Manuals
Page 51
... details about how to use the Document Server function, see "Specifying the Settings for registering a shortcut using the browser function. Shortcut icon You can also review icons of Favorites, see "Specifying the Settings for registering Web pages to store or print documents on the [Home] Screen", Convenient Functions .
... details about how to use the Document Server function, see "Specifying the Settings for registering a shortcut using the browser function. Shortcut icon You can also review icons of Favorites, see "Specifying the Settings for registering Web pages to store or print documents on the [Home] Screen", Convenient Functions .
Security Target
Page 37
... guidance document and users are aware of the security policies and procedures of their organisation and are identified and described. Copyright (c) 2012 RICOH COMPANY, LTD. P.AUDIT.LOGGING Management of audit log records The TOE shall create and maintain a log of TOE use the TOE... itself and RC Gate. 3.3 Assumptions The assumptions related to this TOE usage environment are competent to follow those interfaces shall be reviewed by authorised persons. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that...
... guidance document and users are aware of the security policies and procedures of their organisation and are identified and described. Copyright (c) 2012 RICOH COMPANY, LTD. P.AUDIT.LOGGING Management of audit log records The TOE shall create and maintain a log of TOE use the TOE... itself and RC Gate. 3.3 Assumptions The assumptions related to this TOE usage environment are competent to follow those interfaces shall be reviewed by authorised persons. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that...
Security Target
Page 41
...guidance document for detecting security violations or unusual patterns of activity. have the competence to follow the guidance document; OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that administrators are aware of the security policies and procedures of their organisation....AUTHORIZED Assignment of user authority The responsible manager of MFP shall give users the authority to use their organisation. Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of 93 OE.INTERFACE.MANAGED Management of external interfaces in IT environment The IT environment shall take a...
...guidance document for detecting security violations or unusual patterns of activity. have the competence to follow the guidance document; OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that administrators are aware of the security policies and procedures of their organisation....AUTHORIZED Assignment of user authority The responsible manager of MFP shall give users the authority to use their organisation. Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of 93 OE.INTERFACE.MANAGED Management of external interfaces in IT environment The IT environment shall take a...
Security Target
Page 42
...NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTEC T OE.ADMIN.TRAINED OE.ADMIN.TRUSTED OE.USER.TRAINED T.DOC.....VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD.
...NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTEC T OE.ADMIN.TRAINED OE.ADMIN.TRUSTED OE.USER.TRAINED T.DOC.....VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 45
...and alteration. By OE.PHYSICAL.MANAGED, the TOE is enforced by the unauthorised persons. By OE.AUDIT.REVIEWED, the responsible manager of MFP reviews audit logs at appropriate intervals for security violations or unusual patterns of activity according to another trusted IT product....ENCRYPTED. A.ACCESS.MANAGED A.ACCESS.MANAGED is enforced by authorised persons. A.ACCESS.MANAGED is enforced by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. All rights reserved. By OE.AUDIT_STORAGE.PROTECTED, if audit records are exported from the...
...and alteration. By OE.PHYSICAL.MANAGED, the TOE is enforced by the unauthorised persons. By OE.AUDIT.REVIEWED, the responsible manager of MFP reviews audit logs at appropriate intervals for security violations or unusual patterns of activity according to another trusted IT product....ENCRYPTED. A.ACCESS.MANAGED A.ACCESS.MANAGED is enforced by authorised persons. A.ACCESS.MANAGED is enforced by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. All rights reserved. By OE.AUDIT_STORAGE.PROTECTED, if audit records are exported from the...
Security Target
Page 52
... data loss Hierarchical to: FAU_STG.3 Action in the audit trail from the audit records. FAU_SAR.1 Audit review Hierarchical to associate each auditable event with the identity of the user that caused the event. Copyright (c) 2012 RICOH COMPANY, LTD. Dependencies: FAU_GEN.1 Audit data generation FIA_UID.1 Timing of identification FAU_GEN.2.1 For audit events resulting...
... data loss Hierarchical to: FAU_STG.3 Action in the audit trail from the audit records. FAU_SAR.1 Audit review Hierarchical to associate each auditable event with the identity of the user that caused the event. Copyright (c) 2012 RICOH COMPANY, LTD. Dependencies: FAU_GEN.1 Audit data generation FIA_UID.1 Timing of identification FAU_GEN.2.1 For audit events resulting...
Security Target
Page 53
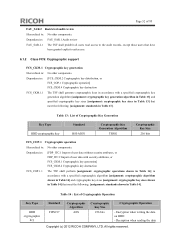
... 256 bits Cryptographic Operation - Dependencies: [FDP_ITC.1 Import of user data without security attributes, or FDP_ITC.2 Import of 93 FAU_SAR.2 Restricted audit review Hierarchical to : No other components. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all users read access to the audit records, except those users that have been granted explicit... key sizes [assignment: cryptographic key sizes in Table 13] that meet the following : [assignment: standards in Table 14]. Decryption when reading the data Copyright (c) 2012 RICOH COMPANY, LTD.
... 256 bits Cryptographic Operation - Dependencies: [FDP_ITC.1 Import of user data without security attributes, or FDP_ITC.2 Import of 93 FAU_SAR.2 Restricted audit review Hierarchical to : No other components. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all users read access to the audit records, except those users that have been granted explicit... key sizes [assignment: cryptographic key sizes in Table 13] that meet the following : [assignment: standards in Table 14]. Decryption when reading the data Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 81
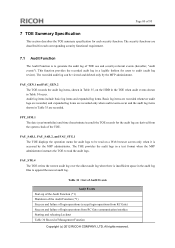
Page 80 of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in Table 35, on a Web browser screen only when it is accessed ... be read the audit logs. FAU_STG.4 The TOE writes the newest audit log over the oldest audit log when there is to audit (audit log review). The security functions are derived from RC Gate communication interface Starting and releasing Lockout Table 30 Record of 93 7 TOE Summary Specification This section describes...
Page 80 of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in Table 35, on a Web browser screen only when it is accessed ... be read the audit logs. FAU_STG.4 The TOE writes the newest audit log over the oldest audit log when there is to audit (audit log review). The security functions are derived from RC Gate communication interface Starting and releasing Lockout Table 30 Record of 93 7 TOE Summary Specification This section describes...