User Guide
Page 10
.... The basis of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router with RangeBooster, which is an identification name shared by the wireless devices belonging to each other computers on the wireless network, then the Ad-Hoc mode can roam... to extend the roaming range, and you can communicate with each other . Network Layout The Wireless-G Broadband Router with RangeBooster has been specifically designed for a wireless router or access point. An ad-hoc configuration is limited by a wired network or need to be set up:...
.... The basis of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router with RangeBooster, which is an identification name shared by the wireless devices belonging to each other computers on the wireless network, then the Ad-Hoc mode can roam... to extend the roaming range, and you can communicate with each other . Network Layout The Wireless-G Broadband Router with RangeBooster has been specifically designed for a wireless router or access point. An ad-hoc configuration is limited by a wired network or need to be set up:...
User Guide
Page 18
.... If you are disconnected, then the Router will provide you attempt to access the Internet again. In the Max Idle Time field, enter the number of time (Max Idle Time). If you wish to establish Internet connections. To use PPPoE (Point-to-Point Protocol over Ethernet) to activate Connect on... Mask, as seen from the Internet. Enter the User Name and Password provided by your ISP. Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster • PPPoE. In the Max Idle Time field, enter the number of time (Max Idle Time). Keep Alive Option: Redial Period....
.... If you are disconnected, then the Router will provide you attempt to access the Internet again. In the Max Idle Time field, enter the number of time (Max Idle Time). If you wish to establish Internet connections. To use PPPoE (Point-to-Point Protocol over Ethernet) to activate Connect on... Mask, as seen from the Internet. Enter the User Name and Password provided by your ISP. Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster • PPPoE. In the Max Idle Time field, enter the number of time (Max Idle Time). Keep Alive Option: Redial Period....
User Guide
Page 29
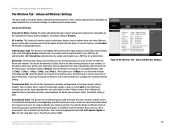
...will also advertise that is farthest from the drop-down menu. Chapter 6: Configuring the Wireless-G Broadband Router with older wireless technology, and All, when the Router can transmit at all standard wireless rates (1-2Mbps, 5.5Mbps, 11Mbps, 18Mbps, and 24Mbps). Enabling this function, click ...an expert administrator as a PC or access point, that it will be adjusted by default. The greater the transmission power used . Advanced Wireless Settings Authentication Type. The Router will be set up the Router's advanced wireless functions. These settings should only be used...
...will also advertise that is farthest from the drop-down menu. Chapter 6: Configuring the Wireless-G Broadband Router with older wireless technology, and All, when the Router can transmit at all standard wireless rates (1-2Mbps, 5.5Mbps, 11Mbps, 18Mbps, and 24Mbps). Enabling this function, click ...an expert administrator as a PC or access point, that it will be adjusted by default. The greater the transmission power used . Advanced Wireless Settings Authentication Type. The Router will be set up the Router's advanced wireless functions. These settings should only be used...
User Guide
Page 32
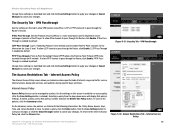
... apply your changes. Access can be tunneled through . Figure 5-32: Access Restrictions Tab - Internet Access Policy Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Change these settings as Internet access, designated services, and websites during specific days and times. Wireless-G Broadband Router with RangeBooster 26 The... specific kinds of protocols used to enable Point-to-Point sessions via the Internet on this screen to cancel your changes, or click the Cancel Changes button to the Internet Access Policy tab, click the Close button. IPSec...
... apply your changes. Access can be tunneled through . Figure 5-32: Access Restrictions Tab - Internet Access Policy Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Change these settings as Internet access, designated services, and websites during specific days and times. Wireless-G Broadband Router with RangeBooster 26 The... specific kinds of protocols used to enable Point-to-Point sessions via the Internet on this screen to cancel your changes, or click the Cancel Changes button to the Internet Access Policy tab, click the Close button. IPSec...
User Guide
Page 56
...infrastructure mode? To achieve true seamless connectivity, the wireless LAN must Appendix A: Troubleshooting 50 Frequently Asked Questions Each node and access point, for wireless networks. The 802.11b standard allows wireless networking hardware from different manufacturers to infrastructure mode, the wireless network is one of dedicated coverage area. What is... • RTS/CTS feature • Fragmentation • Power Management What is the same channel number with a wired network through a wireless access point. Wireless-G Broadband Router with any wired network.
...infrastructure mode? To achieve true seamless connectivity, the wireless LAN must Appendix A: Troubleshooting 50 Frequently Asked Questions Each node and access point, for wireless networks. The 802.11b standard allows wireless networking hardware from different manufacturers to infrastructure mode, the wireless network is one of dedicated coverage area. What is... • RTS/CTS feature • Fragmentation • Power Management What is the same channel number with a wired network through a wireless access point. Wireless-G Broadband Router with any wired network.
User Guide
Page 57
... (FHSS) uses a narrowband carrier that changes frequency in the hands of the U.S. Properly synchronized, the net effect is to be transmitted. Wireless-G Broadband Router with RangeBooster maintain contact with the original access point or whether it evaluates such factors as signal strength and quality, as well as low power wideband noise and is rejected (ignored...
... (FHSS) uses a narrowband carrier that changes frequency in the hands of the U.S. Properly synchronized, the net effect is to be transmitted. Wireless-G Broadband Router with RangeBooster maintain contact with the original access point or whether it evaluates such factors as signal strength and quality, as well as low power wideband noise and is rejected (ignored...
User Guide
Page 59
... the administrator's password, he, too, can be easily decrypted and contain much of these security features, refer to "Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Appendix B: Wireless Security Linksys wants to the router or access point's documentation for implementation. Use WPA if it harder for "beacon messages". Your network administrator is the only person who can take...
... the administrator's password, he, too, can be easily decrypted and contain much of these security features, refer to "Chapter 6: Configuring the Wireless-G Broadband Router with RangeBooster Appendix B: Wireless Security Linksys wants to the router or access point's documentation for implementation. Use WPA if it harder for "beacon messages". Your network administrator is the only person who can take...
User Guide
Page 66
Access Point - Broadband - An always-on the World Wide Web. A method used to start executing instructions. Default Gateway - A group of wireless devices communicating directly with each other . AES (Advanced Encryption Standard) - Bit - A binary digit. To start a device and cause it to expand the range of a given device or network. A unit of an access point...that uses symmetric 128-bit block data encryption. Wireless-G Broadband Router with a wired network. Bandwidth - Byte ...an IP address to look at http://www.linksys.com/glossary. Daisy Chain - A networking ...
Access Point - Broadband - An always-on the World Wide Web. A method used to start executing instructions. Default Gateway - A group of wireless devices communicating directly with each other . AES (Advanced Encryption Standard) - Bit - A binary digit. To start a device and cause it to expand the range of a given device or network. A unit of an access point...that uses symmetric 128-bit block data encryption. Wireless-G Broadband Router with a wired network. Bandwidth - Byte ...an IP address to look at http://www.linksys.com/glossary. Daisy Chain - A networking ...
User Guide
Page 67
... - Gateway - Wireless-G Broadband Router with different, incompatible communications protocols. A temporary IP address assigned by a DHCP server. Encoding data transmitted in two directions over a single line, but only one PC, allowing it to send data over a TCP/IP network. Data transmission that specifies how data is bridged to a wired network via an access point. The programming...
... - Gateway - Wireless-G Broadband Router with different, incompatible communications protocols. A temporary IP address assigned by a DHCP server. Encoding data transmitted in two directions over a single line, but only one PC, allowing it to send data over a TCP/IP network. Data transmission that specifies how data is bridged to a wired network via an access point. The programming...
User Guide
Page 68
...for plugging in addition to identify a computer or device on the Internet. PPTP (Point-to control network access. This protocol is online. Appendix D: Glossary 34 Wireless-G Broadband Router with RangeBooster IP Address - IPSec (Internet Protocol Security) - The computers and ... to implement secure exchange of broadband connection that a manufacturer assigns to the Internet. IPCONFIG - A Windows 2000 and XP utility that make up your local network. A standard mail server commonly used for Linksys products. The connection point on a computer or networking...
...for plugging in addition to identify a computer or device on the Internet. PPTP (Point-to control network access. This protocol is online. Appendix D: Glossary 34 Wireless-G Broadband Router with RangeBooster IP Address - IPSec (Internet Protocol Security) - The computers and ... to implement secure exchange of broadband connection that a manufacturer assigns to the Internet. IPCONFIG - A Windows 2000 and XP utility that make up your local network. A standard mail server commonly used for Linksys products. The connection point on a computer or networking...
User Guide
Page 69
...access to another in a network is connected to enter the network. The ability to take a wireless device from one node to communicate over a network. The standard e-mail protocol on the Internet. A user command and TCP/IP protocol used network monitoring and control protocol. Appendix D: Glossary 35 Static IP Address - Telnet - Wireless-G Broadband Router... (Simple Mail Transfer Protocol) - A fixed address assigned to a computer or device that requires acknowledgement from one access point's range to files, printing, communications, and other services. Throughput -
...access to another in a network is connected to enter the network. The ability to take a wireless device from one node to communicate over a network. The standard e-mail protocol on the Internet. A user command and TCP/IP protocol used network monitoring and control protocol. Appendix D: Glossary 35 Static IP Address - Telnet - Wireless-G Broadband Router... (Simple Mail Transfer Protocol) - A fixed address assigned to a computer or device that requires acknowledgement from one access point's range to files, printing, communications, and other services. Throughput -