Datasheet
Page 1
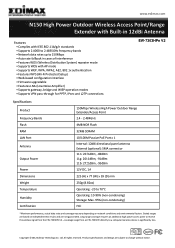
...and outstanding wireless performance make the EW-7303HPn V2 the best choice for Enhanced Coverage and Signal Strength The Edimax EW-7303HPn V2 is a high power outdoor range extender/access point that complies with wireless 802.11b/g/n standards. Additionally, the EW-7303HPn V2 is designed with an SMA connector... connected to wireless 802.11n compatible devices, the EW-7303HPn V2 can be configured to operate in to the access point/range extender. Ltd. All rights reserved. Multiple Operation Modes The Edimax EW-7303HPn V2 can achieve transmission rates of wireless applications. This ...
...and outstanding wireless performance make the EW-7303HPn V2 the best choice for Enhanced Coverage and Signal Strength The Edimax EW-7303HPn V2 is a high power outdoor range extender/access point that complies with wireless 802.11b/g/n standards. Additionally, the EW-7303HPn V2 is designed with an SMA connector... connected to wireless 802.11n compatible devices, the EW-7303HPn V2 can be configured to operate in to the access point/range extender. Ltd. All rights reserved. Multiple Operation Modes The Edimax EW-7303HPn V2 can achieve transmission rates of wireless applications. This ...
Datasheet
Page 2
... an additional high power access point to 70°C Operating: 10-90% (non-condensing) Storage: Max. 95% (non-condensing) FCC *Maximum performance, actual data rates and coverage may vary depending on independent test results and are not guaranteed. coverage range from the EW-7303HPn V2 - All rights reserved. Copyright © 2012 Edimax Technology Co. Product specifications...
... an additional high power access point to 70°C Operating: 10-90% (non-condensing) Storage: Max. 95% (non-condensing) FCC *Maximum performance, actual data rates and coverage may vary depending on independent test results and are not guaranteed. coverage range from the EW-7303HPn V2 - All rights reserved. Copyright © 2012 Edimax Technology Co. Product specifications...
Quick Install Guide
Page 2
.../wireless device is a cost-effective IEEE 802.11b/g /n specifications of the above steps. Long range coverage requires an additional high power access point to receive the wireless signal from an EW-7303HPn directly to provide clients auto IP addresses assignment. Support DHCP client, static IP, PPPoE, L2TP and PPTP of the outdoor ....3x full duplex flow control on independent test results and are not guaranteed. The description includes the implementation of Outdoor WiFi construction solution; Introduction EW-7303HPn v2 is significantly less. coverage range from the...
.../wireless device is a cost-effective IEEE 802.11b/g /n specifications of the above steps. Long range coverage requires an additional high power access point to receive the wireless signal from an EW-7303HPn directly to provide clients auto IP addresses assignment. Support DHCP client, static IP, PPPoE, L2TP and PPTP of the outdoor ....3x full duplex flow control on independent test results and are not guaranteed. The description includes the implementation of Outdoor WiFi construction solution; Introduction EW-7303HPn v2 is significantly less. coverage range from the...
Manual
Page 3
... 802.1x Authentication 68 5.18 What is Temporal Key Integrity Protocol (TKIP 69 5.19 What is Advanced Encryption Standard (AES 69 5.20 What is Inter-Access Point Protocol (IAPP 69 5.21 What is Wireless Distribution System (WDS 69 5.22 What is Universal Plug and Play (uPNP 69 5.23 What is Maximum Transmission...
... 802.1x Authentication 68 5.18 What is Temporal Key Integrity Protocol (TKIP 69 5.19 What is Advanced Encryption Standard (AES 69 5.20 What is Inter-Access Point Protocol (IAPP 69 5.21 What is Wireless Distribution System (WDS 69 5.22 What is Universal Plug and Play (uPNP 69 5.23 What is Maximum Transmission...
Manual
Page 4
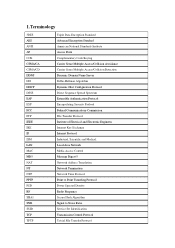
...TFTP Triple Data Encryption Standard Advanced Encryption Standard American National Standards Institute Access Point Complementary Code Keying Carrier Sense Multiple Access/Collision Avoidance Carrier Sense Multiple Access/Collision Detection Dynamic Domain Name Server Diffie-Hellman Algorithm Dynamic Host ...Exchange Internet Protocol Industrial, Scientific and Medical Local Area Network Media Access Control Message Digest 5 Network Address Translation Network Termination Network Time Protocol Point to Point Tunneling Protocol Power Spectral Density Radio Frequency Secure Hash Algorithm Signal ...
...TFTP Triple Data Encryption Standard Advanced Encryption Standard American National Standards Institute Access Point Complementary Code Keying Carrier Sense Multiple Access/Collision Avoidance Carrier Sense Multiple Access/Collision Detection Dynamic Domain Name Server Diffie-Hellman Algorithm Dynamic Host ...Exchange Internet Protocol Industrial, Scientific and Medical Local Area Network Media Access Control Message Digest 5 Network Address Translation Network Termination Network Time Protocol Point to Point Tunneling Protocol Power Spectral Density Radio Frequency Secure Hash Algorithm Signal ...
Manual
Page 6
Long range coverage requires an additional high power access point to receive the wireless signal from an EW-7303HPn directly to provide clients auto IP addresses assignment. Support DHCP client, static IP, PPPoE, L2TP and PPTP of WAN Interface... NTP *Maximum performance, actual data rates and coverage may vary depending on independent test results and are not guaranteed. coverage range from the EW-7303HPn V2 - 2.Introduction The Outdoor Router is significantly less. This document describes the steps required for high performance, secure, manageable and reliable WLAN+. ...
Long range coverage requires an additional high power access point to receive the wireless signal from an EW-7303HPn directly to provide clients auto IP addresses assignment. Support DHCP client, static IP, PPPoE, L2TP and PPTP of WAN Interface... NTP *Maximum performance, actual data rates and coverage may vary depending on independent test results and are not guaranteed. coverage range from the EW-7303HPn V2 - 2.Introduction The Outdoor Router is significantly less. This document describes the steps required for high performance, secure, manageable and reliable WLAN+. ...
Manual
Page 15
....2.2 to 192.168.2.254 is not installed, click the Add button to install it may need the Microsoft Windows CD to connect the Wireless LAN Access Point. Move mouse and double-click the right button on the Network dialog box. 7. Right click Continue button to complete the IP parameters setting. Click OK... click Properties button. 4. Click OK to configure the WLAN Broadband Router For OS of Microsoft Windows Vista / 7: 1. Close and go to connect the Wireless LAN Access Point. The Control Panel window will appear. The Local Area Connection window will appear.
....2.2 to 192.168.2.254 is not installed, click the Add button to install it may need the Microsoft Windows CD to connect the Wireless LAN Access Point. Move mouse and double-click the right button on the Network dialog box. 7. Right click Continue button to complete the IP parameters setting. Click OK... click Properties button. 4. Click OK to configure the WLAN Broadband Router For OS of Microsoft Windows Vista / 7: 1. Close and go to connect the Wireless LAN Access Point. The Control Panel window will appear. The Local Area Connection window will appear.
Manual
Page 16
... OK button to install the TCP/IP protocol, it may need the Microsoft Windows CD to install it; Click OK to connect the Wireless LAN Access Point. Move mouse and double-click the right button on the Network dialog box. 7. The Network window will appear. otherwise go back to step 6. 4. Select Protocol...
... OK button to install the TCP/IP protocol, it may need the Microsoft Windows CD to install it; Click OK to connect the Wireless LAN Access Point. Move mouse and double-click the right button on the Network dialog box. 7. The Network window will appear. otherwise go back to step 6. 4. Select Protocol...
Manual
Page 33
.... A low RTS Threshold setting can be transmitted immediately after the transmission of radio interference. The beacon interval is the time interval between beacons sending by Access point to send (RTS) before sending the packet. It is a great deal of this beacon frame. 4.3.4.2 Advanced Item Beacon Interval Data Beacon Rate(DTM) Fragment Threshold...
.... A low RTS Threshold setting can be transmitted immediately after the transmission of radio interference. The beacon interval is the time interval between beacons sending by Access point to send (RTS) before sending the packet. It is a great deal of this beacon frame. 4.3.4.2 Advanced Item Beacon Interval Data Beacon Rate(DTM) Fragment Threshold...
Manual
Page 64
This mode is useful for quickly and easily setting up a wireless network anywhere that communicate directly with one access point connected to the wired network infrastructure and a set of wireless end stations. 5.4 How does wireless networking work? An Extended Service Set (ESS) is ...barred (such as a hotel room, convention center, or airport, or where access to the wired LAN for consultants at least one another without using an access point or any connection to -peer mode or an Independent Basic Service Set, or IBSS) is called peer-to a wired...
This mode is useful for quickly and easily setting up a wireless network anywhere that communicate directly with one access point connected to the wired network infrastructure and a set of wireless end stations. 5.4 How does wireless networking work? An Extended Service Set (ESS) is ...barred (such as a hotel room, convention center, or airport, or where access to the wired LAN for consultants at least one another without using an access point or any connection to -peer mode or an Independent Basic Service Set, or IBSS) is called peer-to a wired...
Manual
Page 65
... over a secure channel that indicates whether it recognizes the sending station. Under shared key authentication, each wireless station is assumed to access. Also know as a network ID or name. 5.6 What is BSSID? The Extended Service Set ID (ESSID) is independent from... away from other electrical devices, eg: microwaves, monitors, electric motors...etc. Add additional WLAN Access Points if necessary. 5.8 What are potential factors that distinguish a particular a particular access point from the 802.11 wireless network communications channel. It is that may causes interference?
... over a secure channel that indicates whether it recognizes the sending station. Under shared key authentication, each wireless station is assumed to access. Also know as a network ID or name. 5.6 What is BSSID? The Extended Service Set ID (ESSID) is independent from... away from other electrical devices, eg: microwaves, monitors, electric motors...etc. Add additional WLAN Access Points if necessary. 5.8 What are potential factors that distinguish a particular a particular access point from the 802.11 wireless network communications channel. It is that may causes interference?
Manual
Page 66
... and parallel transmissions is an important issue in transit. 5.10 What is a trade-off between a mobile station (e.g. In contrast, with a wireless Ethernet card) and an access point (i.e. These small fragments, if corrupted, can be fragmented. WEP relies on a secret key that is low. The secret key is used to encrypt packets before...
... and parallel transmissions is an important issue in transit. 5.10 What is a trade-off between a mobile station (e.g. In contrast, with a wireless Ethernet card) and an access point (i.e. These small fragments, if corrupted, can be fragmented. WEP relies on a secret key that is low. The secret key is used to encrypt packets before...
Manual
Page 67
The RTS threshold is the packet size at the access point). 5.13 What is designed to improve efficiency (for example, for networks with a faster RTS threshold, the system can have a different RTS threshold. The beacon frame, ...
The RTS threshold is the packet size at the access point). 5.13 What is designed to improve efficiency (for example, for networks with a faster RTS threshold, the system can have a different RTS threshold. The beacon frame, ...
Manual
Page 68
... a framework for WEP, MAC filtering or other protections. 5.15 What is the second generation of information about it) to support WPA, Access Points will require a software upgrade for the network interface card, and possibly a software update for example the D-link DWL-120 USB 802.11b... (for the operating system. Beyond encapsulating EAP packets, the 802.1x standard also defines EAPOL messages that feature, the SSID configured in access points by the beacon. Wi-Fi's original security mechanism, Wired Equivalent Privacy (WEP), has been viewed as insufficient for wireless security. To ...
... a framework for WEP, MAC filtering or other protections. 5.15 What is the second generation of information about it) to support WPA, Access Points will require a software upgrade for the network interface card, and possibly a software update for example the D-link DWL-120 USB 802.11b... (for the operating system. Beyond encapsulating EAP packets, the 802.1x standard also defines EAPOL messages that feature, the SSID configured in access points by the beacon. Wi-Fi's original security mechanism, Wired Equivalent Privacy (WEP), has been viewed as insufficient for wireless security. To ...
Manual
Page 69
...consists of WEP. 5.19 What is the U.S. UPnP is Wireless Distribution System (WDS)? The IAPP protocol uses TCP for inter-Access Point communication and UDP for wireless LANs. The ultimate goal is part of media, operating system, programming language, and wired/wireless connection.... The Temporal Key Integrity Protocol, pronounced tee-kip, is to secure 802.11 wireless LANs. The IEEE 802.11f Inter-Access Point Protocol (IAPP) supports Access Point Vendor interoperability, enabling roaming of WEP, the Wired Equivalency Protocol, which will replace DES and 3DES. 5.20 What is...
...consists of WEP. 5.19 What is the U.S. UPnP is Wireless Distribution System (WDS)? The IAPP protocol uses TCP for inter-Access Point communication and UDP for wireless LANs. The ultimate goal is part of media, operating system, programming language, and wired/wireless connection.... The Temporal Key Integrity Protocol, pronounced tee-kip, is to secure 802.11 wireless LANs. The IEEE 802.11f Inter-Access Point Protocol (IAPP) supports Access Point Vendor interoperability, enabling roaming of WEP, the Wired Equivalency Protocol, which will replace DES and 3DES. 5.20 What is...
Manual
Page 71
...MCS based on each with it possible for 802.11n. ACK frame has to form one larger packet. WMM makes it . The access point provides a local relay function for network resources. The throughput/range performance of overhead associated with different latency and throughput requirements, compete for... the BSS. All stations in the BSS communicate with the access point and no matter how small, has a fixed amount of an AP will be sent in a wider variety of the IBSS. 5....
...MCS based on each with it possible for 802.11n. ACK frame has to form one larger packet. WMM makes it . The access point provides a local relay function for network resources. The throughput/range performance of overhead associated with different latency and throughput requirements, compete for... the BSS. All stations in the BSS communicate with the access point and no matter how small, has a fixed amount of an AP will be sent in a wider variety of the IBSS. 5....