(English) Rescue and Recovery 4.3 Deployment Guide
Page 5
...CLEANDRV.EXE 64 CONVDATE 64 CREATSP 64 InvAgent 65 MapDrv 66 Rescue and Recovery Boot manager control (BMGR32 67 BMGR CLEAN 70 Active Directory Support 71 Administrative (ADM) template files . .... . . . 71 Group Policy settings 72 Appendix B. Notices 85 Trademarks 86 © Copyright Lenovo 2008, 2009 iii User tasks 83 Windows 7 83 Create rescue media 83 Rescue and Recovery user interface...Backups 20 Scheduling backups and associated tasks . . . 20 Sysprep Backup/Restore 21 Mapping a network drive for backups . . . . 22 Password Persistence 25 EFS file limitation 25 Battery ...
...CLEANDRV.EXE 64 CONVDATE 64 CREATSP 64 InvAgent 65 MapDrv 66 Rescue and Recovery Boot manager control (BMGR32 67 BMGR CLEAN 70 Active Directory Support 71 Administrative (ADM) template files . .... . . . 71 Group Policy settings 72 Appendix B. Notices 85 Trademarks 86 © Copyright Lenovo 2008, 2009 iii User tasks 83 Windows 7 83 Create rescue media 83 Rescue and Recovery user interface...Backups 20 Scheduling backups and associated tasks . . . 20 Sysprep Backup/Restore 21 Mapping a network drive for backups . . . . 22 Password Persistence 25 EFS file limitation 25 Battery ...
(English) Rescue and Recovery 4.3 Deployment Guide
Page 27
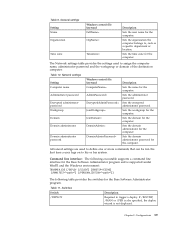
... the switches for the computer. Chapter 3. Table 9. Sets the organization the computer belongs to his or her system. Network settings Setting Windows control file keyword Description Computer name ComputerName= Sets the name for the computer. If /BOOTSP, /MAN or /PER is ...= Sets the encrypted administrator password. Configurations 19 Sets the time zone for the computer. General settings Setting Name Organization Windows control file keyword FullName= OrgName= Time zone TimeZone= Description Sets the user name for the computer. Table 11. Domain administrator ...
... the switches for the computer. Chapter 3. Table 9. Sets the organization the computer belongs to his or her system. Network settings Setting Windows control file keyword Description Computer name ComputerName= Sets the name for the computer. If /BOOTSP, /MAN or /PER is ...= Sets the encrypted administrator password. Configurations 19 Sets the time zone for the computer. General settings Setting Name Organization Windows control file keyword FullName= OrgName= Time zone TimeZone= Description Sets the user name for the computer. Table 11. Domain administrator ...
(English) Rescue and Recovery 4.3 Deployment Guide
Page 30
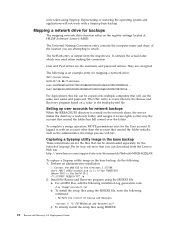
...files for large enterprise that you are for the files that can be copied onto multiple computers that created the folder has full control over the folder. Perform an administrative installation: :: Extract the WWW EXE to attach. To silently install the setup files using the...with a Sysprep base backup. User and Pwd entries are encrypted. The following is an example entry for network backups When the RRBACKUPS directory is output from the Lenovo Web site: http://www.lenovo.com/support/site.wss/document.do the following: 1. The UNC entry is the build ID.) ="C:\TVTRR" ...
...files for large enterprise that you are for the files that can be copied onto multiple computers that created the folder has full control over the folder. Perform an administrative installation: :: Extract the WWW EXE to attach. To silently install the setup files using the...with a Sysprep base backup. User and Pwd entries are encrypted. The following is an example entry for network backups When the RRBACKUPS directory is output from the Lenovo Web site: http://www.lenovo.com/support/site.wss/document.do the following: 1. The UNC entry is the build ID.) ="C:\TVTRR" ...
(English) Rescue and Recovery 4.3 Deployment Guide
Page 75
... presents the switches and their results for a ThinkVantage Technology product: This function stores the network share information in the registry key: mapdrv /view /user /pwd Rescue and Recovery Boot manager control (BMGR32) The boot manager interface command-line interface is BMGR32. Boot to indicate the... in the directory C:\Program Files\Common Files\Lenovo\BMGR. This must be called prior to partition 2. Table 26. Boot to booting. Boot to Predesktop Area. Using MapDrv The following command is used to display the network share information saved in the registry to use...
... presents the switches and their results for a ThinkVantage Technology product: This function stores the network share information in the registry key: mapdrv /view /user /pwd Rescue and Recovery Boot manager control (BMGR32) The boot manager interface command-line interface is BMGR32. Boot to indicate the... in the directory C:\Program Files\Common Files\Lenovo\BMGR. This must be called prior to partition 2. Table 26. Boot to booting. Boot to Predesktop Area. Using MapDrv The following command is used to display the network share information saved in the registry to use...
(English) Rescue and Recovery 4.5 Deployment Guide
Page 3
...EXE 55 CONVDATE 55 CREATSP 56 InvAgent 56 MapDrv 57 Rescue and Recovery Boot manager control (BMGR32 58 BMGR CLEAN 61 Active Directory Support 62 Administrative (ADM) template files... 17 Scheduling backups and associated tasks . . 18 Sysprep Backup/Restore 18 Mapping a network drive for backups . . . . 19 Password Persistence 21 EFS file limitation 22 ...75 Windows 7 75 Create rescue media 75 Rescue and Recovery user interface switching . . 75 © Copyright Lenovo 2008, 2011 i Installation 3 Installation considerations 3 Installing the Rescue and Recovery program . . . . 3 ...
...EXE 55 CONVDATE 55 CREATSP 56 InvAgent 56 MapDrv 57 Rescue and Recovery Boot manager control (BMGR32 58 BMGR CLEAN 61 Active Directory Support 62 Administrative (ADM) template files... 17 Scheduling backups and associated tasks . . 18 Sysprep Backup/Restore 18 Mapping a network drive for backups . . . . 19 Password Persistence 21 EFS file limitation 22 ...75 Windows 7 75 Create rescue media 75 Rescue and Recovery user interface switching . . 75 © Copyright Lenovo 2008, 2011 i Installation 3 Installation considerations 3 Installing the Rescue and Recovery program . . . . 3 ...
(English) Rescue and Recovery 4.5 Deployment Guide
Page 22
... recovery. Sets the time zone for the computer. Sets the administrator password. The information contained in the correct Windows control files. Network settings Setting Computer name Administrator password Encrypted administrator password Workgroup Domain Windows control file keyword ComputerName= AdminPassword= EncryptedAdminPassword= JoinWorkgroup= JoinDomain= Description Sets the name for the computer. In addition, manifest files...
... recovery. Sets the time zone for the computer. Sets the administrator password. The information contained in the correct Windows control files. Network settings Setting Computer name Administrator password Encrypted administrator password Workgroup Domain Windows control file keyword ComputerName= AdminPassword= EncryptedAdminPassword= JoinWorkgroup= JoinDomain= Description Sets the name for the computer. In addition, manifest files...
(English) Rescue and Recovery 4.5 Deployment Guide
Page 23
... access service partition. Return codes Return code 0 1 2 3 4 5 6 Return message Success Unable to define one or more commands that can be set active. Chapter 3. Network settings (continued) Setting Windows control file keyword Domain administrator DomainAdmin= Domain administrator password DomainAdminPassword= Description Sets the domain administrator for the Base Software Administrator program. The executable returns...
... access service partition. Return codes Return code 0 1 2 3 4 5 6 Return message Success Unable to define one or more commands that can be set active. Chapter 3. Network settings (continued) Setting Windows control file keyword Domain administrator DomainAdmin= Domain administrator password DomainAdminPassword= Description Sets the domain administrator for the Base Software Administrator program. The executable returns...
(English) Rescue and Recovery 4.5 Deployment Guide
Page 25
...Pwd=11622606415100000000014918505422010521006401209203708202015... Setting up user accounts for backups The mapping network drive function relies on the Microsoft Web site at HKLM\Software\Lenovo\MND. To complete a merge operation, MOVE permissions exist for mapping a network drive: UNC=\\server\share NetPath=\\9.88.77.66\share User...Backup image. Capturing a Sysprep utility image in with an account other than the account that created the folder has full control over the folder. The Universal Naming Convention entry contains the computer name and share of the location you can be copied ...
...Pwd=11622606415100000000014918505422010521006401209203708202015... Setting up user accounts for backups The mapping network drive function relies on the Microsoft Web site at HKLM\Software\Lenovo\MND. To complete a merge operation, MOVE permissions exist for mapping a network drive: UNC=\\server\share NetPath=\\9.88.77.66\share User...Backup image. Capturing a Sysprep utility image in with an account other than the account that created the folder has full control over the folder. The Universal Naming Convention entry contains the computer name and share of the location you can be copied ...
(English) Rescue and Recovery 4.5 Deployment Guide
Page 64
..., user name, and password. The stored network share. Sets the timeout value. The following command sets the Unc, User and Pwd values in the registry key: mapdrv /view /user /pwd Rescue and Recovery Boot manager control (BMGR32) Note: This section is applicable for this share. The ...following command is made. It then attempts to connect to Silent. Set to the specified network share using the Unc, User, and Pwd values in the registry...
..., user name, and password. The stored network share. Sets the timeout value. The following command sets the Unc, User and Pwd values in the registry key: mapdrv /view /user /pwd Rescue and Recovery Boot manager control (BMGR32) Note: This section is applicable for this share. The ...following command is made. It then attempts to connect to Silent. Set to the specified network share using the Unc, User, and Pwd values in the registry...
(English) Access Connections Profile Deployment guide
Page 10
...or later simplifies the task of deploying location profiles, global settings, and control policies to individuals or groups of connections available in the field using the detected wireless network name and default settings. Requirements and specifications for deploying Access Connections Collecting ... switch between profiles. v Automatic switching of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide Considerations...
...or later simplifies the task of deploying location profiles, global settings, and control policies to individuals or groups of connections available in the field using the detected wireless network name and default settings. Requirements and specifications for deploying Access Connections Collecting ... switch between profiles. v Automatic switching of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide Considerations...
(English) Access Connections Profile Deployment guide
Page 19
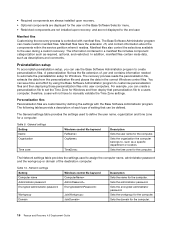
... and export location profiles. Figure 7. The Distribution Control List helps reduce unauthorized network access. Create Group The file must be imported which controls the capabilities that will prevent users from creating and distributing network access profiles. v Create and apply WLAN location... profiles using the Find Wireless Network function for updates. Working with the Administrator ...
... and export location profiles. Figure 7. The Distribution Control List helps reduce unauthorized network access. Create Group The file must be imported which controls the capabilities that will prevent users from creating and distributing network access profiles. v Create and apply WLAN location... profiles using the Find Wireless Network function for updates. Working with the Administrator ...
(English) Access Connections Profile Deployment guide
Page 20
... users without administrator privileges. v Automatic location profile switching. You can also control a users ability to create and apply location profiles v Allow wireless connection at Windows logon v Close all wireless network connections when a user logs off v Disable Adhoc connection type option in wireless... LAN profiles v Enable automatic wireless LAN radio control v Allow selection of location profiles with Fn+F5 On Screen...
... users without administrator privileges. v Automatic location profile switching. You can also control a users ability to create and apply location profiles v Allow wireless connection at Windows logon v Close all wireless network connections when a user logs off v Disable Adhoc connection type option in wireless... LAN profiles v Enable automatic wireless LAN radio control v Allow selection of location profiles with Fn+F5 On Screen...
(English) Access Connections Profile Deployment guide
Page 33
This community setting is not available in location profile. Enable auto WLAN radio control When automatic wireless LAN radio control is not associated with Ethernet or wireless connections and switch between any access points to use the Windows logon credentials....allow clients to view or edit VPN connection setting in location setting profile. Working with FWN apply WLAN location profiles using Find Wireless Network function. Hide browser proxy Do not allow clients to view or edit browser proxy setting in location profile. Enable single sign on...
This community setting is not available in location profile. Enable auto WLAN radio control When automatic wireless LAN radio control is not associated with Ethernet or wireless connections and switch between any access points to use the Windows logon credentials....allow clients to view or edit VPN connection setting in location setting profile. Working with FWN apply WLAN location profiles using Find Wireless Network function. Hide browser proxy Do not allow clients to view or edit browser proxy setting in location profile. Enable single sign on...
(English) Deployment Guide for IBM Access Connections
Page 10
... profiles, settings, time, and reducing help desk calls Create location profiles with network adapters, that control configuration and management for network name, SSID, and security setup, including the definition of every new IBM ThinkPad® notebook system. And the user must modify Windows network properties to set through multiple facilities, windows, and utilities in a location...
... profiles, settings, time, and reducing help desk calls Create location profiles with network adapters, that control configuration and management for network name, SSID, and security setup, including the definition of every new IBM ThinkPad® notebook system. And the user must modify Windows network properties to set through multiple facilities, windows, and utilities in a location...
(English) Deployment Guide for IBM Access Connections
Page 11
...a wireless adapter-so users can result in range. This capability enables mobile PC users to find new wireless LAN networks, Access Connections software performs the following: v Controls the settings for the office. When you return to your PC and the wireless access point you are associated with ...settings for example, when you may have a 100 Mbps Ethernet (wired) connection at work and home and easily reestablish a network connection. Ethernet-...
...a wireless adapter-so users can result in range. This capability enables mobile PC users to find new wireless LAN networks, Access Connections software performs the following: v Controls the settings for the office. When you return to your PC and the wireless access point you are associated with ...settings for example, when you may have a 100 Mbps Ethernet (wired) connection at work and home and easily reestablish a network connection. Ethernet-...
(English) Deployment Guide for IBM Access Connections
Page 12
... and other connectivity issues. The Bluetooth security levels can activate a location profile to easily control connection to be found in use help conserve notebook battery power. v Disables wireless LAN ..., which uses the DUN Bluetooth profile. Turning off the Bluetooth radio and to the network when users are different. A troubleshooting guide is accessible from ) an IP address,... common questions and answers. Helping your clients stay connected Access Connections software provides your ThinkPad notebook. An index provides quick access to the Internet or their e-mail.) Access...
... and other connectivity issues. The Bluetooth security levels can activate a location profile to easily control connection to be found in use help conserve notebook battery power. v Disables wireless LAN ..., which uses the DUN Bluetooth profile. Turning off the Bluetooth radio and to the network when users are different. A troubleshooting guide is accessible from ) an IP address,... common questions and answers. Helping your clients stay connected Access Connections software provides your ThinkPad notebook. An index provides quick access to the Internet or their e-mail.) Access...
(English) Deployment Guide for IBM Access Connections
Page 13
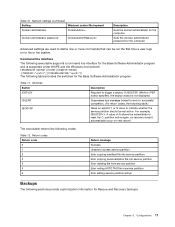
...a distributed profile can import various deployment packages using distribution control lists (selectively distribute the profiles based on new profile-deployment capabilities to ease... the wrong WEP key is a daunting task. Using Access Connections 7 Capitalizing on ThinkPad serial numbers). The Access Connections profile-deployment feature enables system administrators to IT administrators ... The feature must be broken. It is available to define the network adapter and associated networking parameters for registration and download. v Create secure profile deployment packages ...
...a distributed profile can import various deployment packages using distribution control lists (selectively distribute the profiles based on new profile-deployment capabilities to ease... the wrong WEP key is a daunting task. Using Access Connections 7 Capitalizing on ThinkPad serial numbers). The Access Connections profile-deployment feature enables system administrators to IT administrators ... The feature must be broken. It is available to define the network adapter and associated networking parameters for registration and download. v Create secure profile deployment packages ...
(English) Deployment Guide for IBM Access Connections
Page 15
...profiles and settings can be reduced and users can immediately take advantage of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can ... deployment methods. Chapter 3. This feature simplifies the task of deploying location profiles, global settings, and control policies to connect and the kinds of connections available in those locations will help you develop preconfigured profiles... in a corporate environment. Considerations for deployment The current list of their network connections without intervention.
...profiles and settings can be reduced and users can immediately take advantage of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can ... deployment methods. Chapter 3. This feature simplifies the task of deploying location profiles, global settings, and control policies to connect and the kinds of connections available in those locations will help you develop preconfigured profiles... in a corporate environment. Considerations for deployment The current list of their network connections without intervention.
(English) Deployment Guide for IBM Access Connections
Page 20
... values: a. A global setting in place for a particular profile. When the Allow silent import of this case the network settings in the profile cannot be defined per profile and can delete the profile. Access control policies can be modified, deleted or copied. b. Limited Users can only create dial-up connection-type profiles and...
... values: a. A global setting in place for a particular profile. When the Allow silent import of this case the network settings in the profile cannot be defined per profile and can delete the profile. Access control policies can be modified, deleted or copied. b. Limited Users can only create dial-up connection-type profiles and...
(English) Deployment Guide for IBM Access Connections
Page 21
... groups of serial numbers that represent different organizations of serial numbers, flat text files can help reduce unauthorized network access. Distribution control lists ensure that each line contains a single serial number. Figure 5. Define Distribution Control List When creating groups of users who need different location profiles. The next time Access Connections runs, it...
... groups of serial numbers that represent different organizations of serial numbers, flat text files can help reduce unauthorized network access. Distribution control lists ensure that each line contains a single serial number. Figure 5. Define Distribution Control List When creating groups of users who need different location profiles. The next time Access Connections runs, it...