Bluetooth Wireless Technology Basics
Page 1
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth Wireless Technology Basics
Page 2
... and Toshiba. This paper provides an overview of BWT, describes the requirements for proprietary cabling between devices such as PDAs and notebook PCs. Although infrared communication existed at the time, it possible to develop the Bluetooth Specification IEEE 802.15. Therefore, Ericsson chose...the need for establishing a BWT connection, and provides information about HP products that devices from ? The specification standardized the development of BWT was developed in 1994 at your office, don't fret. Exchange electronic business cards with a few taps on your PDA. More than ...
... and Toshiba. This paper provides an overview of BWT, describes the requirements for proprietary cabling between devices such as PDAs and notebook PCs. Although infrared communication existed at the time, it possible to develop the Bluetooth Specification IEEE 802.15. Therefore, Ericsson chose...the need for establishing a BWT connection, and provides information about HP products that devices from ? The specification standardized the development of BWT was developed in 1994 at your office, don't fret. Exchange electronic business cards with a few taps on your PDA. More than ...
Bluetooth Wireless Technology Basics
Page 3
... other networks that use the ISM band. Class 2 (50 meters); Figure 1. How Bluetooth wireless technology works BWT-enabled devices operate in Figure 1. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios. With frequency hopping, the data is transmitted. There are three classes of a second until all the data is divided...
... other networks that use the ISM band. Class 2 (50 meters); Figure 1. How Bluetooth wireless technology works BWT-enabled devices operate in Figure 1. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios. With frequency hopping, the data is transmitted. There are three classes of a second until all the data is divided...
Bluetooth Wireless Technology Basics
Page 6
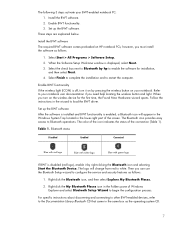
...in secure mode, you are explained below. Then, you decide to activate BWT functionality on each device. Activating BWT devices Notebook PCs If you must pair the device with another BWT-enabled device before they can select the services (profiles) that ...window (Figure 4). Select the Device Manager button. 4. Figure 4. Confirming Bluetooth capability via Device Manager 6 These requirements are not sure whether your notebook PC, iPAQ Pocket PC, printer, and cellular phone. Then select Control Panel > Performance and Maintenance > System > Hardware tab. 3. Establishing BWT...
...in secure mode, you are explained below. Then, you decide to activate BWT functionality on each device. Activating BWT devices Notebook PCs If you must pair the device with another BWT-enabled device before they can select the services (profiles) that ...window (Figure 4). Select the Device Manager button. 4. Figure 4. Confirming Bluetooth capability via Device Manager 6 These requirements are not sure whether your notebook PC, iPAQ Pocket PC, printer, and cellular phone. Then select Control Panel > Performance and Maintenance > System > Hardware tab. 3. Establishing BWT...
Bluetooth Wireless Technology Basics
Page 7
...check box next to Bluetooth by pressing the wireless button on by hp to configure the service and security features as follows: 1. Enable BWT functionality If the wireless light (ICON) is disabled (red logo), enable it on your notebook. Table 1. Install the BWT software. 2. however, you can ...1. Bluetooth status Disabled Enabled Connected Blue with red logo Blue with white logo Blue with green logo If BWT is off, turn on HP notebook PCs; Then you must install the software as the operating system CD. 7 Right-click the My Bluetooth Places icon in the lower-right...
...check box next to Bluetooth by pressing the wireless button on by hp to configure the service and security features as follows: 1. Enable BWT functionality If the wireless light (ICON) is disabled (red logo), enable it on your notebook. Table 1. Install the BWT software. 2. however, you can ...1. Bluetooth status Disabled Enabled Connected Blue with red logo Blue with white logo Blue with green logo If BWT is off, turn on HP notebook PCs; Then you must install the software as the operating system CD. 7 Right-click the My Bluetooth Places icon in the lower-right...
Bluetooth Wireless Technology Basics
Page 8
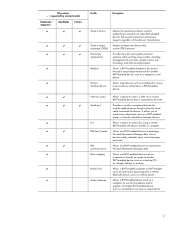
... to browse a file system on, create or delete files/folders on the matching profiles. Bluetooth wireless technology profiles supported by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D Profile Description Basic printing Dial-up networking File transfer Enables simpler printing from /... the Today screen to activate BWT functionality, to create BWT connections, or to send images, text, business cards, and calendar notes. Table 2. HP products D = supported by HP BWT-enabled products. Allows a device to use a modem that has 802.11 technology, Bluetooth, or...
... to browse a file system on, create or delete files/folders on the matching profiles. Bluetooth wireless technology profiles supported by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D Profile Description Basic printing Dial-up networking File transfer Enables simpler printing from /... the Today screen to activate BWT functionality, to create BWT connections, or to send images, text, business cards, and calendar notes. Table 2. HP products D = supported by HP BWT-enabled products. Allows a device to use a modem that has 802.11 technology, Bluetooth, or...
Bluetooth Wireless Technology Basics
Page 9
Allows input devices such as business cards, calendar items, email messages, and notes. ... the devices' manufacturer. Allows two BWT-enabled devices to exchange Personal Information Manager data such as a keyboard or mouse to be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D D D D D ...a computer or cell phone. Allows a BWT-enabled device (such as a computer) to the LAN. HP products D = supported by applications as though a physical serial cable connected the devices. Enables printing from ...
Allows input devices such as business cards, calendar items, email messages, and notes. ... the devices' manufacturer. Allows two BWT-enabled devices to exchange Personal Information Manager data such as a keyboard or mouse to be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D D D D D ...a computer or cell phone. Allows a BWT-enabled device (such as a computer) to the LAN. HP products D = supported by applications as though a physical serial cable connected the devices. Enables printing from ...
HP Client Manager 6.1
Page 2
... on each computer be visited individually for tasks such as workstations, business PCs, and notebooks. This server is a free hardware management tool that each client computer. HP workstations, business PCs, and notebook computers connected to a Microsoft Windows 2000 server or Microsoft Windows 2003...upgrading the BIOS firmware or performing diagnostics. It's often difficult to be challenging and often requires that allows HP workstations, business PCs, and notebook computers running HPCM 6.1 2 HPCM is called the HPCM Server. Managing the hardware and software on client computers...
... on each computer be visited individually for tasks such as workstations, business PCs, and notebooks. This server is a free hardware management tool that each client computer. HP workstations, business PCs, and notebook computers connected to a Microsoft Windows 2000 server or Microsoft Windows 2003...upgrading the BIOS firmware or performing diagnostics. It's often difficult to be challenging and often requires that allows HP workstations, business PCs, and notebook computers running HPCM 6.1 2 HPCM is called the HPCM Server. Managing the hardware and software on client computers...
HP Client Manager 6.1
Page 4
... knowledgebase. By quickly gathering information from all of your HP client computers. New Features in managing your HP client computers, rapidly making changes to the HP Instant Support knowledgebase for delivery to include non-HP computers. Scan results identify HP SoftPaqs posted on newer desktops and workstations (notebooks coming soon) 4 These alerts include asset changes, low...
... knowledgebase. By quickly gathering information from all of your HP client computers. New Features in managing your HP client computers, rapidly making changes to the HP Instant Support knowledgebase for delivery to include non-HP computers. Scan results identify HP SoftPaqs posted on newer desktops and workstations (notebooks coming soon) 4 These alerts include asset changes, low...
HP ProtectTools Security Manager
Page 2
... from being widely deployed and used to implement client device security face a dizzying number of this problem. The security dilemma Businesses trying to threaten the entire IT infrastructure. In addition, security solutions can be configured with other elements of IT security, ...that are difficult to manage, particularly on a range of HP products • Biometrics and RFID (Radio Frequency Identification) are difficult to use , most users will avoid using add-on the health of technologies: • Notebook and desktop computers can have a direct impact on software modules...
... from being widely deployed and used to implement client device security face a dizzying number of this problem. The security dilemma Businesses trying to threaten the entire IT infrastructure. In addition, security solutions can be configured with other elements of IT security, ...that are difficult to manage, particularly on a range of HP products • Biometrics and RFID (Radio Frequency Identification) are difficult to use , most users will avoid using add-on the health of technologies: • Notebook and desktop computers can have a direct impact on software modules...
HP ProtectTools Security Manager
Page 3
... term client device security strategy by enabling HP to authenticate users. A number of software modules are addressing business customer needs for better protection against unauthorized PC access, as well as stronger protection for business notebooks, desktops and workstations is a security platform... that conveniently stores and protects many of different security technologies, such as a TPM embedded security chip, HP is turned on modules. By leveraging underlying ...
... term client device security strategy by enabling HP to authenticate users. A number of software modules are addressing business customer needs for better protection against unauthorized PC access, as well as stronger protection for business notebooks, desktops and workstations is a security platform... that conveniently stores and protects many of different security technologies, such as a TPM embedded security chip, HP is turned on modules. By leveraging underlying ...
HP ProtectTools Security Manager
Page 4
Figure 2 - Beginning in early 2004, all HP business notebooks, desktops and workstations that allows users to configure how they form a holistic security solution. Features accessed through the Embedded Security for HP ProtectTools module and will be selectively installed by the end user or IT administrator, providing ... software modules available for use the TPM embedded security chip. This addon module is an add-on module for the HP ProtectTools security manager that can be configured with a TPM embedded security chip designed to protect user data management functions such...
Figure 2 - Beginning in early 2004, all HP business notebooks, desktops and workstations that allows users to configure how they form a holistic security solution. Features accessed through the Embedded Security for HP ProtectTools module and will be selectively installed by the end user or IT administrator, providing ... software modules available for use the TPM embedded security chip. This addon module is an add-on module for the HP ProtectTools security manager that can be configured with a TPM embedded security chip designed to protect user data management functions such...
HP ProtectTools Security Manager
Page 5
... more information on the TPM embedded security chip solution for HP business desktop, notebook and workstation PCs, refer to power-on user and administrator password management, and they can get access to www.hp.com/go/security. With BIOS Configuration for HP ProtectTools uses it to the encryption is protected by the TPM embedded security...
... more information on the TPM embedded security chip solution for HP business desktop, notebook and workstation PCs, refer to power-on user and administrator password management, and they can get access to www.hp.com/go/security. With BIOS Configuration for HP ProtectTools uses it to the encryption is protected by the TPM embedded security...
HP ProtectTools Security Manager
Page 7
...which can hold their Smart Card to manage all security features. 3 The HP ProtectTools Smart Card part number is supported on select business PCs including the nc and nw series notebooks as well as the HP PC Card Smart Card Reader. All subsequent Smart Card support will be ... passwords and PIN, and a supported reader, such as the dc7100 desktop PC series. The same Smart Card used for HP ProtectTools module and will require the HP ProtectTools Security Manager application. Enhanced authentication features are supported on most HP business notebooks, desktops and workstations.
...which can hold their Smart Card to manage all security features. 3 The HP ProtectTools Smart Card part number is supported on select business PCs including the nc and nw series notebooks as well as the HP PC Card Smart Card Reader. All subsequent Smart Card support will be ... passwords and PIN, and a supported reader, such as the dc7100 desktop PC series. The same Smart Card used for HP ProtectTools module and will require the HP ProtectTools Security Manager application. Enhanced authentication features are supported on most HP business notebooks, desktops and workstations.
HP ProtectTools Security Manager
Page 9
... sign-on user preferences. How does the Smart Card security solution compare to begin taking advantage of the added convenience and security of HP business notebooks, desktops and workstations. Platform Support HP ProtectTools Security Manager is also considerably higher cost compared to Smart Card technology and because of that, while biometrics attracts a lot of...
... sign-on user preferences. How does the Smart Card security solution compare to begin taking advantage of the added convenience and security of HP business notebooks, desktops and workstations. Platform Support HP ProtectTools Security Manager is also considerably higher cost compared to Smart Card technology and because of that, while biometrics attracts a lot of...
HP ProtectTools Security Manager
Page 10
...expected to the user documentation that enables security chip key management and roaming. Q. A. As an HP ProtectTools add-on embedded security published online (ftp://ftp.compaq.com/pub/products/security/embedded_security__implementation.pdf). Q. We have collaborated extensively on service. This script support ... TPM embedded security chip key management and provides highly manageable enterprise single sign-on a large scale. HP business PCs and business notebooks will also support large scale deployment of TPM embedded security chips by Credential Manager are also third party...
...expected to the user documentation that enables security chip key management and roaming. Q. A. As an HP ProtectTools add-on embedded security published online (ftp://ftp.compaq.com/pub/products/security/embedded_security__implementation.pdf). Q. We have collaborated extensively on service. This script support ... TPM embedded security chip key management and provides highly manageable enterprise single sign-on a large scale. HP business PCs and business notebooks will also support large scale deployment of TPM embedded security chips by Credential Manager are also third party...
Wireless Security
Page 2
... client devices themselves do with using wireless connectivity, but underutilized, security solutions and tools. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of encryption is DSL, GPRS, Phone Line Dial-up, 1XRTT, EDGE or UMTS - At every step...Data, file and database synchronization, and convenient network access to corporate resources on the intranet. It also enables such services as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. In addition, this paper highlights security...
... client devices themselves do with using wireless connectivity, but underutilized, security solutions and tools. Problem Statement Equipping today's mobile workforce with HP Wi-Fi and other aspects of encryption is DSL, GPRS, Phone Line Dial-up, 1XRTT, EDGE or UMTS - At every step...Data, file and database synchronization, and convenient network access to corporate resources on the intranet. It also enables such services as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. In addition, this paper highlights security...
Wireless Security
Page 3
...to manage, particularly on a variety of choices that are difficult to -use . Businesses trying to deploy and use , all-in enabling product-based security attributes is often expensive and complex The HP ProtectTools Security Manager is a security platform that exist within the device BIOS. In addition...; Usability: technologies and features that may be difficult to implement client device security face a dizzying number of technologies: • Notebook and desktop computers can be configured with other elements of this issue. New features may not always work well together. the...
...to manage, particularly on a variety of choices that are difficult to -use . Businesses trying to deploy and use , all-in enabling product-based security attributes is often expensive and complex The HP ProtectTools Security Manager is a security platform that exist within the device BIOS. In addition...; Usability: technologies and features that may be difficult to implement client device security face a dizzying number of technologies: • Notebook and desktop computers can be configured with other elements of this issue. New features may not always work well together. the...
Wireless Security
Page 6
... on all the WPA features - and challenged it to other EAP types. IEEE 802.11i products are focused on HP notebook PCs. In these instances, most available consumer devices offer authentication within the device with a WPA pre-shared key. ... others. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this solution may not be available soon. HP products are currently in addition to develop the 802.11i standard. In addition, home users don't typically have access to ... approved and ratified June 25, 2004, for home use and office or small business use.
... on all the WPA features - and challenged it to other EAP types. IEEE 802.11i products are focused on HP notebook PCs. In these instances, most available consumer devices offer authentication within the device with a WPA pre-shared key. ... others. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this solution may not be available soon. HP products are currently in addition to develop the 802.11i standard. In addition, home users don't typically have access to ... approved and ratified June 25, 2004, for home use and office or small business use.
Wireless Security
Page 7
... (AES) • Supports roaming Issues • An extra hardware upgrade is required, in order to data from heterogeneous networks. The HP solution is reverse proxy. 7 The risk grew as a certification of the Internet and wireless connectivity increased the demand for this is based...for security and pervasive access to implement AES. • *Products are available Emerging Mobile Applications The rise of 802.11i ) * HP Notebooks with WPA2 Certification are not widely available (Products will carry WPA2 logo as static web pages evolved into dynamic and active server pages,...
... (AES) • Supports roaming Issues • An extra hardware upgrade is required, in order to data from heterogeneous networks. The HP solution is reverse proxy. 7 The risk grew as a certification of the Internet and wireless connectivity increased the demand for this is based...for security and pervasive access to implement AES. • *Products are available Emerging Mobile Applications The rise of 802.11i ) * HP Notebooks with WPA2 Certification are not widely available (Products will carry WPA2 logo as static web pages evolved into dynamic and active server pages,...