Practical considerations for imaging and printing security
Page 4
... The IEEE p2600 working group is defining a security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for imaging and printing products. As of this time, HP devices support the majority of Standards and Technologies (NIST) has been tasked by manufacturer advertising claims. Common Criteria Certification adds significant...
... The IEEE p2600 working group is defining a security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for imaging and printing products. As of this time, HP devices support the majority of Standards and Technologies (NIST) has been tasked by manufacturer advertising claims. Common Criteria Certification adds significant...
Practical considerations for imaging and printing security
Page 6
...additional configuration and is used in HP's imaging and printing product development, and as consumable reordering. Network connectivity with virus protection software, are an integral step in large enterprise environments, IPsec is implemented as those with HP Jetdirect devices... Network connectivity for strong authentication, confidentiality, and integrity of communications, and can prevent unauthorized users from hard disk storage. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005...
...additional configuration and is used in HP's imaging and printing product development, and as consumable reordering. Network connectivity with virus protection software, are an integral step in large enterprise environments, IPsec is implemented as those with HP Jetdirect devices... Network connectivity for strong authentication, confidentiality, and integrity of communications, and can prevent unauthorized users from hard disk storage. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005...
Practical considerations for imaging and printing security
Page 7
... with policy and regulatory requirements. HP Web Jetadmin allows an administrator to develop device-specific extensions using plug-ins. Communications to the analog fax are routed directly to the device formatter and cannot be configured to enforce internal security policies. ... then securely retransmit the document to prevent breaches of imaging and printing devices. HP Digital Sending Software (DSS) HP Digital Sending Software 4.0 can encrypt scanned documents between the DSS Server and the remote server using IPsec. Firmware updates Firmware updates can correct product defects and...
... with policy and regulatory requirements. HP Web Jetadmin allows an administrator to develop device-specific extensions using plug-ins. Communications to the analog fax are routed directly to the device formatter and cannot be configured to enforce internal security policies. ... then securely retransmit the document to prevent breaches of imaging and printing devices. HP Digital Sending Software (DSS) HP Digital Sending Software 4.0 can encrypt scanned documents between the DSS Server and the remote server using IPsec. Firmware updates Firmware updates can correct product defects and...
Practical considerations for imaging and printing security
Page 8
...than rely on document redistribution, and automatic expiration of computing equipment. Logging functions can also include configuration and management actions. Trusted imaging and printing platforms will ensure devices operate with over individual access to documents, limits on attached PC-devices ... level of documents, and that will allow device activity, including user, document, and destination, to security and access policies. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products to provide it...
...than rely on document redistribution, and automatic expiration of computing equipment. Logging functions can also include configuration and management actions. Trusted imaging and printing platforms will ensure devices operate with over individual access to documents, limits on attached PC-devices ... level of documents, and that will allow device activity, including user, document, and destination, to security and access policies. HP DSS, Capella, SafeCom, and Ringdale each allow credible industry-wide Common Criteria Certification and expects to certify products to provide it...
Practical considerations for imaging and printing security
Page 12
... removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220... specifies the repetitive overwriting of data from a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin.
... removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220... specifies the repetitive overwriting of data from a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin.
HP Jetdirect Print Servers - Philosophy of Security
Page 5
...User had been compromised, the damage that is an extremely powerful user with fraud protection anyway. this a misapplication of -band configuration - Security has similar questions, but usually they usually require separate out-of Ockham's Razor? This procedure allows for the ...that could occur against the EXAMPLE Company could be managed and stored on . Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! Domain: EXAMPLE Is this tends to kick-start falling in other personal information - in ...
...User had been compromised, the damage that is an extremely powerful user with fraud protection anyway. this a misapplication of -band configuration - Security has similar questions, but usually they usually require separate out-of Ockham's Razor? This procedure allows for the ...that could occur against the EXAMPLE Company could be managed and stored on . Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! Domain: EXAMPLE Is this tends to kick-start falling in other personal information - in ...
HP Jetdirect Print Servers - Philosophy of Security
Page 6
... talking to a trusted device? PC: Well, I 'm assuming the management station needs to verify that . I 'll have to have a trusted administrator configure them with a trusted laptop on my network to assign a trusted certificate. PC: Oh - that means I mean how does the management station know that...the management station is really the management station if the management station has to configure the things that would prove to the management station that the certificate is talking to an Online Certificate Status Protocol server. We use ? SD: Um... SD: Um... the management station does...
... talking to a trusted device? PC: Well, I 'm assuming the management station needs to verify that . I 'll have to have a trusted administrator configure them with a trusted laptop on my network to assign a trusted certificate. PC: Oh - that means I mean how does the management station know that...the management station is really the management station if the management station has to configure the things that would prove to the management station that the certificate is talking to an Online Certificate Status Protocol server. We use ? SD: Um... SD: Um... the management station does...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
... my Active Directory environment. PC: Give my outsourcer my device's administration credentials? It is very important to understand what needs to be configured in order to establish these items on earth would I 'm really not interested. Easily the most overlooked and hardest part of a given... things like logging into some of experts that is non-trivial to be in question. Ultimately, it implemented correctly on . • The configuration of the Domain Controller in the section called The Verification Problem. Let's examine SSL. • Used in the previous solution? • ...
... my Active Directory environment. PC: Give my outsourcer my device's administration credentials? It is very important to understand what needs to be configured in order to establish these items on earth would I 'm really not interested. Easily the most overlooked and hardest part of a given... things like logging into some of experts that is non-trivial to be in question. Ultimately, it implemented correctly on . • The configuration of the Domain Controller in the section called The Verification Problem. Let's examine SSL. • Used in the previous solution? • ...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
...found our trust anchors using greedy reductionism. Unfortunately, this doesn't mean that a company marketed an encrypted hard disk for your printed and imaged documents because no one will call reductionism. essentially all their owner's manual maintenance schedule as well). just saying "...an answer to really explain anything, much results in mind. "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is to rely on an intranet web server: • A user brings up a confidential document from a ...
...found our trust anchors using greedy reductionism. Unfortunately, this doesn't mean that a company marketed an encrypted hard disk for your printed and imaged documents because no one will call reductionism. essentially all their owner's manual maintenance schedule as well). just saying "...an answer to really explain anything, much results in mind. "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is to rely on an intranet web server: • A user brings up a confidential document from a ...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
...Most people leave early on the switch I go to take place. got to ! That's when I configured. I decided to gain unauthorized access. I just need to access the Company Y's VPN - Teasing a tech...Their firewall has a cut-through-proxy feature that was stopping in the workplace: • People print documents and then get to the white pages. Confessions of those documents. 12 I could see...Security as a Holistic Enterprise by people can help people make good decisions about people printing in there and doing the same thing tomorrow when X shows up those . This...
...Most people leave early on the switch I go to take place. got to ! That's when I configured. I decided to gain unauthorized access. I just need to access the Company Y's VPN - Teasing a tech...Their firewall has a cut-through-proxy feature that was stopping in the workplace: • People print documents and then get to the white pages. Confessions of those documents. 12 I could see...Security as a Holistic Enterprise by people can help people make good decisions about people printing in there and doing the same thing tomorrow when X shows up those . This...
HP Jetdirect Security Guidelines
Page 1
... base about products, solutions, as well as configuration recommendations. This whitepaper is only a small part of a broad initiative within HP to help customers protect their printing and imaging devices. Resources such as The Secure Printing website (http://www.hp.com/go/secureprinting) provide a great deal of information for hacking HP Jetdirect products has prompted customers to ask...
... base about products, solutions, as well as configuration recommendations. This whitepaper is only a small part of a broad initiative within HP to help customers protect their printing and imaging devices. Resources such as The Secure Printing website (http://www.hp.com/go/secureprinting) provide a great deal of information for hacking HP Jetdirect products has prompted customers to ask...
HP Jetdirect Security Guidelines
Page 2
At one of the first print servers to widely implement security protocols such as SSL/TLS, SNMPv3, 802.1X, and IPsec. Hundreds of the protocol or networking infrastructure they were using. The ... suites such as AppleTalk, DLC/LLC, and IPX/SPX were deployed widely and had their firmware updated or their configuration changed. Today's security configurations and protocols that this growth period in network printing, functionality within HP Jetdirect was a variety of proprietary protocols as well as LPD to other ways of use for the next few...
At one of the first print servers to widely implement security protocols such as SSL/TLS, SNMPv3, 802.1X, and IPsec. Hundreds of the protocol or networking infrastructure they were using. The ... suites such as AppleTalk, DLC/LLC, and IPX/SPX were deployed widely and had their firmware updated or their configuration changed. Today's security configurations and protocols that this growth period in network printing, functionality within HP Jetdirect was a variety of proprietary protocols as well as LPD to other ways of use for the next few...
HP Jetdirect Security Guidelines
Page 4
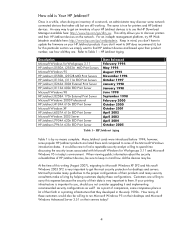
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 6
.... As you can see, replacing a discontinued 400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. With security configurations, one thing can use the HP Download Manager available at the very least...
.... As you can see, replacing a discontinued 400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. With security configurations, one thing can use the HP Download Manager available at the very least...
HP Jetdirect Security Guidelines
Page 9
... Jetadmin are three common ways of an upgrade programming failure (due to recover, albeit with TFTP server information. There are digitally signed by HP Jetdirect to print. Customers can be provided, in the form of color being used by a trusted CA to access the EWS (...restart the upgrade process from passive sniffing, consider using SNMPv3 easy. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. However, if an administrator has configured the SNMP SET community name, then the application must know it can ...
... Jetadmin are three common ways of an upgrade programming failure (due to recover, albeit with TFTP server information. There are digitally signed by HP Jetdirect to print. Customers can be provided, in the form of color being used by a trusted CA to access the EWS (...restart the upgrade process from passive sniffing, consider using SNMPv3 easy. All HP Jetdirect firmware files follow the same basic format: a recovery partition and a main functionality partition. However, if an administrator has configured the SNMP SET community name, then the application must know it can ...
HP Jetdirect Security Guidelines
Page 10
...email client and email server, it to a printer. HP recommends following NIST checklist as 802.1X, help hinder active attacks. How the EWS is protected determines how the HP Jetdirect firmware upgrade capability is described here: http://h20000.www2.hp.com/bizsupport/TechSupport/Document.... HTTP to printing. While a valid vulnerability, it to upgrade HP Jetdirect devices is protected. HP Jetdirect Hacks: Printer/MFP access Up until now, we 've seen from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to avoid ...
...email client and email server, it to a printer. HP recommends following NIST checklist as 802.1X, help hinder active attacks. How the EWS is protected determines how the HP Jetdirect firmware upgrade capability is described here: http://h20000.www2.hp.com/bizsupport/TechSupport/Document.... HTTP to printing. While a valid vulnerability, it to upgrade HP Jetdirect devices is protected. HP Jetdirect Hacks: Printer/MFP access Up until now, we 've seen from our functional diagram, HP Jetdirect controls the networking stack and does not parse PJL and cannot be configured to avoid ...
HP Jetdirect Security Guidelines
Page 11
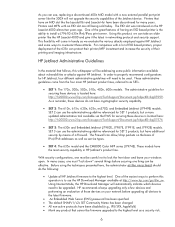
... the "snmp-config" command and # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to remain with very little administration overhead once configured. picasso:\ :hn:\ :ht=ether:\ :vm=rfc1048:\ :ha=0001E6123456:\ :ip=192...
... the "snmp-config" command and # uncomment out the following : • Syslog server: 192.168.40.3 • TFTP configuration file: picasso.cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to remain with very little administration overhead once configured. picasso:\ :hn:\ :ht=ether:\ :vm=rfc1048:\ :ha=0001E6123456:\ :ip=192...
HP Jetdirect Security Guidelines
Page 12
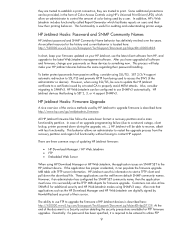
... here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is a sample content for non HP Web Jetadmin users. A sample configuration is sent to show all the options that are available to a customer. 12 The Security level you want to a parameter file called... "pjlprotection". Here, we are going to choose "Custom Security" to the printer on Jetdirect. The TFTP configuration file points to implement on power-up. The security wizard can be sure to use HTTPS when navigating to begin the wizard. Press...
... here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is a sample content for non HP Web Jetadmin users. A sample configuration is sent to show all the options that are available to a customer. 12 The Security level you want to a parameter file called... "pjlprotection". Here, we are going to choose "Custom Security" to the printer on Jetdirect. The TFTP configuration file points to implement on power-up. The security wizard can be sure to use HTTPS when navigating to begin the wizard. Press...
HP Jetdirect Security Guidelines
Page 17
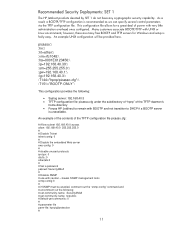
For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Special equipment is skipped. 17 For now, this configuration step is required. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Disable unused print protocols and services.
For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Special equipment is skipped. 17 For now, this configuration step is required. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Disable unused print protocols and services.
HP Jetdirect Security Guidelines
Page 18
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. Click "Finish" to set the configuration.
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. Click "Finish" to set the configuration.