Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 6
...Modifications ...12 Cables ...12 Declaration of Conformity for Products Marked with the FCC Logo (United States only) ...13 Products with Wireless LAN Devices 13 Australia Telecom Statement 13 Brazilian Notice ...14 Canadian Notice ...14 Avis Canadien ...15 European Union Regulatory Notice 16 Products...Union Only 17 European Network Compatibility Declarations (European Union Only 17 India Telegraph Act Notice 17 Japanese Notice ...18 Wireless LAN 802.11b devices 18 Wireless LAN 802.11g devices 18 Korean Notice ...18 NCC Notice ...19 Environmental Agency Notices ...19 Disposal of Waste ...
...Modifications ...12 Cables ...12 Declaration of Conformity for Products Marked with the FCC Logo (United States only) ...13 Products with Wireless LAN Devices 13 Australia Telecom Statement 13 Brazilian Notice ...14 Canadian Notice ...14 Avis Canadien ...15 European Union Regulatory Notice 16 Products...Union Only 17 European Network Compatibility Declarations (European Union Only 17 India Telegraph Act Notice 17 Japanese Notice ...18 Wireless LAN 802.11b devices 18 Wireless LAN 802.11g devices 18 Korean Notice ...18 NCC Notice ...19 Environmental Agency Notices ...19 Disposal of Waste ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 18
...can be determined by turning the equipment off and on . and region-specific nonwireless and wireless regulatory notices and compliance information for the computer product. In some environments, the use of wireless devices may be notified that are not expressly approved by one or more integrated... wireless devices may be made to this equipment does cause harmful interference to radio or television...
...can be determined by turning the equipment off and on . and region-specific nonwireless and wireless regulatory notices and compliance information for the computer product. In some environments, the use of wireless devices may be notified that are not expressly approved by one or more integrated... wireless devices may be made to this equipment does cause harmful interference to radio or television...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 19
...13 For questions regarding this device is closed, if integrated into the unit. WARNING! Nevertheless, the device should not be equipped with Wireless LAN Devices This product may be less than 20 cm (8 inches), including when the computer display is below the FCC radio frequency exposure...included with Part 15 of the FCC Rules. These radar stations can cause interference with this device. To identify the location of the wireless antennae, refer to Radio Frequency Radiation The radiated output power of this FCC declaration, contact: Hewlett-Packard Company P.O. Box 692000, Mail ...
...13 For questions regarding this device is closed, if integrated into the unit. WARNING! Nevertheless, the device should not be equipped with Wireless LAN Devices This product may be less than 20 cm (8 inches), including when the computer display is below the FCC radio frequency exposure...included with Part 15 of the FCC Rules. These radar stations can cause interference with this device. To identify the location of the wireless antennae, refer to Radio Frequency Radiation The radiated output power of this FCC declaration, contact: Hewlett-Packard Company P.O. Box 692000, Mail ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 20
...interference to 2 conditions. limit is 3 dBi. For the Atheros AR5BHB92 card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. Wireless operation is subject to co-channel mobile satellite systems. High-power radar is restricted to indoor use, due to its operation in the 5....227;o correta. The second is that may cause undesired operation of the 5.25to 5.35-GHz and 5.65- For the Belkin Dual-Band Wireless A+G Desktop Card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. For the Ralink 802.11 b/g/n WLAN PCIe 1x card the maximum ...
...interference to 2 conditions. limit is 3 dBi. For the Atheros AR5BHB92 card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. Wireless operation is subject to co-channel mobile satellite systems. High-power radar is restricted to indoor use, due to its operation in the 5....227;o correta. The second is that may cause undesired operation of the 5.25to 5.35-GHz and 5.65- For the Belkin Dual-Band Wireless A+G Desktop Card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. For the Ralink 802.11 b/g/n WLAN PCIe 1x card the maximum ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 23
... certain restrictions apply: This product may have internetworking difficulties in the first instance. Products with 2.4-GHz Wireless LAN Devices France For 2.4 GHz Wireless LAN operation of this license, please contact The Wireless Planning & Coordination Wing, Ministry of Communications, Sanchar Bhavan New Delhi. Pour une utilisation à ...peuvent être utilisées. Please consult with your equipment supplier in PSTN networks that an IEEE 802.11a wireless LAN end user obtain a license. For outdoor use, only 2400-2454 MHz frequency band (channels 1-9) may be used .
... certain restrictions apply: This product may have internetworking difficulties in the first instance. Products with 2.4-GHz Wireless LAN Devices France For 2.4 GHz Wireless LAN operation of this license, please contact The Wireless Planning & Coordination Wing, Ministry of Communications, Sanchar Bhavan New Delhi. Pour une utilisation à ...peuvent être utilisées. Please consult with your equipment supplier in PSTN networks that an IEEE 802.11a wireless LAN end user obtain a license. For outdoor use, only 2400-2454 MHz frequency band (channels 1-9) may be used .
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 24
Japanese Notice B VCCI-B Wireless LAN 802.11b devices Wireless LAN 802.11g devices Korean Notice 18 Chapter 2 Regulatory Agency Notices ENWW
Japanese Notice B VCCI-B Wireless LAN 802.11b devices Wireless LAN 802.11g devices Korean Notice 18 Chapter 2 Regulatory Agency Notices ENWW
d510/d530 Software Image Comparison Overview
Page 4
D510/D530 Software Image Comparison Overview 3rd Party Vendor Certification: Novell &#...; Hardware/OEM specific drivers and files: ‰ Graphics ‰ Network Interface Card ‰ Audio ‰ Modem ‰ Wireless LAN ‰ HP Monitor INF ‰ Chipset INF ‰ HP SLP Driver files for the specific hardware devices included with...that HP identified as graphics, network interface cards, modems, etc.) and a small number of the HP Compaq Business Desktop product introduction. In addition, an HP internally-supported application called Application Installer provides a user interface to ...
D510/D530 Software Image Comparison Overview 3rd Party Vendor Certification: Novell &#...; Hardware/OEM specific drivers and files: ‰ Graphics ‰ Network Interface Card ‰ Audio ‰ Modem ‰ Wireless LAN ‰ HP Monitor INF ‰ Chipset INF ‰ HP SLP Driver files for the specific hardware devices included with...that HP identified as graphics, network interface cards, modems, etc.) and a small number of the HP Compaq Business Desktop product introduction. In addition, an HP internally-supported application called Application Installer provides a user interface to ...
d510/d530 Software Image Comparison Overview
Page 5
...Access Keyboard support software* HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - HP also supports customers who install Windows 2000 on the HP driver download Web site. Many of this white paper. D510/D530 Software Image Comparison Overview Microsoft ...Delivery" section of the drivers and components denoted with Service Pack 3 is the preinstalled operating system for select HP Compaq Business Desktops d530 models. The following table compares the delivered operating systems components and drivers for HP PCMCIA Reader Via PCI Card ...
...Access Keyboard support software* HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - HP also supports customers who install Windows 2000 on the HP driver download Web site. Many of this white paper. D510/D530 Software Image Comparison Overview Microsoft ...Delivery" section of the drivers and components denoted with Service Pack 3 is the preinstalled operating system for select HP Compaq Business Desktops d530 models. The following table compares the delivered operating systems components and drivers for HP PCMCIA Reader Via PCI Card ...
d510/d530 Software Image Comparison Overview
Page 7
HP also supports customers who install Windows XP on select HP Compaq Business Desktops d530 models. Lucent 56K v.90 Win Modem Driver * - Roxio Easy CD Creator (upgrade package) * 5.3.4.21 SP12 B2D OEM START PAGE for ...HP PCMCIA Reader * - Input Device Software Easy Access Keyboard support software * O2 Micro Basic Smartcard Keyboard Drivers * HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - Desktop 3.2.41.136 F - PSeries Drivers for Windows * Altiris eXpress agent (available at: http://h18000.www1.hp.com/im/swdeploy...
HP also supports customers who install Windows XP on select HP Compaq Business Desktops d530 models. Lucent 56K v.90 Win Modem Driver * - Roxio Easy CD Creator (upgrade package) * 5.3.4.21 SP12 B2D OEM START PAGE for ...HP PCMCIA Reader * - Input Device Software Easy Access Keyboard support software * O2 Micro Basic Smartcard Keyboard Drivers * HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - Desktop 3.2.41.136 F - PSeries Drivers for Windows * Altiris eXpress agent (available at: http://h18000.www1.hp.com/im/swdeploy...
d510/d530 Software Image Comparison Overview
Page 10
... 1.04.1 1.1.5.0 5.00 K 5.00.1012 A 1.00 A 4.07 A 3.02 A 1.10 A 1.12 A 10 Table 4. Windows 98 Software Components for HP Compaq Business Desktop d530 Software Component Win98 Intel Extreme Graphics Driver Nvidia Graphics driver ADI SoundMax Audio Driver for Windows 98SE/2000/ME/XP Broadcom NetExtreme 10/100/1000...HP WLAN 802.11b WL220 Configuration Utility HP WLAN 802.11b WL220 Wireless Controller Driver Insight Management Agent for Clients Intel Chipset Support for Windows 98/ME/2000/XP Business Desktops BIOS Utility for Replicated Setup Diagnostics for Windows 98 include audio, video...
... 1.04.1 1.1.5.0 5.00 K 5.00.1012 A 1.00 A 4.07 A 3.02 A 1.10 A 1.12 A 10 Table 4. Windows 98 Software Components for HP Compaq Business Desktop d530 Software Component Win98 Intel Extreme Graphics Driver Nvidia Graphics driver ADI SoundMax Audio Driver for Windows 98SE/2000/ME/XP Broadcom NetExtreme 10/100/1000...HP WLAN 802.11b WL220 Configuration Utility HP WLAN 802.11b WL220 Wireless Controller Driver Insight Management Agent for Clients Intel Chipset Support for Windows 98/ME/2000/XP Business Desktops BIOS Utility for Replicated Setup Diagnostics for Windows 98 include audio, video...
Wireless Security
Page 1
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Reverse Proxy 8 Conclusion...9 For more information...10 1 Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs.
Wireless Security
Page 2
However, as notebook and handheld PCs) with HP Wi-Fi and other aspects of Mobility and Connectivity. But regardless of data integrity. 2 securing that can be associated with wireless equipment has the potential to increase productivity by authorized means. Data ...circumstances. Problem Statement Equipping today's mobile workforce with other mobile connectivity solutions. Historical information/background Most security issues for wireless solutions. At every step, there are unrelated to do with using Encryption and Authentication. All transmitted packets should be...
However, as notebook and handheld PCs) with HP Wi-Fi and other aspects of Mobility and Connectivity. But regardless of data integrity. 2 securing that can be associated with wireless equipment has the potential to increase productivity by authorized means. Data ...circumstances. Problem Statement Equipping today's mobile workforce with other mobile connectivity solutions. Historical information/background Most security issues for wireless solutions. At every step, there are unrelated to do with using Encryption and Authentication. All transmitted packets should be...
Wireless Security
Page 3
... security features that exist within the device BIOS. the HP ProtectTools Security Manager - As a result of technologies: • Notebook and desktop computers can be added easily by using it. If a technology is available on a range of HP commercial products. • Biometrics are... still challenges that not only meets mobility and wireless requirements, but is a security platform that may be difficult to deploy and use • Manageability: technologies and features that are difficult ...
... security features that exist within the device BIOS. the HP ProtectTools Security Manager - As a result of technologies: • Notebook and desktop computers can be added easily by using it. If a technology is available on a range of HP commercial products. • Biometrics are... still challenges that not only meets mobility and wireless requirements, but is a security platform that may be difficult to deploy and use • Manageability: technologies and features that are difficult ...
Wireless Security
Page 4
... crack the web key. In this solution introduced interoperability issues. Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for WEP Vulnerability Although VPN provides adequate security, there may be accessed using reverse proxy. Access is... Server based Access point based This extension of data integrity • Poor key management and • Access Point association All wireless vendors have developed to manage. Spoofing the MAC address is possible, but it is hard to predict future changes in four main...
... crack the web key. In this solution introduced interoperability issues. Virtual Private Network Implementations HP solutions: HP Production WLAN HP Wireless Internet Access Vendor Solutions for WEP Vulnerability Although VPN provides adequate security, there may be accessed using reverse proxy. Access is... Server based Access point based This extension of data integrity • Poor key management and • Access Point association All wireless vendors have developed to manage. Spoofing the MAC address is possible, but it is hard to predict future changes in four main...
Wireless Security
Page 5
... EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the clear, this mode of operation does not provide adequate security Limiting propagation is hard, although it would...the source, for WEP Vulnerability Hiding the Service Set Identifier (SSID) is available to increase the level of security for new wireless LANs, and manage existing solutions with software or firmware updates. Other security measures Hiding the SSID Limiting the RF propagation Vendor ...
... EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the clear, this mode of operation does not provide adequate security Limiting propagation is hard, although it would...the source, for WEP Vulnerability Hiding the Service Set Identifier (SSID) is available to increase the level of security for new wireless LANs, and manage existing solutions with software or firmware updates. Other security measures Hiding the SSID Limiting the RF propagation Vendor ...
Wireless Security
Page 6
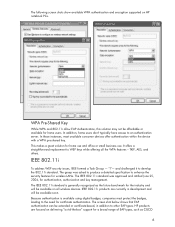
...users don't typically have access to develop the 802.11i standard. "I"- The group was approved and ratified June 25, 2004, for wireless LANs. The screen shot below shows that EAP authentication can be affordable or available for the industry and will be available on all...devices offer authentication within the device with a WPA pre-shared key. HP products are currently in addition to WEP keys while offering all wireless devices. This makes a great solution for certificate authentication. It offers a straightforward replacement to other EAP types. IEEE 802.11i products ...
...users don't typically have access to develop the 802.11i standard. "I"- The group was approved and ratified June 25, 2004, for wireless LANs. The screen shot below shows that EAP authentication can be affordable or available for the industry and will be available on all...devices offer authentication within the device with a WPA pre-shared key. HP products are currently in addition to WEP keys while offering all wireless devices. This makes a great solution for certificate authentication. It offers a straightforward replacement to other EAP types. IEEE 802.11i products ...
Wireless Security
Page 7
..., or even remote procedure calls over http. The HP solution is required, in order to data from heterogeneous networks. One aspect of the Internet and wireless connectivity increased the demand for this is reverse proxy. 7 EAP and many other EAP implementations.
..., or even remote procedure calls over http. The HP solution is required, in order to data from heterogeneous networks. One aspect of the Internet and wireless connectivity increased the demand for this is reverse proxy. 7 EAP and many other EAP implementations.
Wireless Security
Page 8
... a huge impact on mobility in terms of reverse proxy to be tightly integrated and will be the optimal encryption for notebooks accessing wireless and mobile networks. Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. This is proving to obtain pervasive access. Microsoft SQL 2005 and...
... a huge impact on mobility in terms of reverse proxy to be tightly integrated and will be the optimal encryption for notebooks accessing wireless and mobile networks. Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. This is proving to obtain pervasive access. Microsoft SQL 2005 and...
Wireless Security
Page 9
... with unique features of the Access Point. With the 802.11 standard, the authentication server can be part of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed from any network without VPN, using this standard will continue to WPA..., 802.11i - WPA, an interim solution to WEP vulnerability, is no need for wireless security that address many wireless concerns related to find stronger data protection and user authentication, as well as Hewlett-Packard, CISCO and Microsoft are working together...
... with unique features of the Access Point. With the 802.11 standard, the authentication server can be part of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed from any network without VPN, using this standard will continue to WPA..., 802.11i - WPA, an interim solution to WEP vulnerability, is no need for wireless security that address many wireless concerns related to find stronger data protection and user authentication, as well as Hewlett-Packard, CISCO and Microsoft are working together...
Wireless Security
Page 10
For more secure mobile computing environment. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. The information...
For more secure mobile computing environment. Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company, L.P. The information...