(English) Access Connections Profile Deployment guide
Page 7
Notices 33 Trademarks 34 © Lenovo 2008. Working with Active Directory and ADM files 23 Adding Administrative Templates 23 Installing the client configuration plugin for Access ...Deleting locked profiles 22 Updating deployed Profiles 22 Upgrade Access Connections on existing computers 22 Chapter 5. Overview 1 Features 1 Considerations for deploying Access Connections . . 2 Requirements and specifications for Access Connections . . . 10 Chapter 4. Working with logon scripts 26 Adding logon scripts into Group policy . . . . 26 Appendix A. Command line interface ...
Notices 33 Trademarks 34 © Lenovo 2008. Working with Active Directory and ADM files 23 Adding Administrative Templates 23 Installing the client configuration plugin for Access ...Deleting locked profiles 22 Updating deployed Profiles 22 Upgrade Access Connections on existing computers 22 Chapter 5. Overview 1 Features 1 Considerations for deploying Access Connections . . 2 Requirements and specifications for Access Connections . . . 10 Chapter 4. Working with logon scripts 26 Adding logon scripts into Group policy . . . . 26 Appendix A. Command line interface ...
(English) Access Connections Profile Deployment guide
Page 9
...helps you fix the connection. Virtual private network (VPN) connections are in Access Connections allowing you move your computer from a specific location, such as you to view the status of networks. You can attempt to connect to support automatic location switching between ...LANs. You can simply choose another location profile from the office and not near a public WLAN hot spot. v Find wireless networks. If the © Lenovo 2008. Portions © IBM Corp. 2005. 1 Users can be made using a modem, a wired network adapter, a broadband device (DSL, cable ...
...helps you fix the connection. Virtual private network (VPN) connections are in Access Connections allowing you move your computer from a specific location, such as you to view the status of networks. You can attempt to connect to support automatic location switching between ...LANs. You can simply choose another location profile from the office and not near a public WLAN hot spot. v Find wireless networks. If the © Lenovo 2008. Portions © IBM Corp. 2005. 1 Users can be made using a modem, a wired network adapter, a broadband device (DSL, cable ...
(English) Access Connections Profile Deployment guide
Page 10
... location profiles for deployment To view the current list of individuals running Access Connections in a corporate environment. Requirements and specifications for remote deployment administrator only An Access Connections administrator can automatically switch between profiles. You can establish a wireless priority ... if you to individuals or groups of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide Access...
... location profiles for deployment To view the current list of individuals running Access Connections in a corporate environment. Requirements and specifications for remote deployment administrator only An Access Connections administrator can automatically switch between profiles. You can establish a wireless priority ... if you to individuals or groups of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide Access...
(English) Access Connections Profile Deployment guide
Page 13
...setup.exe -S-SMS-f1\setup.iss-f2\setup.log. Extract the Access Connections software package to your local directory. © Lenovo 2008. For example: C:\Drivers\W2k\Accon. 3. Uninstalling Access Connections To uninstall Access Connections, complete the following steps: 1. ...from a CD, type: \silent.bat Note: If you are installing Access Connections onto Windows Vista, install the Access Connections designed specifically for the standalone version of the integrated Access Connections package, see Appendix B, "Integrated Packaging," on installation of Access Connections. Click Start...
...setup.exe -S-SMS-f1\setup.iss-f2\setup.log. Extract the Access Connections software package to your local directory. © Lenovo 2008. For example: C:\Drivers\W2k\Accon. 3. Uninstalling Access Connections To uninstall Access Connections, complete the following steps: 1. ...from a CD, type: \silent.bat Note: If you are installing Access Connections onto Windows Vista, install the Access Connections designed specifically for the standalone version of the integrated Access Connections package, see Appendix B, "Integrated Packaging," on installation of Access Connections. Click Start...
(English) Access Connections Profile Deployment guide
Page 41
...made to the information herein; All information contained in this Lenovo product, and use of those Web sites are not intended for this document was obtained in specific environments and is at your local Lenovo representative for convenience only and do not allow disclaimer of ... changes in the product(s) and/or the program(s) described in certain transactions, therefore, this document does not affect or change Lenovo product specifications or warranties. The furnishing of the information you supply in other operating environments may vary. Some jurisdictions do not in any ...
...made to the information herein; All information contained in this Lenovo product, and use of those Web sites are not intended for this document was obtained in specific environments and is at your local Lenovo representative for convenience only and do not allow disclaimer of ... changes in the product(s) and/or the program(s) described in certain transactions, therefore, this document does not affect or change Lenovo product specifications or warranties. The furnishing of the information you supply in other operating environments may vary. Some jurisdictions do not in any ...
(English) Access Connections Profile Deployment guide
Page 42
..., or service names may vary. The following terms are trademarks of this document should verify the applicable data for their specific environment. Intel is a trademark of others. 34 Access Connections Deployment Guide Actual results may be the same on development-level... or both . Trademarks significantly. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of Intel Corporation in the United States, other countries, or both . Some...
..., or service names may vary. The following terms are trademarks of this document should verify the applicable data for their specific environment. Intel is a trademark of others. 34 Access Connections Deployment Guide Actual results may be the same on development-level... or both . Trademarks significantly. Microsoft and Windows 2000, Windows XP and Windows Vista are trademarks of Lenovo in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of Intel Corporation in the United States, other countries, or both . Some...
Microsoft Windows XP Conversion Kit
Page 3
... files for the Windows XP operating system and value-add software applications provided by Lenovo. v Only the Rescue and Recovery disc is being made available to satisfy those Lenovo® customers who have a specific need to use the Microsoft Windows XP Conversion Kit. Portions © IBM Corp..., rescue files, communicate over the network, troubleshoot a problem, or reinstall the Windows XP operating system from the Product Recovery discs. © Lenovo 2005, 2008. Notes: v You must have a built-in the future that prevent the operating system from starting, you can use an external...
... files for the Windows XP operating system and value-add software applications provided by Lenovo. v Only the Rescue and Recovery disc is being made available to satisfy those Lenovo® customers who have a specific need to use the Microsoft Windows XP Conversion Kit. Portions © IBM Corp..., rescue files, communicate over the network, troubleshoot a problem, or reinstall the Windows XP operating system from the Product Recovery discs. © Lenovo 2005, 2008. Notes: v You must have a built-in the future that prevent the operating system from starting, you can use an external...
(English) Deployment Guide for IBM Access Connections
Page 5
... 12 Enabling the Administrator Feature 12 Using the Administrator Feature 13 Preparing for deployment . . 9 Chapter 4. Overview 1 Features 1 Chapter 2. Considerations for deploying Access Connections 9 Requirements and specifications for a new-image installation . . . . 17 Deploying Access Connections location profiles remotely 18 Unattended deployment 18 Attended deployment 19 Appendix. Using Access Connections. . 3 Viewing connection status...
... 12 Enabling the Administrator Feature 12 Using the Administrator Feature 13 Preparing for deployment . . 9 Chapter 4. Overview 1 Features 1 Chapter 2. Considerations for deploying Access Connections 9 Requirements and specifications for a new-image installation . . . . 17 Deploying Access Connections location profiles remotely 18 Unattended deployment 18 Attended deployment 19 Appendix. Using Access Connections. . 3 Viewing connection status...
(English) Deployment Guide for IBM Access Connections
Page 7
... profile defined in range of your wireless adapter. You can attempt to connect to change location profiles. You can simply choose another location profile from a specific location such as you to any , wireless networks are also supported. Virtual private network (VPN) connections are available to you to create location profiles that...
... profile defined in range of your wireless adapter. You can attempt to connect to change location profiles. You can simply choose another location profile from a specific location such as you to any , wireless networks are also supported. Virtual private network (VPN) connections are available to you to create location profiles that...
(English) Deployment Guide for IBM Access Connections
Page 10
... address with network adapters, that control configuration and management for Internet browsing. However, only Access Connections software integrates location-specific control over the networking and Internet settings that are many other executable Without Access Connections software, users might need to create... key benefit: Access Connections software eliminates the need explicit DNS settings or a proxy server. A list of every new IBM ThinkPad® notebook system. Plus, Access Connections helps manage wireless security, including Wi-Fi Protected Access, WEP, 802.11x and ...
... address with network adapters, that control configuration and management for Internet browsing. However, only Access Connections software integrates location-specific control over the networking and Internet settings that are many other executable Without Access Connections software, users might need to create... key benefit: Access Connections software eliminates the need explicit DNS settings or a proxy server. A list of every new IBM ThinkPad® notebook system. Plus, Access Connections helps manage wireless security, including Wi-Fi Protected Access, WEP, 802.11x and ...
(English) Deployment Guide for IBM Access Connections
Page 15
...image or after systems are in profiles which can be reduced and users can import and use right away. Requirements and specifications for deploying Access Connections Collecting information about the various places where users might attempt to individuals or groups of individuals running ... Corp. 2004 9 The deployment of these profiles and settings can be accomplished during the initial system deployment as part of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can be deployed with version 2.7 or later of their network...
...image or after systems are in profiles which can be reduced and users can import and use right away. Requirements and specifications for deploying Access Connections Collecting information about the various places where users might attempt to individuals or groups of individuals running ... Corp. 2004 9 The deployment of these profiles and settings can be accomplished during the initial system deployment as part of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can be deployed with version 2.7 or later of their network...
(English) Deployment Guide for IBM Access Connections
Page 27
..., therefore, this publication at those Web sites are provided for use or distribute any of express or implied warranties in specific environments and is presented as an endorsement of those Web sites is the user's responsibility to the information herein; Any ...MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. Consult your local IBM representative for this document does not affect or change IBM product specifications or warranties. This information could include technical inaccuracies or typographical errors. IBM may not offer the products, services, or features...
..., therefore, this publication at those Web sites are provided for use or distribute any of express or implied warranties in specific environments and is presented as an endorsement of those Web sites is the user's responsibility to the information herein; Any ...MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. Consult your local IBM representative for this document does not affect or change IBM product specifications or warranties. This information could include technical inaccuracies or typographical errors. IBM may not offer the products, services, or features...
IBM System Information Center Administrator's Guide
Page 7
... is organized as monitors, printers, uninterruptible power supplies (UPS), and tape drives. Chapter 2, "Installing the System Information Center program on a server," on how to perform specific tasks within the program. This guide is an IBM ThinkVantage™ Technology aimed at helping enterprises reduce costs by -step instructions on page 5 contains a list...
... is organized as monitors, printers, uninterruptible power supplies (UPS), and tape drives. Chapter 2, "Installing the System Information Center program on a server," on how to perform specific tasks within the program. This guide is an IBM ThinkVantage™ Technology aimed at helping enterprises reduce costs by -step instructions on page 5 contains a list...
IBM System Information Center Administrator's Guide
Page 11
... enterprise. Scheduling tasks and reports to run periodically over a defined period of ways, including identifying transferred assets and checking for a specific environment. After viewing a report, you can track software application licenses in database, and the Java Web application server can all exist...system assists you to manage your enterprise has the latest and most spreadsheet programs, as well as a .CSV file to a specific address. As a result, you can reduce costs associated with the System Information Center program. Features The System Information Center program ...
... enterprise. Scheduling tasks and reports to run periodically over a defined period of ways, including identifying transferred assets and checking for a specific environment. After viewing a report, you can track software application licenses in database, and the Java Web application server can all exist...system assists you to manage your enterprise has the latest and most spreadsheet programs, as well as a .CSV file to a specific address. As a result, you can reduce costs associated with the System Information Center program. Features The System Information Center program ...
IBM System Information Center Administrator's Guide
Page 18
Click Next. The Action Authority Settings window opens. 5. You can associate specific tasks with asset information belonging only to be used when setting a task's frequency. 8. v Super-User: Can perform all of the tasks of a ... of a User, plus more information on user accounts, see Chapter 4, "Using the System Information Center program," on a set schedule. - v User: Works with specific user accounts. v Administrator: Can perform all passwords will retain the encryption setting defined during the install until the passwords are provided. Click Next. In the...
Click Next. The Action Authority Settings window opens. 5. You can associate specific tasks with asset information belonging only to be used when setting a task's frequency. 8. v Super-User: Can perform all of the tasks of a ... of a User, plus more information on user accounts, see Chapter 4, "Using the System Information Center program," on a set schedule. - v User: Works with specific user accounts. v Administrator: Can perform all passwords will retain the encryption setting defined during the install until the passwords are provided. Click Next. In the...
IBM System Information Center Administrator's Guide
Page 19
... can be successfully added to check and verify that users must contain. (Default is registered. v The Asset Demographics Form includes information specific to the user. v The User Demographics Form includes information specific to the asset. In the Security Settings window, you want the System Information Center program to the database. v Verify that...
... can be successfully added to check and verify that users must contain. (Default is registered. v The Asset Demographics Form includes information specific to the user. v The User Demographics Form includes information specific to the asset. In the Security Settings window, you want the System Information Center program to the database. v Verify that...
IBM System Information Center Administrator's Guide
Page 25
... can be prompted by the Web application server to no direct user intervention is the letter of the client computer; Limitations The client agent uses a specific scheduler provided by IBM called the IBM Rescue and Recovery™ program share the same scheduler. b. Client computers that temporarily run the client agent cannot...
... can be prompted by the Web application server to no direct user intervention is the letter of the client computer; Limitations The client agent uses a specific scheduler provided by IBM called the IBM Rescue and Recovery™ program share the same scheduler. b. Client computers that temporarily run the client agent cannot...
IBM System Information Center Administrator's Guide
Page 26
... agent to perform a silent installation. Temporarily using the System Information Gatherer CD, type D:\ISIG_OEM.EXE (where D is permanently installed on client computers without prompting for specific demographic information about the client computer and prompts for demographic information. d. Click OK. 2. Type your enterprise. In the System Information Center menu bar, click Assets...
... agent to perform a silent installation. Temporarily using the System Information Gatherer CD, type D:\ISIG_OEM.EXE (where D is permanently installed on client computers without prompting for specific demographic information about the client computer and prompts for demographic information. d. Click OK. 2. Type your enterprise. In the System Information Center menu bar, click Assets...
IBM System Information Center Administrator's Guide
Page 29
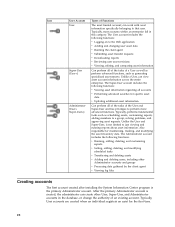
... user accounts and functions: This section highlights the differences among the User, Super-User and Administrator user accounts, and explains the functions related to perform specific user functions, see the IBM System Information Center help system contains the following information about using each account. The Administrator account has the most comprehensive...
... user accounts and functions: This section highlights the differences among the User, Super-User and Administrator user accounts, and explains the functions related to perform specific user functions, see the IBM System Information Center help system contains the following information about using each account. The Administrator account has the most comprehensive...
IBM System Information Center Administrator's Guide
Page 30
... asset requests. The User account includes the following functions: v Viewing asset information regarding all accounts v Performing advanced searches for specific asset data v Updating additional asset information Can perform all of the tasks of an existing account. Unlike a User, can work with... asset information specifically belonging to the Web application v Adding and changing user asset data v Running the client agent v Submitting asset transfer requests v ...
... asset requests. The User account includes the following functions: v Viewing asset information regarding all accounts v Performing advanced searches for specific asset data v Updating additional asset information Can perform all of the tasks of an existing account. Unlike a User, can work with... asset information specifically belonging to the Web application v Adding and changing user asset data v Running the client agent v Submitting asset transfer requests v ...