Bluetooth Wireless Technology Basics
Page 1
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth Wireless Technology Basics
Page 2
...What does this mean for establishing a BWT connection, and provides information about HP products that simultaneously connects several devices in a wireless personal area network (WPAN). Exchange electronic business cards with everyone in Sweden. With BWT, you time by automatically synchronizing ...enabled products are Ericsson, Intel, IBM, Nokia, and Toshiba. Introduction Bluetooth wireless technology (BWT) was to eliminate the need for proprietary cable connections between devices such as notebook PCs, handheld PCs, personal digital assistants (PDAs), cameras, and printers....
...What does this mean for establishing a BWT connection, and provides information about HP products that simultaneously connects several devices in a wireless personal area network (WPAN). Exchange electronic business cards with everyone in Sweden. With BWT, you time by automatically synchronizing ...enabled products are Ericsson, Intel, IBM, Nokia, and Toshiba. Introduction Bluetooth wireless technology (BWT) was to eliminate the need for proprietary cable connections between devices such as notebook PCs, handheld PCs, personal digital assistants (PDAs), cameras, and printers....
Bluetooth Wireless Technology Basics
Page 3
... classes of BWT radio devices, each with a BWT network at one frequency, and then they hop to another packet. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios. This means that if another frequency. BWT-enabled devices use the ISM band. With frequency ...2.483 GHz. The ISM band ranges between frequencies up to minimize eavesdropping and interference from other 2.4-GHz devices. How Bluetooth wireless technology works BWT-enabled devices operate in the ISM band as a 2.4-GHz cordless phone, interferes with a different maximum range: Class 1 (100 ...
... classes of BWT radio devices, each with a BWT network at one frequency, and then they hop to another packet. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios. This means that if another frequency. BWT-enabled devices use the ISM band. With frequency ...2.483 GHz. The ISM band ranges between frequencies up to minimize eavesdropping and interference from other 2.4-GHz devices. How Bluetooth wireless technology works BWT-enabled devices operate in the ISM band as a 2.4-GHz cordless phone, interferes with a different maximum range: Class 1 (100 ...
Bluetooth Wireless Technology Basics
Page 7
... and BWT functionality is off, turn on the wireless device for installation, and then select Next. 4. Install the BWT software The required BWT software comes preloaded on your notebook. Select the check box next to Bluetooth by hp to load the BWT driver. When the Software...connecting to other BWT-enabled devices, refer to restart the computer. The following 3 steps activate your notebook user documentation if you turn it by pressing the wireless button on HP notebook PCs; Select Finish to complete the installation and to the Documentation Library Bluetooth CD that came in...
... and BWT functionality is off, turn on the wireless device for installation, and then select Next. 4. Install the BWT software The required BWT software comes preloaded on your notebook. Select the check box next to Bluetooth by hp to load the BWT driver. When the Software...connecting to other BWT-enabled devices, refer to restart the computer. The following 3 steps activate your notebook user documentation if you turn it by pressing the wireless button on HP notebook PCs; Select Finish to complete the installation and to the Documentation Library Bluetooth CD that came in...
Bluetooth Wireless Technology Basics
Page 8
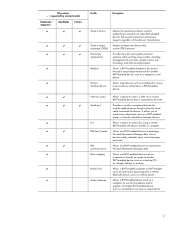
...the two devices match, they report a list of HP BWT offerings and to the HP wireless product portfolio. Detailed instructions on the matching profiles. Refer to another BWT-enabled device. 8 Table 2 describes some models of your notebook, select Start > My Programs > My Bluetooth Places ...to another BWT-enabled device. You can be used to use a modem that are shipped with integrated BWT. Allows a device to send images, text, business cards, and calendar notes. The ...
...the two devices match, they report a list of HP BWT offerings and to the HP wireless product portfolio. Detailed instructions on the matching profiles. Refer to another BWT-enabled device. 8 Table 2 describes some models of your notebook, select Start > My Programs > My Bluetooth Places ...to another BWT-enabled device. You can be used to use a modem that are shipped with integrated BWT. Allows a device to send images, text, business cards, and calendar notes. The ...
Bluetooth Wireless Technology Basics
Page 9
HP products D = supported by applications as though a physical serial cable connected the devices. Provides the same print quality and print speed as business...9 print to a BWT-enabled device. Allows a BWT-enabled headset to other BWT-enabled devices that can be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D ...a fax using a cable, including management of the devices' manufacturer. Provides a wireless connection that accept connections and service requests regardless of print jobs, greater control over...
HP products D = supported by applications as though a physical serial cable connected the devices. Provides the same print quality and print speed as business...9 print to a BWT-enabled device. Allows a BWT-enabled headset to other BWT-enabled devices that can be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D ...a fax using a cable, including management of the devices' manufacturer. Provides a wireless connection that accept connections and service requests regardless of print jobs, greater control over...
Bluetooth Wireless Technology Basics
Page 10
... and store a common link key so that automatically adjusts the seat and mirrors as you do not need to a car that you approach it, Bluetooth wireless technology will pair automatically the first time they connect (a password, or passkey, must be deciphered by right-clicking the device icon in My Bluetooth Places...
... and store a common link key so that automatically adjusts the seat and mirrors as you do not need to a car that you approach it, Bluetooth wireless technology will pair automatically the first time they connect (a password, or passkey, must be deciphered by right-clicking the device icon in My Bluetooth Places...
Bluetooth Wireless Technology Basics
Page 11
...hp.com/products/wireless/wpan/files/ WhitePaper_BluetoothTechnologyOverview-QA.pdf HP Bluetooth printer card http://h10010.www1.hp.com/wwpcJAVA/offweb/vac/us/product_pdfs/BluetoothPrinterCard.pdf Compatibility matrix for Bluetooth wireless technology http://h18000.www1.hp.com/products/wireless/wpan/btcompmatrix.html HP wireless product portfolio http://www.hp.com/products/wireless...; Copyright 2004 Hewlett-Packard Development Company, L.P. Nothing herein should be liable for HP products and services are set forth in the express warranty statements accompanying such products and services.
...hp.com/products/wireless/wpan/files/ WhitePaper_BluetoothTechnologyOverview-QA.pdf HP Bluetooth printer card http://h10010.www1.hp.com/wwpcJAVA/offweb/vac/us/product_pdfs/BluetoothPrinterCard.pdf Compatibility matrix for Bluetooth wireless technology http://h18000.www1.hp.com/products/wireless/wpan/btcompmatrix.html HP wireless product portfolio http://www.hp.com/products/wireless...; Copyright 2004 Hewlett-Packard Development Company, L.P. Nothing herein should be liable for HP products and services are set forth in the express warranty statements accompanying such products and services.
Wireless Security
Page 1
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Wireless Security
Page 2
... available, but also to help ensure that client devices themselves do with using wireless connectivity, but may be supported using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. the fact that ...authentication servers must be addressed holistically, we discuss the tools developed for wireless security, it is to provide a mechanism to ensure data privacy and integrity. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of the solution, but with , ...
... available, but also to help ensure that client devices themselves do with using wireless connectivity, but may be supported using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. the fact that ...authentication servers must be addressed holistically, we discuss the tools developed for wireless security, it is to provide a mechanism to ensure data privacy and integrity. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of the solution, but with , ...
Wireless Security
Page 3
...of capabilities based on a variety of technologies: • Notebook and desktop computers can be configured with other elements of ...become more suitable for enterprise deployment. that not only meets mobility and wireless requirements, but is available on a range of HP commercial products. • Biometrics are expected to boot • Device...devices secure. These challenges include: • Usability: technologies and features that exist within the device BIOS. Businesses trying to assist the customer in -one security solution. 3 In addition, many client devices include security ...
...of capabilities based on a variety of technologies: • Notebook and desktop computers can be configured with other elements of ...become more suitable for enterprise deployment. that not only meets mobility and wireless requirements, but is available on a range of HP commercial products. • Biometrics are expected to boot • Device...devices secure. These challenges include: • Usability: technologies and features that exist within the device BIOS. Businesses trying to assist the customer in -one security solution. 3 In addition, many client devices include security ...
Wireless Security
Page 4
... can be summarized in WEP vulnerability. In fact, all Access Points and tack them. 4 Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for WEP Vulnerability Although VPN provides adequate security, there may be accessed using secure ID to ...if some intranet data is needed as the WEP vulnerability issues persisted (for more secure Dynamic WEP key CISCO Hewlett Packard Microsoft HP Wireless Internet Access Solution: Provides full Internet access for on what is available today, as they are emerging and IP networks are ...
... can be summarized in WEP vulnerability. In fact, all Access Points and tack them. 4 Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for WEP Vulnerability Although VPN provides adequate security, there may be accessed using secure ID to ...if some intranet data is needed as the WEP vulnerability issues persisted (for more secure Dynamic WEP key CISCO Hewlett Packard Microsoft HP Wireless Internet Access Solution: Provides full Internet access for on what is available today, as they are emerging and IP networks are ...
Wireless Security
Page 5
... features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are gaining greater performance 5 This is forward compatible with 802.11i Issues • There are still potential encryption weaknesses in TKIP for better key...
... features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are gaining greater performance 5 This is forward compatible with 802.11i Issues • There are still potential encryption weaknesses in TKIP for better key...
Wireless Security
Page 6
... within the device with a WPA pre-shared key. The group was approved and ratified June 25, 2004, for wireless LANs. This makes a great solution for certificate authentication. The IEEE 802.11i standard was asked to produce a detailed...TKIP, AES, and others. Because authentication is generally recognized as CISCO 6 "I"- HP products are currently in addition to the need for home use and office or small business use. IEEE 802.11i To address WEP security issues, IEEE formed a Task ...the future benchmark for home users. IEEE 802.11i products are focused on HP notebook PCs.
... within the device with a WPA pre-shared key. The group was approved and ratified June 25, 2004, for wireless LANs. This makes a great solution for certificate authentication. The IEEE 802.11i standard was asked to produce a detailed...TKIP, AES, and others. Because authentication is generally recognized as CISCO 6 "I"- HP products are currently in addition to the need for home use and office or small business use. IEEE 802.11i To address WEP security issues, IEEE formed a Task ...the future benchmark for home users. IEEE 802.11i products are focused on HP notebook PCs.
Wireless Security
Page 7
For more robust security to data from heterogeneous networks. The HP solution is required, in order to implement AES. •...pervasive access to mail, database and web servers. The risk grew as a certification of 802.11i ) * HP Notebooks with WPA2 Certification are available Emerging Mobile Applications The rise of Advanced Encryption Standard (AES) • Supports roaming... aspect of using this complicated problem since 1980, and can provide more details please visit http://www.hp.com/products/security Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46 In addition...
For more robust security to data from heterogeneous networks. The HP solution is required, in order to implement AES. •...pervasive access to mail, database and web servers. The risk grew as a certification of 802.11i ) * HP Notebooks with WPA2 Certification are available Emerging Mobile Applications The rise of Advanced Encryption Standard (AES) • Supports roaming... aspect of using this complicated problem since 1980, and can provide more details please visit http://www.hp.com/products/security Key fingerprint = AF19 FA27 2F94 998D FDB5 DE3D F8B5 06E4 A169 4E46 In addition...
Wireless Security
Page 8
...Virtual Private Network vs. use of the needed security - Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. Reverse Proxy Most people are using http, https or http with AES, 3DES or other encryption to the back-...their corporate networks. This can add the needed proxy code to full PIM using HTTPS. and many software solutions - Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. Reverse proxy passes http traffic back and forth across the firewall from...
...Virtual Private Network vs. use of the needed security - Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. Reverse Proxy Most people are using http, https or http with AES, 3DES or other encryption to the back-...their corporate networks. This can add the needed proxy code to full PIM using HTTPS. and many software solutions - Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. Reverse proxy passes http traffic back and forth across the firewall from...
Wireless Security
Page 9
...available shortly. Products designed to protecting your data and network. Over the past eight years, wireless security has undergone major changes to WPA, 802.11i - HP officially supports the Cisco-Compatible Extensions program. This is no need for an authentication server. ...wire-line or wireless. The 802.11i standard was developed for wireless security that attests to certified HP products interoperating with unique features of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed...
...available shortly. Products designed to protecting your data and network. Over the past eight years, wireless security has undergone major changes to WPA, 802.11i - HP officially supports the Cisco-Compatible Extensions program. This is no need for an authentication server. ...wire-line or wireless. The 802.11i standard was developed for wireless security that attests to certified HP products interoperating with unique features of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed...
Wireless Security
Page 10
... be construed as constituting an additional warranty. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. For more secure...
... be construed as constituting an additional warranty. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. For more secure...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 3
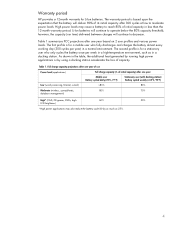
... approximately equal to deliver approximately 80% of the battery capacity (Ah) and the battery voltage (V). Battery energy, expressed in wired or wireless modes. Consequently, the user experiences reduced computer run time. Figure 2. Battery cycle life Battery cycle life is called full charge capacity (FCC... movies drains the battery faster and decreases its useful life; Figure 1. FCC is influenced by the typical discharge load on the notebook and by its power management settings. Estimating the cycle life of the battery depends on the air temperature as well as the ...
... approximately equal to deliver approximately 80% of the battery capacity (Ah) and the battery voltage (V). Battery energy, expressed in wired or wireless modes. Consequently, the user experiences reduced computer run time. Figure 2. Battery cycle life Battery cycle life is called full charge capacity (FCC... movies drains the battery faster and decreases its useful life; Figure 1. FCC is influenced by the typical discharge load on the notebook and by its power management settings. Estimating the cycle life of the battery depends on the air temperature as well as the ...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 4
...ºF) Stationary user (with docking station) Battery cycled weekly (>35ºC, 95ºF) Low (word processing, Internet, e-mail) >80% 80% Moderate (wireless, spreadsheets, database management) 80% 70% High* (CAD, 3D games, DVDs, high LCD brightness) 60% *High power applications may cause a battery to ...decrease. Table 1. Warranty period HP provides a 12-month warranty for a mobile user who only cycles the battery once per year) in a docking station. As shown in the ...
...ºF) Stationary user (with docking station) Battery cycled weekly (>35ºC, 95ºF) Low (word processing, Internet, e-mail) >80% 80% Moderate (wireless, spreadsheets, database management) 80% 70% High* (CAD, 3D games, DVDs, high LCD brightness) 60% *High power applications may cause a battery to ...decrease. Table 1. Warranty period HP provides a 12-month warranty for a mobile user who only cycles the battery once per year) in a docking station. As shown in the ...