Administration Guide
Page 11
... IPS signature file regularly to protect your SPI Firewall, IP Based Access Control List (ACL), Network Address Port Translation (NAPT), and Virtual Private Network (VPN) to communicate with a total of 1101 rules. As of security. The following categories: DDoS, Buffer Overflow, Access Control, Scan, Trojan Horse, Misc., P2P, IM, Virus, Worm, and Web Attacks. Cisco WRVS4400N Wireless-N Gigabit Security Router...
... IPS signature file regularly to protect your SPI Firewall, IP Based Access Control List (ACL), Network Address Port Translation (NAPT), and Virtual Private Network (VPN) to communicate with a total of 1101 rules. As of security. The following categories: DDoS, Buffer Overflow, Access Control, Scan, Trojan Horse, Misc., P2P, IM, Virus, Worm, and Web Attacks. Cisco WRVS4400N Wireless-N Gigabit Security Router...
Administration Guide
Page 136
Click Browse to the file in the Signature Update field c. Click Update. Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 136 Alternatively, enter the path to locate the signature file. STEP 5 Click Save. STEP 3 In the ...cisco.com to the FTP server. The default is Disable. • FTP-FTP attacks use weakness on TELNET protocol to be executed on the TELNET server. Setting Up and Configuring the WRVS4400N Wireless-N Router Configuring IPS Settings 5 To configure general IPS settings: STEP 1 Click IPS > Configuration. STEP 2 In the IPS...
Click Browse to the file in the Signature Update field c. Click Update. Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 136 Alternatively, enter the path to locate the signature file. STEP 5 Click Save. STEP 3 In the ...cisco.com to the FTP server. The default is Disable. • FTP-FTP attacks use weakness on TELNET protocol to be executed on the TELNET server. Setting Up and Configuring the WRVS4400N Wireless-N Router Configuring IPS Settings 5 To configure general IPS settings: STEP 1 Click IPS > Configuration. STEP 2 In the IPS...
Administration Guide
Page 140
Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 140 These attacks includes DoS/DDoS, Buffer Overflow, Web Attack, Scan, Trojan Horse, and IM / P2P. STEP 2 View the administration information. • Signature Version-Displays the version of the signature patterns file loaded in the router that protects against malicious threats. • Last Time Upload-Displays the time when the...
Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 140 These attacks includes DoS/DDoS, Buffer Overflow, Web Attack, Scan, Trojan Horse, and IM / P2P. STEP 2 View the administration information. • Signature Version-Displays the version of the signature patterns file loaded in the router that protects against malicious threats. • Last Time Upload-Displays the time when the...
Administration Guide
Page 221
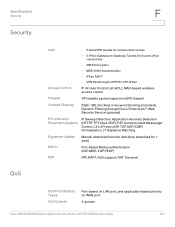
... blocking (included), Dynamic Filtering through Cisco ProtectLink™ Web Security Service (optional) IPS (Intrusion Prevention System) IP Sweep Detection, Application Anomaly Detection (HTTP,F TP,Telnet, RCP),P 2P Control,I nstant Messenger Control, L3-L4 Protocol (IP, TCP, UDP, ICMP) Normalization, L7 Signature Matching Signature Update Manual download from the web (free...NAT Traversal QoS Prioritization Types QoS Queues Port-based on LAN port, and application-based priority on WAN port 4 queues Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 221
... blocking (included), Dynamic Filtering through Cisco ProtectLink™ Web Security Service (optional) IPS (Intrusion Prevention System) IP Sweep Detection, Application Anomaly Detection (HTTP,F TP,Telnet, RCP),P 2P Control,I nstant Messenger Control, L3-L4 Protocol (IP, TCP, UDP, ICMP) Normalization, L7 Signature Matching Signature Update Manual download from the web (free...NAT Traversal QoS Prioritization Types QoS Queues Port-based on LAN port, and application-based priority on WAN port 4 queues Cisco WRVS4400N Wireless-N Gigabit Security Router with VPN Administration Guide 221