User Guide
Page 43
...", Convenient Functions . • For details about the procedure for registering Web pages to Favorites, see p.41 "Adding Icons to the [Home] Screen". You can also review icons of functions and embedded software applications that are registered to Favorites by User cannot be registered to use the Document Server function, see p.45...
...", Convenient Functions . • For details about the procedure for registering Web pages to Favorites, see p.41 "Adding Icons to the [Home] Screen". You can also review icons of functions and embedded software applications that are registered to Favorites by User cannot be registered to use the Document Server function, see p.45...
Security Target
Page 37
The audit log shall be reviewed by authorised persons. P.STORAGE.ENCRYPTION Encryption of storage devices The data stored on the HDD inside the TOE shall be controlled by unauthorised persons. A.... the external interfaces of the TOE, operation of communication with RC Gate As for communication with operation permission of TOE use the TOE. Copyright (c) 2012 RICOH COMPANY, LTD. P.RCGATE.COMM.PROTECT Protection of those policies and procedures. 3.2 Organisational Security Policies The following organisational security policies are identified and described. A.ACCESS....
The audit log shall be reviewed by authorised persons. P.STORAGE.ENCRYPTION Encryption of storage devices The data stored on the HDD inside the TOE shall be controlled by unauthorised persons. A.... the external interfaces of the TOE, operation of communication with RC Gate As for communication with operation permission of TOE use the TOE. Copyright (c) 2012 RICOH COMPANY, LTD. P.RCGATE.COMM.PROTECT Protection of those policies and procedures. 3.2 Organisational Security Policies The following organisational security policies are identified and described. A.ACCESS....
Security Target
Page 41
... organisation; and correctly configure and operate the TOE according to follow those policies and procedures. All rights reserved. Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of 93 OE.INTERFACE.MANAGED Management of external interfaces in IT environment The IT environment shall take a... countermeasure for detecting security violations or unusual patterns of activity. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that audit logs are reviewed at appropriate intervals according to the guidance document for the prevention of unmanaged access to TOE...
... organisation; and correctly configure and operate the TOE according to follow those policies and procedures. All rights reserved. Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of 93 OE.INTERFACE.MANAGED Management of external interfaces in IT environment The IT environment shall take a... countermeasure for detecting security violations or unusual patterns of activity. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that audit logs are reviewed at appropriate intervals according to the guidance document for the prevention of unmanaged access to TOE...
Security Target
Page 42
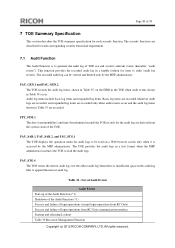
...NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE....STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. Page 41 of Security Objectives Table 11 describes the correspondence between the assumptions, threats and organisational security ...
...NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE....STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. Page 41 of Security Objectives Table 11 describes the correspondence between the assumptions, threats and organisational security ...
Security Target
Page 45
... responsible manager of MFP reviews audit logs at appropriate intervals for security violations or unusual patterns of activity according to TOE external interfaces. P.RCGATE.COMM.PROTECT is enforced by authorised persons. Copyright (c) 2012 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT P.INTERFACE.MANAGEMENT is enforced... RC Gate, and detect any tampering with the security policies. A.ACCESS.MANAGED is upheld by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. Page 44 of 93 P.AUDIT.LOGGING P.AUDIT.LOGGING is enforced by this objective...
... responsible manager of MFP reviews audit logs at appropriate intervals for security violations or unusual patterns of activity according to TOE external interfaces. P.RCGATE.COMM.PROTECT is enforced by authorised persons. Copyright (c) 2012 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT P.INTERFACE.MANAGEMENT is enforced... RC Gate, and detect any tampering with the security policies. A.ACCESS.MANAGED is upheld by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. Page 44 of 93 P.AUDIT.LOGGING P.AUDIT.LOGGING is enforced by this objective...
Security Target
Page 52
... user that caused the event. Dependencies: FAU_GEN.1 Audit data generation FIA_UID.1 Timing of identification FAU_GEN.2.1 For audit events resulting from unauthorised deletion. FAU_SAR.1 Audit review Hierarchical to : No other components. All rights reserved. FAU_STG.1.2 The TSF shall be taken in the audit trail. FAU_GEN.2 User identity association Hierarchical to ...: FAU_STG.1 Protected audit trail storage FAU_STG.4.1 The TSF shall [selection: overwrite the oldest stored audit records] and [assignment: no other components. Copyright (c) 2012 RICOH COMPANY, LTD.
... user that caused the event. Dependencies: FAU_GEN.1 Audit data generation FIA_UID.1 Timing of identification FAU_GEN.2.1 For audit events resulting from unauthorised deletion. FAU_SAR.1 Audit review Hierarchical to : No other components. All rights reserved. FAU_STG.1.2 The TSF shall be taken in the audit trail. FAU_GEN.2 User identity association Hierarchical to ...: FAU_STG.1 Protected audit trail storage FAU_STG.4.1 The TSF shall [selection: overwrite the oldest stored audit records] and [assignment: no other components. Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 53
... AES Cryptographic Key Size 256 bits Cryptographic Operation - All rights reserved. Decryption when reading the data Copyright (c) 2012 RICOH COMPANY, LTD. Page 52 of user data with security attributes, or FCS_CKM.1 Cryptographic key generation] FCS_CKM.4 Cryptographic key...assignment: cryptographic key sizes in Table 13] that meet the following : [assignment: standards in Table 14]. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all users read -access. 6.1.2 Class FCS: Cryptographic support FCS_CKM.1 Cryptographic key generation Hierarchical to: No...
... AES Cryptographic Key Size 256 bits Cryptographic Operation - All rights reserved. Decryption when reading the data Copyright (c) 2012 RICOH COMPANY, LTD. Page 52 of user data with security attributes, or FCS_CKM.1 Cryptographic key generation] FCS_CKM.4 Cryptographic key...assignment: cryptographic key sizes in Table 13] that meet the following : [assignment: standards in Table 14]. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all users read -access. 6.1.2 Class FCS: Cryptographic support FCS_CKM.1 Cryptographic key generation Hierarchical to: No...
Security Target
Page 81
... newest audit log. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in the audit log files to audit (audit log review). FPT_STM.1 The date (year/month/day) and time (hour/minute/second) the TOE records for the audit log are described for each security...login operations (except login operations from RC Gate) Success and failure of login operations from the system clock of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. The security functions are derived from RC Gate communication interface Starting and releasing Lockout Table 30 Record of the TOE. All...
... newest audit log. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in the audit log files to audit (audit log review). FPT_STM.1 The date (year/month/day) and time (hour/minute/second) the TOE records for the audit log are described for each security...login operations (except login operations from RC Gate) Success and failure of login operations from the system clock of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. The security functions are derived from RC Gate communication interface Starting and releasing Lockout Table 30 Record of the TOE. All...