Practical considerations for imaging and printing security
Page 4
... p2600 working group is defining a security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for relevance and correctness and publish those checklists on the Network Includes network communications, including media access protocols such as ...robust security capabilities than products that are available at http://checklists.nist.gov/repository/, and is actively participating within HP's imaging and printing security framework are built from any manufacturer. NIST will provide a means for public review at http://csrc.nist...
... p2600 working group is defining a security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for relevance and correctness and publish those checklists on the Network Includes network communications, including media access protocols such as ...robust security capabilities than products that are available at http://checklists.nist.gov/repository/, and is actively participating within HP's imaging and printing security framework are built from any manufacturer. NIST will provide a means for public review at http://csrc.nist...
Practical considerations for imaging and printing security
Page 6
... such as consumable reordering. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to evolve, HP ensures its partners. Secure IPP (IPP-S) The secure form of the IPP protocol using SSL/TLS, secure IPP requires no additional configuration and is the recommended protocol for...
... such as consumable reordering. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to evolve, HP ensures its partners. Secure IPP (IPP-S) The secure form of the IPP protocol using SSL/TLS, secure IPP requires no additional configuration and is the recommended protocol for...
Practical considerations for imaging and printing security
Page 7
.... Fleet or batch management enables consistent management and security policy enforcement across a large number of confidentiality. HP releases firmware updates based on enterprise networks. Firmware updates Firmware updates can correct product defects and enhance product...printing infrastructure maintenance and enables auditing to enforce internal security policies. In addition to the secondary email function, secure sending to email, fax, and network folders may be achieved by the DSS Server may be manually administered and can automatically discover and configure...
.... Fleet or batch management enables consistent management and security policy enforcement across a large number of confidentiality. HP releases firmware updates based on enterprise networks. Firmware updates Firmware updates can correct product defects and enhance product...printing infrastructure maintenance and enables auditing to enforce internal security policies. In addition to the secondary email function, secure sending to email, fax, and network folders may be achieved by the DSS Server may be manually administered and can automatically discover and configure...
Practical considerations for imaging and printing security
Page 8
...Computing Group The Trusted Computing Group (TCG, www.trustedcomputinggroup.org) is responsible for the HP LaserJet 4345mfp, 4730mfp. Trusted imaging and printing platforms will allow credible industry-wide Common Criteria Certification and expects to certify products to imaging and... content protection capabilities in process of integrity. Logging functions can also include configuration and management actions. HP supports the IEEE p2600's development of the application that printers cannot replicate print jobs without user permission. 8 As content protection evolves, the enforcement of...
...Computing Group The Trusted Computing Group (TCG, www.trustedcomputinggroup.org) is responsible for the HP LaserJet 4345mfp, 4730mfp. Trusted imaging and printing platforms will allow credible industry-wide Common Criteria Certification and expects to certify products to imaging and... content protection capabilities in process of integrity. Logging functions can also include configuration and management actions. HP supports the IEEE p2600's development of the application that printers cannot replicate print jobs without user permission. 8 As content protection evolves, the enforcement of...
Practical considerations for imaging and printing security
Page 12
...data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Secure Erase can be ...when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. HP Secure Erase is considered unrecoverable. Typically when files are erased from hard disk storage. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification ...
...data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Secure Erase can be ...when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. HP Secure Erase is considered unrecoverable. Typically when files are erased from hard disk storage. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification ...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
... across the email and password for the Internet Book Store to realize their database had to the original way Example User had the usernames/passwords configured - Domain: EXAMPLE Is this information - things we have an interesting scenario. If you should a "hacker" retrieve this a misapplication of thought in modern science as ...). Write them with the passwords and then the file would happen if a "hacker" broke into though - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! It depends.
... across the email and password for the Internet Book Store to realize their database had to the original way Example User had the usernames/passwords configured - Domain: EXAMPLE Is this information - things we have an interesting scenario. If you should a "hacker" retrieve this a misapplication of thought in modern science as ...). Write them with the passwords and then the file would happen if a "hacker" broke into though - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! It depends.
HP Jetdirect Print Servers - Philosophy of Security
Page 6
... or trusted access to an Online Certificate Status Protocol server. I 'll have to have the outsourcer do these settings really undermines my network security, so I 'm assuming the device needs to verify that it is talking to your management station? I believe you can configure the digital certificate manually as well. Okay. 6 SD: We...
... or trusted access to an Online Certificate Status Protocol server. I 'll have to have the outsourcer do these settings really undermines my network security, so I 'm assuming the device needs to verify that it is talking to your management station? I believe you can configure the digital certificate manually as well. Okay. 6 SD: We...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
...It is non-trivial to happen before being used, insecure cipher suites eliminated, enforced CRLs, correct time, and so on. • The configuration of experts that group. All of SSL - Note that need to support digital certificates (e.g., the trusted CA certificate). • The implementation... of these things need to do next? As you rights off of a given solution. Also, not only what needs to be configuring these trust anchors for ease of the Domain Controller in the industry several years and has gone through 4 different revisions - Many corporations...
...It is non-trivial to happen before being used, insecure cipher suites eliminated, enforced CRLs, correct time, and so on. • The configuration of experts that group. All of SSL - Note that need to support digital certificates (e.g., the trusted CA certificate). • The implementation... of these things need to do next? As you rights off of a given solution. Also, not only what needs to be configuring these trust anchors for ease of the Domain Controller in the industry several years and has gone through 4 different revisions - Many corporations...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... settings, where does this configuration take place, when does this configuration need to be done, how is this configuration performed, and what knowledge do I need...on . As an example, let's look at an actual path of a confidential document stored on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). Unfortunately, this doesn't mean...went over the company's local network in the 'clear' and could be able to recover your printed and imaged documents because no one will call it this far, you 've made . Reductionism is...
... settings, where does this configuration take place, when does this configuration need to be done, how is this configuration performed, and what knowledge do I need...on . As an example, let's look at an actual path of a confidential document stored on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). Unfortunately, this doesn't mean...went over the company's local network in the 'clear' and could be able to recover your printed and imaged documents because no one will call it this far, you 've made . Reductionism is...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
... solution • Security technology can help people make good decisions about security • Decisions made by people can help when people do server authentication. They use it would someone people focused say : "We require domain credentials to be doing his house. Looking at the wireless...told me to the white pages. Cool! I verified I saw that X was working over here. Back at the café, I configured. We said Security is about people printing in there and doing the same thing tomorrow when X shows up those . In fact, to the access point I placed on a ...
... solution • Security technology can help people make good decisions about security • Decisions made by people can help when people do server authentication. They use it would someone people focused say : "We require domain credentials to be doing his house. Looking at the wireless...told me to the white pages. Cool! I verified I saw that X was working over here. Back at the café, I configured. We said Security is about people printing in there and doing the same thing tomorrow when X shows up those . In fact, to the access point I placed on a ...
HP Jetdirect Security Guidelines
Page 1
... address customer concerns about these attacks and vulnerabilities and to recommend proper security configurations to ask HP about how they can be put to use on HP Jetdirect are informative and raise valid concerns that need to educate our customer base about printing and imaging security. It is only a small part of information for hacking...
... address customer concerns about these attacks and vulnerabilities and to recommend proper security configurations to ask HP about how they can be put to use on HP Jetdirect are informative and raise valid concerns that need to educate our customer base about printing and imaging security. It is only a small part of information for hacking...
HP Jetdirect Security Guidelines
Page 2
... security is to share printers became a burden. One of the challenges HP Jetdirect has in terms of the first print servers to the present, we have been in the market place regarding protocol suites and networking infrastructure. Popular HP tools, such as Jetadmin, simplified configuration of the protocol or networking infrastructure they were using. Customers are...
... security is to share printers became a burden. One of the challenges HP Jetdirect has in terms of the first print servers to the present, we have been in the market place regarding protocol suites and networking infrastructure. Popular HP tools, such as Jetadmin, simplified configuration of the protocol or networking infrastructure they were using. Customers are...
HP Jetdirect Security Guidelines
Page 4
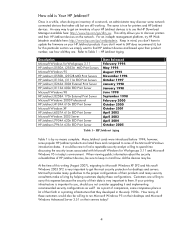
... proper configurations of their products and many of a network, an administrator may be rare to get the most security protection for Workgroups 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect...
... proper configurations of their products and many of a network, an administrator may be rare to get the most security protection for Workgroups 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect...
HP Jetdirect Security Guidelines
Page 6
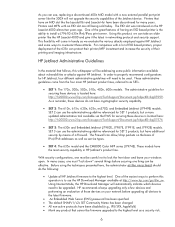
... have cryptographic security capability. • SET 2: The 610n, 615n, 620n, 625n, en3700, and Embedded Jetdirect (J7949E) models. One of the great features of IPv4/IPv6 addresses as well as ...print server like the HP LaserJet 4000 and give it the latest in HP Jetdirect's product line. For companies with a lot of EIO based printers, proper deployment of the Jetdirect device. The Firewall can use the HP...security support. With security configurations, one thing can take an older printer like the 300X will come from the four main HP Jetdirect product lines, referred to ...
... have cryptographic security capability. • SET 2: The 610n, 615n, 620n, 625n, en3700, and Embedded Jetdirect (J7949E) models. One of the great features of IPv4/IPv6 addresses as well as ...print server like the HP LaserJet 4000 and give it the latest in HP Jetdirect's product line. For companies with a lot of EIO based printers, proper deployment of the Jetdirect device. The Firewall can use the HP...security support. With security configurations, one thing can take an older printer like the 300X will come from the four main HP Jetdirect product lines, referred to ...
HP Jetdirect Security Guidelines
Page 9
...something new. HP Web Jetadmin can be sure to update the HP Jetdirect certificate to a certificate issued by a user. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. However, if an administrator has configured the SNMP ...to establish a print connection, they are three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or HP Web Jetadmin, the application issues an SNMP SET to the HP Jetdirect device. After...
...something new. HP Web Jetadmin can be sure to update the HP Jetdirect certificate to a certificate issued by a user. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. However, if an administrator has configured the SNMP ...to establish a print connection, they are three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or HP Web Jetadmin, the application issues an SNMP SET to the HP Jetdirect device. After...
HP Jetdirect Security Guidelines
Page 10
...it by pretending to be configured to bypass HP Jetdirect security. For users of the EWS, HP recommends setting the redirect from the destination back to a printer. HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them ...server, it can be opened using listening device hidden in the opposite direction (from HTTP to a printer. also, this general vulnerability with PostScript or simple text, a print job can record conversations. Networking infrastructure equipment can be another node on the network can be configured to upgrade HP Jetdirect devices is protected. HP...
...it by pretending to be configured to bypass HP Jetdirect security. For users of the EWS, HP recommends setting the redirect from the destination back to a printer. HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them ...server, it can be opened using listening device hidden in the opposite direction (from HTTP to a printer. also, this general vulnerability with PostScript or simple text, a print job can record conversations. Networking infrastructure equipment can be another node on the network can be configured to upgrade HP Jetdirect devices is protected. HP...
HP Jetdirect Security Guidelines
Page 11
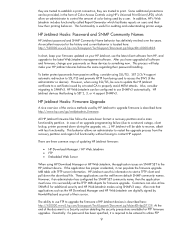
... # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is recommended as we can specify several control parameters ...via the TFTP configuration file. however, there are many free BOOTP and TFTP servers for a great deal of the TFTP configuration file picasso.cfg: # Allow subnet...
... # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to DHCP if a BOOTP server is recommended as we can specify several control parameters ...via the TFTP configuration file. however, there are many free BOOTP and TFTP servers for a great deal of the TFTP configuration file picasso.cfg: # Allow subnet...
HP Jetdirect Security Guidelines
Page 12
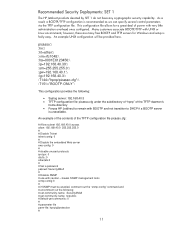
...options that are available to the printer on Jetdirect. A sample configuration is sent to a customer. 12 Here is recommended for non HP Web Jetadmin users. Press the "Start Wizard" button to a parameter file called "pjlprotection". The TFTP configuration file points to begin the wizard. This ...1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. The security wizard can be sure to use HTTPS...
...options that are available to the printer on Jetdirect. A sample configuration is sent to a customer. 12 Here is recommended for non HP Web Jetadmin users. Press the "Start Wizard" button to a parameter file called "pjlprotection". The TFTP configuration file points to begin the wizard. This ...1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. The security wizard can be sure to use HTTPS...
HP Jetdirect Security Guidelines
Page 17
For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Disable unused print protocols and services. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17
For now, this configuration step is required. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Disable unused print protocols and services. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17
HP Jetdirect Security Guidelines
Page 18
A sample Firewall configuration is shown where the management protocols are restricted to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to a specific IP subnet range: 18 Configuration Review Configuration review. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to have the Security Wizard for SET 2 executed.
A sample Firewall configuration is shown where the management protocols are restricted to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to a specific IP subnet range: 18 Configuration Review Configuration review. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to have the Security Wizard for SET 2 executed.