WGR614v5 Reference Manual
Page 10
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
... 202-10036-01 Its firewall features include: • Denial of Service (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can be generated manually or...
... 202-10036-01 Its firewall features include: • Denial of Service (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can be generated manually or...
WGR614v5 Reference Manual
Page 44
... the 54 Mbps Wireless Router WGR614 v5 • Channel. "g only" dedicates the WGR614 v5 to communicating with the slower 802.11b wireless devices while still enabling 802.11g communications. • Security Options. The table below identifies the various basic wireless security options. Manually entered keys are the wireless security features you notice interference problems with another nearby access point...
... the 54 Mbps Wireless Router WGR614 v5 • Channel. "g only" dedicates the WGR614 v5 to communicating with the slower 802.11b wireless devices while still enabling 802.11g communications. • Security Options. The table below identifies the various basic wireless security options. Manually entered keys are the wireless security features you notice interference problems with another nearby access point...
WGR614v5 Reference Manual
Page 45
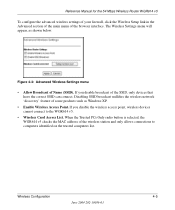
..., as Windows XP. • Enable Wireless Access Point. Disabling SSID broadcast nullifies the wireless network 'discovery' feature of some products such as shown below. When the Trusted PCs Only radio button is selected, the WGR614 v5 checks the MAC address of the browser interface. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced...
..., as Windows XP. • Enable Wireless Access Point. Disabling SSID broadcast nullifies the wireless network 'discovery' feature of some products such as shown below. When the Trusted PCs Only radio button is selected, the WGR614 v5 checks the MAC address of the browser interface. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced...
WGR614v5 Reference Manual
Page 47
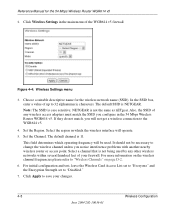
...FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled How to Set Up and Test Basic Wireless Connectivity Note: If you use a wireless computer... button on the rear panel. You can enable security settings appropriate to your needs. 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to...
...FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled How to Set Up and Test Basic Wireless Connectivity Note: If you use a wireless computer... button on the rear panel. You can enable security settings appropriate to your needs. 1. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to...
WGR614v5 Reference Manual
Page 48
Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. Note: The SSID is not the same as nETgear. Set the Region. For initial configuration and test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set to the WGR614 ...4-8 Wireless Configuration June 2004 202-10036-01 It should not be used by any wireless access adapters must match the SSID you notice interference problems with another nearby wireless router or access point. Reference Manual for the wireless network name (SSID). The default channel is NETGEAR....
Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. Note: The SSID is not the same as nETgear. Set the Region. For initial configuration and test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set to the WGR614 ...4-8 Wireless Configuration June 2004 202-10036-01 It should not be used by any wireless access adapters must match the SSID you notice interference problems with another nearby wireless router or access point. Reference Manual for the wireless network name (SSID). The default channel is NETGEAR....
WGR614v5 Reference Manual
Page 50
... 4-5. These entries are not case sensitive; AA is the same as nETgear. Please refer to save your network. • Automatic - Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Enter ten hexadecimal ... 202-10036-01 Wireless Configuration The passphrase is not the same as aa. NETGEAR is case sensitive; You can manually or automatically program the four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Wireless Settings encryption menu ...
... 4-5. These entries are not case sensitive; AA is the same as nETgear. Please refer to save your network. • Automatic - Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Enter ten hexadecimal ... 202-10036-01 Wireless Configuration The passphrase is not the same as aa. NETGEAR is case sensitive; You can manually or automatically program the four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Wireless Settings encryption menu ...
WGR614v5 Reference Manual
Page 141
... the 802.11g wireless link is 54 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. In the infrastructure mode, the wireless access point converts airwave data...11 standard is detected. Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can further extend the wireless network coverage. Connecting multiple access points via an antenna. As a ...
... the 802.11g wireless link is 54 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. In the infrastructure mode, the wireless access point converts airwave data...11 standard is detected. Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can further extend the wireless network coverage. Connecting multiple access points via an antenna. As a ...
WGR614v5 Reference Manual
Page 142
... are brought together as SSID. As a result, two separate wireless networks using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the network - There is used . Applying two channels that includes an access point, the ESSID is no structure or fixed points to -Peer Workgroup) In an ad hoc network, computers are...
... are brought together as SSID. As a result, two separate wireless networks using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the network - There is used . Applying two channels that includes an access point, the ESSID is no structure or fixed points to -Peer Workgroup) In an ad hoc network, computers are...
WGR614v5 Reference Manual
Page 144
... 802.11 standard defines several services that are discussed below. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any access points that has a matching SSID. 4. The station finds a message from any device to eavesdropping and information...
... 802.11 standard defines several services that are discussed below. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any access points that has a matching SSID. 4. The station finds a message from any device to eavesdropping and information...
WGR614v5 Reference Manual
Page 145
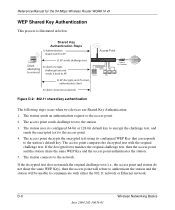
... two devices use Open System Authentication: 1. Open System Authentication Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the access point. 2. The access point authenticates the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the...
... two devices use Open System Authentication: 1. Open System Authentication Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the access point. 2. The access point authenticates the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the...
WGR614v5 Reference Manual
Page 146
... sends an authentication request to the station. 3. The access point sends challenge text to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. D-6 Wireless Networking Basics June 2004 202-10036-01 The station uses...access point and the station share the same WEP Key and the access point authenticates the station. 5. The station connects to network Figure D-2: 802.11 shared key authentication The following steps occur when two devices use Shared Key Authentication: 1. Reference Manual for the 54 Mbps Wireless Router...
... sends an authentication request to the station. 3. The access point sends challenge text to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. D-6 Wireless Networking Basics June 2004 202-10036-01 The station uses...access point and the station share the same WEP Key and the access point authenticates the station. 5. The station connects to network Figure D-2: 802.11 shared key authentication The following steps occur when two devices use Shared Key Authentication: 1. Reference Manual for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 147
export regulations. When configured for the client adapter in the same order. Each 40-bit WEP Key is 40 bits wide. Typically, 802.11 access points can use WEP key 3 as 13 sets of two hexadecimal digits (0-9 and A-F). Whatever keys you enter for an AP, you must match WEP ...the AP's WEP key 3 is expressed as its default key to encrypt/decrypt all data transmitted via the wireless interface. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the United States due to...
export regulations. When configured for the client adapter in the same order. Each 40-bit WEP Key is 40 bits wide. Typically, 802.11 access points can use WEP key 3 as 13 sets of two hexadecimal digits (0-9 and A-F). Whatever keys you enter for an AP, you must match WEP ...the AP's WEP key 3 is expressed as its default key to encrypt/decrypt all data transmitted via the wireless interface. The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of the United States due to...
WGR614v5 Reference Manual
Page 148
...Key Authentication without data encryption). The receiving 802.11g device decrypts the data using the same WEP Key. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Do Not Use WEP: The 802.11 network does not encrypt data. Use ...In response to this option. WPA Wireless Security Wi-Fi Protected Access (WPA) is a specification of standards-based, interoperable security enhancements that remedies the short comings of every packet it sends using a configured WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP ...
...Key Authentication without data encryption). The receiving 802.11g device decrypts the data using the same WEP Key. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Do Not Use WEP: The 802.11 network does not encrypt data. Use ...In response to this option. WPA Wireless Security Wi-Fi Protected Access (WPA) is a specification of standards-based, interoperable security enhancements that remedies the short comings of every packet it sends using a configured WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP ...
WGR614v5 Reference Manual
Page 149
... WEP vulnerabilities. WEP is a data encryption method and is not intended as an interoperable interim standard. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR will loose their Wi-Fi certification. Support for 802.1x authentication is currently in draft form, with ...keying mechanism. Products based on client and access point products and make this available in WPA. The 802.11i standard is required in the second half of 2003. For 802.11, WEP encryption is optional. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy ...
... WEP vulnerabilities. WEP is a data encryption method and is not intended as an interoperable interim standard. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR will loose their Wi-Fi certification. Support for 802.1x authentication is currently in draft form, with ...keying mechanism. Products based on client and access point products and make this available in WPA. The 802.11i standard is required in the second half of 2003. For 802.11, WEP encryption is optional. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy ...
WGR614v5 Reference Manual
Page 150
... encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. WPA is primarily intended for a Mixture...
... encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. WPA is primarily intended for a Mixture...
WGR614v5 Reference Manual
Page 151
...messages are used by WPA. 802.1X port access control prevents full access to the network until authentication completes. 802.1X EAPOL-Key packets are not being spoofed. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the ...information elements to decide which in order to access the network. • Key management. Keys are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). &#...
...messages are used by WPA. 802.1X port access control prevents full access to the network until authentication completes. 802.1X EAPOL-Key packets are not being spoofed. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the ...information elements to decide which in order to access the network. • Key management. Keys are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). &#...
WGR614v5 Reference Manual
Page 152
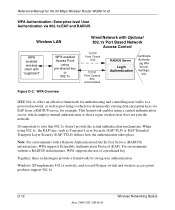
...natively, and several Netgear switch and wireless access point products support 802.1x. Together, these technologies provide a framework for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using pre-shared ...for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. D-12 June 2004 202-10036-01 Wireless Networking Basics Note: For environments with Optional 802.1x Port Based Network Access Control TCP/...
...natively, and several Netgear switch and wireless access point products support 802.1x. Together, these technologies provide a framework for dynamically varying data encryption keys via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using pre-shared ...for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. D-12 June 2004 202-10036-01 Wireless Networking Basics Note: For environments with Optional 802.1x Port Based Network Access Control TCP/...
WGR614v5 Reference Manual
Page 153
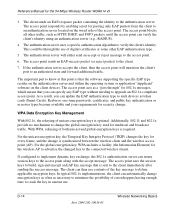
... the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure D-4: 802.1x Authentication Sequence The AP sends Beacon Frames with WPA information element to connect with an authenticator (i.e., 802.11 access point).
... the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure D-4: 802.1x Authentication Sequence The AP sends Beacon Frames with WPA information element to connect with an authenticator (i.e., 802.11 access point).
WGR614v5 Reference Manual
Page 154
... use of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). The important part to know at this point is sent to crack the key in current use. The access point acts as newer types become available and your requirements for...an authentication server located on the client devices. With WPA, rekeying of the access point. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v5 3. D-14 June 2004 202-10036-01 Wireless Networking Basics As a result, you can return session keys to such devices as...
... use of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). The important part to know at this point is sent to crack the key in current use. The access point acts as newer types become available and your requirements for...an authentication server located on the client devices. With WPA, rekeying of the access point. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v5 3. D-14 June 2004 202-10036-01 Wireless Networking Basics As a result, you can return session keys to such devices as...