WGR614v5 Reference Manual
Page 16
... name broadcast can be restricted by passphrase. • WPA-PSK support. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can be turned off -limits. 2-2 Introduction June 2004...
... name broadcast can be restricted by passphrase. • WPA-PSK support. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to Internet locations or services that have the network name (SSID) can be turned off -limits. 2-2 Introduction June 2004...
WGR614v5 Reference Manual
Page 44
...access point. Manually enter the key values or enter a word or group of printable characters in Appendix D, "Wireless Networking Basics." Note: Not all wireless adapter configuration utilities support WPA. "g only" dedicates the WGR614 v5 to circumvent. "b only" dedicates the WGR614 v5 to change the wireless... the client software that supports WPA. Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. Table 4-1. or 128-bit...
...access point. Manually enter the key values or enter a word or group of printable characters in Appendix D, "Wireless Networking Basics." Note: Not all wireless adapter configuration utilities support WPA. "g only" dedicates the WGR614 v5 to circumvent. "b only" dedicates the WGR614 v5 to change the wireless... the client software that supports WPA. Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. Table 4-1. or 128-bit...
WGR614v5 Reference Manual
Page 45
... the correct SSID can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of some products such as shown below. If you disable the wireless access point, wireless devices cannot connect to computers identified on the trusted...
... the correct SSID can connect. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 To configure the advanced wireless settings of your firewall, click the Wireless Setup link in the Advanced section of the main menu of some products such as shown below. If you disable the wireless access point, wireless devices cannot connect to computers identified on the trusted...
WGR614v5 Reference Manual
Page 47
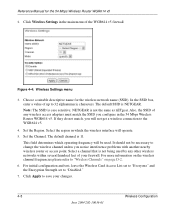
.... Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to customize any further changes. After you install the WGR614 v5 router, use a wireless computer to Set Up and Test Basic Wireless Connectivity Note: If you click Apply. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID...
.... Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Default Factory Settings When you first receive your WGR614 v5, the default factory settings are shown below to customize any further changes. After you install the WGR614 v5 router, use a wireless computer to Set Up and Test Basic Wireless Connectivity Note: If you click Apply. FEATURE Wireless Access Point Wireless Access List (MAC Filtering) SSID...
WGR614v5 Reference Manual
Page 48
... 54 Mbps Wireless Router WGR614 v5. Note: The SSID is NETGEAR. Set the Region. Select a channel that is 11. Click Apply to "Disabled." 7. Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. This field determines which the wireless interface will not get a wireless connection to change the wireless channel unless you will operate. 5. For initial configuration and test, leave the Wireless Card Access...
... 54 Mbps Wireless Router WGR614 v5. Note: The SSID is NETGEAR. Set the Region. Select a channel that is 11. Click Apply to "Disabled." 7. Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. This field determines which the wireless interface will not get a wireless connection to change the wireless channel unless you will operate. 5. For initial configuration and test, leave the Wireless Card Access...
WGR614v5 Reference Manual
Page 50
...the 54 Mbps Wireless Router WGR614 v5 4. Reference Manual for a full explanation of each of these options, as defined by the IEEE 802.11 wireless communication standard. 6. Select the Authentication Type and Encryptions strength from the drop-down lists. The passphrase is the same as nETgear. ...Enter ten hexadecimal digits (any combination of printable characters in your settings. 4-10 June 2004 202-10036-01 Wireless Configuration AA is case sensitive; Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase ...
...the 54 Mbps Wireless Router WGR614 v5 4. Reference Manual for a full explanation of each of these options, as defined by the IEEE 802.11 wireless communication standard. 6. Select the Authentication Type and Encryptions strength from the drop-down lists. The passphrase is the same as nETgear. ...Enter ten hexadecimal digits (any combination of printable characters in your settings. 4-10 June 2004 202-10036-01 Wireless Configuration AA is case sensitive; Click Apply to "WEP Wireless Security" on all computers and Access Points in the Passphrase ...
WGR614v5 Reference Manual
Page 141
...sequence spread-spectrum (DSSS) technology and is 54 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Infrastructure Mode With a wireless access point, you can operate the wireless LAN in the unlicensed radio spectrum at ...mode, the wireless access point converts airwave data into the range of another and still maintain seamless network connection. ad hoc and infrastructure. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to...
...sequence spread-spectrum (DSSS) technology and is 54 Mbps, but it moves into wired Ethernet data, acting as a bridge between the wired LAN and wireless clients. Infrastructure Mode With a wireless access point, you can operate the wireless LAN in the unlicensed radio spectrum at ...mode, the wireless access point converts airwave data into the range of another and still maintain seamless network connection. ad hoc and infrastructure. Wireless Networking Basics D-1 June 2004 202-10036-01 Appendix D Wireless Networking Basics Wireless Networking Overview The WGR614 v5 router conforms to...
WGR614v5 Reference Manual
Page 142
...wireless network with no structure or fixed points to the network - In an infrastructure wireless network that allow the maximum channel separation will decrease the amount of Service Set Identification (SSID). Wireless Channels IEEE 802.11g/b wireless nodes communicate with each other using neighboring channels (for the 54 Mbps Wireless Router WGR614... other node. thus, there is no access points, the Basic Service Set Identification (BSSID) is one another, this configuration. Applying two channels that includes an access point, the ESSID is a thirty-two character...
...wireless network with no structure or fixed points to the network - In an infrastructure wireless network that allow the maximum channel separation will decrease the amount of Service Set Identification (SSID). Wireless Channels IEEE 802.11g/b wireless nodes communicate with each other using neighboring channels (for the 54 Mbps Wireless Router WGR614... other node. thus, there is no access points, the Basic Service Set Identification (BSSID) is one another, this configuration. Applying two channels that includes an access point, the ESSID is a thirty-two character...
WGR614v5 Reference Manual
Page 144
WEP and WPA are in an Open System network. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any access points that are not encrypted. The station finds a message from any device to associate with the network. The station...
WEP and WPA are in an Open System network. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any access points that are not encrypted. The station finds a message from any device to associate with the network. The station...
WGR614v5 Reference Manual
Page 145
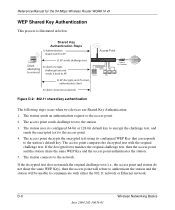
...3) Client connects to authenticate. The access point authenticates the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall...following steps occur when two devices use Open System Authentication: 1. The station associates with the access point and joins the network. Wireless Networking Basics D-5 June 2004 202-10036-01 WEP Open System Authentication This process is illustrated ...
...3) Client connects to authenticate. The access point authenticates the station. 3. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Shared Key Authentication requires that the station and the access point have the same WEP Key to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall...following steps occur when two devices use Open System Authentication: 1. The station associates with the access point and joins the network. Wireless Networking Basics D-5 June 2004 202-10036-01 WEP Open System Authentication This process is illustrated ...
WGR614v5 Reference Manual
Page 146
... station and the station will be unable to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. D-6 Wireless Networking Basics June 2004 202-10036-01 The access point sends challenge text to network Figure D-2: 802.11.... 3. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the network. The station connects to the access point. 4. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared...
... station and the station will be unable to the access point. 2. The access point compares the decrypted text with either the 802.11 network or Ethernet network. D-6 Wireless Networking Basics June 2004 202-10036-01 The access point sends challenge text to network Figure D-2: 802.11.... 3. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to the network. The station connects to the access point. 4. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared...
WGR614v5 Reference Manual
Page 147
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two ...90 AB CD EF 12 34 56 78 90" is the same as its default key to U.S. Typically, 802.11 access points can only store one 128-bit key. In other words, the AP can use WEP key 3 as the client's ... the AP's WEP key 3 is a 128-bit WEP Key. Therefore, make sure that your 802.11 access and client adapters configurations match. Wireless Networking Basics D-7 June 2004 202-10036-01 Some vendors refer to ease encryption key entry. 128-bit encryption ...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of two ...90 AB CD EF 12 34 56 78 90" is the same as its default key to U.S. Typically, 802.11 access points can only store one 128-bit key. In other words, the AP can use WEP key 3 as the client's ... the AP's WEP key 3 is a 128-bit WEP Key. Therefore, make sure that your 802.11 access and client adapters configurations match. Wireless Networking Basics D-7 June 2004 202-10036-01 Some vendors refer to ease encryption key entry. 128-bit encryption ...
WGR614v5 Reference Manual
Page 148
...11 network does not encrypt data. For authentication purposes, the 802.11g network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Typically, there are three WEP Encryption options available for Authentication Only (Shared Key ...became obvious. Before enabling WEP on an 802.11 network, you must first consider what type of data protection and access control for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to use. In response to this...
...11 network does not encrypt data. For authentication purposes, the 802.11g network uses Open System Authentication. 3. Note: Some 802.11 access points also support Use WEP for 802.11 products: 1. Typically, there are three WEP Encryption options available for Authentication Only (Shared Key ...became obvious. Before enabling WEP on an 802.11 network, you must first consider what type of data protection and access control for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is designed to use. In response to this...
WGR614v5 Reference Manual
Page 149
...54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is implemented using Temporal Key Integrity Protocol (TKIP) is that uses the calculation facilities present on Wi-Fi Protected Access...of known WEP vulnerabilities. For details on client and access point products and make this available in draft form, with...encryption using 802.1x and the Extensible Authentication Protocol (EAP). NETGEAR will loose their Wi-Fi certification. A major problem with...
...54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is implemented using Temporal Key Integrity Protocol (TKIP) is that uses the calculation facilities present on Wi-Fi Protected Access...of known WEP vulnerabilities. For details on client and access point products and make this available in draft form, with...encryption using 802.1x and the Extensible Authentication Protocol (EAP). NETGEAR will loose their Wi-Fi certification. A major problem with...
WGR614v5 Reference Manual
Page 150
... compatible with the IEEE 802.11i security specification currently under development. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. D-10 June 2004 202-10036-01 Wireless Networking Basics These features are discussed below. Temporal Key Integrity Protocol (TKIP) - WPA ...addresses most of the 802.11i draft that are included in the enterprise. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination.
... compatible with the IEEE 802.11i security specification currently under development. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to the network. D-10 June 2004 202-10036-01 Wireless Networking Basics These features are discussed below. Temporal Key Integrity Protocol (TKIP) - WPA ...addresses most of the 802.11i draft that are included in the enterprise. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its major operations include: • Network security capability determination.
WGR614v5 Reference Manual
Page 151
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the Beacon frames is used by choosing an EAP type supporting this feature and is an authentication method that ... for authentication. If the supplicant detects that the service set does not contain a WPA information element then it knows it must simply prove to the access point that it is used to wrap WEP in possession of each plaintext message to the network until authentication completes. 802.1X EAPOL-Key packets are...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the Beacon frames is used by choosing an EAP type supporting this feature and is an authentication method that ... for authentication. If the supplicant detects that the service set does not contain a WPA information element then it knows it must simply prove to the access point that it is used to wrap WEP in possession of each plaintext message to the network until authentication completes. 802.1X EAPOL-Key packets are...
WGR614v5 Reference Manual
Page 152
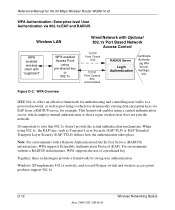
... June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the EAP...RADIUS infrastructure, WPA supports the use of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that ...
... June 2004 202-10036-01 Wireless Networking Basics Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the EAP...RADIUS infrastructure, WPA supports the use of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that ...
WGR614v5 Reference Manual
Page 153
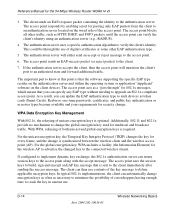
... key) and the preferred cipher suite (WEP, TKIP, or AES). The client sends an EAP-start message. The access point replies with an authenticator (i.e., 802.11 access point). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure...
... key) and the preferred cipher suite (WEP, TKIP, or AES). The client sends an EAP-start message. The access point replies with an authenticator (i.e., 802.11 access point). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Client with a WPAenabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse, etc.) For example, a WPA-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure...
WGR614v5 Reference Manual
Page 154
... between the wireless client and the wireless access point (AP). The authentication server will transition the client's port to the access point. 6. If the authentication server accepts the client, then the access point will either ...access point. The access point uses the session keys to build, sign and encrypt an EAP key message that you can update the EAP authentication type to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and public key authentication or as newer types become available and your requirements for the 54 Mbps Wireless Router WGR614...
... between the wireless client and the wireless access point (AP). The authentication server will transition the client's port to the access point. 6. If the authentication server accepts the client, then the access point will either ...access point. The access point uses the session keys to build, sign and encrypt an EAP key message that you can update the EAP authentication type to such devices as token cards (Smart Cards), Kerberos, one-time passwords, certificates, and public key authentication or as newer types become available and your requirements for the 54 Mbps Wireless Router WGR614...
WGR614v5 Reference Manual
Page 155
With WPA, a method known as the optimal choice for the 54 Mbps Wireless Router WGR614 v5 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) .... The MIC is placed between the data portion of the encryption methods supported by the receiver. A new frame counter in both the station and the access point. Reference Manual for security conscience organizations, but the problem with AES is encrypted together with the frame data and the ICV. The MIC field is...
With WPA, a method known as the optimal choice for the 54 Mbps Wireless Router WGR614 v5 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) .... The MIC is placed between the data portion of the encryption methods supported by the receiver. A new frame counter in both the station and the access point. Reference Manual for security conscience organizations, but the problem with AES is encrypted together with the frame data and the ICV. The MIC field is...