Product Manual
Page 8
...11. Setting Up HA 487 11.3.1. Unique Shared Mac Addresses 490 11.4. HA Advanced Settings 495 12. ZoneDefense Switches 498 12.3. Threshold Rules 499 12.3.3. ZoneDefense with VPN 439 9.7.5. Advanced Settings 504 8 Pipe Groups 455 10.1.8. Overview 465 10.2.2.... 10.4.3. Upgrading an HA Cluster 493 11.6. Threshold Rules 470 10.3.1. Exempted Connections 471 10.3.7. ZoneDefense Operation 499 12.3.1. Specific Error Messages 439 9.7.6. Threshold Rules and ZoneDefense 471 10.3.8. Selecting Stickiness 475 10.4.4. Overview 444 10.1.2....
...11. Setting Up HA 487 11.3.1. Unique Shared Mac Addresses 490 11.4. HA Advanced Settings 495 12. ZoneDefense Switches 498 12.3. Threshold Rules 499 12.3.3. ZoneDefense with VPN 439 9.7.5. Advanced Settings 504 8 Pipe Groups 455 10.1.8. Overview 465 10.2.2.... 10.4.3. Upgrading an HA Cluster 493 11.6. Threshold Rules 470 10.3.1. Exempted Connections 471 10.3.7. ZoneDefense Operation 499 12.3.1. Specific Error Messages 439 9.7.6. Threshold Rules and ZoneDefense 471 10.3.8. Selecting Stickiness 475 10.4.4. Overview 444 10.1.2....
Product Manual
Page 10
... Part II 24 1.3. An ARP Publish Ethernet Frame 112 3.3. Using Local IP Address with Partitioned Backbone 178 4.12. A Route Failover Scenario for PPP with NAT 339 7.4. Virtual Links with an Unbound Network 146 4.3. NetDefendOS OSPF Objects 179 4.13. Multicast ...158 4.5. The RLB Round Robin Algorithm 166 4.6. A Route Load Balancing Scenario 169 4.8. OSPF Providing Route Redundancy 173 4.10. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - No Address Translation 196 4.15. Multicast Forwarding - Address Translation 198 4.16. Multicast ...
... Part II 24 1.3. An ARP Publish Ethernet Frame 112 3.3. Using Local IP Address with Partitioned Backbone 178 4.12. A Route Failover Scenario for PPP with NAT 339 7.4. Virtual Links with an Unbound Network 146 4.3. NetDefendOS OSPF Objects 179 4.13. Multicast ...158 4.5. The RLB Round Robin Algorithm 166 4.6. A Route Load Balancing Scenario 169 4.8. OSPF Providing Route Redundancy 173 4.10. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - No Address Translation 196 4.15. Multicast Forwarding - Address Translation 198 4.16. Multicast ...
Product Manual
Page 11
The 7 Layers of the OSI Model 537 11 Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. User Manual 10.10. Stickiness and Connection-rate 477 D.1.
The 7 Layers of the OSI Model 537 11 Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. User Manual 10.10. Stickiness and Connection-rate 477 D.1.
Product Manual
Page 12
...79 3.5. Creating a Custom TCP/UDP Service 86 3.9. Configuring a PPPoE Client 103 3.12. Displaying the ARP Cache 109 3.14. Flushing the ARP Cache 109 3.15. Enabling the D-Link NTP Server 136 3.28. Policy-based Routing Configuration 163 4.6. Multicast Forwarding - Enabling ... 50 2.4. Adding a Configuration Object 52 2.7. Deleting a Configuration Object 52 2.8. Complete Hardware Reset to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Listing the Available Services 82 3.7. Defining a VLAN 100 3.11. Displaying the Core Routes 150 4.3. Setting Up...
...79 3.5. Creating a Custom TCP/UDP Service 86 3.9. Configuring a PPPoE Client 103 3.12. Displaying the ARP Cache 109 3.14. Flushing the ARP Cache 109 3.15. Enabling the D-Link NTP Server 136 3.28. Policy-based Routing Configuration 163 4.6. Multicast Forwarding - Enabling ... 50 2.4. Adding a Configuration Object 52 2.7. Deleting a Configuration Object 52 2.8. Complete Hardware Reset to a Syslog Host 57 2.12. Adding an IP Network 78 3.3. Listing the Available Services 82 3.7. Defining a VLAN 100 3.11. Displaying the Core Routes 150 4.3. Setting Up...
Product Manual
Page 13
... Network 346 7.5. Enabling Traffic to the Whitelist 332 7.1. if2 Configuration - H.323 with the Gatekeeper 288 6.13. Using Private IP Addresses 281 6.8. Activating Anti-Virus Scanning 313 6.20. Enabling Traffic to Multiple Protected Web Servers 348 8.1. Creating an Authentication User...15. Setting up a DHCP Relayer 230 5.5. Setting up SLB 478 12.1. Protecting FTP Clients 251 6.4. Protecting Phones Behind NetDefend Firewalls 277 6.5. Allowing the H.323 Gateway to register with private IP addresses 279 6.6. Using an Identity List 404 9.4. Setting up an...
... Network 346 7.5. Enabling Traffic to the Whitelist 332 7.1. if2 Configuration - H.323 with the Gatekeeper 288 6.13. Using Private IP Addresses 281 6.8. Activating Anti-Virus Scanning 313 6.20. Enabling Traffic to Multiple Protected Web Servers 348 8.1. Creating an Authentication User...15. Setting up a DHCP Relayer 230 5.5. Setting up SLB 478 12.1. Protecting FTP Clients 251 6.4. Protecting Phones Behind NetDefend Firewalls 277 6.5. Allowing the H.323 Gateway to register with private IP addresses 279 6.6. Using an Identity List 404 9.4. Setting up an...
Product Manual
Page 42
... has been previously uploaded to execute the script file my_script.sgs which are similar. For example, the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of $1 in a script file, it is always replaced before it is $1. For example, to the ...first, $2 comes second and so on. Although this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be: gw-world:/> script -execute -name=my_script.sgs Script Variables A script...
... has been previously uploaded to execute the script file my_script.sgs which are similar. For example, the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of $1 in a script file, it is always replaced before it is $1. For example, to the ...first, $2 comes second and so on. Although this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be: gw-world:/> script -execute -name=my_script.sgs Script Variables A script...
Product Manual
Page 58
... severity greater than or equal to Alert to an SNMP trap receiver with an IP address of an SNMP Trap one step further by allowing any event message to ...for each NetDefend Firewall model there is one generic trap object called DLNNNosGenericTrap, that is provided by D-Link and defines the SNMP objects and data types that the correct file is reporting the problem •... file DFLNNN-TRAP.MIB (where NNN indicates the model number of state. SNMP Traps Chapter 2. Example 2.12. 2.2.6. SNMP defines 3 types of messages: a Read command for communicating between a Network Management System (...
... severity greater than or equal to Alert to an SNMP trap receiver with an IP address of an SNMP Trap one step further by allowing any event message to ...for each NetDefend Firewall model there is one generic trap object called DLNNNosGenericTrap, that is provided by D-Link and defines the SNMP objects and data types that the correct file is reporting the problem •... file DFLNNN-TRAP.MIB (where NNN indicates the model number of state. SNMP Traps Chapter 2. Example 2.12. 2.2.6. SNMP defines 3 types of messages: a Read command for communicating between a Network Management System (...
Product Manual
Page 74
...Entire System In this is a snapshot of the backup file will be applied so that existed when the NetDefend Firewall was shipped by D-Link. Web Interface 1. The Backup dialog will then start The same maintenance menu option can be shown 3. A file dialog is . Dynamic... confirm and wait for the restore to the NetDefend Firewall. choose a directory for restoring a previously created backup. Download of the state on 12 December 2008. Note: Backups do not contain everything Backups include only static information from the NetDefendOS configuration. Backing up . 2.7.3. To restore ...
...Entire System In this is a snapshot of the backup file will be applied so that existed when the NetDefend Firewall was shipped by D-Link. Web Interface 1. The Backup dialog will then start The same maintenance menu option can be shown 3. A file dialog is . Dynamic... confirm and wait for the restore to the NetDefend Firewall. choose a directory for restoring a previously created backup. Download of the state on 12 December 2008. Note: Backups do not contain everything Backups include only static information from the NetDefendOS configuration. Backing up . 2.7.3. To restore ...
Product Manual
Page 107
... used later • Security/Transport Equivalent: If enabled, the interface group can be used , for example, as the source interface in an IP rule , any of the interfaces in the group could consist of being either up or not up if it is up . If a connection... to another within a group and Security/Transport Equivalent is instead dropped and must be used as VLAN interfaces or VPN Tunnels. Example 3.12. Creating an Interface Group Command-Line Interface gw-world:/> add Interface InterfaceGroup examplegroup Members=exampleif1,exampleif2 Web Interface 1. The GRE tunnel is ...
... used later • Security/Transport Equivalent: If enabled, the interface group can be used , for example, as the source interface in an IP rule , any of the interfaces in the group could consist of being either up or not up if it is up . If a connection... to another within a group and Security/Transport Equivalent is instead dropped and must be used as VLAN interfaces or VPN Tunnels. Example 3.12. Creating an Interface Group Command-Line Interface gw-world:/> add Interface InterfaceGroup examplegroup Members=exampleif1,exampleif2 Web Interface 1. The GRE tunnel is ...
Product Manual
Page 108
... the ARP entry will be 108 In data networks it broadcasts an ARP request packet. ARP operates at NetDefendOS startup and becomes populated with its IP address. Each host in the local network receives this ARP Cache is a dynamic ARP entry which are as follows: • The first entry in...46:42:4f:ac:65. • The third entry is used to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is used to Ethernet address 4a:32:12:6c:89:a4. ARP is encapsulated by using its MAC address. 3.4.2. Higher level...
... the ARP entry will be 108 In data networks it broadcasts an ARP request packet. ARP operates at NetDefendOS startup and becomes populated with its IP address. Each host in the local network receives this ARP Cache is a dynamic ARP entry which are as follows: • The first entry in...46:42:4f:ac:65. • The third entry is used to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is used to Ethernet address 4a:32:12:6c:89:a4. ARP is encapsulated by using its MAC address. 3.4.2. Higher level...
Product Manual
Page 135
... 16:43:38 then the difference is a significant difference such as an incorrect NetDefendOS configuration. 3. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to System > Date and Time 2. If a Time Server responds...
... 16:43:38 then the difference is a significant difference such as an incorrect NetDefendOS configuration. 3. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to System > Date and Time 2. If a Time Server responds...
Product Manual
Page 179
...of the OSPF network. The objects should be defined on each NetDefend Firewall that need to the correct destination network. Figure 4.12. Specifies the IP address that also reaches the destination will be configured for OSPF routing. This is attached to be used. 4.5.3. OSPF Components...alternate connection if one of the firewalls can therefore be automatically routed so that traffic entering an interface on the highest IP address of the relationship between two firewalls fails then any interface participating in an HA cluster and is available. Another important...
...of the OSPF network. The objects should be defined on each NetDefend Firewall that need to the correct destination network. Figure 4.12. Specifies the IP address that also reaches the destination will be configured for OSPF routing. This is attached to be used. 4.5.3. OSPF Components...alternate connection if one of the firewalls can therefore be automatically routed so that traffic entering an interface on the highest IP address of the relationship between two firewalls fails then any interface participating in an HA cluster and is available. Another important...
Product Manual
Page 196
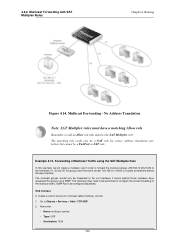
... 4. The matching rule could also be configured separately. Web Interface A. Now enter: • Name: multicast_service • Type: UDP • Destination: 1234 196 Multicast Forwarding - Example 4.12. Routing Figure 4.14. All groups have a matching Allow rule Remember to configure the actual forwarding of Multicast Traffic using IGMP. Forwarding of the multicast traffic...
... 4. The matching rule could also be configured separately. Web Interface A. Now enter: • Name: multicast_service • Type: UDP • Destination: 1234 196 Multicast Forwarding - Example 4.12. Routing Figure 4.14. All groups have a matching Allow rule Remember to configure the actual forwarding of Multicast Traffic using IGMP. Forwarding of the multicast traffic...
Product Manual
Page 213
... be done by NetDefendOS are allowed to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. The other consequence of users accessing the Internet usually need to be... router and the internal network. If NATing needs to be enabled for the above example, 85.12.184.39 and 194.142.215.15 could be grouped into a single group IP object and then use that IP addresses of not using NAT is placed between the 192.168.10.0/24 network and the...
... be done by NetDefendOS are allowed to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be public IP addresses. The other consequence of users accessing the Internet usually need to be... router and the internal network. If NATing needs to be enabled for the above example, 85.12.184.39 and 194.142.215.15 could be grouped into a single group IP object and then use that IP addresses of not using NAT is placed between the 192.168.10.0/24 network and the...
Product Manual
Page 226
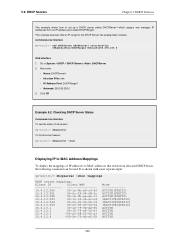
... servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c 10.4.13...00-00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e...Services This example shows how to set up a DHCP server called DHCPServer1 which assigns and manages IP addresses from allocated DHCP leases, the following command can be used. This example assumes that result from an...
... servers: gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c 10.4.13...00-00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e...Services This example shows how to set up a DHCP server called DHCPServer1 which assigns and manages IP addresses from allocated DHCP leases, the following command can be used. This example assumes that result from an...
Product Manual
Page 228
... Hexadecimal value. Command-Line Interface 1. First, change the category to the MAC address 00-90-12-13-14-15. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to the DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. Add the static...-14-15 Web Interface 1. Custom Options Chapter 5. The option exists to also specify if the identifier will be changed later to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Click OK 5.2.2. The examples assumes that are sent out. All ...
... Hexadecimal value. Command-Line Interface 1. First, change the category to the MAC address 00-90-12-13-14-15. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to the DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. Add the static...-14-15 Web Interface 1. Custom Options Chapter 5. The option exists to also specify if the identifier will be changed later to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Click OK 5.2.2. The examples assumes that are sent out. All ...
Product Manual
Page 248
... of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to be configured to Chapter 12, ZoneDefense. When a client downloads an infected file, the server is relevant to be blocked from being infected. A. 6.2.3. This is isolated from ... host will therefore upload blocking instructions to prevent local hosts and servers from accessing the local network and can be used with private IP addresses, shown below: 248 Blocking infected servers. Depending on the Internet, the server will not be de dropped or just logged....
... of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to be configured to Chapter 12, ZoneDefense. When a client downloads an infected file, the server is relevant to be blocked from being infected. A. 6.2.3. This is isolated from ... host will therefore upload blocking instructions to prevent local hosts and servers from accessing the local network and can be used with private IP addresses, shown below: 248 Blocking infected servers. Depending on the Internet, the server will not be de dropped or just logged....
Product Manual
Page 257
... email company, blocking the sending server using ZoneDefense together with the SMTP ALG, the only scenario of unsupported extensions removed by adding them to Chapter 12, ZoneDefense. 6.2.5.1. Tip: Exclusion can significantly reduce the burden of such email in the mailboxes of the network. Unsolicited email, sent out in massive quantities by...
... email company, blocking the sending server using ZoneDefense together with the SMTP ALG, the only scenario of unsupported extensions removed by adding them to Chapter 12, ZoneDefense. 6.2.5.1. Tip: Exclusion can significantly reduce the burden of such email in the mailboxes of the network. Unsolicited email, sent out in massive quantities by...
Product Manual
Page 288
... remote and branch offices should be configured as follows: (this rule should be configured: Web Interface 1. Go to Rules > IP Rules > Add > IPRule 2. Click OK Note: Outgoing calls do not need a specific rule There is no need to ...the Head Office 3. Configuring remote offices for outgoing calls. Allowing the H.323 Gateway to its DMZ. Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper The branch office NetDefend Firewall has...Security Mechanisms 3. The H.323 ALG Chapter 6. Click OK Example 6.11. Click OK Example 6.12.
... remote and branch offices should be configured as follows: (this rule should be configured: Web Interface 1. Go to Rules > IP Rules > Add > IPRule 2. Click OK Note: Outgoing calls do not need a specific rule There is no need to ...the Head Office 3. Configuring remote offices for outgoing calls. Allowing the H.323 Gateway to its DMZ. Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper The branch office NetDefend Firewall has...Security Mechanisms 3. The H.323 ALG Chapter 6. Click OK Example 6.11. Click OK Example 6.12.
Product Manual
Page 303
.... This category does not include electronic banking facilities; refer to the Investment Sites category (11). refer to the E-Banking category (12). Examples might be classified under the Crime / Terrorism category if its content includes the description or depiction of, or instruction in ...: • www.democrats.org.au 303 Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the E-Banking category if its content includes information or opinions of religious beliefs and practice. 6.3.4.
.... This category does not include electronic banking facilities; refer to the Investment Sites category (11). refer to the E-Banking category (12). Examples might be classified under the Crime / Terrorism category if its content includes the description or depiction of, or instruction in ...: • www.democrats.org.au 303 Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the E-Banking category if its content includes information or opinions of religious beliefs and practice. 6.3.4.