User Guide
Page 3
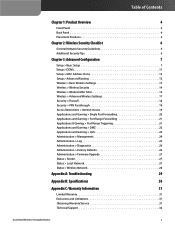
...Security Checklist 6 General Network Security Guidelines 6 Additional Security Tips 6 Chapter 3: Advanced Configuration 7 Setup > Basic Setup 7 Setup > DDNS 11 Setup > MAC Address Clone 12 Setup > Advanced Routing 12 Wireless > Basic Wireless Settings 13 Wireless > Wireless Security 14 Wireless > Wireless MAC Filter 16 Wireless > Advanced Wireless Settings 17 Security > Firewall 18 Security > VPN... 26 Administration > Firmware Upgrade 27 Status > Router 27 Status > Local Network 27 Status > Wireless Network 28 Appendix A: Troubleshooting 29 Appendix B: Specifications ...
...Security Checklist 6 General Network Security Guidelines 6 Additional Security Tips 6 Chapter 3: Advanced Configuration 7 Setup > Basic Setup 7 Setup > DDNS 11 Setup > MAC Address Clone 12 Setup > Advanced Routing 12 Wireless > Basic Wireless Settings 13 Wireless > Wireless Security 14 Wireless > Wireless MAC Filter 16 Wireless > Advanced Wireless Settings 17 Security > Firewall 18 Security > VPN... 26 Administration > Firmware Upgrade 27 Status > Router 27 Status > Local Network 27 Status > Wireless Network 28 Appendix A: Troubleshooting 29 Appendix B: Specifications ...
User Guide
Page 20
... changes. Select this screen to pass through the Router, keep the default, Enabled. To allow IPSec tunnels to pass through an IP network. To allow cookie usage. To enable a policy, select Enabled. To delete a policy, click Delete. Advanced Configuration Security > VPN Passthrough VPN Passthrough IPSec Passthrough Internet Protocol Security (IPSec) is the method used to filter...
... changes. Select this screen to pass through the Router, keep the default, Enabled. To allow IPSec tunnels to pass through an IP network. To allow cookie usage. To enable a policy, select Enabled. To delete a policy, click Delete. Advanced Configuration Security > VPN Passthrough VPN Passthrough IPSec Passthrough Internet Protocol Security (IPSec) is the method used to filter...