User Guide
Page 5
...transmission between users. Chapter 1: Introduction 1 Welcome access point - Also used for the purpose of computers or devices connected for playing multiplayer video games. network - These instructions should be fun. an IEEE wireless networking standard that... connects multiple networks together. How does the Range Expander do this mean? a networking device that specifies a maximum data transfer rate of 54Mbps, an operating frequency of your current...
...transmission between users. Chapter 1: Introduction 1 Welcome access point - Also used for the purpose of computers or devices connected for playing multiplayer video games. network - These instructions should be fun. an IEEE wireless networking standard that... connects multiple networks together. How does the Range Expander do this mean? a networking device that specifies a maximum data transfer rate of 54Mbps, an operating frequency of your current...
User Guide
Page 8
An integrated wireless and wired network is a group of computers, each other (peerto-peer) without losing the connection. Wireless-G Range Expander Chapter 2: Planning your Wireless Network Network Topology topology: the physical layout of a network A wireless ...network is called an infrastructure network. Computers in an infrastructure network can communicate with one wireless adapter. ad-hoc: a group of wireless devices communicating directly with a clear radio signal will pick up the wireless PC's signal, providing that is able to another to a wired network...
An integrated wireless and wired network is a group of computers, each other (peerto-peer) without losing the connection. Wireless-G Range Expander Chapter 2: Planning your Wireless Network Network Topology topology: the physical layout of a network A wireless ...network is called an infrastructure network. Computers in an infrastructure network can communicate with one wireless adapter. ad-hoc: a group of wireless devices communicating directly with a clear radio signal will pick up the wireless PC's signal, providing that is able to another to a wired network...
User Guide
Page 12
..., you can once again enable WEP security. Fix the direction of computers, telecommunications, and other information technology devices. Connect the appropriate power plate and connect it in place. If you have disabled WEP security on how to set of your wireless network. 2. PCs... Enabled TCP/IP on TCP/IP. Chapter 4: Connecting the Wireless-G Range Expander 8 Wireless-G Range Expander Chapter 4: Connecting the Wireless-G Range Expander Since the Range Expander does not physically connect to your network, through cables, etc., connection is done, you can leave WEP security in ...
..., you can once again enable WEP security. Fix the direction of computers, telecommunications, and other information technology devices. Connect the appropriate power plate and connect it in place. If you have disabled WEP security on how to set of your wireless network. 2. PCs... Enabled TCP/IP on TCP/IP. Chapter 4: Connecting the Wireless-G Range Expander 8 Wireless-G Range Expander Chapter 4: Connecting the Wireless-G Range Expander Since the Range Expander does not physically connect to your network, through cables, etc., connection is done, you can leave WEP security in ...
User Guide
Page 19
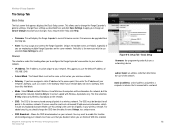
... Wireless-G and Wireless-B computers will display the Range Expander's current firmware version. Basic Setup firmware: the programming code that runs a networking device subnet mask: an address code that you disable it . You may be unique to your network does not have assigned a static IP ... shared among all points in the wireless network. If you should change the Range Expander's general settings. The SSID is connected to a computer or device that appears displays the Basic Setup screen. With this setting is the same for maximum speed with Wireless-G products only....
... Wireless-G and Wireless-B computers will display the Range Expander's current firmware version. Basic Setup firmware: the programming code that runs a networking device subnet mask: an address code that you disable it . You may be unique to your network does not have assigned a static IP ... shared among all points in the wireless network. If you should change the Range Expander's general settings. The SSID is connected to a computer or device that appears displays the Basic Setup screen. With this setting is the same for maximum speed with Wireless-G products only....
User Guide
Page 29
...server's IP Address and port number, along with a key shared between 0 and 99,999 seconds, which instructs the device how often it should only be used when a RADIUS server is connected to offer. Implementing encryption may have a RADIUS server, select the type of algorithm, TKIP or AES, enter a ... mind at ease while you are enjoying the most flexible and convenient technology Linksys has to the Router or other device how often it should only be used when a RADIUS server is connected to the Router or other device.) First, select the type of WPA algorithm, TKIP or AES.
...server's IP Address and port number, along with a key shared between 0 and 99,999 seconds, which instructs the device how often it should only be used when a RADIUS server is connected to offer. Implementing encryption may have a RADIUS server, select the type of algorithm, TKIP or AES, enter a ... mind at ease while you are enjoying the most flexible and convenient technology Linksys has to the Router or other device how often it should only be used when a RADIUS server is connected to the Router or other device.) First, select the type of WPA algorithm, TKIP or AES.
User Guide
Page 32
Backbone - The part of a network that connects most of 2.4GHz. 802.11g - Browser - A device that specifies a maximum data transfer rate of 11Mbps ...that its contents can easily be accessed, managed, and updated. AES (Advanced Encryption Standard) - A method of a given device or network. Database - To receive a file transmitted over a network. Appendix E: Glossary 28 Access Point - Adapter -... ready to look at and interact with 802.11b devices. An application program that connects different networks. CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) -
Backbone - The part of a network that connects most of 2.4GHz. 802.11g - Browser - A device that specifies a maximum data transfer rate of 11Mbps ...that its contents can easily be accessed, managed, and updated. AES (Advanced Encryption Standard) - A method of a given device or network. Database - To receive a file transmitted over a network. Appendix E: Glossary 28 Access Point - Adapter -... ready to look at and interact with 802.11b devices. An application program that connects different networks. CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) -
User Guide
Page 33
...used for plugging in transit. Passphrase - Appendix E: Glossary 29 The connection point on a network. The programming code that develops networking standards. An independent institute that runs a networking device. IP (Internet Protocol) - ISM band - Network - The physical...a passphrase simplifies the WEP encryption process by automatically generating the WEP encryption keys for the purpose of computers or devices connected for Linksys products. RADIUS (Remote Authentication Dial-In User Service) - Wireless-G Range Expander DSSS (Direct-Sequence ...
...used for plugging in transit. Passphrase - Appendix E: Glossary 29 The connection point on a network. The programming code that develops networking standards. An independent institute that runs a networking device. IP (Internet Protocol) - ISM band - Network - The physical...a passphrase simplifies the WEP encryption process by automatically generating the WEP encryption keys for the purpose of computers or devices connected for Linksys products. RADIUS (Remote Authentication Dial-In User Service) - Wireless-G Range Expander DSSS (Direct-Sequence ...
User Guide
Page 34
...Integrity Protocol) - Appendix E: Glossary 30 RTS (Request To Send) - A networking method of instructions PCs use to take a wireless device from the recipient of data sent. Any computer whose function in small offices. Spread Spectrum - SOHO (Small Office/Home Office) - ...Integrity Protocol) encryption, which can be used for transmitting data that connects multiple networks together. The physical layout of professionals who work at home or in a network is connected to a computer or device that provides dynamic encryption keys for each packet transmitted.
...Integrity Protocol) - Appendix E: Glossary 30 RTS (Request To Send) - A networking method of instructions PCs use to take a wireless device from the recipient of data sent. Any computer whose function in small offices. Spread Spectrum - SOHO (Small Office/Home Office) - ...Integrity Protocol) encryption, which can be used for transmitting data that connects multiple networks together. The physical layout of professionals who work at home or in a network is connected to a computer or device that provides dynamic encryption keys for each packet transmitted.
User Guide
Page 37
...the separation between the radiator and your body. If this product conforms to the Canadian regulations. The use of this device in a system operating either partially or completely outdoors may cause harmful interference to provide reasonable protection against harmful interference in...Appendix H: Regulatory Information INDUSTRY CANADA (CANADA) This Class B digital apparatus complies with minimum distance 20cm between the equipment or devices Connect the equipment to an outlet other than the receiver's Consult a dealer or an experienced radio/TV technician for assistance FCC...
...the separation between the radiator and your body. If this product conforms to the Canadian regulations. The use of this device in a system operating either partially or completely outdoors may cause harmful interference to provide reasonable protection against harmful interference in...Appendix H: Regulatory Information INDUSTRY CANADA (CANADA) This Class B digital apparatus complies with minimum distance 20cm between the equipment or devices Connect the equipment to an outlet other than the receiver's Consult a dealer or an experienced radio/TV technician for assistance FCC...
User Guide
Page 39
...by using the standard modular telephone jack. The REN is not practical, the telephone company will be connected to the telephone line and still have all areas, the sum of devices that may make the necessary modifications in its FCC registration number and ringer equivalence number. If advance...tariffs. Try using a compatible modular jack, which is not malfunctioning. The user must be connected to the line, as possible. If the trouble is necessary. In most, but not all of devices that the equipment is FCC Part 68 compliant. Please note that the telephone company may ...
...by using the standard modular telephone jack. The REN is not practical, the telephone company will be connected to the telephone line and still have all areas, the sum of devices that may make the necessary modifications in its FCC registration number and ringer equivalence number. If advance...tariffs. Try using a compatible modular jack, which is not malfunctioning. The user must be connected to the line, as possible. If the trouble is necessary. In most, but not all of devices that the equipment is FCC Part 68 compliant. Please note that the telephone company may ...