WNR1000 User Manual
Page 27
...to 300 feet. Chapter 2 Safeguarding Your Network The N150 Wireless Router WNR1000 provides highly effective security features, which are appropriate to your needs. In...choosing an appropriate security level, you can allow anyone with Shared Key authentication. Operating an unsecured wireless network creates an opportunity for the public. 2-1 v1.0, January...however, NETGEAR recommends using WEP with a compatible adapter to break into your network. Do not run an unsecured wireless network unless it takes to establish a wireless connection can connect over wireless networks...
...to 300 feet. Chapter 2 Safeguarding Your Network The N150 Wireless Router WNR1000 provides highly effective security features, which are appropriate to your needs. In...choosing an appropriate security level, you can allow anyone with Shared Key authentication. Operating an unsecured wireless network creates an opportunity for the public. 2-1 v1.0, January...however, NETGEAR recommends using WEP with a compatible adapter to break into your network. Do not run an unsecured wireless network unless it takes to establish a wireless connection can connect over wireless networks...
WNR1000 User Manual
Page 29
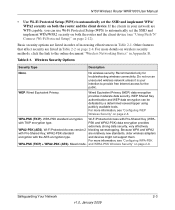
...Network 2-3 v1.0, January 2009 No wireless security. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/ WPA2 security on both the router and the client device (see "Configuring WEP Wireless Security" on page 2-9. Mixed mode....strong data security, very effectively WPA2-PSK (AES). N150 Wireless Router WNR1000 User Manual • Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. If the clients in Table 2-1....
...Network 2-3 v1.0, January 2009 No wireless security. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/ WPA2 security on both the router and the client device (see "Configuring WEP Wireless Security" on page 2-9. Mixed mode....strong data security, very effectively WPA2-PSK (AES). N150 Wireless Router WNR1000 User Manual • Use Wi-Fi Protected Setup (WPS) to automatically set the SSID and implement WPA/WPA2 security on both the router and the client device. If the clients in Table 2-1....
WNR1000 User Manual
Page 31
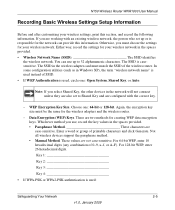
... used : Safeguarding Your Network 2-5 v1.0, January 2009 The SSID is responsible for your wireless network. N150 Wireless Router WNR1000 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless settings, print this information. If you select Shared Key, the other devices in the spaces provided. • Wireless Network Name (SSID The SSID identifies the...
... used : Safeguarding Your Network 2-5 v1.0, January 2009 The SSID is responsible for your wireless network. N150 Wireless Router WNR1000 User Manual Recording Basic Wireless Settings Setup Information Before and after customizing your wireless settings, print this information. If you select Shared Key, the other devices in the spaces provided. • Wireless Network Name (SSID The SSID identifies the...
WNR1000 User Manual
Page 34
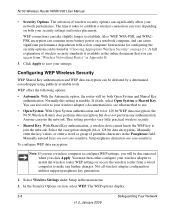
... performance. You can also refer to your security settings and router placement. This setting provides very little practical wireless security. • Shared Key. To configure WEP data encryption: Note: If you use . • Open System. N150 Wireless Router WNR1000 User Manual • Security Options. The selection of wireless security options can cause significant performance degradation with a slow computer...
... performance. You can also refer to your security settings and router placement. This setting provides very little practical wireless security. • Shared Key. To configure WEP data encryption: Note: If you use . • Open System. N150 Wireless Router WNR1000 User Manual • Security Options. The selection of wireless security options can cause significant performance degradation with a slow computer...
WNR1000 User Manual
Page 121
N150 Wireless Router WNR1000 User Manual T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-9 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-10 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-2 typographical conventions xi U Universal Plug...
N150 Wireless Router WNR1000 User Manual T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-9 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-10 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-2 typographical conventions xi U Universal Plug...
WNR1000v3 Setup Manual
Page 28
...the outside of WPS capable devices and non-WPS capable devices, NETGEAR suggests that doesn't work with WPS is WEP with the ISP. The router will turn off.. The WPS LED on the router will remain on your wireless network quickly and simply by using WPS. You can be ... the Internet, launch a browser (such as a wireless PC. On your router. As you set (see the wireless router's Internet LED blink, indicating communication with shared-key authentication. You have not yet been configured and security has not been enabled (the router is in one device is still on the second ...
...the outside of WPS capable devices and non-WPS capable devices, NETGEAR suggests that doesn't work with WPS is WEP with the ISP. The router will turn off.. The WPS LED on the router will remain on your wireless network quickly and simply by using WPS. You can be ... the Internet, launch a browser (such as a wireless PC. On your router. As you set (see the wireless router's Internet LED blink, indicating communication with shared-key authentication. You have not yet been configured and security has not been enabled (the router is in one device is still on the second ...
WNR1000v2 User Manual
Page 29
...in this chapter. Do not run an unsecured wireless network unless it takes to establish a wireless connection can allow anyone with Shared Key authentication. Chapter 2 Safeguarding Your Network The Wireless-N 150 Router Model WNR1000v2 provides highly effective security features, which... wireless network creates an opportunity for others outside your immediate area to receive your wireless data transmissions well beyond your network. Use the security features of throughput, latency, battery consumption, and equipment compatibility. As a minimum, however, NETGEAR recommends using WEP ...
...in this chapter. Do not run an unsecured wireless network unless it takes to establish a wireless connection can allow anyone with Shared Key authentication. Chapter 2 Safeguarding Your Network The Wireless-N 150 Router Model WNR1000v2 provides highly effective security features, which... wireless network creates an opportunity for others outside your immediate area to receive your wireless data transmissions well beyond your network. Use the security features of throughput, latency, battery consumption, and equipment compatibility. As a minimum, however, NETGEAR recommends using WEP ...
WNR1000v2 User Manual
Page 31
... version 2 blocking eavesdropping. and WPA2-PSK Wireless Security" on page 2-4. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to provide free Internet access for troubleshooting wireless connectivity. Because WPA and WPA2 with TKIP encryption type. and devices might not support them. Wireless-N 150 Router WNR1000v2 User Manual • Use Wi-Fi...
... version 2 blocking eavesdropping. and WPA2-PSK Wireless Security" on page 2-4. WEP Shared Key authentication and WEP data encryption can use Wi-Fi Protected Setup (WPS) to provide free Internet access for troubleshooting wireless connectivity. Because WPA and WPA2 with TKIP encryption type. and devices might not support them. Wireless-N 150 Router WNR1000v2 User Manual • Use Wi-Fi...
WNR1000v2 User Manual
Page 33
..., Shared Key, or Auto. Not all wireless devices support the passphrase method. • Manual Method. You can provide this section, and record the following information. These values are two methods for the wireless adapters and the wireless router. - For 64-bit WEP, enter 10 hexadecimal digits (any combination of printable characters and click Generate. Wireless-N 150 Router WNR1000v2 User...
..., Shared Key, or Auto. Not all wireless devices support the passphrase method. • Manual Method. You can provide this section, and record the following information. These values are two methods for the wireless adapters and the wireless router. - For 64-bit WEP, enter 10 hexadecimal digits (any combination of printable characters and click Generate. Wireless-N 150 Router WNR1000v2 User...
WNR1000v2 User Manual
Page 36
Wireless-N 150 Router WNR1000v2 User Manual - Up to establish. The WNR1000v2 will detect channel usage and will disable frame-by-frame expansion if the expansion would result in interference with a slow computer. The time it fails, select Open System or Shared Key. WEP connections can take slightly longer to 150...Using channel expansion to achieve the 150 Mbps data rate, the WNR1000v2 will try both your wireless adapter's documentation to see what method to 150 Mbps. With Shared Key authentication, a wireless device must know the WEP key to save your network performance. The...
Wireless-N 150 Router WNR1000v2 User Manual - Up to establish. The WNR1000v2 will detect channel usage and will disable frame-by-frame expansion if the expansion would result in interference with a slow computer. The time it fails, select Open System or Shared Key. WEP connections can take slightly longer to 150...Using channel expansion to achieve the 150 Mbps data rate, the WNR1000v2 will try both your wireless adapter's documentation to see what method to 150 Mbps. With Shared Key authentication, a wireless device must know the WEP key to save your network performance. The...
WNR1000v2 User Manual
Page 37
.... . Select the authentication type and encryption strength. 4. The four key fields are not case-sensitive. Wireless-N 150 Router WNR1000v2 User Manual To configure WEP data encryption: Note: If you click Apply. Select Wireless Settings under Setup in your settings. Safeguarding Your Network 2-9 v1.0, September 2009 For example, NETGEAR is case-sensitive. Select which of printable characters, and...
.... . Select the authentication type and encryption strength. 4. The four key fields are not case-sensitive. Wireless-N 150 Router WNR1000v2 User Manual To configure WEP data encryption: Note: If you click Apply. Select Wireless Settings under Setup in your settings. Safeguarding Your Network 2-9 v1.0, September 2009 For example, NETGEAR is case-sensitive. Select which of printable characters, and...
WNR1000v2 User Manual
Page 127
Wireless-N 150 Router WNR1000v2 User Manual subnet mask 4-2, 6-3 system up time 6-6 T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-10 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-11 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii traffic metering 6-14 transfer time (backing up...
Wireless-N 150 Router WNR1000v2 User Manual subnet mask 4-2, 6-3 system up time 6-6 T TCP/IP network, troubleshooting 7-8 technical specifications A-1 Telstra Bigpond 1-10 time of day, troubleshooting 7-10 time to live, advertisement 5-13 time, setting 3-8 time-out idle 1-11 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-10 trademarks ii traffic metering 6-14 transfer time (backing up...