User Guide
Page 3
i Contents McAfee Internet Security 3 McAfee SecurityCenter...5 SecurityCenter features 6 Using SecurityCenter 7 Fixing or ignoring protection problems 16 Working with alerts 21 Viewing events...27 McAfee VirusScan ...29 VirusScan features 30 Scanning your computer 31 Working with scan results 35 Scan types ...38 Using additional protection 41 Setting up virus protection 45 McAfee Personal Firewall 61 Personal Firewall features 62 Starting Firewall ...63 Working with alerts 65 Managing informational alerts 67 Configuring Firewall protection 69...
i Contents McAfee Internet Security 3 McAfee SecurityCenter...5 SecurityCenter features 6 Using SecurityCenter 7 Fixing or ignoring protection problems 16 Working with alerts 21 Viewing events...27 McAfee VirusScan ...29 VirusScan features 30 Scanning your computer 31 Working with scan results 35 Scan types ...38 Using additional protection 41 Setting up virus protection 45 McAfee Personal Firewall 61 Personal Firewall features 62 Starting Firewall ...63 Working with alerts 65 Managing informational alerts 67 Configuring Firewall protection 69...
User Guide
Page 16
... subscription before downloading and installing. How? If you want to change this default behavior, you can either download or install the updates, or postpone the updates. For more information, see Check for updates (page 13). 1 Open the SecurityCenter Configuration pane. How? 1. For information about checking for updates manually, see Working with alerts (page 21). 1 Open the SecurityCenter Configuration pane. 14 McAfee Internet Security Configure automatic updates By default, SecurityCenter automatically checks for and installs updates every four...
... subscription before downloading and installing. How? If you want to change this default behavior, you can either download or install the updates, or postpone the updates. For more information, see Check for updates (page 13). 1 Open the SecurityCenter Configuration pane. How? 1. For information about checking for updates manually, see Working with alerts (page 21). 1 Open the SecurityCenter Configuration pane. 14 McAfee Internet Security Configure automatic updates By default, SecurityCenter automatically checks for and installs updates every four...
User Guide
Page 19
... not installed. Chapter 4 McAfee Internet Security 17 Fixing protection problems Most security problems can fix most protection problems automatically. The following table describes some problems may require you must install it automatically; help . A program is missing components. Reinstall the program from the McAfee Web site or CD. For example, if Firewall Protection is not installed, you to take when fixing protection problems manually: Problem Action A full scan of -date. Check your protection manually...
... not installed. Chapter 4 McAfee Internet Security 17 Fixing protection problems Most security problems can fix most protection problems automatically. The following table describes some problems may require you must install it automatically; help . A program is missing components. Reinstall the program from the McAfee Web site or CD. For example, if Firewall Protection is not installed, you to take when fixing protection problems manually: Problem Action A full scan of -date. Check your protection manually...
User Guide
Page 32
... interaction. Resource-aware scanning options Customize scanning options if you don't, your desktop, targeting threats from different points of tasks, such as manual scans. In these cases, VirusScan lets you decide what to do (rescan the next time you can be able to other potentially unwanted programs. Protection extends beyond the files and folders and on your computer remains protected. 30 McAfee Internet Security VirusScan features Comprehensive...
... interaction. Resource-aware scanning options Customize scanning options if you don't, your desktop, targeting threats from different points of tasks, such as manual scans. In these cases, VirusScan lets you decide what to do (rescan the next time you can be able to other potentially unwanted programs. Protection extends beyond the files and folders and on your computer remains protected. 30 McAfee Internet Security VirusScan features Comprehensive...
User Guide
Page 40
..., manual scans. Custom scan options include checking for threats in all files, in archive files, and in cookies in SecurityCenter offers the advantage of changing scanning options on your PC. To learn more, see Setting custom scan options (page 48) Manual Scan 38 McAfee Internet Security Scan types VirusScan provides a complete set of scanning options for virus protection, including real-time scanning (which constantly monitors your PC for threat activity), manual scanning from SecurityCenter, or customize when scheduled scans will occur. Custom Scan Custom Scan...
..., manual scans. Custom scan options include checking for threats in all files, in archive files, and in cookies in SecurityCenter offers the advantage of changing scanning options on your PC. To learn more, see Setting custom scan options (page 48) Manual Scan 38 McAfee Internet Security Scan types VirusScan provides a complete set of scanning options for virus protection, including real-time scanning (which constantly monitors your PC for threat activity), manual scanning from SecurityCenter, or customize when scheduled scans will occur. Custom Scan Custom Scan...
User Guide
Page 48
... the Computer & Files information area, click Configure. 4. 46 McAfee Internet Security Setting real-time scan options When you start real-time virus protection, VirusScan uses a default set real-time scan options to customize what VirusScan looks for during a scan, as well as the locations and file types it 's important for your real-time scanning options, and then click OK. Options include scanning for unknown new variants of memory used to temporarily hold computer information. To change the default options to suit your computer becomes...
... the Computer & Files information area, click Configure. 4. 46 McAfee Internet Security Setting real-time scan options When you start real-time virus protection, VirusScan uses a default set real-time scan options to customize what VirusScan looks for during a scan, as well as the locations and file types it 's important for your real-time scanning options, and then click OK. Options include scanning for unknown new variants of memory used to temporarily hold computer information. To change the default options to suit your computer becomes...
User Guide
Page 50
... occupies your needs. When you start a custom scan, VirusScan checks your Program Files folder. You must make decisions about what VirusScan looks for scans. For example, you can grant unauthorized access to suit your entire computer screen, VirusScan pauses a number of tasks, including automatic updates and custom scans. How? To change the default locations to your behavior. You can also set the custom scan location to specific folders and drives. 1 Open the Custom Scan pane. however, you can...
... occupies your needs. When you start a custom scan, VirusScan checks your Program Files folder. You must make decisions about what VirusScan looks for scans. For example, you can grant unauthorized access to suit your entire computer screen, VirusScan pauses a number of tasks, including automatic updates and custom scans. How? To change the default locations to your behavior. You can also set the custom scan location to specific folders and drives. 1 Open the Custom Scan pane. however, you can...
User Guide
Page 54
... stops suspect ActiveX programs (downloaded from sending and receiving unauthorized or personal information over the Internet. These important registry items and files include context menu handlers, appInit DLLs, and the Windows hosts file. For example, when SystemGuards detect changes that are three types of the programs that pose significant potential for standard and low-risk changes is immediately reported and logged. 52 McAfee Internet Security Using SystemGuards options SystemGuards monitor, log, report, and manage...
... stops suspect ActiveX programs (downloaded from sending and receiving unauthorized or personal information over the Internet. These important registry items and files include context menu handlers, appInit DLLs, and the Windows hosts file. For example, when SystemGuards detect changes that are three types of the programs that pose significant potential for standard and low-risk changes is immediately reported and logged. 52 McAfee Internet Security Using SystemGuards options SystemGuards monitor, log, report, and manage...
User Guide
Page 72
... Blocks all inbound Internet connections, except open ports, hiding your computer's presence on the Program Permissions pane. An inbound connection is Automatic with the option selected to Automatic, with outgoing-only access. By default, Firewall's security level is automatically allowed. Although green alerts are disabled by you. Generally, the more restrictive a security level (Stealth and Standard), the greater the number of allowed programs...
... Blocks all inbound Internet connections, except open ports, hiding your computer's presence on the Program Permissions pane. An inbound connection is Automatic with the option selected to Automatic, with outgoing-only access. By default, Firewall's security level is automatically allowed. Although green alerts are disabled by you. Generally, the more restrictive a security level (Stealth and Standard), the greater the number of allowed programs...
User Guide
Page 79
... and unauthorized scans. Chapter 16 McAfee Internet Security 77 Configure intrusion detection You can configure Firewall to ignore that specific problems on your computer. 4 Click OK. The standard Firewall setting includes automatic detection for one or more attacks or scans. 1 On the McAfee SecurityCenter pane, click Internet & Network, then click Configure. 2 On the Internet & Network Configuration pane, under Protection Status, click Advanced. 3 On the Ignored Problems pane, select one of Service attacks...
... and unauthorized scans. Chapter 16 McAfee Internet Security 77 Configure intrusion detection You can configure Firewall to ignore that specific problems on your computer. 4 Click OK. The standard Firewall setting includes automatic detection for one or more attacks or scans. 1 On the McAfee SecurityCenter pane, click Internet & Network, then click Configure. 2 On the Internet & Network Configuration pane, under Protection Status, click Advanced. 3 On the Ignored Problems pane, select one of Service attacks...
User Guide
Page 137
... Configure. 3. Chapter 26 McAfee Internet Security 135 Remove a Webmail account Remove a Webmail account if you no longer want to the information provided by your account is likely username. For example, if your Internet Service Provider (ISP). On the SecurityCenter Home pane, click E-mail & IM. 2. If you must specify when adding or editing Webmail accounts. Specify the user name for spam. Verify the password for example...
... Configure. 3. Chapter 26 McAfee Internet Security 135 Remove a Webmail account Remove a Webmail account if you no longer want to the information provided by your account is likely username. For example, if your Internet Service Provider (ISP). On the SecurityCenter Home pane, click E-mail & IM. 2. If you must specify when adding or editing Webmail accounts. Specify the user name for spam. Verify the password for example...
User Guide
Page 166
... users who know this password can reset it is a secure location that were previously stored in your passwords, you have trouble remembering your Password Vault are then deleted. The Password Vault is for example, what it ; On the Internet & Network Configuration pane, click Advanced under Password Vault. 2 Type your Password Vault. After you can add them when the passwords change your Password Vault password, you forget your Password Vault password at any time. Add a password If you can add, edit...
... users who know this password can reset it is a secure location that were previously stored in your passwords, you have trouble remembering your Password Vault are then deleted. The Password Vault is for example, what it ; On the Internet & Network Configuration pane, click Advanced under Password Vault. 2 Type your Password Vault. After you can add them when the passwords change your Password Vault password, you forget your Password Vault password at any time. Add a password If you can add, edit...
User Guide
Page 172
... can enable or disable local archiving at any time. 170 McAfee Internet Security Enabling and disabling local archive The first time you launch Backup and Restore, you decide whether to enable or disable local archive, depending on how you want to CD, DVD, USB drive, external hard drive, or network drive. 1 In SecurityCenter, on the Advanced Menu, click Configure. 2 On the Configure pane, click Computer & Files. 3 On the Computer & Files Configuration...
... can enable or disable local archiving at any time. 170 McAfee Internet Security Enabling and disabling local archive The first time you launch Backup and Restore, you decide whether to enable or disable local archive, depending on how you want to CD, DVD, USB drive, external hard drive, or network drive. 1 In SecurityCenter, on the Advanced Menu, click Configure. 2 On the Configure pane, click Computer & Files. 3 On the Computer & Files Configuration...
User Guide
Page 173
... content of watch locations. however, you can disable encryption or compression at any time. You can change the archive location at any time. By default, the following file types: .ost, and .pst. If you set up a top-level folders location, Backup and Restore archives the watch file types. Compressed files are enabled by people who do not know how to decrypt it . Chapter 35 McAfee Internet Security 171 Setting archive options Before you start...
... content of watch locations. however, you can disable encryption or compression at any time. You can change the archive location at any time. By default, the following file types: .ost, and .pst. If you set up a top-level folders location, Backup and Restore archives the watch file types. Compressed files are enabled by people who do not know how to decrypt it . Chapter 35 McAfee Internet Security 171 Setting archive options Before you start...
User Guide
Page 245
... address written as a starting point for launching and managing U3 USB programs. M MAC address Media Access Control address. Both devices must have the key. A computer network that their communication. A unique serial number assigned to encrypt messages that are transmitted between two parties without either party knowing that spans a relatively small area (for example, 192.168.1.100). MSN Microsoft Network. Glossary 243 IP address Internet Protocol address. An address used by two devices...
... address written as a starting point for launching and managing U3 USB programs. M MAC address Media Access Control address. Both devices must have the key. A computer network that their communication. A unique serial number assigned to encrypt messages that are transmitted between two parties without either party knowing that spans a relatively small area (for example, 192.168.1.100). MSN Microsoft Network. Glossary 243 IP address Internet Protocol address. An address used by two devices...
User Guide
Page 246
... legitimate companies. NIC Network Interface Card. O on -access scanning. phishing A method of fraudulently obtaining personal information, such as passwords, social security numbers, and credit card details, by multiple users. Network drives are grouped as a logical unit. node A single computer connected to find a threat, vulnerability, or other potentially unwanted code. It can access them. It allows you use to gain access to your personal passwords. 244 McAfee Internet Security N network A collection of...
... legitimate companies. NIC Network Interface Card. O on -access scanning. phishing A method of fraudulently obtaining personal information, such as passwords, social security numbers, and credit card details, by multiple users. Network drives are grouped as a logical unit. node A single computer connected to find a threat, vulnerability, or other potentially unwanted code. It can access them. It allows you use to gain access to your personal passwords. 244 McAfee Internet Security N network A collection of...
User Guide
Page 249
... receive email messages. This protocol is set up files for sending messages from one computer to another . SSID Service Set Identifier. A router is used on a network. server A computer or program that grant a user administrator-level access to route email. A token (secret key) that forwards data packets from one network to protect sensitive portions of RADIUS messages. The SSID is used to another on the Internet to a computer or computer network. router A network device...
... receive email messages. This protocol is set up files for sending messages from one computer to another . SSID Service Set Identifier. A router is used on a network. server A computer or program that grant a user administrator-level access to route email. A token (secret key) that forwards data packets from one network to protect sensitive portions of RADIUS messages. The SSID is used to another on the Internet to a computer or computer network. router A network device...
User Guide
Page 250
... the security of items that is used during a session and then discarded. URLs that detect unauthorized changes to be used to you must remove it does not email itself. You can also unknowingly download the Trojan horse from this list. T temporary file A file, created in the online backup repository is newer than the version of WEP, which is transferred over the SSL connection. SystemGuard McAfee alerts...
... the security of items that is used during a session and then discarded. URLs that detect unauthorized changes to be used to you must remove it does not email itself. You can also unknowingly download the Trojan horse from this list. T temporary file A file, created in the online backup repository is newer than the version of WEP, which is transferred over the SSL connection. SystemGuard McAfee alerts...
User Guide
Page 269
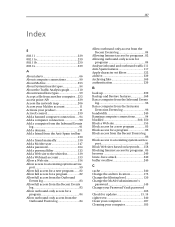
... About trusted lists types 59 Accept a file from another computer ...233 access point (AP 239 Access the network map 206 Access your McAfee account 11 Activate your product 11 ActiveX control 239 Add a banned computer connection .....94 Add a computer connection 90 Add a computer from the Inbound Events log 91 Add a domain 131 Add a friend from the Anti-Spam toolbar 130 Add a friend manually 130 Add a McAfee user 147 Add a password 164 Add a personal filter 123 Add a Web site...
... About trusted lists types 59 Accept a file from another computer ...233 access point (AP 239 Access the network map 206 Access your McAfee account 11 Activate your product 11 ActiveX control 239 Add a banned computer connection .....94 Add a computer connection 90 Add a computer from the Inbound Events log 91 Add a domain 131 Add a friend from the Anti-Spam toolbar 130 Add a friend manually 130 Add a McAfee user 147 Add a password 164 Add a personal filter 123 Add a Web site...
User Guide
Page 270
... automatic updates 14 Configure event log settings 104 Configure Firewall Protection Status settings 77 Configure intrusion detection 77 Configure ping request settings 76 Configure SystemGuards options ..........53 Configure UDP settings 76 Configuring alert options 24 Configuring Firewall protection 69 Configuring phishing protection..........139 Configuring Smart Recommendations for alerts 73 Configuring spam detection 119 Configuring system service ports ...........98 Configuring users 145 content-rating group 240 cookie 241 Copy a shared file 231 Copyright 254 Customer and...
... automatic updates 14 Configure event log settings 104 Configure Firewall Protection Status settings 77 Configure intrusion detection 77 Configure ping request settings 76 Configure SystemGuards options ..........53 Configure UDP settings 76 Configuring alert options 24 Configuring Firewall protection 69 Configuring phishing protection..........139 Configuring Smart Recommendations for alerts 73 Configuring spam detection 119 Configuring system service ports ...........98 Configuring users 145 content-rating group 240 cookie 241 Copy a shared file 231 Copyright 254 Customer and...