Compaq ArmadaStation EM Maintenance and Service Guide
Page 4
......5-14 5.10 Left Speaker ...5-23 5.11 Control Bay ...5-24 5.12 Control Panel...5-26 5.13 Mechanism Assembly...5-27 5.14 Power Supply ...5-29 5.15 Backplane...5-31 chapter 6 SPECIFICATIONS ...6-1 appendix 1 CONNECTOR PIN ASSIGNMENTS ...A-1 appendix 2 POWER CORD SET REQUIREMENTS ...B-1 INDEX ...I-1 iv Contents
......5-14 5.10 Left Speaker ...5-23 5.11 Control Bay ...5-24 5.12 Control Panel...5-26 5.13 Mechanism Assembly...5-27 5.14 Power Supply ...5-29 5.15 Backplane...5-31 chapter 6 SPECIFICATIONS ...6-1 appendix 1 CONNECTOR PIN ASSIGNMENTS ...A-1 appendix 2 POWER CORD SET REQUIREMENTS ...B-1 INDEX ...I-1 iv Contents
Compaq ArmadaStation EM Maintenance and Service Guide
Page 5
... provide at the component level or to make changes to the Compaq ArmadaStation EM without notice. IMPORTANT: Text set off in this manner indicates that failure to follow directions in the caution could result in this manner presents clarifying information or specific instructions. Because of the complexity of information. All troubleshooting and...
... provide at the component level or to make changes to the Compaq ArmadaStation EM without notice. IMPORTANT: Text set off in this manner indicates that failure to follow directions in the caution could result in this manner presents clarifying information or specific instructions. Because of the complexity of information. All troubleshooting and...
Compaq ArmadaStation EM Maintenance and Service Guide
Page 62
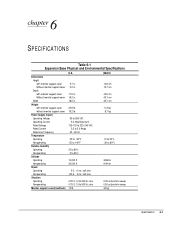
... 6-1 Expansion Base Physical and Environmental Specifications U.S. Metric Dimensions Height with monitor support cover Without monitor support cover Depth with monitor support cover Without monitor support cover Width Weight with monitor support ... 45.7 cm 11.3 kg 8.7 kg 10 to 35°C -30 to 60°C 3048 m 9144 m 0.25 octave/min sweep 0.50 octave/min sweep 34 kg Specifications 6-1
... 6-1 Expansion Base Physical and Environmental Specifications U.S. Metric Dimensions Height with monitor support cover Without monitor support cover Depth with monitor support cover Without monitor support cover Width Weight with monitor support ... 45.7 cm 11.3 kg 8.7 kg 10 to 35°C -30 to 60°C 3048 m 9144 m 0.25 octave/min sweep 0.50 octave/min sweep 34 kg Specifications 6-1
Compaq ArmadaStation EM Maintenance and Service Guide
Page 63
The Expansion Base is designed for IT power systems with ANSI specifications (no. NOTE: This product is designed in accordance with phase-to-phase voltage not exceeding 240Vrms minimum charge. 6-2 Specifications X3.131-1993, Rev 10h) and IEEE 802.3 specifications.
The Expansion Base is designed for IT power systems with ANSI specifications (no. NOTE: This product is designed in accordance with phase-to-phase voltage not exceeding 240Vrms minimum charge. 6-2 Specifications X3.131-1993, Rev 10h) and IEEE 802.3 specifications.
Compaq ArmadaStation EM Maintenance and Service Guide
Page 71
... be Type VCT or VCTF, 3-conductor, 0.75mm2 conductor size. B-2 Power Cord Set Requirements The wall plug must be Type HO5VV-F, 3-conductor, 1.0 mm2 conductor size. Country-Specific Requirements 3-Conductor Power Cord Set Requirements-By Country Country Accredited Agency Applicable Note Numbers Australia EANSW 1 Austria OVE 1 Belgium CEBC 1 Canada CSA 2 Denmark DEMKO 1 Finland...
... be Type VCT or VCTF, 3-conductor, 0.75mm2 conductor size. B-2 Power Cord Set Requirements The wall plug must be Type HO5VV-F, 3-conductor, 1.0 mm2 conductor size. Country-Specific Requirements 3-Conductor Power Cord Set Requirements-By Country Country Accredited Agency Applicable Note Numbers Australia EANSW 1 Austria OVE 1 Belgium CEBC 1 Canada CSA 2 Denmark DEMKO 1 Finland...
Compaq ArmadaStation EM Maintenance and Service Guide
Page 72
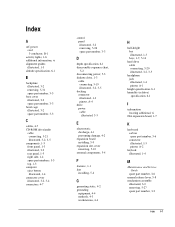
... 1-4 connector cover illustrated, 3-2, 3-4 connectors, 4-7 control panel illustrated, 3-2 removing, 5-26 spare part number, 3-3 D depth specification, 6-1 disassembly sequence chart, 5-2 disconnecting power, 5-3 diskette drive, 1-3 cable connecting, 5-19 illustrated, 3-2, 3-5 docking connector illustrated... 1-7, 5-14 hard drive cable connecting, 5-20 illustrated, 3-2, 3-5 headphone jack illustrated, 1-4 pinout, A-1 height specification, 6-1 humidity (relative) specification, 6-1 I information locating additional, vi ISA expansion board, 1-7 K keyboard carbon spare part number, 3-6 connector ...
... 1-4 connector cover illustrated, 3-2, 3-4 connectors, 4-7 control panel illustrated, 3-2 removing, 5-26 spare part number, 3-3 D depth specification, 6-1 disassembly sequence chart, 5-2 disconnecting power, 5-3 diskette drive, 1-3 cable connecting, 5-19 illustrated, 3-2, 3-5 docking connector illustrated... 1-7, 5-14 hard drive cable connecting, 5-20 illustrated, 3-2, 3-5 headphone jack illustrated, 1-4 pinout, A-1 height specification, 6-1 humidity (relative) specification, 6-1 I information locating additional, vi ISA expansion board, 1-7 K keyboard carbon spare part number, 3-6 connector ...
Compaq ArmadaStation EM Maintenance and Service Guide
Page 73
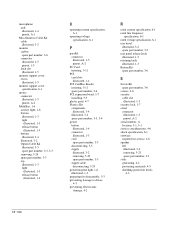
...number, 3-3 top illustrated, 1-3 light illustrated, 1-3 release button illustrated, 1-3 O operating current specification, 6-1 operating voltage specification, 6-1 P parallel connector illustrated, 1-5 pinout, A-2 PC Card inserting, 5-11 PCI card slots illustrated, 1-4 PCI CardBus Reader inserting, 5-11 spare part... disassembly, 5-3 preventing damage to drives, 4-3 preventing electrostatic damage, 4-2 R rated current specification, 6-1 rated line frequency specification, 6-1 rated voltage specification, 6-1 rear bezel illustrated, 3-2 spare part number, 3-3 rear panel release latch illustrated...
...number, 3-3 top illustrated, 1-3 light illustrated, 1-3 release button illustrated, 1-3 O operating current specification, 6-1 operating voltage specification, 6-1 P parallel connector illustrated, 1-5 pinout, A-2 PC Card inserting, 5-11 PCI card slots illustrated, 1-4 PCI CardBus Reader inserting, 5-11 spare part... disassembly, 5-3 preventing damage to drives, 4-3 preventing electrostatic damage, 4-2 R rated current specification, 6-1 rated line frequency specification, 6-1 rated voltage specification, 6-1 rear bezel illustrated, 3-2 spare part number, 3-3 rear panel release latch illustrated...
Compaq ArmadaStation EM Maintenance and Service Guide
Page 74
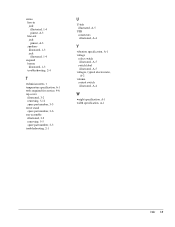
stereo line-in jack illustrated, 1-4 pinout, A-3 line-out jack pinout, A-3 speakers illustrated, 1-3 jack illustrated, 1-4 suspend button illustrated, 1-3 troubleshooting, 2-4 T technician notes, v temperature specification, 6-1 tools required for service, 4-6 top cover illustrated, 3-2 removing, 5-12 spare part number, 3-3 tower stand spare part number, 3-6 tray assembly illustrated, 3-2 removing, 5-5 spare part number, 3-3 troubleshooting, 2-1 U U-...
stereo line-in jack illustrated, 1-4 pinout, A-3 line-out jack pinout, A-3 speakers illustrated, 1-3 jack illustrated, 1-4 suspend button illustrated, 1-3 troubleshooting, 2-4 T technician notes, v temperature specification, 6-1 tools required for service, 4-6 top cover illustrated, 3-2 removing, 5-12 spare part number, 3-3 tower stand spare part number, 3-6 tray assembly illustrated, 3-2 removing, 5-5 spare part number, 3-3 troubleshooting, 2-1 U U-...
Installing Microsoft Windows Millennium Edition on Compaq Armada E700, M700, E500, V300, and M300
Page 7
...to manually upgrade to table 1 for your Armada notebook have been installed. A. Removing Software If you need to ensure that all of the specific drivers and support software for a list of this information. TABLE 3 - Properly shutdown your system. Compaq strongly recommends a "cold dock" for Windows.... Control Panel → Add/Remove Programs ... Place the computer in the docking station or convenience base and then turn on Compaq Armada E700, M700, E500, V300, and M300 7 Appendices A. Under Windows 98, applications and utilities can be manually turned off, do so now....
...to manually upgrade to table 1 for your Armada notebook have been installed. A. Removing Software If you need to ensure that all of the specific drivers and support software for a list of this information. TABLE 3 - Properly shutdown your system. Compaq strongly recommends a "cold dock" for Windows.... Control Panel → Add/Remove Programs ... Place the computer in the docking station or convenience base and then turn on Compaq Armada E700, M700, E500, V300, and M300 7 Appendices A. Under Windows 98, applications and utilities can be manually turned off, do so now....
Installing Microsoft Windows Millennium Edition on Compaq Armada E700, M700, E500, V300, and M300
Page 9
...PCs. No testing was based on a newly formatted hard drive. What hardware does Windows Me require? Microsoft Windows Millennium Edition on Armada notebooks? Q & A Why doesn't Compaq... provide full support for drivers included in the OS or check with some additional drivers are being made available by Compaq was performed on the Armada E700, M700, E500, V300, and M300 families with Windows Me by Compaq...specific drivers work with the hardware vendor for many devices, including most satisfactory results. Is Compaq making Windows Me specific ...
...PCs. No testing was based on a newly formatted hard drive. What hardware does Windows Me require? Microsoft Windows Millennium Edition on Armada notebooks? Q & A Why doesn't Compaq... provide full support for drivers included in the OS or check with some additional drivers are being made available by Compaq was performed on the Armada E700, M700, E500, V300, and M300 families with Windows Me by Compaq...specific drivers work with the hardware vendor for many devices, including most satisfactory results. Is Compaq making Windows Me specific ...
Wireless Security
Page 3
This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into context, the paper ... lie and what can be eavesdroppers' gold mine" (Wall Street Journal Online, April 27, 2001). 2 Gomes. This ability to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for managing corporate network security...
This is so in part because many users are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of wireless security into context, the paper ... lie and what can be eavesdroppers' gold mine" (Wall Street Journal Online, April 27, 2001). 2 Gomes. This ability to Assure E-Business Success" (http://activeanswers.compaq.com/ActiveAnswers/Render/1,1027,1317-6-100-225-1,00.html February, 2000) for important detail on best practices and established technologies for managing corporate network security...
Wireless Security
Page 6
...of the tasks that the devices hold. Minimizing vulnerability to protect the hardware and the data that notebook computers address. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible... stationary devices. Companies treat the devices as opposed to continue working. However, handheld computers and PDAs are on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of the transmission medium (air). Loss and Theft Mobile access...
...of the tasks that the devices hold. Minimizing vulnerability to protect the hardware and the data that notebook computers address. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible... stationary devices. Companies treat the devices as opposed to continue working. However, handheld computers and PDAs are on Compaq notebook computers, see http://www.compaq.com/showroom/handhelds.html. This violates the security tenet of the transmission medium (air). Loss and Theft Mobile access...
Wireless Security
Page 7
... solution to the problem of securing data transmissions to and from the device, in a wallet for mobile access devices. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device in the plastic. Simply keeping the smart card separate...
... solution to the problem of securing data transmissions to and from the device, in a wallet for mobile access devices. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the device in the plastic. Simply keeping the smart card separate...
Wireless Security
Page 9
...server. Notwithstanding the protection offered, such firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use . Software-based firewalls are available from Network ICE Corporation. either because of the...code every sixty seconds in strict synchronicity with his or her PIN. For example, they roam. SecurID SecurID is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. Connectivity Technologies The second key juncture...
...server. Notwithstanding the protection offered, such firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use . Software-based firewalls are available from Network ICE Corporation. either because of the...code every sixty seconds in strict synchronicity with his or her PIN. For example, they roam. SecurID SecurID is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. Connectivity Technologies The second key juncture...
Wireless Security
Page 11
...'s NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. Wireless Security White Paper 11 Wireless Personal-area Networks...
...'s NT DoCoMo uses I-mode technology in Europe, is a TDMA technology. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in its market. Wireless Security White Paper 11 Wireless Personal-area Networks...
Wireless Security
Page 13
... encryption and tunneling. Those technologies are slightly less secure since they include only digital encoding without encryption. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to achieving security for the wireless exchange of information over public highways...
... encryption and tunneling. Those technologies are slightly less secure since they include only digital encoding without encryption. and Entrust do not have point solutions to specific applications that run on the various operating systems. Public Key Infrastructure Most approaches to achieving security for the wireless exchange of information over public highways...
Wireless Security
Page 19
... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. the base station is ... and the subscriber identification key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
... hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of encryption. the base station is ... and the subscriber identification key. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products...
Wireless Security
Page 20
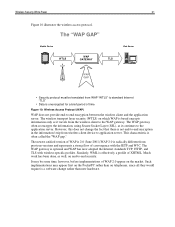
...adds a function that allows a WAP client to authenticate themselves by means of random or bulk transmissions over a WWAN. WAP 2.0 is designed specifically for the secure download of WAP used WTLS server certificates to authenticate a WTLS server to a WTLS client, and to eliminate the "WAP ...uses a transmission technique called "spread spectrum" that occur as to provide a basis for WAP applications. WAP 2.0 was developed to solve problems specific to a WTLS server. WTLS is based on Transport Layer Security (TLS), a security layer used by the military with which authenticate a ...
...adds a function that allows a WAP client to authenticate themselves by means of random or bulk transmissions over a WWAN. WAP 2.0 is designed specifically for the secure download of WAP used WTLS server certificates to authenticate a WTLS server to a WTLS client, and to eliminate the "WAP ...uses a transmission technique called "spread spectrum" that occur as to provide a basis for WAP applications. WAP 2.0 was developed to solve problems specific to a WTLS server. WTLS is based on Transport Layer Security (TLS), a security layer used by the military with which authenticate a ...
Wireless Security
Page 21
... period of WAP 2.0 appear on telephones, since all they would require is a software change the fact that there is effectively a profile of convergence with wireless-specific profiles. Wireless Security White Paper 21 Figure 10 illustrates the wireless access protocol.
... period of WAP 2.0 appear on telephones, since all they would require is a software change the fact that there is effectively a profile of convergence with wireless-specific profiles. Wireless Security White Paper 21 Figure 10 illustrates the wireless access protocol.
Wireless Security
Page 24
...The attacker would be used to authenticate user access to any authentication database (EAP RADIUS server). Access Points The third key juncture in this effort. Compaq is a piece of hardware, a hub, which data travels to the wired lines or Internet. For example, a company may have a private.... 6 Wired Equivalent Privacy (WEP) is used to provide data security equivalent to any closed network. In the current draft specification, a strengthened version of a wired LAN without privacy-enhancing encryption techniques. It can be the future encryption standard. According to the WEP...
...The attacker would be used to authenticate user access to any authentication database (EAP RADIUS server). Access Points The third key juncture in this effort. Compaq is a piece of hardware, a hub, which data travels to the wired lines or Internet. For example, a company may have a private.... 6 Wired Equivalent Privacy (WEP) is used to provide data security equivalent to any closed network. In the current draft specification, a strengthened version of a wired LAN without privacy-enhancing encryption techniques. It can be the future encryption standard. According to the WEP...