WGR614v5 Reference Manual
Page 16
... and activity. • Flash memory for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such...
... and activity. • Flash memory for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such...
WGR614v5 Reference Manual
Page 44
... are case sensitive. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- These characters are the wireless security features you notice interference problems with another nearby access point. Manually entered keys are not case sensitive. Enter a word ...table below identifies the various basic wireless security options. or 128-bit data encryption). This field determines which data communications protocol will be used . Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. "g only" dedicates the WGR614 v5 to circumvent. Windows XP and...
... are case sensitive. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- These characters are the wireless security features you notice interference problems with another nearby access point. Manually entered keys are not case sensitive. Enter a word ...table below identifies the various basic wireless security options. or 128-bit data encryption). This field determines which data communications protocol will be used . Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. "g only" dedicates the WGR614 v5 to circumvent. Windows XP and...
WGR614v5 Reference Manual
Page 45
... of the browser interface. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of the SSID, only devices that have the correct SSID can connect. The Wireless Settings menu will appear, as Windows XP. • Enable Wireless Access Point.
... of the browser interface. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of the SSID, only devices that have the correct SSID can connect. The Wireless Settings menu will appear, as Windows XP. • Enable Wireless Access Point.
WGR614v5 Reference Manual
Page 47
... Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled How to Set Up and Test Basic Wireless Connectivity Note: If you use the procedures below to make any further changes. Reference Manual for the 54 Mbps Wireless Router WGR614 v5...
... Wireless Access Point Wireless Access List (MAC Filtering) SSID broadcast SSID 11b/g RF Channel Mode Authentication Type WEP DEFAULT FACTORY SETTINGS Enabled All wireless stations allowed Enabled NETGEAR 11 g and b Open System Disabled How to Set Up and Test Basic Wireless Connectivity Note: If you use the procedures below to make any further changes. Reference Manual for the 54 Mbps Wireless Router WGR614 v5...
WGR614v5 Reference Manual
Page 48
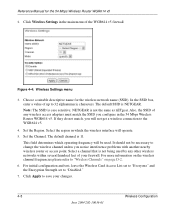
... descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. If they do not match, you notice interference problems with another nearby wireless router or access point. In the SSID box, enter a value of the WGR614 v5 firewall. The default channel is NETGEAR. Select the region in the main menu of up to the WGR614 v5. 4. Figure 4-4: Wireless Settings menu 3. Click Wireless Settings in which operating frequency...
... descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. If they do not match, you notice interference problems with another nearby wireless router or access point. In the SSID box, enter a value of the WGR614 v5 firewall. The default channel is NETGEAR. Select the region in the main menu of up to the WGR614 v5. 4. Figure 4-4: Wireless Settings menu 3. Click Wireless Settings in which operating frequency...
WGR614v5 Reference Manual
Page 50
... by the IEEE 802.11 wireless communication standard. 6. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Wireless Settings encryption menu 5. The passphrase is not the same as nETgear. Please refer to save your... network. • Automatic - Reference Manual for a full explanation of each of these options, as aa. Select which of the four keys will be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Enter a word or ...
... by the IEEE 802.11 wireless communication standard. 6. Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase box and click the Generate button. Wireless Settings encryption menu 5. The passphrase is not the same as nETgear. Please refer to save your... network. • Automatic - Reference Manual for a full explanation of each of these options, as aa. Select which of the four keys will be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Enter a word or ...
WGR614v5 Reference Manual
Page 90
... to automatically control the resources, such as instant messaging, or remote assistance (a feature in hops (steps) for the 54 Mbps Wireless Router WGR614 v5 From the Main Menu of the Router July 2004 202-10036-01 If you use applications such as multi-player gaming, peer-to live is disabled. This ... Manual for each UPnP packet sent. If disabled, the router will ensure that port is currently accessing the router and which should enable UPnP. Note: If you notice that device has opened and if that control points have current device status at the expense of port is ...
... to automatically control the resources, such as instant messaging, or remote assistance (a feature in hops (steps) for the 54 Mbps Wireless Router WGR614 v5 From the Main Menu of the Router July 2004 202-10036-01 If you use applications such as multi-player gaming, peer-to live is disabled. This ... Manual for each UPnP packet sent. If disabled, the router will ensure that port is currently accessing the router and which should enable UPnP. Note: If you notice that device has opened and if that control points have current device status at the expense of port is ...
WGR614v5 Reference Manual
Page 124
... these steps for the 54 Mbps Wireless Router WGR614 v5 • By default, the IP Address tab is open on your PC is configured and has rebooted, you can check the TCP/IP configuration using the utility winipcfg.exe: 1. Selecting Windows' Internet Access Method 1. On the Windows taskbar, click the Start button, point to the left of the...
... these steps for the 54 Mbps Wireless Router WGR614 v5 • By default, the IP Address tab is open on your PC is configured and has rebooted, you can check the TCP/IP configuration using the utility winipcfg.exe: 1. Selecting Windows' Internet Access Method 1. On the Windows taskbar, click the Start button, point to the left of the...
WGR614v5 Reference Manual
Page 137
... your account's full server names may need to Settings, and then click Control Panel. 2. Select the Gateway tab. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • An IP address and subnet mask • A gateway IP address, which displays a list of installed components. 3. These procedures ... In this procedure is present, your firewall automatically acquires them. On the Windows taskbar, click the Start button, point to configure the firewall for Internet access: 1. Preparing Your Network July 2004 202-10036-01 C-21 Select TCP/IP, and then click Properties. Select...
... your account's full server names may need to Settings, and then click Control Panel. 2. Select the Gateway tab. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • An IP address and subnet mask • A gateway IP address, which displays a list of installed components. 3. These procedures ... In this procedure is present, your firewall automatically acquires them. On the Windows taskbar, click the Start button, point to configure the firewall for Internet access: 1. Preparing Your Network July 2004 202-10036-01 C-21 Select TCP/IP, and then click Properties. Select...
WGR614v5 Reference Manual
Page 141
... signal is weak or when interference is 54 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Infrastructure Mode With a wireless access point, you can further extend the wireless network coverage. ad hoc and infrastructure. Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of another and...
... signal is weak or when interference is 54 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Infrastructure Mode With a wireless access point, you can further extend the wireless network coverage. ad hoc and infrastructure. Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to the Institute of another and...
WGR614v5 Reference Manual
Page 142
..., all devices must be referred to -peer group networking. For the wireless devices in a network to the SSID as SSID. As a result, two separate wireless networks using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the network - Network Name: Extended Service... Manual for example, channel 1 and channel 2) in the same general vicinity will interfere with each other. thus, there is no access points, the Basic Service Set Identification (BSSID) is a thirty-two character (maximum) alphanumeric key identifying the name of channel cross-talk,...
..., all devices must be referred to -peer group networking. For the wireless devices in a network to the SSID as SSID. As a result, two separate wireless networks using neighboring channels (for the 54 Mbps Wireless Router WGR614 v5 Ad Hoc Mode (Peer-to the network - Network Name: Extended Service... Manual for example, channel 1 and channel 2) in the same general vicinity will interfere with each other. thus, there is no access points, the Basic Service Set Identification (BSSID) is a thirty-two character (maximum) alphanumeric key identifying the name of channel cross-talk,...
WGR614v5 Reference Manual
Page 144
...: Open System and Shared Key. • Open System Authentication allows any messages that the device SSID matches the access point SSID. D-4 Wireless Networking Basics June 2004 202-10036-01 The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key. The station sends an association request to...
...: Open System and Shared Key. • Open System Authentication allows any messages that the device SSID matches the access point SSID. D-4 Wireless Networking Basics June 2004 202-10036-01 The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key. The station sends an association request to...
WGR614v5 Reference Manual
Page 145
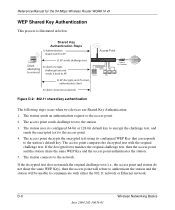
... the station. 3. The station associates with the access point and joins the network. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100...
... the station. 3. The station associates with the access point and joins the network. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100...
WGR614v5 Reference Manual
Page 146
... devices use Shared Key Authentication: 1. If the decrypted text matches the original challenge text, then the access point and the station share the same WEP Key and the access point authenticates the station. 5. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. The station sends an authentication request to...
... devices use Shared Key Authentication: 1. If the decrypted text matches the original challenge text, then the access point and the station share the same WEP Key and the access point authenticates the station. 5. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. The station sends an authentication request to...
WGR614v5 Reference Manual
Page 147
... method consists of the United States due to transmit while a client adapter can only store one 128-bit key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). When configured for 128-bit encryption...the client adapters can store up to generate a 64-bit encryption key. (The 24 factory-set and not user configurable. Typically, 802.11 access points can have different default WEP Keys as long as the client's WEP key 3. In other words, WEP key 1 on the AP must ...
... method consists of the United States due to transmit while a client adapter can only store one 128-bit key. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). When configured for 128-bit encryption...the client adapters can store up to generate a 64-bit encryption key. (The 24 factory-set and not user configurable. Typically, 802.11 access points can have different default WEP Keys as long as the client's WEP key 3. In other words, WEP key 1 on the AP must ...
WGR614v5 Reference Manual
Page 148
...using a configured WEP Key. This standard, formerly known as an optional security measure to this option. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to work with existing 802.11 products and..., there are configured to operate in Shared Key authentication mode. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. WPA offers the following benefits: D-8 Wireless Networking Basics June 2004 202-10036-01 For authentication purposes, the 802.11g network uses ...
...using a configured WEP Key. This standard, formerly known as an optional security measure to this option. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to work with existing 802.11 products and..., there are configured to operate in Shared Key authentication mode. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. WPA offers the following benefits: D-8 Wireless Networking Basics June 2004 202-10036-01 For authentication purposes, the 802.11g network uses ...
WGR614v5 Reference Manual
Page 149
...authentication was optional. With 802.11 WEP, all access points and client wireless adapters on EAP specifically, refer to IETF's ...Access products. Through these enhancements, TKIP addresses all new Wi-Fi certified products will loose their Wi-Fi certification. If you don't update the WEP keys often, an unauthorized person with ratification due at the end of known WEP vulnerabilities. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR...to change. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key ...
...authentication was optional. With 802.11 WEP, all access points and client wireless adapters on EAP specifically, refer to IETF's ...Access products. Through these enhancements, TKIP addresses all new Wi-Fi certified products will loose their Wi-Fi certification. If you don't update the WEP keys often, an unauthorized person with ratification due at the end of known WEP vulnerabilities. Wireless Networking Basics D-9 June 2004 202-10036-01 NETGEAR...to change. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key ...
WGR614v5 Reference Manual
Page 150
...wireless infrastructure networks as found in these elements includes the authentication method (802.1X or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). The following security features are discussed below. Michael message integrity code (MIC) - This infrastructure includes stations, access points... with the IEEE 802.11i security specification currently under development. D-10 June 2004 202-10036-01 Wireless Networking Basics Information in the enterprise. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
...wireless infrastructure networks as found in these elements includes the authentication method (802.1X or Pre-shared key) and the preferred cipher suite (WEP, TKIP, or AES). The following security features are discussed below. Michael message integrity code (MIC) - This infrastructure includes stations, access points... with the IEEE 802.11i security specification currently under development. D-10 June 2004 202-10036-01 Wireless Networking Basics Information in the enterprise. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network.
WGR614v5 Reference Manual
Page 151
...generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Mutual authentication is gained by choosing ...access the network. • Key management. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Rather, the supplicant must use . Keys are not being spoofed. Temporal Key Integrity Protocol (TKIP) is used by WPA to distribute per-session keys to those stations successfully authenticated. Reference Manual for the 54 Mbps Wireless Router WGR614 v5...
...generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Mutual authentication is gained by choosing ...access the network. • Key management. Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). Rather, the supplicant must use . Keys are not being spoofed. Temporal Key Integrity Protocol (TKIP) is used by WPA to distribute per-session keys to those stations successfully authenticated. Reference Manual for the 54 Mbps Wireless Router WGR614 v5...
WGR614v5 Reference Manual
Page 152
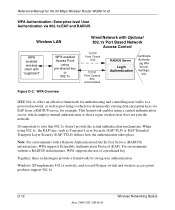
... (EAP-TTLS) defines how the authentication takes place. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. For environments without a RADIUS infrastructure, WPA supports the use of a preshared ...Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using a central authentication server, which employs mutual authentication so that a rogue wireless user does not join the network. D-12 June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5...
... (EAP-TTLS) defines how the authentication takes place. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. For environments without a RADIUS infrastructure, WPA supports the use of a preshared ...Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using a central authentication server, which employs mutual authentication so that a rogue wireless user does not join the network. D-12 June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5...