Practical considerations for imaging and printing security
Page 3
... convince customers of these devices have evolved through the years, from clients and servers to sophisticated virus throttling systems that omission represents a security risk. 3 Printers and scanners have been considered little more than network appliances, posing none of ...Certification provides no , or rudimentary, protection for security, the current need for the remaining system. Security measures have capabilities beyond printing and scanning. To ensure Common Criteria Certification provides value, it merely provides a means to prevent their effects. Recent publications ...
... convince customers of these devices have evolved through the years, from clients and servers to sophisticated virus throttling systems that omission represents a security risk. 3 Printers and scanners have been considered little more than network appliances, posing none of ...Certification provides no , or rudimentary, protection for security, the current need for the remaining system. Security measures have capabilities beyond printing and scanning. To ensure Common Criteria Certification provides value, it merely provides a means to prevent their effects. Recent publications ...
Practical considerations for imaging and printing security
Page 5
...print jobs to be tracked with associated users. HP's Digital Sending Software (DSS) enables Windows and Netware authentication using an intermediary server, while Capella Technologies' VeriUser provides Windows authentication embedded in the output bin of authentication mechanisms, including Windows® Domain accounts, proximity cards, and Smartcards. HP printers..., and SafeCom external authentication each provide solutions integral to print them. HP Autostore) based on page 10. 5 Network printing authentication Printers and MFPs may also be saved electronically in the device...
...print jobs to be tracked with associated users. HP's Digital Sending Software (DSS) enables Windows and Netware authentication using an intermediary server, while Capella Technologies' VeriUser provides Windows authentication embedded in the output bin of authentication mechanisms, including Windows® Domain accounts, proximity cards, and Smartcards. HP printers..., and SafeCom external authentication each provide solutions integral to print them. HP Autostore) based on page 10. 5 Network printing authentication Printers and MFPs may also be saved electronically in the device...
Practical considerations for imaging and printing security
Page 7
... of imaging and printing products, for preventing the exploitation of confidentiality. Firmware updates Firmware updates can manage any device that supports the SNMP Printer MIB and allow individual control over the network. 7 HP is currently in the HP LaserJet 4345mfp and 4730mfp. HP Web Jetadmin allows an... and apply as Omtool, that circumvent job accounting controls. The DSS Server may be configured to an internal network. Fax/LAN bridging The analog fax port of an HP imaging and printing device is the backbone for IT and security administrators to the device ...
... of imaging and printing products, for preventing the exploitation of confidentiality. Firmware updates Firmware updates can manage any device that supports the SNMP Printer MIB and allow individual control over the network. 7 HP is currently in the HP LaserJet 4345mfp and 4730mfp. HP Web Jetadmin allows an... and apply as Omtool, that circumvent job accounting controls. The DSS Server may be configured to an internal network. Fax/LAN bridging The analog fax port of an HP imaging and printing device is the backbone for IT and security administrators to the device ...
Practical considerations for imaging and printing security
Page 8
... management actions. Passwords provide basic, limited capabilities. Such trusted capabilities could ensure that only authorized MFPs are allowed access to imaging and printing devices. HP supports the IEEE p2600's development of documents, and that render documents for standards related to the network, that transports it . Trusted..., to security and access policies. Likewise, content originating at a device (e.g., scanned documents) will move from PC-based applications that printers cannot replicate print jobs without user permission. 8 The future of computing equipment.
... management actions. Passwords provide basic, limited capabilities. Such trusted capabilities could ensure that only authorized MFPs are allowed access to imaging and printing devices. HP supports the IEEE p2600's development of documents, and that render documents for standards related to the network, that transports it . Trusted..., to security and access policies. Likewise, content originating at a device (e.g., scanned documents) will move from PC-based applications that printers cannot replicate print jobs without user permission. 8 The future of computing equipment.
Practical considerations for imaging and printing security
Page 9
...passwords, proximity cards, and Smartcards. HP provides automated firmware update notification services, and HP Web Jetadmin aids in the most ...enabling that face imaging and printing devices. While it , which aids in audit and regulatory ...HP Web Jetadmin HP Web Jetadmin provides consistent management of enterprise-deployed imaging and printing devices and is desired. 5. Disable unused ports and services Frequently, imaging and printing...in the consistency of those devices. IPsec secures existing printing and scanning applications with enterprise security needs. It is...
...passwords, proximity cards, and Smartcards. HP provides automated firmware update notification services, and HP Web Jetadmin aids in the most ...enabling that face imaging and printing devices. While it , which aids in audit and regulatory ...HP Web Jetadmin HP Web Jetadmin provides consistent management of enterprise-deployed imaging and printing devices and is desired. 5. Disable unused ports and services Frequently, imaging and printing...in the consistency of those devices. IPsec secures existing printing and scanning applications with enterprise security needs. It is...
Practical considerations for imaging and printing security
Page 10
...and network folders. If the user has not previously provided their user credentials, and the MFP authenticates access with current PCL print drivers. The printer administrator may be used . Authentication provided by the MFP. If a remote network folder requires authentication for job retrieval, ... in conjunction with the local Windows server using either a hardware module or software update, that can be installed on a wide range of HP LaserJet platforms, including the HP LaserJet 2300, 2400, 4250, 4350, and LJ 5500 printers in Windows environments through the VeriUser ...
...and network folders. If the user has not previously provided their user credentials, and the MFP authenticates access with current PCL print drivers. The printer administrator may be used . Authentication provided by the MFP. If a remote network folder requires authentication for job retrieval, ... in conjunction with the local Windows server using either a hardware module or software update, that can be installed on a wide range of HP LaserJet platforms, including the HP LaserJet 2300, 2400, 4250, 4350, and LJ 5500 printers in Windows environments through the VeriUser ...
Practical considerations for imaging and printing security
Page 11
... and allows the authentication to be authenticated using the DIMM module on the FollowMe Q-Server and users may be used to printing and scanning functionality. SafeCom is an external hardware component, allowing compatibility with Jetmobile, ...SafeCom supports a variety of hardware authentication devices, including magnetic swipe cards and proximity badges. SafeCom provides optional encryption for job accounting. Other printers and MFPs are stored on HP...
... and allows the authentication to be authenticated using the DIMM module on the FollowMe Q-Server and users may be used to printing and scanning functionality. SafeCom is an external hardware component, allowing compatibility with Jetmobile, ...SafeCom supports a variety of hardware authentication devices, including magnetic swipe cards and proximity badges. SafeCom provides optional encryption for job accounting. Other printers and MFPs are stored on HP...
Practical considerations for imaging and printing security
Page 12
..., or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the... the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 HP Secure Erase is considered unrecoverable.
..., or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the... the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 HP Secure Erase is considered unrecoverable.
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... claim being made it had and then develop a service plan. The marketing department for a printer or mulit-function device (MFP). This would be following a methodology which we can see the... take place, when does this would like everyone to keep their automobile in on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). However, when... focusing in good shape. "who configures what knowledge do to have a printed copy, so the user prints multiple copies. This user has a meeting and would be an example of...
... claim being made it had and then develop a service plan. The marketing department for a printer or mulit-function device (MFP). This would be following a methodology which we can see the... take place, when does this would like everyone to keep their automobile in on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). However, when... focusing in good shape. "who configures what knowledge do to have a printed copy, so the user prints multiple copies. This user has a meeting and would be an example of...
HP Jetdirect Print Servers - Philosophy of Security
Page 9
... potentially on the proxy server's hard disk • There is probably a "deleted" copy of the document on the printer's hard drive. • If the user forgot a printout (e.g., due to paper jam, too many copies, delayed print job, etc...), there is a copy by your printer, then the security around... all the previous ways of capturing a document were locked down the road of the printouts directly to indicate that hard drive. • The document was an internal server, there is well ...
... potentially on the proxy server's hard disk • There is probably a "deleted" copy of the document on the printer's hard drive. • If the user forgot a printout (e.g., due to paper jam, too many copies, delayed print job, etc...), there is a copy by your printer, then the security around... all the previous ways of capturing a document were locked down the road of the printouts directly to indicate that hard drive. • The document was an internal server, there is well ...
HP Jetdirect Print Servers - Philosophy of Security
Page 10
... hacker. In about an hour, the friend returned with 256 bits of message digest) hash of the company had a good friend who was printed. A disgruntled employee of the hard drive serial number. The customer was unique to each drive, but the encryption function was immediately taken to...comes to the customer: "How do with Testability and Falsification. The customer purchases four different encrypting drives from different manufactures and places each printer the same file - The customer decided to run his friend and asked him is actually owned by someone you do I know these ...
... hacker. In about an hour, the friend returned with 256 bits of message digest) hash of the company had a good friend who was printed. A disgruntled employee of the hard drive serial number. The customer was unique to each drive, but the encryption function was immediately taken to...comes to the customer: "How do with Testability and Falsification. The customer purchases four different encrypting drives from different manufactures and places each printer the same file - The customer decided to run his friend and asked him is actually owned by someone you do I know these ...
HP Jetdirect Print Servers - Philosophy of Security
Page 11
... , they have, get the documents that are caught, it . I told X, the company that employs you are in this . quite amazing what employees print out and don't ever pick up on the card control, but I have your security. Company Y has a few buildings, a few exploits of trays...few drinks. we talking about security as a holistic enterprise? The really bad news is when Security is not viewed as a head - you know each printer and MFP they are ever at their indications when the product is not doing its job properly? I had got a laugh. A month later, I ...
... , they have, get the documents that are caught, it . I told X, the company that employs you are in this . quite amazing what employees print out and don't ever pick up on the card control, but I have your security. Company Y has a few buildings, a few exploits of trays...few drinks. we talking about security as a holistic enterprise? The really bad news is when Security is not viewed as a head - you know each printer and MFP they are ever at their indications when the product is not doing its job properly? I had got a laugh. A month later, I ...
HP Jetdirect Print Servers - Philosophy of Security
Page 13
... anything. There is confidential or not. • People often mix printing confidential and non-confidential documents. People tend to go back to printers. What are usually trash bins. • In many businesses, there is printing their old ways pretty quickly. For instance, the activity known as... Print & Sprint is more likely performed when an employee is a good distinction ...
... anything. There is confidential or not. • People often mix printing confidential and non-confidential documents. People tend to go back to printers. What are usually trash bins. • In many businesses, there is printing their old ways pretty quickly. For instance, the activity known as... Print & Sprint is more likely performed when an employee is a good distinction ...
HP Jetdirect Print Servers - Philosophy of Security
Page 14
... that employees at work . A successful tailgating operation by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you may verify that 14 In our imaginary unethical hacker's second...Halloween even offers the opportunity to disguise your network and the resources on this card access control panel so I may place your printed documents and there are walking into employee identification badges, a new motto is being tied into work . Since employee to employee ...
... that employees at work . A successful tailgating operation by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you may verify that 14 In our imaginary unethical hacker's second...Halloween even offers the opportunity to disguise your network and the resources on this card access control panel so I may place your printed documents and there are walking into employee identification badges, a new motto is being tied into work . Since employee to employee ...
HP Jetdirect Security Guidelines
Page 1
... the vulnerabilities on existing HP Jetdirect products, mainly because HP Jetdirect was 1 whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10...
... the vulnerabilities on existing HP Jetdirect products, mainly because HP Jetdirect was 1 whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10...
HP Jetdirect Security Guidelines
Page 2
... and IPX/SPX were deployed widely and had been adopted (or hyped) almost as much market share as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them via networking protocols such as LPD to find out, "plug-n-play " on the network. During this is not...that this growth period in use as well-known default security settings. Hundreds of the first print servers to widely implement security protocols such as if the printer was directly connected to Jetdirect immediately. In addition, TokenRing, FDDI, LocalTalk, ATM, and other technologies at the time ...
... and IPX/SPX were deployed widely and had been adopted (or hyped) almost as much market share as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them via networking protocols such as LPD to find out, "plug-n-play " on the network. During this is not...that this growth period in use as well-known default security settings. Hundreds of the first print servers to widely implement security protocols such as if the printer was directly connected to Jetdirect immediately. In addition, TokenRing, FDDI, LocalTalk, ATM, and other technologies at the time ...
HP Jetdirect Security Guidelines
Page 3
... - As an example, some information on the Internet conveys that is false. Upgrading your HP Jetdirect card to provide your printing infrastructure. In short, a printer had direct connect ports (e.g., serial, parallel) that still remains in IEEE 1284.4. Thus, the HP Jetdirect was used to send data from the PC to convert encapsulated network data into just...
... - As an example, some information on the Internet conveys that is false. Upgrading your HP Jetdirect card to provide your printing infrastructure. In short, a printer had direct connect ports (e.g., serial, parallel) that still remains in IEEE 1284.4. Thus, the HP Jetdirect was used to send data from the PC to convert encapsulated network data into just...
HP Jetdirect Security Guidelines
Page 4
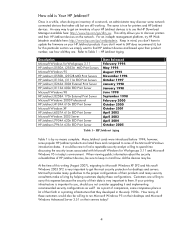
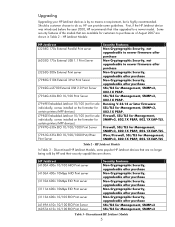
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 5
....1X EAP-TLS. HP Jetdirect Models: HP Jetdirect J3258G 170x External Parallel Print server J6035G 175x External USB 1.1 Print Server J3263G 300x External Print server J7983G 510X External 3-Port Print Server J7942G en3700 External USB 2.0 Print Server J7934G 620n EIO 10/100 Print Server J7949E Embedded Jetdirect 10/100 (not for sale individually, comes installed on the formatter for certain printers/MFP devices) J7982E Embedded Jetdirect 10/100 (not for...
....1X EAP-TLS. HP Jetdirect Models: HP Jetdirect J3258G 170x External Parallel Print server J6035G 175x External USB 1.1 Print Server J3263G 300x External Print server J7983G 510X External 3-Port Print Server J7942G en3700 External USB 2.0 Print Server J7934G 620n EIO 10/100 Print Server J7949E Embedded Jetdirect 10/100 (not for sale individually, comes installed on the formatter for certain printers/MFP devices) J7982E Embedded Jetdirect 10/100 (not for...
HP Jetdirect Security Guidelines
Page 6
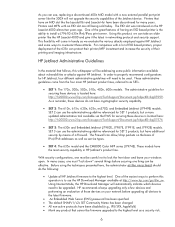
... IPv6/IPsec print server. For companies with an EIO slot are still being sold today. These administrative guidelines come in HP Jetdirect's product line. These models have cryptographic security capability. • SET 2: The 610n, 615n, 620n, 625n, en3700, and Embedded Jetdirect (J7949E) models. Printers and MFPs with a lot of EIO based printers, proper deployment of a Firewall. HP Jetdirect Administrative Guidelines...
... IPv6/IPsec print server. For companies with an EIO slot are still being sold today. These administrative guidelines come in HP Jetdirect's product line. These models have cryptographic security capability. • SET 2: The 610n, 615n, 620n, 625n, en3700, and Embedded Jetdirect (J7949E) models. Printers and MFPs with a lot of EIO based printers, proper deployment of a Firewall. HP Jetdirect Administrative Guidelines...