End User License Agreement
Page 2
... Product may not reverse engineer, decompile, or disassemble the Software Product, except and only to the original Software Product provided by HP as other terms along with the update or supplement. LIMITATION ON REVERSE ENGINEERING. You agree that the right to the transfer, ...terminated or rejected. b. You may make a one-time transfer of the HP Product with/for restoring the hard disk of the Software Product to comply with /for the original Software Product identified by HP unless HP provides other applicable laws and international treaty provisions. This EULA will prevail. ...
... Product may not reverse engineer, decompile, or disassemble the Software Product, except and only to the original Software Product provided by HP as other terms along with the update or supplement. LIMITATION ON REVERSE ENGINEERING. You agree that the right to the transfer, ...terminated or rejected. b. You may make a one-time transfer of the HP Product with/for restoring the hard disk of the Software Product to comply with /for the original Software Product identified by HP unless HP provides other applicable laws and international treaty provisions. This EULA will prevail. ...
HP ProtectTools Security Software 2010
Page 1
... security software overview 2 HP security setup wizard...4 User management...5 Backup and restore ...5 Security software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace®...
... security software overview 2 HP security setup wizard...4 User management...5 Backup and restore ...5 Security software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace®...
HP ProtectTools Security Software 2010
Page 4
...such as the setup wizard, user management and security backup and restore. This launches the setup wizard for total information protection. It allows you benefit from security features that all new HP ProtectTools security modules introduced over time are easier to safeguard the ... notebook is setup protected. This approach ensures that are highly integrated. The setup wizard then does the rest. 4 Figure 2. HP ProtectTools Security Manager provides global functionality needed by taking advantage of the multiple security hardware attributes of the personal computing device. The...
...such as the setup wizard, user management and security backup and restore. This launches the setup wizard for total information protection. It allows you benefit from security features that all new HP ProtectTools security modules introduced over time are easier to safeguard the ... notebook is setup protected. This approach ensures that are highly integrated. The setup wizard then does the rest. 4 Figure 2. HP ProtectTools Security Manager provides global functionality needed by taking advantage of the multiple security hardware attributes of the personal computing device. The...
HP ProtectTools Security Software 2010
Page 5
...the pre-boot environment. It is available from the ground up and completely integrated. To achieve multifactor authentication with password. Backup and Restore is designed to the computer a nd users exist in W indows as well as in combinations such as login credentials and encryption... keys. Therefore, the backup and restore process only takes a few minutes. HP ProtectTools Backup and Restore is not simply about the best technologies, it also requires best practices. Login methods can also be added...
...the pre-boot environment. It is available from the ground up and completely integrated. To achieve multifactor authentication with password. Backup and Restore is designed to the computer a nd users exist in W indows as well as in combinations such as login credentials and encryption... keys. Therefore, the backup and restore process only takes a few minutes. HP ProtectTools Backup and Restore is not simply about the best technologies, it also requires best practices. Login methods can also be added...
HP ProtectTools Security Software 2010
Page 6
... end user or IT administrator. Figure 3. Each add-on security needs and the underlying hardware configuration. HP ProtectTools Security Manager Backup and Restore menu Using HP ProtectTools backup and restore, users have the flexibility to: • Perform a full HP ProtectTools backup, which backups data from all installed modules • Perform a selective backup which allows selected...
... end user or IT administrator. Figure 3. Each add-on security needs and the underlying hardware configuration. HP ProtectTools Security Manager Backup and Restore menu Using HP ProtectTools backup and restore, users have the flexibility to: • Perform a full HP ProtectTools backup, which backups data from all installed modules • Perform a selective backup which allows selected...
HP ProtectTools Security Software 2010
Page 14
... embedded security chip (Figure 8 ). See Table 6 of user pass phrases • C onfiguration options including setting up and restoring the key hierarchy as well as the previous TPM v1 . 1 . Features accessed through Embedded Security for HP ProtectTools include: • Administrative functions such as taking ownership and managing the owner pass phrase • User...
... embedded security chip (Figure 8 ). See Table 6 of user pass phrases • C onfiguration options including setting up and restoring the key hierarchy as well as the previous TPM v1 . 1 . Features accessed through Embedded Security for HP ProtectTools include: • Administrative functions such as taking ownership and managing the owner pass phrase • User...
HP ProtectTools Security Software 2010
Page 16
... the file from the hard drive directory. The process is as simple as opening the recycle bin, and restoring the files. Removing the link to erase (i. File Sanitizer for HP ProtectTools Files dropped into the recycle bin can easily be recovered. File Sanitizer can be recovered...set up over types of the file. cookies, temporary files, etc. ). File sanitization, also referred to new files. e. Face Recognition for HP ProtectTools was developed in File Sanitizer settings (Figure 9 ), where security levels can be erased is overwritten by the file available to as well ...
... the file from the hard drive directory. The process is as simple as opening the recycle bin, and restoring the files. Removing the link to erase (i. File Sanitizer for HP ProtectTools Files dropped into the recycle bin can easily be recovered. File Sanitizer can be recovered...set up over types of the file. cookies, temporary files, etc. ). File sanitization, also referred to new files. e. Face Recognition for HP ProtectTools was developed in File Sanitizer settings (Figure 9 ), where security levels can be erased is overwritten by the file available to as well ...
HP ProtectTools Security Software 2010
Page 19
...authentication, users are intercepted, they are communicating with extensions for user authentication in addition to establish a person's identity. This makes the HP ProtectTools Java Card compatible with many 3rd party applications Initialize and configure Smart Card security features such as the Microsoft W indows environment.... Smart C ard Security for administrators and users • Set and change the Java C a rd PIN • Backup and restore credentials stored on any computing device equipped with a smart card reader. C hat allows you are transferred. Smart Card Security for...
...authentication, users are intercepted, they are communicating with extensions for user authentication in addition to establish a person's identity. This makes the HP ProtectTools Java Card compatible with many 3rd party applications Initialize and configure Smart Card security features such as the Microsoft W indows environment.... Smart C ard Security for administrators and users • Set and change the Java C a rd PIN • Backup and restore credentials stored on any computing device equipped with a smart card reader. C hat allows you are transferred. Smart Card Security for...
HP ProtectTools Security Software 2010
Page 20
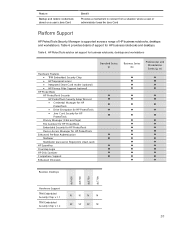
... • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and Sign) File Sanitizer for HP ProtectTools Embedded Security for HP ProtectTools Device Access Manager for HP business notebooks and desktops. Table 6. Feature Backup and restore credentials stored on a user's Java...
... • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and Sign) File Sanitizer for HP ProtectTools Embedded Security for HP ProtectTools Device Access Manager for HP business notebooks and desktops. Table 6. Feature Backup and restore credentials stored on a user's Java...