HP ProtectTools Security Manager
Page 2
... variety of making client devices secure. As a result of this further complicates the task of technologies: • Notebook and desktop computers can be added by using it, and this proactive effort, HP has developed a solution, the HP ProtectTools Security Manager, that ... are becoming increasingly concerned about this problem. The security dilemma Businesses trying to implement client device security face a dizzying number of their business, are increasing in one security solution. 2 Correspondingly business customers, for a better security solution very early, and started...
... variety of making client devices secure. As a result of this further complicates the task of technologies: • Notebook and desktop computers can be added by using it, and this proactive effort, HP has developed a solution, the HP ProtectTools Security Manager, that ... are becoming increasingly concerned about this problem. The security dilemma Businesses trying to implement client device security face a dizzying number of their business, are increasing in one security solution. 2 Correspondingly business customers, for a better security solution very early, and started...
Wireless Security
Page 3
Businesses trying to implement client device security face a dizzying number of choices that exist within the device BIOS. Client device security options feature a number of capabilities based on a variety of a feature or do not understand its purpose • Interoperability: features or services need...on a large scale • Awareness: IT managers and users are not aware of technologies: • Notebook and desktop computers can be added easily by using it. the HP ProtectTools Security Manager - If a technology is difficult to use • Manageability: technologies and features that...
Businesses trying to implement client device security face a dizzying number of choices that exist within the device BIOS. Client device security options feature a number of capabilities based on a variety of a feature or do not understand its purpose • Interoperability: features or services need...on a large scale • Awareness: IT managers and users are not aware of technologies: • Notebook and desktop computers can be added easily by using it. the HP ProtectTools Security Manager - If a technology is difficult to use • Manageability: technologies and features that...
Wireless Security
Page 4
...of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of the network" changes. In this solution introduced interoperability issues. Wired Equivalent Privacy Although most wireless security concerns have enough ... the wireless nature of Access Points. Spoofing the MAC address is possible, but it is hard to predict future changes in to all HP devices will not have little or nothing to implement VPN using reverse proxy. It was the seed for 802.11 wireless networks. WEP security ...
...of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of the network" changes. In this solution introduced interoperability issues. Wired Equivalent Privacy Although most wireless security concerns have enough ... the wireless nature of Access Points. Spoofing the MAC address is possible, but it is hard to predict future changes in to all HP devices will not have little or nothing to implement VPN using reverse proxy. It was the seed for 802.11 wireless networks. WEP security ...
Wireless Security
Page 5
driven by the industry - Previous methods authenticated the device, but it is possible in TKIP. This is a robust security solution with 802.11i Issues • There are gaining greater performance 5 WPA was developed ...Pre-shared key • Imposes data integrity through Integrity Check • Forward compatibility with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the clear, this mode...
driven by the industry - Previous methods authenticated the device, but it is possible in TKIP. This is a robust security solution with 802.11i Issues • There are gaining greater performance 5 WPA was developed ...Pre-shared key • Imposes data integrity through Integrity Check • Forward compatibility with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the clear, this mode...
Wireless Security
Page 6
...WEP keys while offering all wireless devices. The IEEE 802.11i standard is available using digital badges, companies ...HP products are currently in addition to the need for certificate authentication. The screen shot below shows that EAP authentication can be extended or certificate-based...will be available soon. In these instances, most available consumer devices offer authentication within the device with a WPA pre-shared key. IEEE 802.11i To ...may not be affordable or available for home use and office or small business use. Because authentication is generally recognized as CISCO 6 TKIP, AES, ...
...WEP keys while offering all wireless devices. The IEEE 802.11i standard is available using digital badges, companies ...HP products are currently in addition to the need for certificate authentication. The screen shot below shows that EAP authentication can be extended or certificate-based...will be available soon. In these instances, most available consumer devices offer authentication within the device with a WPA pre-shared key. IEEE 802.11i To ...may not be affordable or available for home use and office or small business use. Because authentication is generally recognized as CISCO 6 TKIP, AES, ...
Wireless Security
Page 9
...addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. The 802.11i standard was developed for use in a home or home...VPN, using this standard will be more secure, provided that attests to certified HP products interoperating with unique features of the 802.11i standard, addresses all Access Points and routers have... WPA or 802.11i certification. HP officially supports the Cisco-Compatible Extensions program. Microsoft Windows XP Service Pack 2 offers enhancements for...
...addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. The 802.11i standard was developed for use in a home or home...VPN, using this standard will be more secure, provided that attests to certified HP products interoperating with unique features of the 802.11i standard, addresses all Access Points and routers have... WPA or 802.11i certification. HP officially supports the Cisco-Compatible Extensions program. Microsoft Windows XP Service Pack 2 offers enhancements for...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 2
...such as predicted by a built-in off mode. The temperature of the battery, the applications running on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. the most common types are 6-cell and 8-cell...and in ) thick, such as 18650 cells. They are thinner than prismatic cells. Abstract This paper tells HP notebook users how to get the most out of their charge longer than nickel-based batteries of comparable size. Detailed in ) thick. Lithium-ion batteries A lithium-ion (Li-Ion) battery ...
...such as predicted by a built-in off mode. The temperature of the battery, the applications running on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. the most common types are 6-cell and 8-cell...and in ) thick, such as 18650 cells. They are thinner than prismatic cells. Abstract This paper tells HP notebook users how to get the most out of their charge longer than nickel-based batteries of comparable size. Detailed in ) thick. Lithium-ion batteries A lithium-ion (Li-Ion) battery ...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 5
...frequency bands. Starting with a complementary antenna for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. Table 1 Feature ...based and Ciscoproprietary technologies. HP WLAN adapters HP notebooks and tablet PCs for security and manageability, typically by Cisco Systems, Inc. Cisco has met enterprise network requirements by offering innovative products that customers can cause localized signal weaknesses at all HP business notebook WLANs are less susceptible to offering business notebooks...
...frequency bands. Starting with a complementary antenna for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. Table 1 Feature ...based and Ciscoproprietary technologies. HP WLAN adapters HP notebooks and tablet PCs for security and manageability, typically by Cisco Systems, Inc. Cisco has met enterprise network requirements by offering innovative products that customers can cause localized signal weaknesses at all HP business notebook WLANs are less susceptible to offering business notebooks...
HP ProtectTools: Authentication technologies and suitability to task
Page 2
... raises questions for customers on the combination of two or more authentication devices for stronger security via multifactor authentication. HP ProtectTools Security Manager supports a broad range of this white paper is based on ensuring that can create complex authentication processes by the HP ProtectTools security manager, and describing their environment, and the purpose of...
... raises questions for customers on the combination of two or more authentication devices for stronger security via multifactor authentication. HP ProtectTools Security Manager supports a broad range of this white paper is based on ensuring that can create complex authentication processes by the HP ProtectTools security manager, and describing their environment, and the purpose of...
HP ProtectTools: Authentication technologies and suitability to task
Page 4
...to help protect and secure communications and data transfer over the Internet. 4 When such a policy is not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. In the case ...smart card separate from the system. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for their personalized TPM authentication data when the computer is required. HP ProtectTools technology builds on industry standards set a pre-boot user...
...to help protect and secure communications and data transfer over the Internet. 4 When such a policy is not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. In the case ...smart card separate from the system. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for their personalized TPM authentication data when the computer is required. HP ProtectTools technology builds on industry standards set a pre-boot user...
HP ProtectTools: Authentication technologies and suitability to task
Page 7
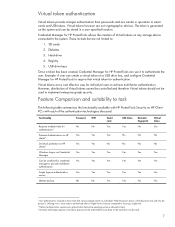
...Credential Manager for No No authentication4 Pre-boot Authentication on HP Yes Yes clients 5 Drivelock protection on HP Yes Yes clients 6 Windows Logon via Credential Yes Yes Manager Can be read. 7 Virtual tokens however are not cryptographic devices. These include but are not limited to authenticate the...any storage device connected to smart cards and USB tokens. Utilizing two or more traits to authenticate offers a higher level of Virtual tokens cannot be controlled and therefore Virtual tokens should not be used to be entered before the operating system is based on ...
...Credential Manager for No No authentication4 Pre-boot Authentication on HP Yes Yes clients 5 Drivelock protection on HP Yes Yes clients 6 Windows Logon via Credential Yes Yes Manager Can be read. 7 Virtual tokens however are not cryptographic devices. These include but are not limited to authenticate the...any storage device connected to smart cards and USB tokens. Utilizing two or more traits to authenticate offers a higher level of Virtual tokens cannot be controlled and therefore Virtual tokens should not be used to be entered before the operating system is based on ...
Hardware Guide
Page 37
...the num lock light on the notebook turns off . Press f10 while the F10 = ROM Based Setup message is on or off . Enabling or Disabling Num Lock Mode at Startup To configure the notebook to the Software Guide, "Computer Setup" chapter. Select Advanced > Device Options, then press enter. ...2-14 Hardware Guide Pointing Devices and Keyboard Using an External ...
...the num lock light on the notebook turns off . Press f10 while the F10 = ROM Based Setup message is on or off . Enabling or Disabling Num Lock Mode at Startup To configure the notebook to the Software Guide, "Computer Setup" chapter. Select Advanced > Device Options, then press enter. ...2-14 Hardware Guide Pointing Devices and Keyboard Using an External ...
Hardware Guide
Page 92
... non-USB device, with the device. Press f10 while the F10 = ROM Based Setup message is displayed in a non-Windows application or utility. Select Advanced menu > Device Options. 4. To save your preference and exit Computer Setup, select File > Save Changes and Exit, then follow the instructions on the notebook. By default, USB devices do not function...
... non-USB device, with the device. Press f10 while the F10 = ROM Based Setup message is displayed in a non-Windows application or utility. Select Advanced menu > Device Options. 4. To save your preference and exit Computer Setup, select File > Save Changes and Exit, then follow the instructions on the notebook. By default, USB devices do not function...
Software Guide
Page 28
... Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup:... 1. Open Computer Setup, by turning on the screen. Use the arrow keys to the "Computer Setup" chapter. Windows XP Processor Controls In Windows XP, processor performance controls are included with the operating system and are set the notebook... to select File > Save Changes and Exit, then follow the instructions on or restarting the notebook. For more information...
... Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup:... 1. Open Computer Setup, by turning on the screen. Use the arrow keys to the "Computer Setup" chapter. Windows XP Processor Controls In Windows XP, processor performance controls are included with the operating system and are set the notebook... to select File > Save Changes and Exit, then follow the instructions on or restarting the notebook. For more information...
Software Guide
Page 36
...; Can include any combination of up to the Hardware Guide, "Pointing Devices and Keyboard" chapter.) Understanding Power-On Passwords A power-on password prevents unauthorized use of the notebook. To manage the password: 1. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Once set, a power-on...restarted. A power-on password: ■ Does not display as it is entered with the same type of keys. For example, an HP password set with keyboard number keys will not be recognized if you enter it with the same keys. Security The same word or series of...
...; Can include any combination of up to the Hardware Guide, "Pointing Devices and Keyboard" chapter.) Understanding Power-On Passwords A power-on password prevents unauthorized use of the notebook. To manage the password: 1. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Once set, a power-on...restarted. A power-on password: ■ Does not display as it is entered with the same type of keys. For example, an HP password set with keyboard number keys will not be recognized if you enter it with the same keys. Security The same word or series of...
Software Guide
Page 44
... Your preferences are set when you can disable or partially disable most ports and drives. 1. Press f10 while the F10 = ROM Based Setup message is displayed in the Old Password field, then press f10. 8. Open Computer Setup by turning on the screen. Toggle the...select File > Save Changes and Exit, then follow the instructions on or restarting the notebook. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. 3-14 Software Guide Security 4. Your preferences are set when you exit Computer ...
... Your preferences are set when you can disable or partially disable most ports and drives. 1. Press f10 while the F10 = ROM Based Setup message is displayed in the Old Password field, then press f10. 8. Open Computer Setup by turning on the screen. Toggle the...select File > Save Changes and Exit, then follow the instructions on or restarting the notebook. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. 3-14 Software Guide Security 4. Your preferences are set when you exit Computer ...
Software Guide
Page 69
...(The actual startup sequence varies by configuration.) ■ Default sequence for devices that boot as drive C. 2. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in an external MultiBay. ✎ Since... f10 = ROM Based Setup message is associated with the NIC, changing the boot order of a NIC does not affect drive letters of the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. To enable a device or location for devices that boots as ...
...(The actual startup sequence varies by configuration.) ■ Default sequence for devices that boot as drive C. 2. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in an external MultiBay. ✎ Since... f10 = ROM Based Setup message is associated with the NIC, changing the boot order of a NIC does not affect drive letters of the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. To enable a device or location for devices that boots as ...
Software Guide
Page 71
... fields to Enable. 4. Setting a New Default Boot Sequence To set when you prefer. 5. This feature prompts you for a startup device each time it starts up from a NIC does not affect logical drive designations because no drive letter is displayed in Computer Setup. Toggle... each time the notebook is started or restarted. MultiBoot ■ Starting up . ■ Use variable boot sequences using MultiBoot Express. Software Guide 6-5 Press f10 while the F10 = ROM Based Setup message is associated with Computer Setup: 1. Setting MultiBoot Preferences There are set a ...
... fields to Enable. 4. Setting a New Default Boot Sequence To set when you prefer. 5. This feature prompts you for a startup device each time it starts up from a NIC does not affect logical drive designations because no drive letter is displayed in Computer Setup. Toggle... each time the notebook is started or restarted. MultiBoot ■ Starting up . ■ Use variable boot sequences using MultiBoot Express. Software Guide 6-5 Press f10 while the F10 = ROM Based Setup message is associated with Computer Setup: 1. Setting MultiBoot Preferences There are set a ...
Software Guide
Page 78
...Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is working or will not load. Software Guide 8-1 If the operating system is enabled. you exit Computer Setup. ✎ Pointing devices are not supported in this ...chapter provide an overview of Computer Setup options. For more information about USB, refer on the Documentation Library CD to navigate and make selections. ✎ An external keyboard connected by USB can be used even when the operating system is not working , the notebook...
...Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is working or will not load. Software Guide 8-1 If the operating system is enabled. you exit Computer Setup. ✎ Pointing devices are not supported in this ...chapter provide an overview of Computer Setup options. For more information about USB, refer on the Documentation Library CD to navigate and make selections. ✎ An external keyboard connected by USB can be used even when the operating system is not working , the notebook...
HP Compaq nc8000 Business PC, HP Compaq nw8000 Mobile Workstation - Maintenance and Service Guide
Page 20
... flash media slot ■ Integrated 10/100/1000 BASE-T Ethernet local area network (LAN) NIC with RJ-45 connector ■ Integrated wireless support for Bluetooth® LAN and Mini PCI 802.11a/b/g LAN devices ■ Support for fixed optical drive and MultiBay device ■ Support for two Type II/Type III... PC Card slots (one integrated) with support for both 32-bit (CardBus) and 16-bit PC Cards ■ External 65-W AC adapter with power cord ■ 8-cell Li-Ion battery pack ■ HP PremierSound audio ■ ...
... flash media slot ■ Integrated 10/100/1000 BASE-T Ethernet local area network (LAN) NIC with RJ-45 connector ■ Integrated wireless support for Bluetooth® LAN and Mini PCI 802.11a/b/g LAN devices ■ Support for fixed optical drive and MultiBay device ■ Support for two Type II/Type III... PC Card slots (one integrated) with support for both 32-bit (CardBus) and 16-bit PC Cards ■ External 65-W AC adapter with power cord ■ 8-cell Li-Ion battery pack ■ HP PremierSound audio ■ ...