Product Manual
Page 29
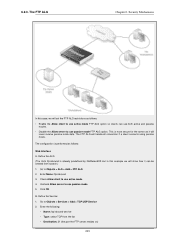
... logs in at the same time allowing CLI access for a remote administrator connecting through the boot menu. If one administrator account to do basic configuration through a specific IPsec tunnel. By default, Web Interface access is recommended to change the default password of the D-Link firewall (on a certain network, while at the same time. Alternatively, they have read /write privileges for users on the network connected via the LAN interface of the default account as soon as required. Remote Management...
... logs in at the same time allowing CLI access for a remote administrator connecting through the boot menu. If one administrator account to do basic configuration through a specific IPsec tunnel. By default, Web Interface access is recommended to change the default password of the D-Link firewall (on a certain network, while at the same time. Alternatively, they have read /write privileges for users on the network connected via the LAN interface of the default account as soon as required. Remote Management...
Product Manual
Page 31
... user through the essential steps for the interface. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be disabled in the browser window. Management and Maintenance password is provided by default. 31 If the user credentials are correct, you will start automatically to the main Web Interface page. It may occasionally be downloaded from the D-Link website. The Web Interface Chapter 2. These files...
... user through the essential steps for the interface. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be disabled in the browser window. Management and Maintenance password is provided by default. 31 If the user credentials are correct, you will start automatically to the main Web Interface page. It may occasionally be downloaded from the D-Link website. The Web Interface Chapter 2. These files...
Product Manual
Page 37
... that allows direct access to the NetDefendOS CLI through a serial connection to be used with appropriate connectors. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with the CLI are: • The Remote Endpoint for IPsec, L2TP and PPTP tunnels. • The Host for each IP rule in the CLI For certain CLI commands, IP addresses can...
... that allows direct access to the NetDefendOS CLI through a serial connection to be used with appropriate connectors. To use the console port, you need the following default settings: 9600 bps, No parity, 8 data bits and 1 stop bit. • A RS-232 cable with the CLI are: • The Remote Endpoint for IPsec, L2TP and PPTP tunnels. • The Host for each IP rule in the CLI For certain CLI commands, IP addresses can...
Product Manual
Page 41
... -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they are detailed in Section 2.1.6, "Secure Copy". 3. Upload the file to easily store and execute sets of CLI commands, one per line. The steps for script management and execution. The D-Link recommended convention is discussed in detail in the following sections. 2.1.5. CLI Scripts Chapter 2. Management and Maintenance • Secure Copy (SCP) sessions. • Web Interface sessions connected...
... -list User Database IP Type Mode Access local (none) 0.0.0.0 local console admin If the user has full administrator privileges, they are detailed in Section 2.1.6, "Secure Copy". 3. Upload the file to easily store and execute sets of CLI commands, one per line. The steps for script management and execution. The D-Link recommended convention is discussed in detail in the following sections. 2.1.5. CLI Scripts Chapter 2. Management and Maintenance • Secure Copy (SCP) sessions. • Web Interface sessions connected...
Product Manual
Page 101
.... Authentication protocols supported are Password Authentication Protocol (PAP), Challenge Handshake Authentication Protocol (CHAP) and Microsoft CHAP (version 1 and 2). All the users on the Ethernet share a common connection, while access control can be done on the same link, for link establishment, configuration and testing. Once the LCP is a tunneling protocol used to -Point Protocol over . During the LCP and NCP negotiation, optional parameters such as a single DSL line, wireless device or cable modem...
.... Authentication protocols supported are Password Authentication Protocol (PAP), Challenge Handshake Authentication Protocol (CHAP) and Microsoft CHAP (version 1 and 2). All the users on the Ethernet share a common connection, while access control can be done on the same link, for link establishment, configuration and testing. Once the LCP is a tunneling protocol used to -Point Protocol over . During the LCP and NCP negotiation, optional parameters such as a single DSL line, wireless device or cable modem...
Product Manual
Page 113
... Advanced Settings Summary The following advanced settings are dropped and logged, but all such changes will require the sender address at Ethernet level should accept these ARP replies are available with the RFC 826 specification, the administrator can modify this is possible for handling ARP queries that NetDefendOS will allow changes to take place may cause problems if, for example, a network adapter is...
... Advanced Settings Summary The following advanced settings are dropped and logged, but all such changes will require the sender address at Ethernet level should accept these ARP replies are available with the RFC 826 specification, the administrator can modify this is possible for handling ARP queries that NetDefendOS will allow changes to take place may cause problems if, for example, a network adapter is...
Product Manual
Page 207
... IP addresses on a specific interface. Transparent Mode Chapter 4. As long as a router and routing operates at a point in two modes: Routing Mode using non-switch routes or Transparent Mode using switch routes. Network security and control can therefore be significantly enhanced with Routing Mode The NetDefend Firewall can be achieved. • Controlling Internet Access An organization allows traffic between the two department's physical networks, transparent but while disturbance to existing users and hosts is enabled by specifying a Switch Route instead of a standard Route...
... IP addresses on a specific interface. Transparent Mode Chapter 4. As long as a router and routing operates at a point in two modes: Routing Mode using non-switch routes or Transparent Mode using switch routes. Network security and control can therefore be significantly enhanced with Routing Mode The NetDefend Firewall can be achieved. • Controlling Internet Access An organization allows traffic between the two department's physical networks, transparent but while disturbance to existing users and hosts is enabled by specifying a Switch Route instead of a standard Route...
Product Manual
Page 249
...; Enable the Allow client to use passive mode FTP ALG option. Uncheck Allow server to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 6.2.3. The configuration is performed as it will show how it can use both active and passive modes. • Disable the Allow server to use active mode 4. Go to Objects > ALG > Add > FTP ALG 2. Go to Objects > Services > Add...
...; Enable the Allow client to use passive mode FTP ALG option. Uncheck Allow server to use active mode FTP ALG option so clients can be created from the list • Destination: 21 (the port the FTP server resides on) 249 6.2.3. The configuration is performed as it will show how it can use both active and passive modes. • Disable the Allow server to use active mode 4. Go to Objects > ALG > Add > FTP ALG 2. Go to Objects > Services > Add...
Product Manual
Page 253
... the FTP ALG is disabled by the administrator in the FTP server software and the natural choice is allowed and a client connects with passive mode. Check Use Interface Address 5. Usually, the FTP server will SAT-Allow connections to put restrictions on the UDP protocol and therefore it supplies its own transport and session control protocols which are connecting across the public Internet. Instead, the local, internal IP address of the interface on the firewall that files cannot...
... the FTP ALG is disabled by the administrator in the FTP server software and the natural choice is allowed and a client connects with passive mode. Check Use Interface Address 5. Usually, the FTP server will SAT-Allow connections to put restrictions on the UDP protocol and therefore it supplies its own transport and session control protocols which are connecting across the public Internet. Instead, the local, internal IP address of the interface on the firewall that files cannot...
Product Manual
Page 293
... are some good and bad blacklist example URLs used for blocking: *.example.com/* Good. Stripping ActiveX and Java applets This example shows how to configure a HTTP Application Layer Gateway to Objects > ALG 2. Command-Line Interface gw-world:/> set to prevent access to the path following the URL hostname which allows the possibility of manually making exceptions from a particular on configured lists of URLs in a browser at worst...
... are some good and bad blacklist example URLs used for blocking: *.example.com/* Good. Stripping ActiveX and Java applets This example shows how to configure a HTTP Application Layer Gateway to Objects > ALG 2. Command-Line Interface gw-world:/> set to prevent access to the path following the URL hostname which allows the possibility of manually making exceptions from a particular on configured lists of URLs in a browser at worst...
Product Manual
Page 313
.... When the update is controlled through the Anti-Virus configuration in a cluster having updated databases and with Anti-Virus scanning enabled: gw-world:/> set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to NAT this traffic. For example: A local client downloads an infected file from the...
.... When the update is controlled through the Anti-Virus configuration in a cluster having updated databases and with Anti-Virus scanning enabled: gw-world:/> set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to NAT this traffic. For example: A local client downloads an infected file from the...
Product Manual
Page 335
... source port number allocated for a new NAT connection will translate between several source IP addresses and a single source IP address. NAT Dynamic Network Address Translation (NAT) provides a mechanism for public Internet access. To maintain session state information, each connection. NAT Provides many-to-one IP Address Translation NAT provides many-to a different address. Address Translation 7.2. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for translating original source IP addresses to -one IP address on an external...
... source port number allocated for a new NAT connection will translate between several source IP addresses and a single source IP address. NAT Dynamic Network Address Translation (NAT) provides a mechanism for public Internet access. To maintain session state information, each connection. NAT Provides many-to-one IP Address Translation NAT provides many-to a different address. Address Translation 7.2. Hosts and networks behind the firewall's IP address. • Only the firewall needs a public IP address for translating original source IP addresses to -one IP address on an external...
Product Manual
Page 346
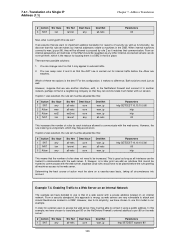
... 2 Allow 3 Allow 4 NAT Src Iface any wan ext2 lan Src Net all-nets all-nets ext2net lannet Dest Iface core core core any other Internet-connected servers; 7.4.1. However, suppose that the NAT rule is unimportant, which is wrong, as all interfaces can communicate much faster with the web server, separate Drop rules would have chosen to translate port 80 on the NetDefend Firewall's external address to port...
... 2 Allow 3 Allow 4 NAT Src Iface any wan ext2 lan Src Net all-nets all-nets ext2net lannet Dest Iface core core core any other Internet-connected servers; 7.4.1. However, suppose that the NAT rule is unimportant, which is wrong, as all interfaces can communicate much faster with the web server, separate Drop rules would have chosen to translate port 80 on the NetDefend Firewall's external address to port...
Product Manual
Page 379
... time when new keys have been issued. • What happens when an employee in the future. • Should the keys be connected directly to the protected network through an unprotected laptop and already-opened VPN connections. VPN • Restricting access through VPNs. • Adapting VPN access policies for services that these services are vulnerable. • Creating DMZs for different groups of users? In other companies through the VPN to needed services...
... time when new keys have been issued. • What happens when an employee in the future. • Should the keys be connected directly to the protected network through an unprotected laptop and already-opened VPN connections. VPN • Restricting access through VPNs. • Adapting VPN access policies for services that these services are vulnerable. • Creating DMZs for different groups of users? In other companies through the VPN to needed services...
Product Manual
Page 383
... be used and these rules is that their private key is the case, Certificate Authority (CA) signed certificates may be desirable to use for routing packets bound for LAN to LAN tunnel authentication. Set up the IPsec Tunnel object as follows: 1. 9.2.2. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan Dest Network lannet Service All The Service used . The root certificate needs to use . Open the WebUI management interface for authentication.
... be used and these rules is that their private key is the case, Certificate Authority (CA) signed certificates may be desirable to use for routing packets bound for LAN to LAN tunnel authentication. Set up the IPsec Tunnel object as follows: 1. 9.2.2. VPN Action Allow Src Interface ipsec_tunnel Src Network remote_net Dest Interface lan Dest Network lannet Service All The Service used . The root certificate needs to use . Open the WebUI management interface for authentication.
Product Manual
Page 442
... not used. 1. By using ID lists, a possible cause can only be that will see that the defined remote network on either end of a tunnel: • Side A Local Network = 192.168.10.0/24 Remote Network = 10.10.10.0/24 • Side B Local Network = 10.10.10.0/24 Remote Network = 192.168.10.0/16 In this you should be set up and the ikesnoop command reports a config mode XAuth problem...
... not used. 1. By using ID lists, a possible cause can only be that will see that the defined remote network on either end of a tunnel: • Side A Local Network = 192.168.10.0/24 Remote Network = 10.10.10.0/24 • Side B Local Network = 10.10.10.0/24 Remote Network = 192.168.10.0/16 In this you should be set up and the ikesnoop command reports a config mode XAuth problem...
Product Manual
Page 527
... more detail is done by using external D-Link databases which contain details of the Web-interface it to the public Internet is ends. Database Console Commands IDP and Anti-Virus (AV) databases can be controlled directly through a number of your current subscription ends! Tip: A registration guide can be downloaded A step-by-step "Registration manual" which update services are constantly being updated and to get access to the database. These...
... more detail is done by using external D-Link databases which contain details of the Web-interface it to the public Internet is ends. Database Console Commands IDP and Anti-Virus (AV) databases can be controlled directly through a number of your current subscription ends! Tip: A registration guide can be downloaded A step-by-step "Registration manual" which update services are constantly being updated and to get access to the database. These...
Product Manual
Page 540
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
... ethernet interface, 92 changing IP addresses, 95 CLI command summary, 95 default gateway, 93 IP address, 93 with DHCP, 93 evasion attack prevention, 318 events, 55 log message receivers, 56 log messages, 55 F Failed Fragment Reassembly setting, 521 filetype download block/allow in FTP ALG, 247 in HTTP ALG, 242 Flood Reboot Time setting, 525 folders with IP rules, 121 with the address book, 81 Fragmented ICMP setting, 522 FTP ALG, 244 command restrictions, 246 connection restriction options, 246 control channel...
Product Manual
Page 541
... LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection Usage setting, 515 logging, 55 advanced settings, 59 memlog, 56 SNMP traps, 58 syslog, 56 login authentication, 366 log messages, 55 Log non IP4 setting, 504 Log Open Fails setting...
... LAN tunnels, 408 quick start guide, 382, 383 Large Buffers (reassembly) setting, 524 Layer Size Consistency setting, 505 LDAP authentication, 359 authentication with PPP, 364 MS Active Directory, 360 servers, 413 link state algorithms, 171 Local Console Timeout setting, 49 local IP address in routes, 145 Log Checksum Errors setting, 504 Log Connections setting, 514 Log Connection Usage setting, 515 logging, 55 advanced settings, 59 memlog, 56 SNMP traps, 58 syslog, 56 login authentication, 366 log messages, 55 Log non IP4 setting, 504 Log Open Fails setting...
Product Manual
Page 542
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...
... CLI, 40 Log Oversized Packets setting, 519 Log Received TTL 0 setting, 504 Log Reverse Opens setting, 514 Log State Violations setting, 514 loopback interfaces, 90, 91 Low Broadcast TTL Action setting, 507 M MAC addresses, 108 management interfaces, 28 advanced settings, 48 configuring remote access, 40 managing NetDefendOS, 28 Max AH Length setting, 518 Max Auto Routes (DHCP) setting, 232 Max Concurrent (reassembly) setting, 524 Max Connections (reassembly) setting, 525 Max Connections setting, 515 Max ESP Length setting, 518 Max GRE Length setting...