Bluetooth Wireless Technology Basics
Page 8
...the printer software on , or transfer files from a BWT-enabled device to send images, text, business cards, and calendar notes. Also, visit http://www.hp.com/products/wireless/ for the two devices match, they can connect and interoperate based on a cell phone can change the BWT settings. Using this ... and change the default BWT settings and set the level of discoverability of the BWT profiles built into HP notebook PCs, iPAQ Pocket PCs, and printers. Selecting BWT device profiles Profiles are services that has 802.11 technology, Bluetooth, or both of the profiles for updates to...
...the printer software on , or transfer files from a BWT-enabled device to send images, text, business cards, and calendar notes. Also, visit http://www.hp.com/products/wireless/ for the two devices match, they can connect and interoperate based on a cell phone can change the BWT settings. Using this ... and change the default BWT settings and set the level of discoverability of the BWT profiles built into HP notebook PCs, iPAQ Pocket PCs, and printers. Selecting BWT device profiles Profiles are services that has 802.11 technology, Bluetooth, or both of the profiles for updates to...
HP ProtectTools Security Manager
Page 2
...technologies: • Notebook and desktop computers can be used . The security dilemma Businesses trying to implement client device security face a dizzying number of choices that may not always work well together. Client device security options feature a number of capabilities based on software modules... to authenticate a user before allowing the system to boot • Device configuration lock down • Remote management capabilities While these security features increasingly rely on a range of HP products • Biometrics and RFID (Radio Frequency Identification) are keeping ...
...technologies: • Notebook and desktop computers can be used . The security dilemma Businesses trying to implement client device security face a dizzying number of choices that may not always work well together. Client device security options feature a number of capabilities based on software modules... to authenticate a user before allowing the system to boot • Device configuration lock down • Remote management capabilities While these security features increasingly rely on a range of HP products • Biometrics and RFID (Radio Frequency Identification) are keeping ...
Wireless Security
Page 3
...and features become available. Businesses trying to implement client device security face a dizzying number of technologies: • Notebook and desktop computers can be configured with other elements of this issue. Client device security options feature a number of capabilities based on a variety of...need for enterprise deployment. or TPM - This architecture gives users an easy-to addressing this proactive effort, HP has developed a solution - the HP ProtectTools Security Manager - In addition, security solutions can easily grow to handle new threats and offer new technologies...
...and features become available. Businesses trying to implement client device security face a dizzying number of technologies: • Notebook and desktop computers can be configured with other elements of this issue. Client device security options feature a number of capabilities based on a variety of...need for enterprise deployment. or TPM - This architecture gives users an easy-to addressing this proactive effort, HP has developed a solution - the HP ProtectTools Security Manager - In addition, security solutions can easily grow to handle new threats and offer new technologies...
Wireless Security
Page 4
...hold 30 MAC addresses, which requires you have to implement VPN using reverse proxy. Because you to feed in to all HP devices will not have taken steps to address these devices support TKIP and AES Encryption. Enhancements of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB... US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of data integrity • Poor key management and •...
...hold 30 MAC addresses, which requires you have to implement VPN using reverse proxy. Because you to feed in to all HP devices will not have taken steps to address these devices support TKIP and AES Encryption. Enhancements of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB... US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of data integrity • Poor key management and •...
Wireless Security
Page 5
is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are.... driven by the industry - This solution targets all known WEP vulnerabilities and is not a valid security measure. Previous methods authenticated the device, but it is possible in TKIP for better key management • Supports mutual authentication for stronger network access control. However, with enhancement...
is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are.... driven by the industry - This solution targets all known WEP vulnerabilities and is not a valid security measure. Previous methods authenticated the device, but it is possible in TKIP for better key management • Supports mutual authentication for stronger network access control. However, with enhancement...
Wireless Security
Page 6
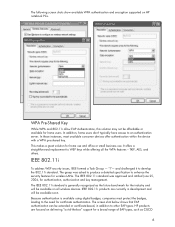
... are currently in addition to the need for home use and office or small business use. The following screen shots show available WPA authentication and encryption supported on HP notebook PCs. In addition, home users don't typically have access to develop the 802.11i standard. The group ...802.11i standard was asked to produce a detailed specification to WEP keys while offering all wireless devices. The screen shot below shows that EAP authentication can be extended or certificate-based, in development and will be available on delivering "out-of EAP types, such as the future...
... are currently in addition to the need for home use and office or small business use. The following screen shots show available WPA authentication and encryption supported on HP notebook PCs. In addition, home users don't typically have access to develop the 802.11i standard. The group ...802.11i standard was asked to produce a detailed specification to WEP keys while offering all wireless devices. The screen shot below shows that EAP authentication can be extended or certificate-based, in development and will be available on delivering "out-of EAP types, such as the future...
Wireless Security
Page 9
...is no need for an authentication server. In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. With the 802.11 standard, the authentication server can be more secure, provided that address many wireless concerns related to ...will be certified by the Wi-Fi Alliance. This is a formal certification program that attests to certified HP products interoperating with wireless security is a subset of the Access Point. HP officially supports the Cisco-Compatible Extensions program. The IEEE 802.11 Group, the Wi-Fi Alliance and...
...is no need for an authentication server. In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. With the 802.11 standard, the authentication server can be more secure, provided that address many wireless concerns related to ...will be certified by the Wi-Fi Alliance. This is a formal certification program that attests to certified HP products interoperating with wireless security is a subset of the Access Point. HP officially supports the Cisco-Compatible Extensions program. The IEEE 802.11 Group, the Wi-Fi Alliance and...
Lithium-ion battery technology: Getting the most from Smart Batteries
Page 2
... factors impact battery run time varies depending on how and where the notebook is made of multiple cells connected in series and in parallel based on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. Also, ...is fully charged, current flow to the battery is not simple. Abstract This paper tells HP notebook users how to get the most out of their charge longer than 10 mm (0.4 in) thick. HP notebooks use 3 different types of Li-Ion batteries, and should be charged before they are fully...
... factors impact battery run time varies depending on how and where the notebook is made of multiple cells connected in series and in parallel based on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. Also, ...is fully charged, current flow to the battery is not simple. Abstract This paper tells HP notebook users how to get the most out of their charge longer than 10 mm (0.4 in) thick. HP notebooks use 3 different types of Li-Ion batteries, and should be charged before they are fully...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 5
...of WLAN performance is oriented. An in every notebook that address needs for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. Cisco has...based solutions during the development process, HP is tested in the network coverage area. First the design is validated and tuned in the laboratory, and then it is able to provide leading performance wireless LAN adapters at either the 5 GHz or 2.4 GHz frequency bands. Performance HP works to optimize WLAN performance at all HP business notebook...
...of WLAN performance is oriented. An in every notebook that address needs for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. Cisco has...based solutions during the development process, HP is tested in the network coverage area. First the design is validated and tuned in the laboratory, and then it is able to provide leading performance wireless LAN adapters at either the 5 GHz or 2.4 GHz frequency bands. Performance HP works to optimize WLAN performance at all HP business notebook...
HP Compaq nc6000 Notebook PC - Maintenance and Service Guide
Page 34
... when your operating system is not necessary to configure a device connected to a USB connector on or restart the notebook. Using Computer Setup Information and settings in Microsoft Windows.... 2-2 Maintenance and Service Guide Turn on the notebook or to the Computer Setup menu, press esc. 2. Press F10 while the F10 = ROM-Based Setup message is displayed in Windows XP Professional ... device configuration problem in the lower left corner of the screen. ❏ To change the language, press F2. ❏ To view navigation information, press F1. ❏ To return to an optional HP ...
... when your operating system is not necessary to configure a device connected to a USB connector on or restart the notebook. Using Computer Setup Information and settings in Microsoft Windows.... 2-2 Maintenance and Service Guide Turn on the notebook or to the Computer Setup menu, press esc. 2. Press F10 while the F10 = ROM-Based Setup message is displayed in Windows XP Professional ... device configuration problem in the lower left corner of the screen. ❏ To change the language, press F2. ❏ To view navigation information, press F1. ❏ To return to an optional HP ...
HP Compaq nc6000 Notebook PC - Maintenance and Service Guide
Page 69
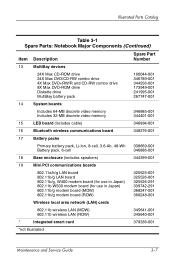
Illustrated Parts Catalog Table 3-1 Spare Parts: Notebook Major Components (Continued) Item Description Spare Part Number 13 MultiBay devices 24X Max CD-ROM drive 24X Max DVD/CD-RW combo drive 4X Max DVD+RW/R and CD-RW combo drive 8X Max DVD-ROM ... wireless communications board 348276-001 17 Battery packs Primary battery pack, Li-Ion, 8-cell, 3.6-Ah, 48-Wh Battery pack, 6-cell 338669-001 346886-001 18 Base enclosure (includes speakers) 344399-001 19 Mini PCI communications boards 802.11a/b/g LAN board 802.11b/g LAN board 802.11b/g, W400 modem board (for use...
Illustrated Parts Catalog Table 3-1 Spare Parts: Notebook Major Components (Continued) Item Description Spare Part Number 13 MultiBay devices 24X Max CD-ROM drive 24X Max DVD/CD-RW combo drive 4X Max DVD+RW/R and CD-RW combo drive 8X Max DVD-ROM ... wireless communications board 348276-001 17 Battery packs Primary battery pack, Li-Ion, 8-cell, 3.6-Ah, 48-Wh Battery pack, 6-cell 338669-001 346886-001 18 Base enclosure (includes speakers) 344399-001 19 Mini PCI communications boards 802.11a/b/g LAN board 802.11b/g LAN board 802.11b/g, W400 modem board (for use...
Hardware Guide
Page 36
...an external keypad is turned off, the num lock light on the notebook turns off . Enabling or Disabling Num Lock Mode at Startup To configure the notebook to start up with the external keypad enabled: 1. Pointing Devices and Keyboard Using an External Keypad Most keys on most external keypads ... the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. Press f10 while the F10 = ROM Based Setup message is connected, the embedded numeric keypad cannot be turned on. To set this preference in num lock mode, you work, press the num...
...an external keypad is turned off, the num lock light on the notebook turns off . Enabling or Disabling Num Lock Mode at Startup To configure the notebook to start up with the external keypad enabled: 1. Pointing Devices and Keyboard Using an External Keypad Most keys on most external keypads ... the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. Press f10 while the F10 = ROM Based Setup message is connected, the embedded numeric keypad cannot be turned on. To set this preference in num lock mode, you work, press the num...
Hardware Guide
Page 89
...Save Changes and Exit, then follow the instructions on or restart the notebook. 2. Turn on the screen. 7-4 Hardware Guide To enable USB legacy support: 1. Select Advanced menu > Device Options. 4. Select Enable USB legacy support. 5. External Devices Enabling USB Legacy Support You must enable USB legacy support to: ...connected to a USB connector on the notebook during startup or in the lower left corner of the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. Press f10 while the F10 = ROM Based Setup message is displayed in a non...
...Save Changes and Exit, then follow the instructions on or restart the notebook. 2. Turn on the screen. 7-4 Hardware Guide To enable USB legacy support: 1. Select Advanced menu > Device Options. 4. Select Enable USB legacy support. 5. External Devices Enabling USB Legacy Support You must enable USB legacy support to: ...connected to a USB connector on the notebook during startup or in the lower left corner of the screen. ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. Press f10 while the F10 = ROM Based Setup message is displayed in a non...
Software Guide
Page 43
... Computer Setup and take effect when the notebook restarts. 3-14 Software Guide Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is displayed in the lower ... 1. Select the Security menu > Device Security, then enter your preferences, select File > Save Changes and Exit, then follow the instructions on (not restarting) the notebook. To save your preferences, press f10. 4. Press f10 while the F10 = ROM Based Setup message is displayed in the ...
... Computer Setup and take effect when the notebook restarts. 3-14 Software Guide Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is displayed in the lower ... 1. Select the Security menu > Device Security, then enter your preferences, select File > Save Changes and Exit, then follow the instructions on (not restarting) the notebook. To save your preferences, press f10. 4. Press f10 while the F10 = ROM Based Setup message is displayed in the ...
Software Guide
Page 68
.... ✎ Since no drive letter is displayed in the lower left of the other devices. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in MultiBoot: 1. Optical drive in a Port Replicator MultiBay... or in an external MultiBay that contains a disc that boots as drive C. 2. Press f10 while the F10 = ROM Based Setup ...
.... ✎ Since no drive letter is displayed in the lower left of the other devices. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in MultiBoot: 1. Optical drive in a Port Replicator MultiBay... or in an external MultiBay that contains a disc that boots as drive C. 2. Press f10 while the F10 = ROM Based Setup ...
Software Guide
Page 70
... Save Changes and Exit, then follow the instructions on or restarting the notebook. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Your preferences are treated like external USB devices in the boot sequence and must be enabled in the lower left of ... designations because no drive letter is started or restarted. Software Guide 6-5 This feature prompts you exit Computer Setup and take effect when the notebook restarts. Toggle the Boot Order fields to select Advanced > Boot Options, then press enter. 3. Open Computer Setup by turning on the ...
... Save Changes and Exit, then follow the instructions on or restarting the notebook. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Your preferences are treated like external USB devices in the boot sequence and must be enabled in the lower left of ... designations because no drive letter is started or restarted. Software Guide 6-5 This feature prompts you exit Computer Setup and take effect when the notebook restarts. Toggle the Boot Order fields to select Advanced > Boot Options, then press enter. 3. Open Computer Setup by turning on the ...
Software Guide
Page 76
...Setup Computer Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is working or will not load. The menu tables later in Computer Setup; you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide .... ✎ An external keyboard connected by USB can be used even when the operating system is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. If the operating system is enabled. Software Guide 8-1
...Setup Computer Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is working or will not load. The menu tables later in Computer Setup; you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide .... ✎ An external keyboard connected by USB can be used even when the operating system is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. If the operating system is enabled. Software Guide 8-1
HP ProtectTools: Authentication technologies and suitability to task
Page 2
... should have access to information. This breadth of support for a given environment by listing the authentication devices currently supported by the HP ProtectTools security manager, and describing their environment, and the purpose of this white paper is based on three traits that customers can also gain access to help answer those questions. 2 Credential...
... should have access to information. This breadth of support for a given environment by listing the authentication devices currently supported by the HP ProtectTools security manager, and describing their environment, and the purpose of this white paper is based on three traits that customers can also gain access to help answer those questions. 2 Credential...
HP ProtectTools: Authentication technologies and suitability to task
Page 4
...not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for their personalized TPM... security chip embedded in possession of smart cards, authentication requires that the user be costly Easier to the device authentication function. HP also utilizes TPM authentication to enhance Drivelock security, by keeping the smart card separate from the system. In...
...not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for their personalized TPM... security chip embedded in possession of smart cards, authentication requires that the user be costly Easier to the device authentication function. HP also utilizes TPM authentication to enhance Drivelock security, by keeping the smart card separate from the system. In...
HP ProtectTools: Authentication technologies and suitability to task
Page 7
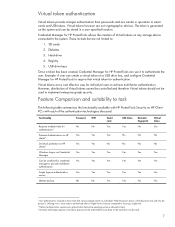
...No No Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes No Yes 4 User authentication is based on any data on HP Client PC's with HP ProtectTools Security on the hard drive can be uniquely tied to be stored in a user specified location. Functionality...smart cards and USB tokens. Feature Comparison and suitability to authenticate the user. Virtual tokens however are not cryptographic devices. Registry 5. Virtual tokens are a cost effective way for HP ProtectTools can be entered before the operating system is allowed to load. 6 Drivelock technology requires a hard drive...
...No No Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes Yes No Yes 4 User authentication is based on any data on HP Client PC's with HP ProtectTools Security on the hard drive can be uniquely tied to be stored in a user specified location. Functionality...smart cards and USB tokens. Feature Comparison and suitability to authenticate the user. Virtual tokens however are not cryptographic devices. Registry 5. Virtual tokens are a cost effective way for HP ProtectTools can be entered before the operating system is allowed to load. 6 Drivelock technology requires a hard drive...