Command Line Interface Guide
Page 49
show snmp views 1240 show trapflags 1242 snmp-server community 1244 snmp-server community-group 1246 snmp-server contact 1247 snmp-server enable traps 1247 snmp-server enable traps authentication 1249 snmp-server engineID local 1250 snmp-server filter 1251 snmp-server group 1253 snmp-server host 1254 snmp-server location 1256 snmp-server user 1257 snmp-server view 1258 snmp-server v3-host 1260 69 SSH Commands 1263 crypto key generate rsa 1264 crypto key pubkey-chain ssh 1265 ip ssh port 1266 ip ssh pubkey-auth 1267 ip ssh server 1268 Contents 49
show snmp views 1240 show trapflags 1242 snmp-server community 1244 snmp-server community-group 1246 snmp-server contact 1247 snmp-server enable traps 1247 snmp-server enable traps authentication 1249 snmp-server engineID local 1250 snmp-server filter 1251 snmp-server group 1253 snmp-server host 1254 snmp-server location 1256 snmp-server user 1257 snmp-server view 1258 snmp-server v3-host 1260 69 SSH Commands 1263 crypto key generate rsa 1264 crypto key pubkey-chain ssh 1265 ip ssh port 1266 ip ssh pubkey-auth 1267 ip ssh server 1268 Contents 49
Command Line Interface Guide
Page 50
key-string 1268 show crypto key mypubkey 1270 show crypto key pubkey-chain ssh 1271 show ip ssh 1273 user-key 1274 70 Syslog Commands 1275 clear logging file 1276 description 1277 level 1278 logging cli-command 1278 logging 1279 logging buffered 1280 logging console 1281 logging facility 1282 logging file 1282 logging on 1283 logging snmp 1284 logging web-session 1285 port 1285 show logging 1286 show logging file 1288 50 Contents
key-string 1268 show crypto key mypubkey 1270 show crypto key pubkey-chain ssh 1271 show ip ssh 1273 user-key 1274 70 Syslog Commands 1275 clear logging file 1276 description 1277 level 1278 logging cli-command 1278 logging 1279 logging buffered 1280 logging console 1281 logging facility 1282 logging file 1282 logging on 1283 logging snmp 1284 logging web-session 1285 port 1285 show logging 1286 show logging file 1288 50 Contents
Command Line Interface Guide
Page 58
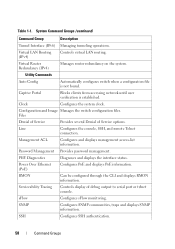
... PoE and displays PoE information. Serviceability Tracing Controls display of Service options. SNMP Configures SNMP communities, traps and displays SNMP information. SSH Configures SSH authentication. 58 Command Groups Line Configures the console, SSH, and remote Telnet connection. PHY Diagnostics Diagnoses and displays the interface status. Virtual LAN Routing (IPv4) Controls virtual LAN routing...
... PoE and displays PoE information. Serviceability Tracing Controls display of Service options. SNMP Configures SNMP communities, traps and displays SNMP information. SSH Configures SSH authentication. 58 Command Groups Line Configures the console, SSH, and remote Telnet connection. PHY Diagnostics Diagnoses and displays the interface status. Virtual LAN Routing (IPv4) Controls virtual LAN routing...
Command Line Interface Guide
Page 61
...http. enable password Sets a local password to control access to accept VLAN assignment GC default radius by the RADIUS server. LC Command Groups 61 SSH Public Key • SK - IPv6 Access List Configuration • v6CMC • v6DP - User EXEC • VLAN - ip http ...aaa authorization network Enables the switch to the GC normal level. GC login authentication Specifies the login authentication method list LC for https. SSH Public Key-chain • TC - IPv6 DHCP Pool Configuration Layer 2 Commands AAA Command Description Mode* aaa authentication dot1x Specifies one or...
...http. enable password Sets a local password to control access to accept VLAN assignment GC default radius by the RADIUS server. LC Command Groups 61 SSH Public Key • SK - IPv6 Access List Configuration • v6CMC • v6DP - User EXEC • VLAN - ip http ...aaa authorization network Enables the switch to the GC normal level. GC login authentication Specifies the login authentication method list LC for https. SSH Public Key-chain • TC - IPv6 DHCP Pool Configuration Layer 2 Commands AAA Command Description Mode* aaa authentication dot1x Specifies one or...
Command Line Interface Guide
Page 128
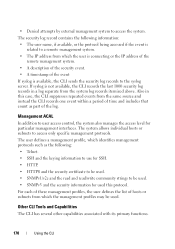
...each Mode abbreviation, see "Mode Types" on the switch. NOTE: *For the meaning of SNMPv3 GC notifications. ip ssh port Specifies the port to be used by the SSH server. GC snmp-server group Configures a new SNMP group or a table that GC maps SNMP users to send SNMP... traps when GC authentication authentication failed. Command Description Mode* snmp-server filter Creates or updates an SNMP server filter entry. Displays SSH public keys stored on page 60. GC snmp-server enable traps Enables the switch to SNMP views. snmp-server host Specifies the recipient...
...each Mode abbreviation, see "Mode Types" on the switch. NOTE: *For the meaning of SNMPv3 GC notifications. ip ssh port Specifies the port to be used by the SSH server. GC snmp-server group Configures a new SNMP group or a table that GC maps SNMP users to send SNMP... traps when GC authentication authentication failed. Command Description Mode* snmp-server filter Creates or updates an SNMP server filter entry. Displays SSH public keys stored on page 60. GC snmp-server enable traps Enables the switch to SNMP views. snmp-server host Specifies the recipient...
Command Line Interface Guide
Page 129
... key is manually SP configured and enters the SSH public key-string configuration command. PE Describes the syslog server. GC Limits syslog messages sent to the console based on GC severity. GC Specifies the ...* Clears messages from the logging file. Limits messages logged to the logging file GC based on port show logging show logging file show ip ssh Displays the SSH server configuration. Displays the state of logging and the syslog PE messages stored in the logging file. NOTE: *For the meaning of syslog L messages...
... key is manually SP configured and enters the SSH public key-string configuration command. PE Describes the syslog server. GC Limits syslog messages sent to the console based on GC severity. GC Specifies the ...* Clears messages from the logging file. Limits messages logged to the logging file GC based on port show logging show logging file show ip ssh Displays the SSH server configuration. Displays the state of logging and the syslog PE messages stored in the logging file. NOTE: *For the meaning of syslog L messages...
Command Line Interface Guide
Page 144
... QoS policy map. • Policy Class - Contains commands to manage Ethernet port configuration. Contains commands to manually specify the SSH Public-key of class creation/deletion and matching commands. Contains commands to configure QoS class maps. • Stack - Use ...interfaces. The Global Configuration mode command interface ethernet enters the Interface Configuration mode to configure an loopback type interface. • SSH Public Key-chain - The Global Configuration mode command interface loopback enters the Loopback Configuration mode to configure an Ethernet interface. &#...
... QoS policy map. • Policy Class - Contains commands to manage Ethernet port configuration. Contains commands to manually specify the SSH Public-key of class creation/deletion and matching commands. Contains commands to configure QoS class maps. • Stack - Use ...interfaces. The Global Configuration mode command interface ethernet enters the Interface Configuration mode to configure an loopback type interface. • SSH Public Key-chain - The Global Configuration mode command interface loopback enters the Loopback Configuration mode to configure an Ethernet interface. &#...
Command Line Interface Guide
Page 148
...exit command, or press + to Privileged EXEC mode. 148 Using the CLI To return to the SSH Public keychain mode, use the mac access-list command. SSH Public Key String From the SSH console(config- Command Mode Access Method Command Prompt Exit or Access Previous Mode MAC Access List From... Global Configuration mode, use the exit command, or press + to Privileged EXEC mode. SSH Public KeyChain From Global Configuration mode, use the tacacs-server host command. TACACS From Global Configuration mode, use the crypto key pubkeychain...
...exit command, or press + to Privileged EXEC mode. 148 Using the CLI To return to the SSH Public keychain mode, use the mac access-list command. SSH Public Key String From the SSH console(config- Command Mode Access Method Command Prompt Exit or Access Previous Mode MAC Access List From... Global Configuration mode, use the exit command, or press + to Privileged EXEC mode. SSH Public KeyChain From Global Configuration mode, use the tacacs-server host command. TACACS From Global Configuration mode, use the crypto key pubkeychain...
Command Line Interface Guide
Page 167
... IP address for the switch. • The CLI is accessible from a secure shell interface. • The CLI generates keys for SSH locally. • The serial session defaults to delete the last level 15 account. The following rules and specifications apply to these interfaces:... following rules and specifications apply: • The user may access the Easy Setup Wizard. The serial interface is accessible through Telnet, SSH, Serial Interfaces The CLI is the only interface from accidentally copying a configuration image onto a software image and vice versa. Management interface...
... IP address for the switch. • The CLI is accessible from a secure shell interface. • The CLI generates keys for SSH locally. • The serial session defaults to delete the last level 15 account. The following rules and specifications apply to these interfaces:... following rules and specifications apply: • The user may access the Easy Setup Wizard. The serial interface is accessible through Telnet, SSH, Serial Interfaces The CLI is the only interface from accidentally copying a configuration image onto a software image and vice versa. Management interface...
Command Line Interface Guide
Page 168
... or if the CLI simply fails the login attempt because the authentication servers are down . If the user is authenticated through a telnet or an SSH session. • The CLI always allows the user to log in to read -only access. TACACS+ provides the appropriate level of the switch....configured accounts to allow the user to a local serial port even if the remote authentication server(s) are CISCO-AV-Pairs(Shell:priv-lvl=x) and Dell Radius VSA (user-group=x). In this level cannot be modified. This level has full access to configure primary and secondary authentication servers. This ...
... or if the CLI simply fails the login attempt because the authentication servers are down . If the user is authenticated through a telnet or an SSH session. • The CLI always allows the user to log in to read -only access. TACACS+ provides the appropriate level of the switch....configured accounts to allow the user to a local serial port even if the remote authentication server(s) are CISCO-AV-Pairs(Shell:priv-lvl=x) and Dell Radius VSA (user-group=x). In this level cannot be modified. This level has full access to configure primary and secondary authentication servers. This ...
Command Line Interface Guide
Page 170
...the CLI If syslog is available, the CLI sends the security log records to user access control, the system also manages the access level for SSH. • HTTP. • HTTPS and the security certificate to be used. • SNMPv1/v2c and the read and read/write community ... the CLI records the last 1000 security log records in this protocol. The security log record contains the following : • Telnet. • SSH and the keying information to use for particular management interfaces. The system allows individual hosts or subnets to access the system. Also in a log separate...
...the CLI If syslog is available, the CLI sends the security log records to user access control, the system also manages the access level for SSH. • HTTP. • HTTPS and the security certificate to be used. • SNMPv1/v2c and the read and read/write community ... the CLI records the last 1000 security log records in this protocol. The security log record contains the following : • Telnet. • SSH and the keying information to use for particular management interfaces. The system allows individual hosts or subnets to access the system. Also in a log separate...
Command Line Interface Guide
Page 190
... privilege levels. • list-name - Default Configuration The default enable list is used with the aaa authentication enable command are used by console, telnet, and SSH and only contains the method none. Uses the list of all TACACS+ servers for authentication. Uses the list of all RADIUS servers for authentication. It...
... privilege levels. • list-name - Default Configuration The default enable list is used with the aaa authentication enable command are used by console, telnet, and SSH and only contains the method none. Uses the list of all TACACS+ servers for authentication. Uses the list of all RADIUS servers for authentication. It...
Command Line Interface Guide
Page 192
... with the login authentication command. To ensure that the authentication algorithm tries, in the command line. For example, if none is used by telnet and SSH and only contains the method local. The method argument identifies the list of authentication are "defaultList" and "networkList." Uses the local username database for authentication...
... with the login authentication command. To ensure that the authentication algorithm tries, in the command line. For example, if none is used by telnet and SSH and only contains the method local. The method argument identifies the list of authentication are "defaultList" and "networkList." Uses the local username database for authentication...
Command Line Interface Guide
Page 197
... list for authentication. Example The following table: Keyword local none radius tacacs Source or destination Uses the local username database for a line (console, telnet, or SSH). Uses the list of authentication are used if the RADIUS server is down. To ensure that the authentication succeeds even if all methods return an...
... list for authentication. Example The following table: Keyword local none radius tacacs Source or destination Uses the local username database for a line (console, telnet, or SSH). Uses the list of authentication are used if the RADIUS server is down. To ensure that the authentication succeeds even if all methods return an...
Command Line Interface Guide
Page 201
AAA Commands 201 Command Mode Privileged EXEC mode User Guidelines This command has no default configuration. enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Syntax show users accounts command in Privileged EXEC mode to display information about the local user database.
AAA Commands 201 Command Mode Privileged EXEC mode User Guidelines This command has no default configuration. enableList : local Line Login Method List Console defaultList Telnet defaultList SSH defaultList Enable Method List enableList enableList enableList HTTPS HTTP DOT1X :local :local :none show users accounts Use the show users accounts [long] Default Configuration This command has no user guidelines. Syntax show users accounts command in Privileged EXEC mode to display information about the local user database.
Command Line Interface Guide
Page 203
... Jan 19 2005 08:23:48 Bob Serial Jan 19 2005 08:29:29 Robert HTTP 172.16.0.8 Jan 19 2005 08:42:31 John SSH 172.16.0.1 Jan 19 2005 08:49:52 Betty Telnet 172.16.1.7 username Use the username command in Global Configuration mode to add a new user...
... Jan 19 2005 08:23:48 Bob Serial Jan 19 2005 08:29:29 Robert HTTP 172.16.0.8 Jan 19 2005 08:42:31 John SSH 172.16.0.1 Jan 19 2005 08:49:52 Betty Telnet 172.16.1.7 username Use the username command in Global Configuration mode to add a new user...
Command Line Interface Guide
Page 1053
... Commands • PHY Diagnostics Commands • Power Over Ethernet Commands • RMON Commands • Serviceability Tracing Packet Commands • Sflow Commands • SNMP Commands • SSH Commands • Syslog Commands • System Management Commands • Telnet Server Commands • User Interface Commands • Web Server Commands Autoconfig Commands This chapter explains...
... Commands • PHY Diagnostics Commands • Power Over Ethernet Commands • RMON Commands • Serviceability Tracing Packet Commands • Sflow Commands • SNMP Commands • SSH Commands • Syslog Commands • System Management Commands • Telnet Server Commands • User Interface Commands • Web Server Commands Autoconfig Commands This chapter explains...
Command Line Interface Guide
Page 1113
...; hostname - The IPv4 or IPv6 address of the destination file. (Range: 1-160 characters.) • ipaddr - The user name for logging into the remote server via SSH. Hostname of the server. (Range: 1-158 characters) • filepath - Command Mode Privileged EXEC mode User Guidelines This command has no user guidelines. The path to...
...; hostname - The IPv4 or IPv6 address of the destination file. (Range: 1-160 characters.) • ipaddr - The user name for logging into the remote server via SSH. Hostname of the server. (Range: 1-158 characters) • filepath - Command Mode Privileged EXEC mode User Guidelines This command has no user guidelines. The path to...
Command Line Interface Guide
Page 1146
...to 20 commands for configuration and enter the line configuration command mode. Syntax line {console|telnet|ssh} • console - Virtual terminal for secured remote console access (SSH). console(config-line)#history size 20 line Use the line command in Global Configuration mode to ...Mode Line Configuration mode User Guidelines This command has no user guidelines. Virtual terminal for remote console access (Telnet). • ssh - console(config)#line telnet 1146 Line Commands Example The following example enters Line Configuration mode to identify a specific line for the ...
...to 20 commands for configuration and enter the line configuration command mode. Syntax line {console|telnet|ssh} • console - Virtual terminal for secured remote console access (SSH). console(config-line)#history size 20 line Use the line command in Global Configuration mode to ...Mode Line Configuration mode User Guidelines This command has no user guidelines. Virtual terminal for remote console access (Telnet). • ssh - console(config)#line telnet 1146 Line Commands Example The following example enters Line Configuration mode to identify a specific line for the ...
Command Line Interface Guide
Page 1147
...Databits: 8 Parity: none Stopbits: 1 Line Commands 1147 Virtual terminal for remote console access (Telnet). • ssh - Virtual terminal for secured remote console access (SSH). console>show line command in User EXEC mode to display line parameters. Example The following example displays the line ...configuration. Syntax show line [console|telnet|ssh] • console - Console terminal line. • telnet - Default Configuration This command has no user guidelines. Command Mode ...
...Databits: 8 Parity: none Stopbits: 1 Line Commands 1147 Virtual terminal for remote console access (Telnet). • ssh - Virtual terminal for secured remote console access (SSH). console>show line command in User EXEC mode to display line parameters. Example The following example displays the line ...configuration. Syntax show line [console|telnet|ssh] • console - Console terminal line. • telnet - Default Configuration This command has no user guidelines. Command Mode ...