Command Line Interface Guide
Page 18
show (mst 372 exit (mst 373 abort (mst 374 show spanning-tree 375 spanning-tree guard root 389 29 SSH Commands 391 ip ssh port 391 ip ssh server 391 crypto key generate dsa 392 crypto key generate rsa 393 ip ssh pubkey-auth 393 crypto key pubkey-chain ssh 394 user-key 395 key-string 396 show ip ssh 398 show crypto key mypubkey 399 show crypto key pubkey-chain ssh 400 30 Syslog Commands 401 logging on 401 logging 401 logging console 403 logging buffered 404 logging buffered size 404 clear logging 405 logging file 406 18 Contents
show (mst 372 exit (mst 373 abort (mst 374 show spanning-tree 375 spanning-tree guard root 389 29 SSH Commands 391 ip ssh port 391 ip ssh server 391 crypto key generate dsa 392 crypto key generate rsa 393 ip ssh pubkey-auth 393 crypto key pubkey-chain ssh 394 user-key 395 key-string 396 show ip ssh 398 show crypto key mypubkey 399 show crypto key pubkey-chain ssh 400 30 Syslog Commands 401 logging on 401 logging 401 logging console 403 logging buffered 404 logging buffered size 404 clear logging 405 logging file 406 18 Contents
Command Line Interface Guide
Page 25
Entering a question mark "?" Using the CLI 25 The standard order to access the modes is divided into different command modes. at the system prompt (console prompt) displays a list of specific commands. The following figure illustrates the command mode access path. Using the CLI This chapter describes how to start using the CLI and describes the...
Entering a question mark "?" Using the CLI 25 The standard order to access the modes is divided into different command modes. at the system prompt (console prompt) displays a list of specific commands. The following figure illustrates the command mode access path. Using the CLI This chapter describes how to start using the CLI and describes the...
Command Line Interface Guide
Page 26
... restricted on a global level. To enter the next level, the Privileged EXEC mode, a password is the User EXEC mode. In general, the User EXEC commands allow the user to the device Configuration mode. Only a limited subset of the device host name followed by the angle bracket (>). User EXEC Mode After ... User EXEC mode and provides access to perform basic tests, and list system information. The Interface Configuration mode configures specific interfaces in the User EXEC command mode unless the user is reserved for tasks that are available in the User EXEC mode...
... restricted on a global level. To enter the next level, the Privileged EXEC mode, a password is the User EXEC mode. In general, the User EXEC commands allow the user to the device Configuration mode. Only a limited subset of the device host name followed by the angle bracket (>). User EXEC Mode After ... User EXEC mode and provides access to perform basic tests, and list system information. The Interface Configuration mode configures specific interfaces in the User EXEC command mode unless the user is reserved for tasks that are available in the User EXEC mode...
Command Line Interface Guide
Page 27
...Global Configuration mode. For example, the exit command is password protected to enter the Global Configuration mode. Using the CLI 27 The password is used to prevent unauthorized use the disable command. Console# To return from the Interface Configuration mode... the screen and is Console unless it was changed using the hostname command in the Global Configuration mode. Global Configuration Mode Global Configuration mode commands apply to the User EXEC mode: Console> enable Enter Password: ****** Console# Console# disable Console> The exit (mst) command is displayed as a whole...
...Global Configuration mode. For example, the exit command is password protected to enter the Global Configuration mode. Using the CLI 27 The password is used to prevent unauthorized use the disable command. Console# To return from the Interface Configuration mode... the screen and is Console unless it was changed using the hostname command in the Global Configuration mode. Global Configuration Mode Global Configuration mode commands apply to the User EXEC mode: Console> enable Enter Password: ****** Console# Console# disable Console> The exit (mst) command is displayed as a whole...
Command Line Interface Guide
Page 28
... The Global Configuration mode prompt is used to the Privileged EXEC mode: Console# Console# configure Console(config)# exit Console# Interface Configuration Mode and Specific Configuration Modes Interface Configuration mode commands modify specific interface operations. The following example illustrates how to access the .... The Global Configuration mode prompt consists of these commands are the same as the commands in the Ethernet interface mode, and are the Interface Configuration modes: • Line Interface - Console(config)# To return from the Global Configuration mode ...
... The Global Configuration mode prompt is used to the Privileged EXEC mode: Console# Console# configure Console(config)# exit Console# Interface Configuration Mode and Specific Configuration Modes Interface Configuration mode commands modify specific interface operations. The following example illustrates how to access the .... The Global Configuration mode prompt consists of these commands are the same as the commands in the Ethernet interface mode, and are the Interface Configuration modes: • Line Interface - Console(config)# To return from the Global Configuration mode ...
Command Line Interface Guide
Page 29
... for Emulation mode. d Select Terminal keys for Ryan, is installed. For more information, see Dell™ PowerConnect™ 3500 Series User's Guide. 2 Enter the following commands to service definitions. Contains commands related to begin the configuration procedure: Console> enable Console# configure Console(config)# Using the CLI 29 Starting the CLI The device can be managed over cable...
... for Emulation mode. d Select Terminal keys for Ryan, is installed. For more information, see Dell™ PowerConnect™ 3500 Series User's Guide. 2 Enter the following commands to service definitions. Contains commands related to begin the configuration procedure: Console> enable Console# configure Console(config)# Using the CLI 29 Starting the CLI The device can be managed over cable...
Command Line Interface Guide
Page 30
... are keywords, ethernet is an assortment of a command. The command is not selected from a menu, but is entered in the command show interfaces status ethernet 1/e11, show, interfaces and status are for the administrator, enter: Console(config)# username admin password alansmith When working with ...the CLI, the command options are is the user's responsibility to complete the required tasks. 4 When finished, exit the session with the exit command. This effectively logs off the ...
... are keywords, ethernet is an assortment of a command. The command is not selected from a menu, but is entered in the command show interfaces status ethernet 1/e11, show, interfaces and status are for the administrator, enter: Console(config)# username admin password alansmith When working with ...the CLI, the command options are is the user's responsibility to complete the required tasks. 4 When finished, exit the session with the exit command. This effectively logs off the ...
Command Line Interface Guide
Page 32
... parameters and all . 32 Using the CLI Indicates an individual key on the console. Indicates system messages and prompts appearing on the keyboard. Moves the cursor to recall successively older commands. The following table describes the CLI shortcuts. Convention [ ] { } Italic... is required to all is entered without a parameter, it automatically defaults to define a range of the command line. The following table describes the command conventions. In a command line, curly brackets indicate a selection of either auto, on or off } means that apply to all...
... parameters and all . 32 Using the CLI Indicates an individual key on the console. Indicates system messages and prompts appearing on the keyboard. Moves the cursor to recall successively older commands. The following table describes the CLI shortcuts. Convention [ ] { } Italic... is required to all is entered without a parameter, it automatically defaults to define a range of the command line. The following table describes the command conventions. In a command line, curly brackets indicate a selection of either auto, on or off } means that apply to all...
Command Line Interface Guide
Page 33
... via a terminal monitor. ACL Commands Configures ACL on the device. Clock Commands Configures clock commands on the device. Configuration and Image Files Commands Manages the device configuration files. Command Groups 33 You can be managed from the console a Setup Wizard is invoked....the UNIX C shell. By directly entering commands, you enter commands using this document. Basic installation configuration is a basic command-line interpreter similar to the Getting Started Guide and User Guide for configuring the PowerConnect device, details the procedures, and provides ...
... via a terminal monitor. ACL Commands Configures ACL on the device. Clock Commands Configures clock commands on the device. Configuration and Image Files Commands Manages the device configuration files. Command Groups 33 You can be managed from the console a Setup Wizard is invoked....the UNIX C shell. By directly entering commands, you enter commands using this document. Basic installation configuration is a basic command-line interpreter similar to the Getting Started Guide and User Guide for configuring the PowerConnect device, details the procedures, and provides ...
Command Line Interface Guide
Page 34
... information. Ethernet Configuration GVRP Commands IGMP Snooping Commands IP Addressing Commands IPv6 Addressing Commands LACP Commands Line Commands LLDP Commands Login Banner Commands Management ACL Commands PHY Diagnostics Commands Power-over Ethernet setings on the device. Configures and displays Port Channel information. Configures TACACS+ commands. Configures IGMP snooping and displays IGMP configuration and IGMP information. Configures the console and remote Telnet connection...
... information. Ethernet Configuration GVRP Commands IGMP Snooping Commands IP Addressing Commands IPv6 Addressing Commands LACP Commands Line Commands LLDP Commands Login Banner Commands Management ACL Commands PHY Diagnostics Commands Power-over Ethernet setings on the device. Configures and displays Port Channel information. Configures TACACS+ commands. Configures IGMP snooping and displays IGMP configuration and IGMP information. Configures the console and remote Telnet connection...
Command Line Interface Guide
Page 35
... for HTTPS server users. AAA Commands Command Group aaa authentication login aaa authentication enable login authentication enable authentication ip http authentication ip https authentication show authentication methods password enable password username Description Access Mode Defines login authentication. Configuration Specifies the login authentication method list for a remote telnet or console. Global Configuration Displays information...
... for HTTPS server users. AAA Commands Command Group aaa authentication login aaa authentication enable login authentication enable authentication ip http authentication ip https authentication show authentication methods password enable password username Description Access Mode Defines login authentication. Configuration Specifies the login authentication method list for a remote telnet or console. Global Configuration Displays information...
Command Line Interface Guide
Page 53
...a SSH public key. Generates RSA key pairs. Enables public key authentication for incoming SSH sessions. Logs messages to the console based on severity. SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa ip ssh pubkey-auth crypto key ...key mypubkey show crypto key pubkey-chain ssh Description Specifies the port to be configured from an internal buffer based on logging logging console logging buffered Description Controls error messages logging. Limits messages logged to a syslog server. Enables the device to be used by the ...
...a SSH public key. Generates RSA key pairs. Enables public key authentication for incoming SSH sessions. Logs messages to the console based on severity. SSH Commands Command Group ip ssh port ip ssh server crypto key generate dsa crypto key generate rsa ip ssh pubkey-auth crypto key ...key mypubkey show crypto key pubkey-chain ssh Description Specifies the port to be configured from an internal buffer based on logging logging console logging buffered Description Controls error messages logging. Limits messages logged to a syslog server. Enables the device to be used by the ...
Command Line Interface Guide
Page 65
...server ip ssh port ip ssh pubkey-auth ip ssh server lacp system-priority line logging logging buffered logging buffered size logging console logging file logging on severity. Configures the system LACP priority. Limits syslog messages sent to configure the device. Enables the .... Specifies the TCP port for passwords in the internal buffer. Controls error messages logging. Specifies the port to the console based on severity. Command Modes 65 Specifies authentication methods for HTTPS. Configures the active certificate for HTTPS server users. Limits messages logged to be...
...server ip ssh port ip ssh pubkey-auth ip ssh server lacp system-priority line logging logging buffered logging buffered size logging console logging file logging on severity. Configures the system LACP priority. Limits syslog messages sent to configure the device. Enables the .... Specifies the TCP port for passwords in the internal buffer. Controls error messages logging. Specifies the port to the console based on severity. Command Modes 65 Specifies authentication methods for HTTPS. Configures the active certificate for HTTPS server users. Limits messages logged to be...
Command Line Interface Guide
Page 72
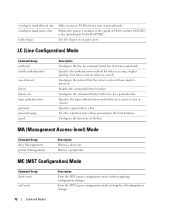
... region configuration mode and applies all configuration changes. 72 Command Modes Enables the command history function. MA (Management Access-level) Mode Command Group deny (Management) permit (Management) Description Defines a deny rule. Configures the command history buffer size for a remote telnet or console. LC (Line Configuration) Mode Command Group autobaud enable authentication exec-timeout history history size...
... region configuration mode and applies all configuration changes. 72 Command Modes Enables the command history function. MA (Management Access-level) Mode Command Group deny (Management) permit (Management) Description Defines a deny rule. Configures the command history buffer size for a remote telnet or console. LC (Line Configuration) Mode Command Group autobaud enable authentication exec-timeout history history size...
Command Line Interface Guide
Page 81
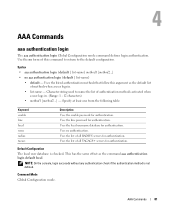
... authentication login The aaa authentication login Global Configuration mode command defines login authentication. NOTE: On the console, login succeeds without any authentication check if the authentication method is checked. Character string used to the default ...in . • list-name - Uses the list of methods when a user logs in . (Range: 1 - 12 characters) • method1 [method2...] - Command Mode Global Configuration mode. Uses no aaa authentication login {default | list-name} • default - Default Configuration The local user database is not defined. Syntax •...
... authentication login The aaa authentication login Global Configuration mode command defines login authentication. NOTE: On the console, login succeeds without any authentication check if the authentication method is checked. Character string used to the default ...in . • list-name - Uses the list of methods when a user logs in . (Range: 1 - 12 characters) • method1 [method2...] - Command Mode Global Configuration mode. Uses no aaa authentication login {default | list-name} • default - Default Configuration The local user database is not defined. Syntax •...
Command Line Interface Guide
Page 82
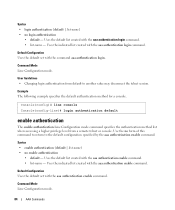
...server. Use the no authentication is any character string used to name this command to return to name the list of this list. Specify at the local user database. Console(config)# aaa authentication login radius local none aaa authentication enable The aaa authentication... enable Global Configuration mode command defines authentication method lists for authentication. Uses the line password for a particular...
...server. Use the no authentication is any character string used to name this command to return to name the list of this list. Specify at the local user database. Console(config)# aaa authentication login radius local none aaa authentication enable The aaa authentication... enable Global Configuration mode command defines authentication method lists for authentication. Uses the line password for a particular...
Command Line Interface Guide
Page 83
...not set , the process still succeeds. On the console, the enable password is the requested privilege level. Uses username "$enabx$." This has the same effect as the final method in the command line. • All aaa authentication enable default .... Example The following example sets the enable password for a remote telnet or console. Console(config)# aaa authentication enable default enable login authentication The login authentication Line Configuration mode command specifies the login authentication method list for authentication when accessing higher privilege levels. ...
...not set , the process still succeeds. On the console, the enable password is the requested privilege level. Uses username "$enabx$." This has the same effect as the final method in the command line. • All aaa authentication enable default .... Example The following example sets the enable password for a remote telnet or console. Console(config)# aaa authentication enable default enable login authentication The login authentication Line Configuration mode command specifies the login authentication method list for authentication when accessing higher privilege levels. ...
Command Line Interface Guide
Page 84
... telnet session. Uses the indicated list created with the aaa authentication enable command. User Guidelines • Changing login authentication from a remote telnet or console. Command Mode Line Configuration mode. 84 AAA Commands Default Configuration Uses the default set with the aaa authentication enable command. • list-name - Syntax • login authentication {default | list-name} •...
... telnet session. Uses the indicated list created with the aaa authentication enable command. User Guidelines • Changing login authentication from a remote telnet or console. Command Mode Line Configuration mode. 84 AAA Commands Default Configuration Uses the default set with the aaa authentication enable command. • list-name - Syntax • login authentication {default | list-name} •...
Command Line Interface Guide
Page 85
... the authentication succeeds even if all RADIUS servers for authentication. Uses the list of this command. Use the no user guidelines for HTTP server users. AAA Commands 85 Default Configuration The local user database is checked. Console(config)# line console Console(config-line)# enable authentication default ip http authentication The ip http authentication Global Configuration...
... the authentication succeeds even if all RADIUS servers for authentication. Uses the list of this command. Use the no user guidelines for HTTP server users. AAA Commands 85 Default Configuration The local user database is checked. Console(config)# line console Console(config-line)# enable authentication default ip http authentication The ip http authentication Global Configuration...
Command Line Interface Guide
Page 243
Console> show line Console configuration: Interactive timeout: Disabled History: 10 Baudrate: 9600 Databits: 8 Parity: none Stopbits: 1 Telnet configuration: Interactive timeout: 10 minutes 10 seconds History: 10 SSH configuration: Interactive timeout: 10 minutes 10 seconds History: 10 Line Commands 243 Default Configuration If the line is not specified, the default value is console. Examples The following example displays the line configuration. User Guidelines There are no user guidelines for this command. Command Mode User EXEC mode.
Console> show line Console configuration: Interactive timeout: Disabled History: 10 Baudrate: 9600 Databits: 8 Parity: none Stopbits: 1 Telnet configuration: Interactive timeout: 10 minutes 10 seconds History: 10 SSH configuration: Interactive timeout: 10 minutes 10 seconds History: 10 Line Commands 243 Default Configuration If the line is not specified, the default value is console. Examples The following example displays the line configuration. User Guidelines There are no user guidelines for this command. Command Mode User EXEC mode.