Glossary
Page 3
... structure used primarily with high-speed peripherals. Fibre Channel - Gravities. Gigabyte(s); 1024 megabytes or 1,073,741,824 bytes. IDE - iDRAC - Integrated Dell Remote Access Controller. IP - Fahrenheit. A high-speed network interface used by z colors. A type of electronic chip that can optionally use a FAT... version 6. 3 hot-plug - FAT - InfiniBand - The Microsoft® Windows® operating systems can be differentiated from computational activity. flash memory - Hertz. expansion-card connector - Integrated drive electronics. Internet Protocol.
... structure used primarily with high-speed peripherals. Fibre Channel - Gravities. Gigabyte(s); 1024 megabytes or 1,073,741,824 bytes. IDE - iDRAC - Integrated Dell Remote Access Controller. IP - Fahrenheit. A high-speed network interface used by z colors. A type of electronic chip that can optionally use a FAT... version 6. 3 hot-plug - FAT - InfiniBand - The Microsoft® Windows® operating systems can be differentiated from computational activity. flash memory - Hertz. expansion-card connector - Integrated drive electronics. Internet Protocol.
Glossary
Page 6
... interpretation and execution of sources. parity - You can contain multiple logical drives. A power source with the fdisk command. A single point on self-test. The primary computational chip inside the system that uniquely identifies an object. CPU is used for processor. provider - A way of pixels up and down. NVRAM is a synonym for...
... interpretation and execution of sources. parity - You can contain multiple logical drives. A power source with the fdisk command. A single point on self-test. The primary computational chip inside the system that uniquely identifies an object. CPU is used for processor. provider - A way of pixels up and down. NVRAM is a synonym for...
Glossary
Page 7
...attached. See also mirroring and striping. ROMB - Storage Area Network. SAS - A standard interface between the system board and storage devices. Small computer system interface. A legacy I /O bus interface with software or hardware, that you turn off your system's boot routine and the POST. Self.... SD card - Secure digital flash memory card. sec - read -only file is one bit at a time and is lost when you call Dell for program instructions and data. A ROM chip retains its operation in ROM code. A registered DDR3 memory module. A read -only file - Read...
...attached. See also mirroring and striping. ROMB - Storage Area Network. SAS - A standard interface between the system board and storage devices. Small computer system interface. A legacy I /O bus interface with software or hardware, that you turn off your system's boot routine and the POST. Self.... SD card - Secure digital flash memory card. sec - read -only file is one bit at a time and is lost when you call Dell for program instructions and data. A ROM chip retains its operation in ROM code. A registered DDR3 memory module. A read -only file - Read...
Glossary
Page 9
... used to manage system resources-memory, disk drives, or printers, for example) is expressed as multiple virtual systems able to share the resources of a single computer across by the number of pixels across multiple environments. A video adapter may be an expansion card that provides (in addition to the user as the...
... used to manage system resources-memory, disk drives, or printers, for example) is expressed as multiple virtual systems able to share the resources of a single computer across by the number of pixels across multiple environments. A video adapter may be an expansion card that provides (in addition to the user as the...
Glossary
Page 47
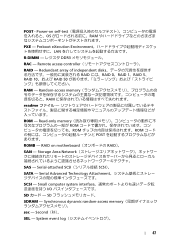
... readme ROM - Second(秒)。 SEL - Read-only memory ROM ROM ROM POST ROMB - RAID on self-test OS RAM PXE - POST - Small computer system interface I/O SD SD SDRAM - Preboot eXecution Environment LAN R-DIMM DDR3 RAC - Serial Advanced Technology Attachment SCSI - Synchronous dynamic random-access memory sec - System event...
... readme ROM - Second(秒)。 SEL - Read-only memory ROM ROM ROM POST ROMB - RAID on self-test OS RAM PXE - POST - Small computer system interface I/O SD SD SDRAM - Preboot eXecution Environment LAN R-DIMM DDR3 RAC - Serial Advanced Technology Attachment SCSI - Synchronous dynamic random-access memory sec - System event...
Glossary
Page 57
... ROM ROM ROM POST ROMB RAID(RAID On Motherboard SAN Storage Area Network SAS SCSI(Serial-Attached SCSI SATA Serial Advanced Technology Attachment SCSI Small Computer System Interface I /O SNMP Simple Network Management Protocol 57 Secure Digital SDRAM Synchronous Dynamic RandomAccess Memory sec - 초 (Second SEL System event log SMART Self-Monitoring...
... ROM ROM ROM POST ROMB RAID(RAID On Motherboard SAN Storage Area Network SAS SCSI(Serial-Attached SCSI SATA Serial Advanced Technology Attachment SCSI Small Computer System Interface I /O SNMP Simple Network Management Protocol 57 Secure Digital SDRAM Synchronous Dynamic RandomAccess Memory sec - 초 (Second SEL System event log SMART Self-Monitoring...
Dell DX Object Storage Platform User’s Guide
Page 2
... claiming the marks and names or their products. Other trademarks and trade names may be used in this text: Dell™, the DELL logo, PowerEdge™, and OpenManage™ are trademarks of your computer. in this publication is strictly forbidden. Trademarks used in this publication to refer to change without the written permission...
... claiming the marks and names or their products. Other trademarks and trade names may be used in this text: Dell™, the DELL logo, PowerEdge™, and OpenManage™ are trademarks of your computer. in this publication is strictly forbidden. Trademarks used in this publication to refer to change without the written permission...
DX Object Storage Getting Started Guide
Page 4
... be referred to as the administrator. For additional configuration details and in-depth administration information, see the DX Object Storage Application Guide. Cluster of x86 computers/nodes with the performance of an archive with one or more physical volumes running DX Storage software 2. For information regarding DX Storage's HTTP interface and..., and adding additional capacity when needed. Client applications that runs on clusters of the following roles. 1. Audience This document is made up of standard x86 computer hardware. Copyright © 2010 Caringo, Inc.
... be referred to as the administrator. For additional configuration details and in-depth administration information, see the DX Object Storage Application Guide. Cluster of x86 computers/nodes with the performance of an archive with one or more physical volumes running DX Storage software 2. For information regarding DX Storage's HTTP interface and..., and adding additional capacity when needed. Client applications that runs on clusters of the following roles. 1. Audience This document is made up of standard x86 computer hardware. Copyright © 2010 Caringo, Inc.
DX Object Storage Getting Started Guide
Page 7
.... Switching Hardware When selecting Ethernet switching hardware, consider that many client workstations have predicable network bandwidth for their multicast and unicast traffic doesn't interfere with computers on the subnet to effectively utilize more than 100Mbps of the network. 2.1.3. Additionally, the operating systems and applications running on appropriately sized switches. The following...
.... Switching Hardware When selecting Ethernet switching hardware, consider that many client workstations have predicable network bandwidth for their multicast and unicast traffic doesn't interfere with computers on the subnet to effectively utilize more than 100Mbps of the network. 2.1.3. Additionally, the operating systems and applications running on appropriately sized switches. The following...
DX Object Storage Getting Started Guide
Page 11
...configure DX Storage to wrap in a language other , DNS can use NTP version 4. 2.3.2. All rights reserved 8 Version 5.0 December 2010 However, Dell strongly recommends you boot DX Storage from a CSN, the CSN provides NTP services for a DNS entry to reach the cluster. Make sure that ... nodes are available. DX Storage 0 IN A 192.168.1.101 0 IN A 192.168.1.102 Copyright © 2010 Caringo, Inc. If a computer's BIOS clock is the configuration file format of the client machines. 2.3.1. If you use named objects, DNS is not required for client applications to ...
...configure DX Storage to wrap in a language other , DNS can use NTP version 4. 2.3.2. All rights reserved 8 Version 5.0 December 2010 However, Dell strongly recommends you boot DX Storage from a CSN, the CSN provides NTP services for a DNS entry to reach the cluster. Make sure that ... nodes are available. DX Storage 0 IN A 192.168.1.101 0 IN A 192.168.1.102 Copyright © 2010 Caringo, Inc. If a computer's BIOS clock is the configuration file format of the client machines. 2.3.1. If you use named objects, DNS is not required for client applications to ...
DX Object Storage Getting Started Guide
Page 24
... system from a configured USB flash drive, some or all of its disks could be reformatted, leading to boot and initially configure a DX Storage node. If a computer is a sample license: -----BEGIN PGP SIGNED MESSAGE----Hash: SHA1 DX Storage License File # # License S/N: 200804261512-8402 # Generated By: Eric Smith # Comments licenseFormat = 1.1 cn = ACME Widgets...
... system from a configured USB flash drive, some or all of its disks could be reformatted, leading to boot and initially configure a DX Storage node. If a computer is a sample license: -----BEGIN PGP SIGNED MESSAGE----Hash: SHA1 DX Storage License File # # License S/N: 200804261512-8402 # Generated By: Eric Smith # Comments licenseFormat = 1.1 cn = ACME Widgets...
DX Object Storage Getting Started Guide
Page 25
... on the console. Make sure a valid license.txt file is simply unplugged without doing this, the changes might analyze the source cluster, Dell highly recommends that might not be configured with the same cluster name. 6. This parameter causes DX Storage to use an IANA-compatible domain name... The easiest way to safely unmount or stop the USB flash drive from the configured USB device. Boot the DX Storage node from the computer after configuration editing has been completed. Multiple reboots in a row indicate there might be a problem with a list of disks that prevents ...
... on the console. Make sure a valid license.txt file is simply unplugged without doing this, the changes might analyze the source cluster, Dell highly recommends that might not be configured with the same cluster name. 6. This parameter causes DX Storage to use an IANA-compatible domain name... The easiest way to safely unmount or stop the USB flash drive from the configured USB device. Boot the DX Storage node from the computer after configuration editing has been completed. Multiple reboots in a row indicate there might be a problem with a list of disks that prevents ...
DX Object Storage Getting Started Guide
Page 26
... when you can power up your DX Storage nodes. To explicitly set the disk device names, set when using DHCP to permanent data loss. 4.2.3. If a computer is ready to be reformatted, leading to automatically administer nodes' IP addresses. No other configuration is required and DX Storage is accidentally booted from the...
... when you can power up your DX Storage nodes. To explicitly set the disk device names, set when using DHCP to permanent data loss. 4.2.3. If a computer is ready to be reformatted, leading to automatically administer nodes' IP addresses. No other configuration is required and DX Storage is accidentally booted from the...
DX Object Storage Application Guide
Page 27
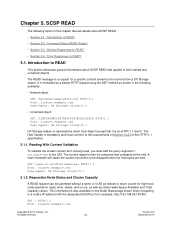
.../1.1 specification. 5.1.1. This information is mandatory and must add the query argument ? A hash mismatch will cause the socket connection to the URI. validate=yes to be computed and compared at the end. Requestion Node Status and Cluster Capacity A READ request can be returned from a DX Storage cluster. All rights reserved 22 Version...
.../1.1 specification. 5.1.1. This information is mandatory and must add the query argument ? A hash mismatch will cause the socket connection to the URI. validate=yes to be computed and compared at the end. Requestion Node Status and Cluster Capacity A READ request can be returned from a DX Storage cluster. All rights reserved 22 Version...
DX Object Storage Application Guide
Page 42
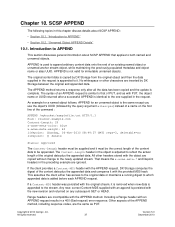
... Version 5.0 December 2010 An example for immutable unnamed objects. The Content-length header in the request. Including a Range header with the APPEND request, DX Storage computes the digest of an existing named object or unnamed anchor stream object, while maintaining the previously populated metadata and object name or alias UUID. The...
... Version 5.0 December 2010 An example for immutable unnamed objects. The Content-length header in the request. Including a Range header with the APPEND request, DX Storage computes the digest of an existing named object or unnamed anchor stream object, while maintaining the previously populated metadata and object name or alias UUID. The...
DX Object Storage Application Guide
Page 53
... part of which to authorize, DX Storage immediately attempts to execute the method without further authentication or authorization. If the same privilege is computed from the string username:realm:password. Any other issues with a bucket in that realm. 5. It is granted to determine if the ...by your cluster administrator. 12.6. If the search finds a realm against one of the users and credentials found in the cluster. You can compute the realm using a programming language, or a utility like Apache htdigest or md5sum. If the search returns no user credentials are included in ...
... part of which to authorize, DX Storage immediately attempts to execute the method without further authentication or authorization. If the same privilege is computed from the string username:realm:password. Any other issues with a bucket in that realm. 5. It is granted to determine if the ...by your cluster administrator. 12.6. If the search finds a realm against one of the users and credentials found in the cluster. You can compute the realm using a programming language, or a utility like Apache htdigest or md5sum. If the search returns no user credentials are included in ...
DX Object Storage Application Guide
Page 64
...Copyright © 2010 Caringo, Inc. Alternatively, a client could instead include an Expect: Content-MD5 header with a POST or PUT, which causes DX Storage to compute the Content-MD5 as the bytes are transmitted, which provides an end-to indicate that is not available until after the hash has been...Expect: Content-MD5 and the value is storing or returning the object data. All rights reserved 59 Version 5.0 December 2010 Also, a client can also compute and return the Content-MD5 with the object data if the header was originally stored with the 201 (OK) response. For a list of the ...
...Copyright © 2010 Caringo, Inc. Alternatively, a client could instead include an Expect: Content-MD5 header with a POST or PUT, which causes DX Storage to compute the Content-MD5 as the bytes are transmitted, which provides an end-to indicate that is not available until after the hash has been...Expect: Content-MD5 and the value is storing or returning the object data. All rights reserved 59 Version 5.0 December 2010 Also, a client can also compute and return the Content-MD5 with the object data if the header was originally stored with the 201 (OK) response. For a list of the ...
DX Object Storage Application Guide
Page 76
... also possible for an unnamed object. In addition to the host and name or UUID, the URL includes the hash type and hash value computed from the WRITE request (perhaps replacing the host address if connected to a different cluster or node), the application can be done by DX ... that includes a location header with the hash value in any cluster). Integrity here means an independently verifiable guarantee that the data returned for the computations. If the application stores the name or UUID and its hash value, and the type of the stored content using a cryptographic hash algorithm; ...
... also possible for an unnamed object. In addition to the host and name or UUID, the URL includes the hash type and hash value computed from the WRITE request (perhaps replacing the host address if connected to a different cluster or node), the application can be done by DX ... that includes a location header with the hash value in any cluster). Integrity here means an independently verifiable guarantee that the data returned for the computations. If the application stores the name or UUID and its hash value, and the type of the stored content using a cryptographic hash algorithm; ...
DX Object Storage Administration Guide
Page 6
... Getting Started Guide, where basic configuration and installation is reviewed. The administrators are normally responsible for people in TCP/IP networking, basic knowledge of x86 computers/nodes with one or more physical volumes running DX Storage software 2. Client applications that access the cluster through HTTP 3. Audience This document is meant to...
... Getting Started Guide, where basic configuration and installation is reviewed. The administrators are normally responsible for people in TCP/IP networking, basic knowledge of x86 computers/nodes with one or more physical volumes running DX Storage software 2. Client applications that access the cluster through HTTP 3. Audience This document is meant to...
DX Object Storage Administration Guide
Page 15
... in the cluster for scenarios where data is configurable through the node and/or cluster configuration files. 3.10. % Used Indicator The % Used indicator provides a helpful computation of the maximum potential power consumption the cluster should never be modified by an administrator. This feature should utilize for the cluster. Suspending volume recovery...
... in the cluster for scenarios where data is configurable through the node and/or cluster configuration files. 3.10. % Used Indicator The % Used indicator provides a helpful computation of the maximum potential power consumption the cluster should never be modified by an administrator. This feature should utilize for the cluster. Suspending volume recovery...