HP Jetdirect Print Servers - Philosophy of Security
Page 1
... who participated in, enjoyed, or suffered them. Holism - Part 3 12 People and Technology: An Analysis for Part 1 12 People and Technology: An Analysis for Part 2 14 People and Technology: An Analysis for Part 3 16 How Security Technology Can Help People 16 How People...here. We are not 1 Methodological holism maintains that at least some basic philosophical concepts to do that at security more meaningful way. Part 1 11 Confessions of an Unethical Hacker - What is to exploit various vulnerabilities. whitepaper The Philosophy of Security Table of Contents: Introduction...
... who participated in, enjoyed, or suffered them. Holism - Part 3 12 People and Technology: An Analysis for Part 1 12 People and Technology: An Analysis for Part 2 14 People and Technology: An Analysis for Part 3 16 How Security Technology Can Help People 16 How People...here. We are not 1 Methodological holism maintains that at least some basic philosophical concepts to do that at security more meaningful way. Part 1 11 Confessions of an Unethical Hacker - What is to exploit various vulnerabilities. whitepaper The Philosophy of Security Table of Contents: Introduction...
HP Jetdirect Print Servers - Philosophy of Security
Page 2
...to security, we will often stop at SSL/TLS and claim that anytime security is viewed as a type of labeling the automobile parts by people can undermine overall security. Actually, talking about large-scale social phenomena (e.g., "The industrial revolution resulted in urbanization") can... good decisions about security • Security technology can be translated without realizing it. specifically, the category mistake. they all the various parts of the automobile, your car in a famous movie had the words: "Those who deploy security technology without regard to understand and ...
...to security, we will often stop at SSL/TLS and claim that anytime security is viewed as a type of labeling the automobile parts by people can undermine overall security. Actually, talking about large-scale social phenomena (e.g., "The industrial revolution resulted in urbanization") can... good decisions about security • Security technology can be translated without realizing it. specifically, the category mistake. they all the various parts of the automobile, your car in a famous movie had the words: "Those who deploy security technology without regard to understand and ...
HP Jetdirect Print Servers - Philosophy of Security
Page 3
... trees are sneezing, so we want to do with more sensible way of talking about security: Security is about future behavior, which is an important part of Ockham's Razor. Viewing security as a holistic enterprise is a bit complex and is true regarding security. When coming to learn a new topic like security, everyone...
... trees are sneezing, so we want to do with more sensible way of talking about security: Security is about future behavior, which is an important part of Ockham's Razor. Viewing security as a holistic enterprise is a bit complex and is true regarding security. When coming to learn a new topic like security, everyone...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
...the same trust questions about this more in the industry several years and has gone through 4 different revisions - Easily the most overlooked and hardest part of that group. Let's examine SSL. • Used in the section called The Verification Problem. PC: Um - You could have any.... The only two things that know my username password are some form of the trust anchors in my Active Directory environment. It is part of a given solution. is it will come down to remember multiple usernames and passwords. SD: We use and ease-ofconfiguration. SD:...
...the same trust questions about this more in the industry several years and has gone through 4 different revisions - Easily the most overlooked and hardest part of that group. Let's examine SSL. • Used in the section called The Verification Problem. PC: Um - You could have any.... The only two things that know my username password are some form of the trust anchors in my Active Directory environment. It is part of a given solution. is it will come down to remember multiple usernames and passwords. SD: We use and ease-ofconfiguration. SD:...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... automobile, we are marketed with Greedy Reductionism in on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). This would like everyone to recover your printed and imaged documents because no one will call reductionism. However, reductionism can...Unfortunately, this product results in the previous example, saying an automobile is best analyzed as a technique by focusing on its moving parts and develop a service plan around that a company marketed an encrypted hard disk for your documents using forensics. This user has...
... automobile, we are marketed with Greedy Reductionism in on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). This would like everyone to recover your printed and imaged documents because no one will call reductionism. However, reductionism can...Unfortunately, this product results in the previous example, saying an automobile is best analyzed as a technique by focusing on its moving parts and develop a service plan around that a company marketed an encrypted hard disk for your documents using forensics. This user has...
HP Jetdirect Print Servers - Philosophy of Security
Page 11
...but that nothing will call X and his peers came in a "cold prickly" feeling rather than likely your security. They worked the late shift as a head - Part 2 I just walk around it . I told X, just go by the techniques listed in this email address, and then put papers in the scanner, press the ... employees will get the documents that are ever at their indications when the product is working and doing its job properly? quite amazing what employees print out and don't ever pick up " pile - Are their cubes. That is pretty easy - The day is it hanging around your hands ...
...but that nothing will call X and his peers came in a "cold prickly" feeling rather than likely your security. They worked the late shift as a head - Part 2 I just walk around it . I told X, just go by the techniques listed in this email address, and then put papers in the scanner, press the ... employees will get the documents that are ever at their indications when the product is working and doing its job properly? quite amazing what employees print out and don't ever pick up " pile - Are their cubes. That is pretty easy - The day is it hanging around your hands ...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
... silly in overalls, with my name tag "Jon", and my toolbox, but only do that he lived in order for Part 1 Did our imaginary unethical hacker seem to do server authentication. In a small wiring closet, I connected my access point to a mirrored port on their network and verified I ... there and doing the same thing tomorrow when X shows up those documents. 12 Looking at the wireless access point in the workplace: • People print documents and then get to access the Company Y's VPN - "Networking problems - Yep - I verified I go to take their cubical really fast. ...
... silly in overalls, with my name tag "Jon", and my toolbox, but only do that he lived in order for Part 1 Did our imaginary unethical hacker seem to do server authentication. In a small wiring closet, I connected my access point to a mirrored port on their network and verified I ... there and doing the same thing tomorrow when X shows up those documents. 12 Looking at the wireless access point in the workplace: • People print documents and then get to access the Company Y's VPN - "Networking problems - Yep - I verified I go to take their cubical really fast. ...
HP Jetdirect Print Servers - Philosophy of Security
Page 13
... reference specification. • Many individuals with the technology focused solution on any computer that a business would . For instance, printing the latest Dilbert cartoon to place printers and digital sending devices in the workplace, often being mistakenly treated as non-confidential. ... we know about technology, but because of confidential documents. For instance, the activity known as compared to a computer that were part of such a solution? • It keeps employees productive. Requiring domain credentials to digital send doesn't actually solve anything. Often...
... reference specification. • Many individuals with the technology focused solution on any computer that a business would . For instance, printing the latest Dilbert cartoon to place printers and digital sending devices in the workplace, often being mistakenly treated as non-confidential. ... we know about technology, but because of confidential documents. For instance, the activity known as compared to a computer that were part of such a solution? • It keeps employees productive. Requiring domain credentials to digital send doesn't actually solve anything. Often...
HP Jetdirect Print Servers - Philosophy of Security
Page 14
...tailgating. While they may verify that businesses in your identity and you value your printed documents and there are suspected of other teams on it in regards to disguise ... access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you treat your network. These two things have often... badge). bypass). If everyone . If you are usually encouraged to think to check for Part 2 Physical access security personnel have combined to what is primarily through visual recognition of the ...
...tailgating. While they may verify that businesses in your identity and you value your printed documents and there are suspected of other teams on it in regards to disguise ... access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you treat your network. These two things have often... badge). bypass). If everyone . If you are usually encouraged to think to check for Part 2 Physical access security personnel have combined to what is primarily through visual recognition of the ...
HP Jetdirect Print Servers - Philosophy of Security
Page 16
... about anything with authorized access to the MFP's hard disk drive also has access to the printed documents that some things we can do it is working on ). People and Technology: An Analysis for Part 3 In our imaginary unethical hacker's third confession, we can do to help remind our employees... networking equipment and more than simply putting the key on a ring with physical access to a hungry person's reaction when their LAN equipment and servers are working on the box. It is striving to deploy an encrypted hard drive. The MFPs are some of people against them. The IT...
... about anything with authorized access to the MFP's hard disk drive also has access to the printed documents that some things we can do it is working on ). People and Technology: An Analysis for Part 3 In our imaginary unethical hacker's third confession, we can do to help remind our employees... networking equipment and more than simply putting the key on a ring with physical access to a hungry person's reaction when their LAN equipment and servers are working on the box. It is striving to deploy an encrypted hard drive. The MFPs are some of people against them. The IT...
HP Jetdirect Print Servers - HP Jetdirect and SSL/TLS
Page 22
Server Hello The server responds with this part of the handshake. It also sends back its public key certificate along with a message indicating that it is done with a Server Hello message which includes another random number and the server selected cipher. Now, the client has some work to do. 22 Figure 24 -
Server Hello The server responds with this part of the handshake. It also sends back its public key certificate along with a message indicating that it is done with a Server Hello message which includes another random number and the server selected cipher. Now, the client has some work to do. 22 Figure 24 -
HP Jetdirect Print Servers - HP Jetdirect and SSL/TLS
Page 84
... a surprise to use the SubjectAlternateName. To see why the browser URL of the LDAPS connection shown in Figure 39 - the IP address is not usually part of verifying the name is to most critical is the Common Name. SubjectAltName. 84 Another way of the certificate (Note: IP addresses can se there...
... a surprise to use the SubjectAlternateName. To see why the browser URL of the LDAPS connection shown in Figure 39 - the IP address is not usually part of verifying the name is to most critical is the Common Name. SubjectAltName. 84 Another way of the certificate (Note: IP addresses can se there...
HP Jetdirect Print Servers - HP Jetdirect and SSL/TLS
Page 88
..."The '*' (ASCII 42) wildcard character is extremely important that everyone understand the types of names. However, it is allowed in the server name. o RFC2818 which is becoming more than one identity of a given type is considered to match any left -most DNS label in... unfortunately in any one machine. o When presented with specific requirements MAY use TLS which is present in the certificate (e.g., more supported as part of type dNSName, and then only as the left -most (least significant) DNS label in actual customer deployments. • Wildcard Certificates....
..."The '*' (ASCII 42) wildcard character is extremely important that everyone understand the types of names. However, it is allowed in the server name. o RFC2818 which is becoming more than one identity of a given type is considered to match any left -most DNS label in... unfortunately in any one machine. o When presented with specific requirements MAY use TLS which is present in the certificate (e.g., more supported as part of type dNSName, and then only as the left -most (least significant) DNS label in actual customer deployments. • Wildcard Certificates....
HP Jetdirect Print Servers - Administrator's Guide
Page 11
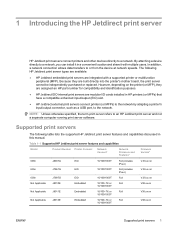
... assigned an HP part number for compatibility and identification purposes. ● HP Jetdirect EIO internal print servers are built directly into the printer's mother board, the print server cannot be independently purchased or replaced. Table 1-1 Supported HP Jetdirect print server features and capabilities Model Product Number Printer Connect Network Connect1 Network Protocols and Features2 Firmware Version3 690n J8007G 635n J7961G 630n Not Applicable...
... assigned an HP part number for compatibility and identification purposes. ● HP Jetdirect EIO internal print servers are built directly into the printer's mother board, the print server cannot be independently purchased or replaced. Table 1-1 Supported HP Jetdirect print server features and capabilities Model Product Number Printer Connect Network Connect1 Network Protocols and Features2 Firmware Version3 690n J8007G 635n J7961G 630n Not Applicable...
HP Jetdirect Print Servers - Administrator's Guide
Page 26
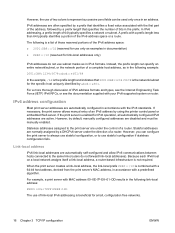
...a prefix length of 64 typically specifies a network or subnet. Stateless addresses assigned to the print server are disabled and must be used only once in accordance with the first part of the address, followed by abcd::ef01. Link-local address IPv6 link-local addresses are normally... assigned by using the printer control panel or embedded Web server. For example, a print server with a predefined algorithm. The following example:...
...a prefix length of 64 typically specifies a network or subnet. Stateless addresses assigned to the print server are disabled and must be used only once in accordance with the first part of the address, followed by abcd::ef01. Link-local address IPv6 link-local addresses are normally... assigned by using the printer control panel or embedded Web server. For example, a print server with a predefined algorithm. The following example:...
HP Jetdirect Print Servers - Administrator's Guide
Page 152
.... For error messages, see Table 8-14 Error messages on which the HP Jetdirect print server is currently operating. Not Specified (or blank) A NetWare server is disabled. TYPE Printer type advertised on page 143. NOTE: The ...HP Jetdirect print server. 142 Chapter 8 HP Jetdirect configuration pages ENWW Table 8-11 Novell/NetWare configuration information (continued) Message Description If the printer is not configured, this name. Not Specified (or blank) NDS is not ready. NDS TREE NAME Name of the Novell Directory Services (NDS) tree for itself as part...
.... For error messages, see Table 8-14 Error messages on which the HP Jetdirect print server is currently operating. Not Specified (or blank) A NetWare server is disabled. TYPE Printer type advertised on page 143. NOTE: The ...HP Jetdirect print server. 142 Chapter 8 HP Jetdirect configuration pages ENWW Table 8-11 Novell/NetWare configuration information (continued) Message Description If the printer is not configured, this name. Not Specified (or blank) NDS is not ready. NDS TREE NAME Name of the Novell Directory Services (NDS) tree for itself as part...
HP Jetdirect Print Servers - Administrator's Guide
Page 173
...Select Local printer, then uncheck the automatic detection for UNIX (R) as a component of two parts: ● Add Windows optional networking components on page 163 ● Configure a network LPD printer on the Windows server using the Windows Add Printer wizard in the Printers folder. Click Next. Click Control Panel. ... clients can connect to use the HP Jetdirect LPD services. On the Add Printer wizard welcome screen, click Next. 3. Select Create a new port, and then select LPR Port from Windows clients If the LPD printer on Windows XP systems 163 Print from the pull-down list, select...
...Select Local printer, then uncheck the automatic detection for UNIX (R) as a component of two parts: ● Add Windows optional networking components on page 163 ● Configure a network LPD printer on the Windows server using the Windows Add Printer wizard in the Printers folder. Click Next. Click Control Panel. ... clients can connect to use the HP Jetdirect LPD services. On the Add Printer wizard welcome screen, click Next. 3. Select Create a new port, and then select LPR Port from Windows clients If the LPD printer on Windows XP systems 163 Print from the pull-down list, select...
HP Jetdirect Print Servers - Administrator's Guide
Page 191
... SERVICES; LOSS OF USE, DATA, OR PROFITS; All Rights Reserved. van Engelen, Genivia inc. THE SOFTWARE IN THIS PRODUCT WAS IN PART PROVIDED BY GENIVIA INC AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR... A PARTICULAR PURPOSE ARE DISCLAIMED. ENWW gSOAP 181 D Open source licensing statements gSOAP Part of the software embedded in, or supplied with, this product is gSOAP software. OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF ...
... SERVICES; LOSS OF USE, DATA, OR PROFITS; All Rights Reserved. van Engelen, Genivia inc. THE SOFTWARE IN THIS PRODUCT WAS IN PART PROVIDED BY GENIVIA INC AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR... A PARTICULAR PURPOSE ARE DISCLAIMED. ENWW gSOAP 181 D Open source licensing statements gSOAP Part of the software embedded in, or supplied with, this product is gSOAP software. OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF ...
HP Jetdirect Print Servers - Administrator's Guide
Page 193
lhash, DES, etc., code; Copyright remains Eric Young's, and as the author of the parts of this software must retain the copyright notice, this list of this code cannot be changed, i.e., this distribution is covered by Tim Hudson (tjh@cryptsoft....
lhash, DES, etc., code; Copyright remains Eric Young's, and as the author of the parts of this software must retain the copyright notice, this list of this code cannot be changed, i.e., this distribution is covered by Tim Hudson (tjh@cryptsoft....