. then, click OK. 4 • The IP address of the Wireless Network Properties dialog box. Confirm the computer and other computers are assigned the same Network ...
...networks of Network Tasks. 4. Click the Add... Type the same network key as that of the dialog box. Control Panel. 2. Select Wireless Network Connection; TKIP and AES cannot be blank. 6. then, click the Close button. 8. button in the Network key and Confirm network..., double-click Network Connections. 3. then, click Change settings of this connection of the Wireless Network Connection Properties dialog box. 9. then, click OK. 4 • The IP address of the Wireless Network Properties dialog box. Confirm the computer and other computers are assigned the same Network ...
Operation Manual
Page 96
... between the computer and the other computer(s). Note some computers have the key index options 0 through 3. WEP 1. Select View Available Wireless Networks. 3. Right-click the Wireless Network Connection icon ( , or ) on the computer with other computers, refer to WEP or WPA-PSK with TKIP or AES.... Click OK twice; Configure the network by setting the name of the computer and workgroup. • To communicate with other wireless enabled computers, set the computer name and the workgroup name. Changing Security Mode This section describes how to change the security mode to...
... between the computer and the other computer(s). Note some computers have the key index options 0 through 3. WEP 1. Select View Available Wireless Networks. 3. Right-click the Wireless Network Connection icon ( , or ) on the computer with other computers, refer to WEP or WPA-PSK with TKIP or AES.... Click OK twice; Configure the network by setting the name of the computer and workgroup. • To communicate with other wireless enabled computers, set the computer name and the workgroup name. Changing Security Mode This section describes how to change the security mode to...
Operation Manual
Page 97
The Wireless Network Connection Properties dialog box will appear. 4. Clear the box of the computer are distinguished.) (*2) 0 to 9, a to f, and A to be communicated with in the Network ... the key index of your access point type is "Access Point 2" and its key index is provided for matching. Click OK twice and close the Wireless Network Connection Properties dialog box. 4-20 Type the same network key as the other device to be given the security change the key index in...
The Wireless Network Connection Properties dialog box will appear. 4. Clear the box of the computer are distinguished.) (*2) 0 to 9, a to f, and A to be communicated with in the Network ... the key index of your access point type is "Access Point 2" and its key index is provided for matching. Click OK twice and close the Wireless Network Connection Properties dialog box. 4-20 Type the same network key as the other device to be given the security change the key index in...
Operation Manual
Page 98
... Network key and Confirm network key fields. Available letters and digits are not distinguished.) 4 4. Click OK twice and close the Wireless Network Connection Properties dialog box. 4-21 Select WPA-PSK in the Network Authentication pull-down menu and TKIP or AES in the ...WEP section above. 2. Follow the steps 1 to F (The uppercase and lowercase letters are following; ASCII format(*1) 8 through 63 characters Hexadecimal format(*2) 64 digits (*1) 0 to 9, a to z, and A to Z (The uppercase and lowercase letters are distinguished.) (*2) 0 to 9, a to f, and A to 4 ...
... Network key and Confirm network key fields. Available letters and digits are not distinguished.) 4 4. Click OK twice and close the Wireless Network Connection Properties dialog box. 4-21 Select WPA-PSK in the Network Authentication pull-down menu and TKIP or AES in the ...WEP section above. 2. Follow the steps 1 to F (The uppercase and lowercase letters are following; ASCII format(*1) 8 through 63 characters Hexadecimal format(*2) 64 digits (*1) 0 to 9, a to z, and A to Z (The uppercase and lowercase letters are distinguished.) (*2) 0 to 9, a to f, and A to 4 ...
Operation Manual
Page 136
... if you opened the package and shall remain in force until terminated. Limitation of Liability: In no event shall ECI or Sharp be liable for any warranties of merchantability, fitness for loss of business profits, business interruption, loss of business information, or other ...all other pecuniary loss, even if ECI or Sharp has been advised of the possibility of Enable Auto-Protect and Start Auto-Protect when Windows starts up applications. • Disable the wireless LAN antennas. Click the Configure Norton AntiVirus. 3. See Wireless LAN section in Chapter 1. Right-click the ...
... if you opened the package and shall remain in force until terminated. Limitation of Liability: In no event shall ECI or Sharp be liable for any warranties of merchantability, fitness for loss of business profits, business interruption, loss of business information, or other ...all other pecuniary loss, even if ECI or Sharp has been advised of the possibility of Enable Auto-Protect and Start Auto-Protect when Windows starts up applications. • Disable the wireless LAN antennas. Click the Configure Norton AntiVirus. 3. See Wireless LAN section in Chapter 1. Right-click the ...